Computer memory on:
[Wikipedia]
[Google]
[Amazon]
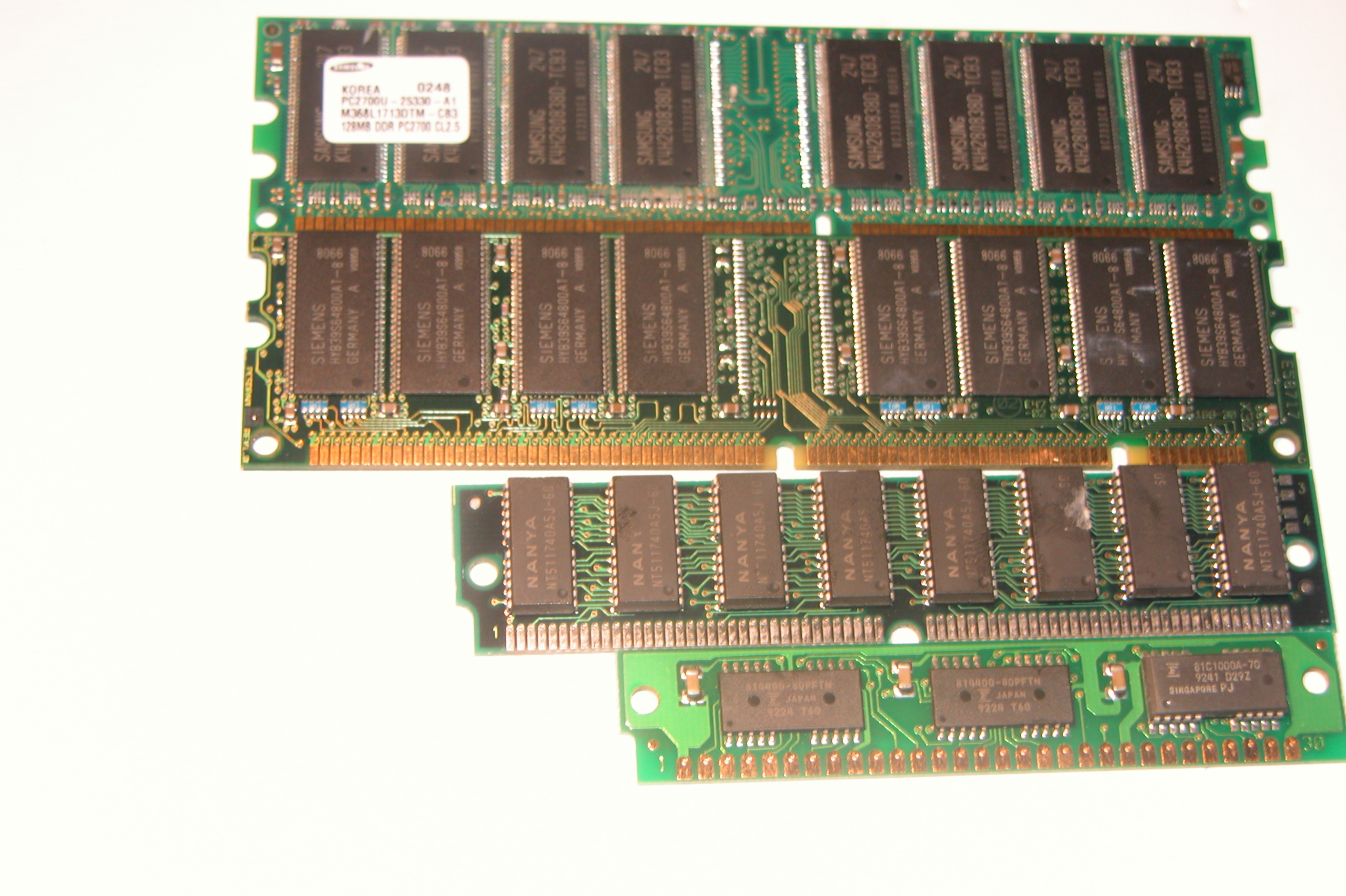
Computer memory stores information, such as data and programs, for immediate use in the




 In the early 1940s, memory technology often permitted a capacity of a few bytes. The first electronic programmable
In the early 1940s, memory technology often permitted a capacity of a few bytes. The first electronic programmable
history-computer.com
 Volatile memory is computer memory that requires power to maintain the stored information. Most modern
Volatile memory is computer memory that requires power to maintain the stored information. Most modern
computer
A computer is a machine that can be Computer programming, programmed to automatically Execution (computing), carry out sequences of arithmetic or logical operations (''computation''). Modern digital electronic computers can perform generic set ...
. The term ''memory'' is often synonymous with the terms ''RAM
Ram, ram, or RAM most commonly refers to:
* A male sheep
* Random-access memory, computer memory
* Ram Trucks, US, since 2009
** List of vehicles named Dodge Ram, trucks and vans
** Ram Pickup, produced by Ram Trucks
Ram, ram, or RAM may also ref ...
,'' ''main memory
Computer data storage or digital data storage is a technology consisting of computer components and recording media that are used to retain digital data. It is a core function and fundamental component of computers.
The central processin ...
,'' or ''primary storage
Computer data storage or digital data storage is a technology consisting of computer components and recording media that are used to retain digital data. It is a core function and fundamental component of computers.
The central processin ...
.'' Archaic synonyms for main memory include ''core'' (for magnetic core memory) and ''store''.
Main memory operates at a high speed compared to mass storage
In computing, mass storage refers to the storage of large amounts of data in a persisting and machine-readable fashion. In general, the term ''mass'' in ''mass storage'' is used to mean ''large'' in relation to contemporaneous hard disk drive ...
which is slower but less expensive per bit and higher in capacity. Besides storing opened programs and data being actively processed, computer memory serves as a mass storage cache and write buffer to improve both reading and writing performance. Operating systems borrow RAM
Ram, ram, or RAM most commonly refers to:
* A male sheep
* Random-access memory, computer memory
* Ram Trucks, US, since 2009
** List of vehicles named Dodge Ram, trucks and vans
** Ram Pickup, produced by Ram Trucks
Ram, ram, or RAM may also ref ...
capacity for caching so long as it is not needed by running software. If needed, contents of the computer memory can be transferred to storage; a common way of doing this is through a memory management technique called ''virtual memory
In computing, virtual memory, or virtual storage, is a memory management technique that provides an "idealized abstraction of the storage resources that are actually available on a given machine" which "creates the illusion to users of a ver ...
''.
Modern computer memory is implemented as semiconductor memory
Semiconductor memory is a digital electronic semiconductor device used for digital data storage, such as computer memory. It typically refers to devices in which data is stored within metal–oxide–semiconductor (MOS) memory cells on a si ...
, where data is stored within memory cells built from MOS transistors and other components on an integrated circuit
An integrated circuit (IC), also known as a microchip or simply chip, is a set of electronic circuits, consisting of various electronic components (such as transistors, resistors, and capacitors) and their interconnections. These components a ...
. There are two main kinds of semiconductor memory: volatile and non-volatile
Non-volatile memory (NVM) or non-volatile storage is a type of computer memory that can retain stored information even after power is removed. In contrast, volatile memory needs constant power in order to retain data.
Non-volatile memory typ ...
. Examples of non-volatile memory
Non-volatile memory (NVM) or non-volatile storage is a type of computer memory that can retain stored information even after power is removed. In contrast, volatile memory needs constant power in order to retain data.
Non-volatile memory typ ...
are flash memory
Flash memory is an Integrated circuit, electronic Non-volatile memory, non-volatile computer memory storage medium that can be electrically erased and reprogrammed. The two main types of flash memory, NOR flash and NAND flash, are named for t ...
and ROM
Rom, or ROM may refer to:
Biomechanics and medicine
* Risk of mortality, a medical classification to estimate the likelihood of death for a patient
* Rupture of membranes, a term used during pregnancy to describe a rupture of the amniotic sac
* ...
, PROM
A promenade dance or prom is a formal dance party for graduating high school students at the end of the school year.
Students participating in the prom will typically vote for a ''prom king'' and ''prom queen''. Other students may be honored ...
, EPROM
An EPROM (rarely EROM), or erasable programmable read-only memory, is a type of programmable read-only memory (PROM) integrated circuit, chip that retains its data when its power supply is switched off. Computer memory that can retrieve stored d ...
, and EEPROM
EEPROM or E2PROM (electrically erasable programmable read-only memory) is a type of non-volatile memory. It is used in computers, usually integrated in microcontrollers such as smart cards and remote keyless systems, or as a separate chip d ...
memory. Examples of volatile memory
Volatile memory, in contrast to non-volatile memory, is computer memory that requires power to maintain the stored information; it retains its contents while powered on but when the power is interrupted, the stored data is quickly lost.
Volatile ...
are dynamic random-access memory
Dynamics (from Greek language, Greek δυναμικός ''dynamikos'' "powerful", from δύναμις ''dynamis'' "power (disambiguation), power") or dynamic may refer to:
Physics and engineering
* Dynamics (mechanics), the study of forces and t ...
(DRAM) used for primary storage and static random-access memory
Static random-access memory (static RAM or SRAM) is a type of random-access memory (RAM) that uses latching circuitry (flip-flop) to store each bit. SRAM is volatile memory; data is lost when power is removed.
The ''static'' qualifier diffe ...
(SRAM) used mainly for CPU cache
A CPU cache is a hardware cache used by the central processing unit (CPU) of a computer to reduce the average cost (time or energy) to access data from the main memory. A cache is a smaller, faster memory, located closer to a processor core, whi ...
.
Most semiconductor memory is organized into memory cells each storing one bit (0 or 1). Flash memory
Flash memory is an Integrated circuit, electronic Non-volatile memory, non-volatile computer memory storage medium that can be electrically erased and reprogrammed. The two main types of flash memory, NOR flash and NAND flash, are named for t ...
organization includes both one bit per memory cell and a multi-level cell
In electronics, a multi-level cell (MLC) is a memory cell (computing), memory cell capable of storing more than a single bit of information, compared to a single-level cell (SLC), which can store only one bit per memory cell. A memory cell typical ...
capable of storing multiple bits per cell. The memory cells are grouped into words of fixed word length
In computing, a word is any processor design's natural unit of data. A word is a fixed-sized datum handled as a unit by the instruction set or the hardware of the processor. The number of bits or digits in a word (the ''word size'', ''word wid ...
, for example, 1, 2, 4, 8, 16, 32, 64 or 128 bits. Each word can be accessed by a binary address of ''N'' bits, making it possible to store 2''N'' words in the memory.
History



 In the early 1940s, memory technology often permitted a capacity of a few bytes. The first electronic programmable
In the early 1940s, memory technology often permitted a capacity of a few bytes. The first electronic programmable digital computer
A computer is a machine that can be programmed to automatically carry out sequences of arithmetic or logical operations (''computation''). Modern digital electronic computers can perform generic sets of operations known as ''programs'', wh ...
, the ENIAC
ENIAC (; Electronic Numerical Integrator and Computer) was the first Computer programming, programmable, Electronics, electronic, general-purpose digital computer, completed in 1945. Other computers had some of these features, but ENIAC was ...
, using thousands of vacuum tube
A vacuum tube, electron tube, thermionic valve (British usage), or tube (North America) is a device that controls electric current flow in a high vacuum between electrodes to which an electric voltage, potential difference has been applied. It ...
s, could perform simple calculations involving 20 numbers of ten decimal digits stored in the vacuum tubes.
The next significant advance in computer memory came with acoustic delay-line memory
Delay-line memory is a form of computer memory, mostly obsolete, that was used on some of the earliest Digital data, digital computers, and is reappearing in the form of #Optical_delay_lines, optical delay lines. Like many modern forms of electro ...
, developed by J. Presper Eckert in the early 1940s. Through the construction of a glass tube filled with mercury and plugged at each end with a quartz crystal, delay lines could store bits of information in the form of sound waves propagating through the mercury, with the quartz crystals acting as transducer
A transducer is a device that Energy transformation, converts energy from one form to another. Usually a transducer converts a signal in one form of energy to a signal in another.
Transducers are often employed at the boundaries of automation, M ...
s to read and write bits. Delay-line memory was limited to a capacity of up to a few thousand bits.
Two alternatives to the delay line, the Williams tube
The Williams tube, or the Williams–Kilburn tube named after inventors Frederic Calland Williams, Freddie Williams and Tom Kilburn, is an early form of computer memory. It was the first Random-access memory, random-access digital storage devi ...
and Selectron tube, originated in 1946, both using electron beams in glass tubes as means of storage. Using cathode-ray tube
A cathode-ray tube (CRT) is a vacuum tube containing one or more electron guns, which emit electron beams that are manipulated to display images on a phosphorescent screen. The images may represent electrical waveforms on an oscilloscope, a ...
s, Fred Williams invented the Williams tube, which was the first random-access computer memory. The Williams tube was able to store more information than the Selectron tube (the Selectron was limited to 256 bits, while the Williams tube could store thousands) and was less expensive. The Williams tube was nevertheless frustratingly sensitive to environmental disturbances.
Efforts began in the late 1940s to find non-volatile memory
Non-volatile memory (NVM) or non-volatile storage is a type of computer memory that can retain stored information even after power is removed. In contrast, volatile memory needs constant power in order to retain data.
Non-volatile memory typ ...
. Magnetic-core memory
In computing, magnetic-core memory is a form of random-access memory. It predominated for roughly 20 years between 1955 and 1975, and is often just called core memory, or, informally, core.
Core memory uses toroids (rings) of a hard magneti ...
allowed for memory recall after power loss. It was developed by Frederick W. Viehe and An Wang in the late 1940s, and improved by Jay Forrester and Jan A. Rajchman in the early 1950s, before being commercialized with the Whirlwind I
Whirlwind I was a Cold War-era vacuum-tube computer developed by the MIT Servomechanisms Laboratory for the U.S. Navy. Operational in 1951, it was among the first digital electronic computers that operated in real-time for output, and the firs ...
computer in 1953. Magnetic-core memory was the dominant form of memory until the development of MOS semiconductor memory
Semiconductor memory is a digital electronic semiconductor device used for digital data storage, such as computer memory. It typically refers to devices in which data is stored within metal–oxide–semiconductor (MOS) memory cells on a si ...
in the 1960s.
The first semiconductor memory
Semiconductor memory is a digital electronic semiconductor device used for digital data storage, such as computer memory. It typically refers to devices in which data is stored within metal–oxide–semiconductor (MOS) memory cells on a si ...
was implemented as a flip-flop circuit in the early 1960s using bipolar transistors
A bipolar junction transistor (BJT) is a type of transistor that uses both electrons and electron holes as charge carriers. In contrast, a unipolar transistor, such as a field-effect transistor (FET), uses only one kind of charge carrier. A ...
. Semiconductor memory made from discrete device
An electronic component is any basic discrete electronic device or physical entity part of an electronic system used to affect electrons or their associated fields. Electronic components are mostly industrial products, available in a singular ...
s was first shipped by Texas Instruments
Texas Instruments Incorporated (TI) is an American multinational semiconductor company headquartered in Dallas, Texas. It is one of the top 10 semiconductor companies worldwide based on sales volume. The company's focus is on developing analog ...
to the United States Air Force
The United States Air Force (USAF) is the Air force, air service branch of the United States Department of Defense. It is one of the six United States Armed Forces and one of the eight uniformed services of the United States. Tracing its ori ...
in 1961. In the same year, the concept of solid-state memory on an integrated circuit
An integrated circuit (IC), also known as a microchip or simply chip, is a set of electronic circuits, consisting of various electronic components (such as transistors, resistors, and capacitors) and their interconnections. These components a ...
(IC) chip was proposed by applications engineer Bob Norman at Fairchild Semiconductor
Fairchild Semiconductor International, Inc. was an American semiconductor company based in San Jose, California. It was founded in 1957 as a division of Fairchild Camera and Instrument by the " traitorous eight" who defected from Shockley Semi ...
. The first bipolar semiconductor memory IC chip was the SP95 introduced by IBM
International Business Machines Corporation (using the trademark IBM), nicknamed Big Blue, is an American Multinational corporation, multinational technology company headquartered in Armonk, New York, and present in over 175 countries. It is ...
in 1965. While semiconductor memory offered improved performance over magnetic-core memory, it remained larger and more expensive and did not displace magnetic-core memory until the late 1960s.
MOS memory
The invention of the metal–oxide–semiconductor field-effect transistor (MOSFET
upright=1.3, Two power MOSFETs in amperes">A in the ''on'' state, dissipating up to about 100 watt">W and controlling a load of over 2000 W. A matchstick is pictured for scale.
In electronics, the metal–oxide–semiconductor field- ...
) enabled the practical use of metal–oxide–semiconductor
upright=1.3, Two power MOSFETs in amperes">A in the ''on'' state, dissipating up to about 100 watt">W and controlling a load of over 2000 W. A matchstick is pictured for scale.
In electronics, the metal–oxide–semiconductor field- ...
(MOS) transistors as memory cell storage elements. MOS memory was developed by John Schmidt at Fairchild Semiconductor
Fairchild Semiconductor International, Inc. was an American semiconductor company based in San Jose, California. It was founded in 1957 as a division of Fairchild Camera and Instrument by the " traitorous eight" who defected from Shockley Semi ...
in 1964. In addition to higher performance, MOS semiconductor memory
Semiconductor memory is a digital electronic semiconductor device used for digital data storage, such as computer memory. It typically refers to devices in which data is stored within metal–oxide–semiconductor (MOS) memory cells on a si ...
was cheaper and consumed less power than magnetic core memory. In 1965, J. Wood and R. Ball of the Royal Radar Establishment proposed digital storage systems that use CMOS
Complementary metal–oxide–semiconductor (CMOS, pronounced "sea-moss
", , ) is a type of MOSFET, metal–oxide–semiconductor field-effect transistor (MOSFET) semiconductor device fabrication, fabrication process that uses complementary an ...
(complementary MOS) memory cells, in addition to MOSFET power devices for the power supply
A power supply is an electrical device that supplies electric power to an electrical load. The main purpose of a power supply is to convert electric current from a source to the correct voltage, electric current, current, and frequency to power ...
, switched cross-coupling, switches
In electrical engineering, a switch is an electrical component that can disconnect or connect the conducting path in an electrical circuit, interrupting the electric current or diverting it from one conductor to another. The most common type o ...
and delay-line storage. The development of silicon-gate MOS integrated circuit
upright=1.4, gate oxide">insulating layer (pink).
The MOSFET (metal–oxide–semiconductor field-effect transistor) is a type of insulated-gate field-effect transistor (IGFET) that is fabricated by the controlled oxidation of a semiconduct ...
(MOS IC) technology by Federico Faggin
Federico Faggin (, ; born 1 December 1941) is an Italian-American physicist, engineer, inventor and entrepreneur. He is best known for designing the first commercial microprocessor, the Intel 4004. He led the 4004 (MCS-4) project and the desig ...
at Fairchild in 1968 enabled the production of MOS memory chip
Semiconductor memory is a digital electronic semiconductor device used for digital data storage, such as computer memory. It typically refers to devices in which data is stored within metal–oxide–semiconductor (MOS) memory cells on a sil ...
s. NMOS memory was commercialized by IBM
International Business Machines Corporation (using the trademark IBM), nicknamed Big Blue, is an American Multinational corporation, multinational technology company headquartered in Armonk, New York, and present in over 175 countries. It is ...
in the early 1970s. MOS memory overtook magnetic core memory as the dominant memory technology in the early 1970s.
The two main types of volatile random-access memory
Random-access memory (RAM; ) is a form of Computer memory, electronic computer memory that can be read and changed in any order, typically used to store working Data (computing), data and machine code. A random-access memory device allows ...
(RAM) are static random-access memory
Static random-access memory (static RAM or SRAM) is a type of random-access memory (RAM) that uses latching circuitry (flip-flop) to store each bit. SRAM is volatile memory; data is lost when power is removed.
The ''static'' qualifier diffe ...
(SRAM) and dynamic random-access memory
Dynamics (from Greek language, Greek δυναμικός ''dynamikos'' "powerful", from δύναμις ''dynamis'' "power (disambiguation), power") or dynamic may refer to:
Physics and engineering
* Dynamics (mechanics), the study of forces and t ...
(DRAM). Bipolar SRAM was invented by Robert Norman at Fairchild Semiconductor in 1963, followed by the development of MOS SRAM by John Schmidt at Fairchild in 1964. SRAM became an alternative to magnetic-core memory, but requires six transistors for each bit of data. Commercial use of SRAM began in 1965, when IBM introduced their SP95 SRAM chip for the System/360 Model 95.
Toshiba
is a Japanese multinational electronics company headquartered in Minato, Tokyo. Its diversified products and services include power, industrial and social infrastructure systems, elevators and escalators, electronic components, semiconductors ...
introduced bipolar DRAM memory cells for its Toscal BC-1411 electronic calculator
An electronic calculator is typically a portable Electronics, electronic device used to perform calculations, ranging from basic arithmetic to complex mathematics.
The first solid-state electronic calculator was created in the early 1960s. ...
in 1965. While it offered improved performance, bipolar DRAM could not compete with the lower price of the then dominant magnetic-core memory. MOS technology is the basis for modern DRAM. In 1966, Robert H. Dennard at the IBM Thomas J. Watson Research Center was working on MOS memory. While examining the characteristics of MOS technology, he found it was possible to build capacitors
In electrical engineering, a capacitor is a device that stores electrical energy by accumulating electric charges on two closely spaced surfaces that are insulated from each other. The capacitor was originally known as the condenser, a term st ...
, and that storing a charge or no charge on the MOS capacitor could represent the 1 and 0 of a bit, while the MOS transistor could control writing the charge to the capacitor. This led to his development of a single-transistor DRAM memory cell. In 1967, Dennard filed a patent for a single-transistor DRAM memory cell based on MOS technology. This led to the first commercial DRAM IC chip, the Intel 1103 in October 1970.''The DRAM memory of Robert Dennard''history-computer.com
Synchronous dynamic random-access memory
Synchronous dynamic random-access memory (synchronous dynamic RAM or SDRAM) is any DRAM where the operation of its external pin interface is coordinated by an externally supplied clock signal.
DRAM integrated circuits (ICs) produced from the ...
(SDRAM) later debuted with the Samsung
Samsung Group (; stylised as SΛMSUNG) is a South Korean Multinational corporation, multinational manufacturing Conglomerate (company), conglomerate headquartered in the Samsung Town office complex in Seoul. The group consists of numerous a ...
KM48SL2000 chip in 1992.
The term ''memory'' is also often used to refer to non-volatile memory
Non-volatile memory (NVM) or non-volatile storage is a type of computer memory that can retain stored information even after power is removed. In contrast, volatile memory needs constant power in order to retain data.
Non-volatile memory typ ...
including read-only memory
Read-only memory (ROM) is a type of non-volatile memory used in computers and other electronic devices. Data stored in ROM cannot be electronically modified after the manufacture of the memory device. Read-only memory is useful for storing sof ...
(ROM) through modern flash memory
Flash memory is an Integrated circuit, electronic Non-volatile memory, non-volatile computer memory storage medium that can be electrically erased and reprogrammed. The two main types of flash memory, NOR flash and NAND flash, are named for t ...
. Programmable read-only memory
A programmable read-only memory (PROM) is a form of digital memory where the contents can be changed once after manufacture of the device. The data is then permanent and cannot be changed. It is one type of read-only memory (ROM). PROMs are used i ...
(PROM) was invented by Wen Tsing Chow in 1956, while working for the Arma Division of the American Bosch Arma Corporation. In 1967, Dawon Kahng and Simon Sze
Simon Min Sze, or Shi Min (; 21 March 1936 – 6 November 2023), was a Taiwanese-American electrical engineer. He is best known for inventing the floating-gate MOSFET with Korean electrical engineer Dawon Kahng in 1967.
Early life and educat ...
of Bell Labs proposed that the floating gate of a MOS semiconductor device
A semiconductor device is an electronic component that relies on the electronic properties of a semiconductor material (primarily silicon, germanium, and gallium arsenide, as well as organic semiconductors) for its function. Its conductivit ...
could be used for the cell of a reprogrammable ROM, which led to Dov Frohman of Intel
Intel Corporation is an American multinational corporation and technology company headquartered in Santa Clara, California, and Delaware General Corporation Law, incorporated in Delaware. Intel designs, manufactures, and sells computer compo ...
inventing EPROM
An EPROM (rarely EROM), or erasable programmable read-only memory, is a type of programmable read-only memory (PROM) integrated circuit, chip that retains its data when its power supply is switched off. Computer memory that can retrieve stored d ...
(erasable PROM) in 1971. EEPROM
EEPROM or E2PROM (electrically erasable programmable read-only memory) is a type of non-volatile memory. It is used in computers, usually integrated in microcontrollers such as smart cards and remote keyless systems, or as a separate chip d ...
(electrically erasable PROM) was developed by Yasuo Tarui, Yutaka Hayashi and Kiyoko Naga at the Electrotechnical Laboratory in 1972. Flash memory was invented by Fujio Masuoka
is a Japanese engineer, who has worked for Toshiba and Tohoku University, and is currently chief technical officer (CTO) of Unisantis Electronics. He is best known as the inventor of flash memory, including the development of both the NOR flash ...
at Toshiba
is a Japanese multinational electronics company headquartered in Minato, Tokyo. Its diversified products and services include power, industrial and social infrastructure systems, elevators and escalators, electronic components, semiconductors ...
in the early 1980s. Masuoka and colleagues presented the invention of NOR flash in 1984, and then NAND flash
Flash memory is an Integrated circuit, electronic Non-volatile memory, non-volatile computer memory storage medium that can be electrically erased and reprogrammed. The two main types of flash memory, NOR flash and NAND flash, are named for t ...
in 1987. Toshiba commercialized NAND flash memory in 1987.
Developments in technology and economies of scale have made possible so-called (VLM) computers.
Volatility categories
Volatile memory
semiconductor
A semiconductor is a material with electrical conductivity between that of a conductor and an insulator. Its conductivity can be modified by adding impurities (" doping") to its crystal structure. When two regions with different doping level ...
volatile memory is either static RAM
Static random-access memory (static RAM or SRAM) is a type of random-access memory (RAM) that uses latching circuitry (flip-flop) to store each bit. SRAM is volatile memory; data is lost when power is removed.
The ''static'' qualifier differ ...
(SRAM) or dynamic RAM (DRAM). DRAM dominates for desktop system memory. SRAM is used for CPU cache
A CPU cache is a hardware cache used by the central processing unit (CPU) of a computer to reduce the average cost (time or energy) to access data from the main memory. A cache is a smaller, faster memory, located closer to a processor core, whi ...
. SRAM is also found in small embedded system
An embedded system is a specialized computer system—a combination of a computer processor, computer memory, and input/output peripheral devices—that has a dedicated function within a larger mechanical or electronic system. It is e ...
s requiring little memory.
SRAM retains its contents as long as the power is connected and may use a simpler interface, but commonly uses six transistors per bit. Dynamic RAM is more complicated for interfacing and control, needing regular refresh cycles to prevent losing its contents, but uses only one transistor and one capacitor per bit, allowing it to reach much higher densities and much cheaper per-bit costs.
Non-volatile memory
Non-volatile memory can retain the stored information even when not powered. Examples of non-volatile memory includeread-only memory
Read-only memory (ROM) is a type of non-volatile memory used in computers and other electronic devices. Data stored in ROM cannot be electronically modified after the manufacture of the memory device. Read-only memory is useful for storing sof ...
, flash memory
Flash memory is an Integrated circuit, electronic Non-volatile memory, non-volatile computer memory storage medium that can be electrically erased and reprogrammed. The two main types of flash memory, NOR flash and NAND flash, are named for t ...
, most types of magnetic computer storage devices (e.g. hard disk drive
A hard disk drive (HDD), hard disk, hard drive, or fixed disk is an electro-mechanical data storage device that stores and retrieves digital data using magnetic storage with one or more rigid rapidly rotating hard disk drive platter, pla ...
s, floppy disk
A floppy disk or floppy diskette (casually referred to as a floppy, a diskette, or a disk) is a type of disk storage composed of a thin and flexible disk of a magnetic storage medium in a square or nearly square plastic enclosure lined with a ...
s and magnetic tape
Magnetic tape is a medium for magnetic storage made of a thin, magnetizable coating on a long, narrow strip of plastic film. It was developed in Germany in 1928, based on the earlier magnetic wire recording from Denmark. Devices that use magnetic ...
), optical disc
An optical disc is a flat, usuallyNon-circular optical discs exist for fashion purposes; see shaped compact disc. disc-shaped object that stores information in the form of physical variations on its surface that can be read with the aid o ...
s, and early computer storage methods such as magnetic drum
Drum memory was a magnetic data storage device invented by Gustav Tauschek in 1932 in Austria. Drums were widely used in the 1950s and into the 1960s as computer memory.
Many early computers, called drum computers or drum machines, used dru ...
, paper tape
Five- and eight-hole wide punched paper tape
Paper tape reader on the Harwell computer with a small piece of five-hole tape connected in a circle – creating a physical program loop
Punched tape or perforated paper tape is a form of data st ...
and punched card
A punched card (also punch card or punched-card) is a stiff paper-based medium used to store digital information via the presence or absence of holes in predefined positions. Developed over the 18th to 20th centuries, punched cards were widel ...
s.
Non-volatile memory technologies under development include ferroelectric RAM
Ferroelectric RAM (FeRAM, F-RAM or FRAM) is a random-access memory similar in construction to DRAM but using a ferroelectric layer instead of a dielectric layer to achieve non-volatility. FeRAM is one of a growing number of alternative non-vol ...
, programmable metallization cell
The programmable metallization cell, or PMC, is a non-volatile computer memory developed at Arizona State University. PMC, a technology developed to replace the widely used flash memory, providing a combination of longer lifetimes, lower power, a ...
, Spin-transfer torque magnetic RAM, SONOS
Sonos, Inc. is an American audio equipment manufacturer headquartered in Santa Barbara, California. The company was founded in 2002 by John MacFarlane, Craig Shelburne, Tom Cullen, and Trung Mai.
Sonos has partnered with over 100 companies th ...
, resistive random-access memory, racetrack memory, Nano-RAM
Nano-RAM is a proprietary computer memory technology from the company Nantero. It is a type of non-volatile memory, nonvolatile random-access memory based on the position of carbon nanotubes deposited on a chip-like substrate. In theory, the small ...
, 3D XPoint, and millipede memory.
Semi-volatile memory
A third category of memory is ''semi-volatile''. The term is used to describe a memory that has some limited non-volatile duration after power is removed, but then data is ultimately lost. A typical goal when using a semi-volatile memory is to provide the high performance and durability associated with volatile memories while providing some benefits of non-volatile memory. For example, some non-volatile memory types experience wear when written. A ''worn'' cell has increased volatility but otherwise continues to work. Data locations which are written frequently can thus be directed to use worn circuits. As long as the location is updated within some known retention time, the data stays valid. After a period of time without update, the value is copied to a less-worn circuit with longer retention. Writing first to the worn area allows a high write rate while avoiding wear on the not-worn circuits. As a second example, an STT-RAM can be made non-volatile by building large cells, but doing so raises the cost per bit and power requirements and reduces the write speed. Using small cells improves cost, power, and speed, but leads to semi-volatile behavior. In some applications, the increased volatility can be managed to provide many benefits of a non-volatile memory, for example by removing power but forcing a wake-up before data is lost; or by caching read-only data and discarding the cached data if the power-off time exceeds the non-volatile threshold. The term semi-volatile is also used to describe semi-volatile behavior constructed from other memory types, such as nvSRAM, which combines SRAM and a non-volatile memory on the same chip, where an external signal copies data from the volatile memory to the non-volatile memory, but if power is removed before the copy occurs, the data is lost. Another example is battery-backed RAM, which uses an external battery to power the memory device in case of external power loss. If power is off for an extended period of time, the battery may run out, resulting in data loss.Management
Proper management of memory is vital for a computer system to operate properly. Modernoperating system
An operating system (OS) is system software that manages computer hardware and software resources, and provides common daemon (computing), services for computer programs.
Time-sharing operating systems scheduler (computing), schedule tasks for ...
s have complex systems to properly manage memory. Failure to do so can lead to bugs or slow performance.
Bugs
Improper management of memory is a common cause of bugs and security vulnerabilities, including the following types: * Amemory leak
In computer science, a memory leak is a type of resource leak that occurs when a computer program incorrectly manages memory allocations in a way that memory which is no longer needed is not released. A memory leak may also happen when an objec ...
occurs when a program requests memory from the operating system and never returns the memory when it is done with it. A program with this bug will gradually require more and more memory until the program fails as the operating system runs out.
* A segmentation fault results when a program tries to access memory that it does not have permission to access. Generally, a program doing so will be terminated by the operating system.
* A buffer overflow occurs when a program writes data to the end of its allocated space and then continues to write data beyond this to memory that has been allocated for other purposes. This may result in erratic program behavior, including memory access errors, incorrect results, a crash, or a breach of system security. They are thus the basis of many software vulnerabilities and can be maliciously exploited.
Virtual memory
Virtual memory is a system where physical memory is managed by the operating system typically with assistance from amemory management unit
A memory management unit (MMU), sometimes called paged memory management unit (PMMU), is a computer hardware unit that examines all references to computer memory, memory, and translates the memory addresses being referenced, known as virtual mem ...
, which is part of many modern CPUs. It allows multiple types of memory to be used. For example, some data can be stored in RAM while other data is stored on a hard drive
A hard disk drive (HDD), hard disk, hard drive, or fixed disk is an electro-mechanical data storage device that stores and retrieves digital data using magnetic storage with one or more rigid rapidly rotating hard disk drive platter, pla ...
(e.g. in a swapfile), functioning as an extension of the cache hierarchy
Cache hierarchy, or multi-level cache, is a memory architecture that uses a hierarchy of memory stores based on varying access speeds to cache data. Highly requested data is cached in high-speed access memory stores, allowing swifter access by cent ...
. This offers several advantages. Computer programmers no longer need to worry about where their data is physically stored or whether the user's computer will have enough memory. The operating system will place actively used data in RAM, which is much faster than hard disks. When the amount of RAM is not sufficient to run all the current programs, it can result in a situation where the computer spends more time moving data from RAM to disk and back than it does accomplishing tasks; this is known as thrashing.
Protected memory
Protected memory is a system where each program is given an area of memory to use and is prevented from going outside that range. If the operating system detects that a program has tried to alter memory that does not belong to it, the program is terminated (or otherwise restricted or redirected). This way, only the offending program crashes, and other programs are not affected by the misbehavior (whether accidental or intentional). Use of protected memory greatly enhances both the reliability and security of a computer system. Without protected memory, it is possible that a bug in one program will alter the memory used by another program. This will cause that other program to run off of corrupted memory with unpredictable results. If the operating system's memory is corrupted, the entire computer system may crash and need to be rebooted. At times programs intentionally alter the memory used by other programs. This is done by viruses and malware to take over computers. It may also be used benignly by desirable programs which are intended to modify other programs,debugger
A debugger is a computer program used to test and debug other programs (the "target" programs). Common features of debuggers include the ability to run or halt the target program using breakpoints, step through code line by line, and display ...
s, for example, to insert breakpoints or hooks.
See also
*Memory geometry
In the design of modern computers, memory geometry describes the internal structure of random-access memory. Memory geometry is of concern to consumers upgrading their computers, since older memory controllers may not be compatible with later pr ...
* Memory hierarchy
In computer architecture, the memory hierarchy separates computer storage into a hierarchy based on response time. Since response time, complexity, and capacity are related, the levels may also be distinguished by their performance and contr ...
* Memory organization
* Processor register
A processor register is a quickly accessible location available to a computer's processor. Registers usually consist of a small amount of fast storage, although some registers have specific hardware functions, and may be read-only or write-onl ...
s store data but normally are not considered as memory, since they only store one word and do not include an addressing mechanism.
* Universal memory
Universal memory refers to a computer data storage device combining the cost benefits of DRAM, the speed of SRAM, the non-volatility of flash memory along with infinite durability, and longevity. Such a device, if it ever becomes possible to dev ...
, memory combining both large capacity and high speed
Notes
References
Further reading
* * {{Benchmark MOSFETs Digital electronics