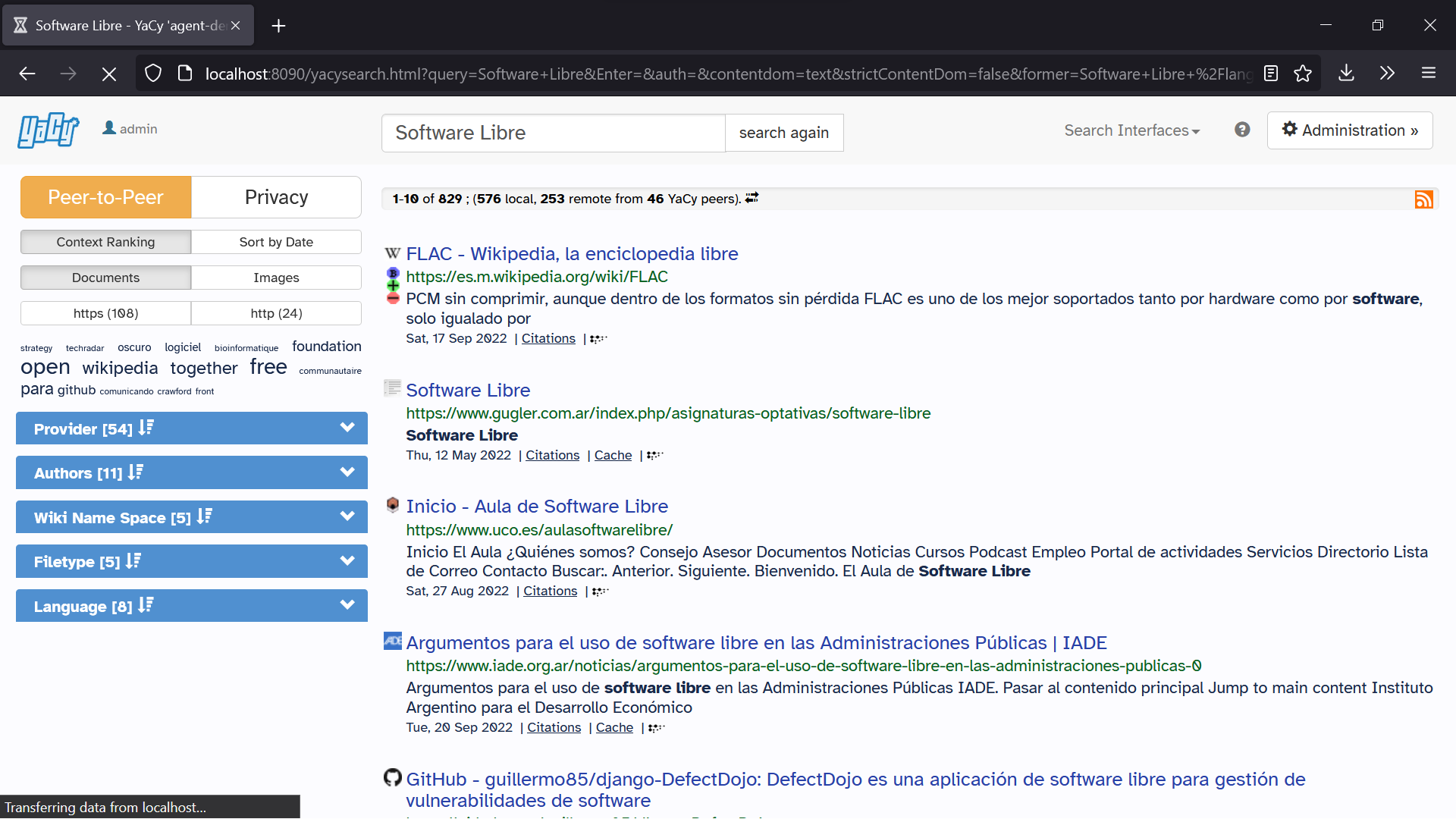
Peer-to-peer Network on:
[Wikipedia]
[Google]
[Amazon]
 Peer-to-peer (P2P) computing or networking is a
Peer-to-peer (P2P) computing or networking is a
 While P2P systems had previously been used in many application domains, the concept was popularized by
While P2P systems had previously been used in many application domains, the concept was popularized by
 ''Unstructured peer-to-peer networks'' do not impose a particular structure on the overlay network by design, but rather are formed by nodes that randomly form connections to each other. ( Gnutella, Gossip, and Kazaa are examples of unstructured P2P protocols).
Because there is no structure globally imposed upon them, unstructured networks are easy to build and allow for localized optimizations to different regions of the overlay. Also, because the role of all peers in the network is the same, unstructured networks are highly robust in the face of high rates of "churn"—that is, when large numbers of peers are frequently joining and leaving the network.
However, the primary limitations of unstructured networks also arise from this lack of structure. In particular, when a peer wants to find a desired piece of data in the network, the search query must be flooded through the network to find as many peers as possible that share the data. Flooding causes a very high amount of signaling traffic in the network, uses more
''Unstructured peer-to-peer networks'' do not impose a particular structure on the overlay network by design, but rather are formed by nodes that randomly form connections to each other. ( Gnutella, Gossip, and Kazaa are examples of unstructured P2P protocols).
Because there is no structure globally imposed upon them, unstructured networks are easy to build and allow for localized optimizations to different regions of the overlay. Also, because the role of all peers in the network is the same, unstructured networks are highly robust in the face of high rates of "churn"—that is, when large numbers of peers are frequently joining and leaving the network.
However, the primary limitations of unstructured networks also arise from this lack of structure. In particular, when a peer wants to find a desired piece of data in the network, the search query must be flooded through the network to find as many peers as possible that share the data. Flooding causes a very high amount of signaling traffic in the network, uses more
 In ''structured peer-to-peer networks'' the overlay is organized into a specific topology, and the protocol ensures that any node can efficiently search the network for a file/resource, even if the resource is extremely rare.
The most common type of structured P2P networks implement a distributed hash table (DHT), in which a variant of consistent hashing is used to assign ownership of each file to a particular peer. This enables peers to search for resources on the network using a
In ''structured peer-to-peer networks'' the overlay is organized into a specific topology, and the protocol ensures that any node can efficiently search the network for a file/resource, even if the resource is extremely rare.
The most common type of structured P2P networks implement a distributed hash table (DHT), in which a variant of consistent hashing is used to assign ownership of each file to a particular peer. This enables peers to search for resources on the network using a  However, in order to route traffic efficiently through the network, nodes in a structured overlay must maintain lists of neighbors that satisfy specific criteria. This makes them less robust in networks with a high rate of ''churn'' (i.e. with large numbers of nodes frequently joining and leaving the network). More recent evaluation of P2P resource discovery solutions under real workloads have pointed out several issues in DHT-based solutions such as high cost of advertising/discovering resources and static and dynamic load imbalance.
Notable distributed networks that use DHTs include Tixati, an alternative to BitTorrent's distributed tracker, the Kad network, the
However, in order to route traffic efficiently through the network, nodes in a structured overlay must maintain lists of neighbors that satisfy specific criteria. This makes them less robust in networks with a high rate of ''churn'' (i.e. with large numbers of nodes frequently joining and leaving the network). More recent evaluation of P2P resource discovery solutions under real workloads have pointed out several issues in DHT-based solutions such as high cost of advertising/discovering resources and static and dynamic load imbalance.
Notable distributed networks that use DHTs include Tixati, an alternative to BitTorrent's distributed tracker, the Kad network, the
in an attempt to use locality. If multiple peers are found with the same file it designates that the node choose the fastest of its neighbors.
 There are both advantages and disadvantages in P2P networks related to the topic of data backup, recovery, and availability. In a centralized network, the system administrators are the only forces controlling the availability of files being shared. If the administrators decide to no longer distribute a file, they simply have to remove it from their servers, and it will no longer be available to users. Along with leaving the users powerless in deciding what is distributed throughout the community, this makes the entire system vulnerable to threats and requests from the government and other large forces. For example,
There are both advantages and disadvantages in P2P networks related to the topic of data backup, recovery, and availability. In a centralized network, the system administrators are the only forces controlling the availability of files being shared. If the administrators decide to no longer distribute a file, they simply have to remove it from their servers, and it will no longer be available to users. Along with leaving the users powerless in deciding what is distributed throughout the community, this makes the entire system vulnerable to threats and requests from the government and other large forces. For example,
 *
*
 Cooperation among a community of participants is key to the continued success of P2P systems aimed at casual human users; these reach their full potential only when large numbers of nodes contribute resources. But in current practice, P2P networks often contain large numbers of users who utilize resources shared by other nodes, but who do not share anything themselves (often referred to as the "freeloader problem"). Freeloading can have a profound impact on the network and in some cases can cause the community to collapse. In these types of networks "users have natural disincentives to cooperate because cooperation consumes their own resources and may degrade their own performance."Feldman, M., Lai, K., Stoica, I., & Chuang, J. (2004, May). Robust incentive techniques for peer-to-peer networks. In Proceedings of the 5th ACM conference on Electronic commerce (pp. 102-111). ACM. Studying the social attributes of P2P networks is challenging due to large populations of turnover, asymmetry of interest and zero-cost identity. A variety of incentive mechanisms have been implemented to encourage or even force nodes to contribute resources.
Some researchers have explored the benefits of enabling virtual communities to self-organize and introduce incentives for resource sharing and cooperation, arguing that the social aspect missing from today's P2P systems should be seen both as a goal and a means for self-organized virtual communities to be built and fostered. Ongoing research efforts for designing effective incentive mechanisms in P2P systems, based on principles from game theory, are beginning to take on a more psychological and information-processing direction.
Cooperation among a community of participants is key to the continued success of P2P systems aimed at casual human users; these reach their full potential only when large numbers of nodes contribute resources. But in current practice, P2P networks often contain large numbers of users who utilize resources shared by other nodes, but who do not share anything themselves (often referred to as the "freeloader problem"). Freeloading can have a profound impact on the network and in some cases can cause the community to collapse. In these types of networks "users have natural disincentives to cooperate because cooperation consumes their own resources and may degrade their own performance."Feldman, M., Lai, K., Stoica, I., & Chuang, J. (2004, May). Robust incentive techniques for peer-to-peer networks. In Proceedings of the 5th ACM conference on Electronic commerce (pp. 102-111). ACM. Studying the social attributes of P2P networks is challenging due to large populations of turnover, asymmetry of interest and zero-cost identity. A variety of incentive mechanisms have been implemented to encourage or even force nodes to contribute resources.
Some researchers have explored the benefits of enabling virtual communities to self-organize and introduce incentives for resource sharing and cooperation, arguing that the social aspect missing from today's P2P systems should be seen both as a goal and a means for self-organized virtual communities to be built and fostered. Ongoing research efforts for designing effective incentive mechanisms in P2P systems, based on principles from game theory, are beginning to take on a more psychological and information-processing direction.
"Free-rider detection and punishment in BitTorrent based P2P networks"
International Advanced Computing Conference, 2014.
P2P-VoD Streaming: Design Issues & User Experience Challenges
Springer Proceedings, June 2014
of P2P terminology
Foundation of Peer-to-Peer Computing
Special Issue, Elsevier Journal of Computer Communication, (Ed) Javed I. Khan and Adam Wierzbicki, Volume 31, Issue 2, February 2008 * * Marling Engle & J. I. Khan
Vulnerabilities of P2P systems and a critical look at their solutions
May 2006 * Stephanos Androutsellis-Theotokis and Diomidis Spinellis
ACM Computing Surveys, 36(4):335–371, December 2004. * Biddle, Peter, Paul England, Marcus Peinado, and Bryan Willman
The Darknet and the Future of Content Distribution
In ''2002 ACM Workshop on Digital Rights Management'', November 2002. * John F. Buford, Heather Yu, Eng Keong Lu
P2P Networking and Applications
, Morgan Kaufmann, December 2008 * Djamal-Eddine Meddour, Mubashar Mushtaq, and Toufik Ahmed,
Open Issues in P2P Multimedia Streaming
, in the proceedings of the 1st Multimedia Communications Workshop MULTICOMM 2006 held in conjunction with IEEE ICC 2006 pp 43–48, June 2006, Istanbul, Turkey. * Detlef Schoder and Kai Fischbach,
Core Concepts in Peer-to-Peer (P2P) Networking
. In: Subramanian, R.; Goodman, B. (eds.): ''P2P Computing: The Evolution of a Disruptive Technology'', Idea Group Inc, Hershey. 2005 * Ramesh Subramanian and Brian Goodman (eds),
Peer-to-Peer Computing: Evolution of a Disruptive Technology
', , Idea Group Inc., Hershey, PA, United States, 2005. *
Advanced Peer-Based Technology Business Models
Music Downloads: Pirates- or Customers?
'. Harvard Business School Working Knowledge, 2004.
Glasnost
test P2P traffic shaping ( Max Planck Institute for Software Systems) {{DEFAULTSORT:Peer-To-Peer File sharing networks File sharing Software engineering terminology
distributed application
A distributed system is a system whose components are located on different networked computers, which communicate and coordinate their actions by passing messages to one another from any system. Distributed computing is a field of computer sci ...
architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network. They are said to form a peer-to-peer network of nodes.
Peers make a portion of their resources, such as processing power, disk storage or network bandwidth, directly available to other network participants, without the need for central coordination by servers or stable hosts. Peers are both suppliers and consumers of resources, in contrast to the traditional client–server model
The client–server model is a distributed application structure that partitions tasks or workloads between the providers of a resource or service, called servers, and service requesters, called clients. Often clients and servers communicate ov ...
in which the consumption and supply of resources are divided.
While P2P systems had previously been used in many application domains, the architecture was popularized by the file sharing system Napster
Napster was a peer-to-peer file sharing application. It originally launched on June 1, 1999, with an emphasis on digital audio file distribution. Audio songs shared on the service were typically encoded in the MP3 format. It was founded by Sh ...
, originally released in 1999. The concept has inspired new structures and philosophies in many areas of human interaction. In such social contexts, peer-to-peer as a meme refers to the egalitarian
Egalitarianism (), or equalitarianism, is a school of thought within political philosophy that builds from the concept of social equality, prioritizing it for all people. Egalitarian doctrines are generally characterized by the idea that all hu ...
social network
A social network is a social structure made up of a set of social actors (such as individuals or organizations), sets of dyadic ties, and other social interactions between actors. The social network perspective provides a set of methods for ...
ing that has emerged throughout society, enabled by Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a ''internetworking, network of networks'' that consists ...
technologies in general.
Historical development
 While P2P systems had previously been used in many application domains, the concept was popularized by
While P2P systems had previously been used in many application domains, the concept was popularized by file sharing
File sharing is the practice of distributing or providing access to digital media, such as computer programs, multimedia (audio, images and video), documents or electronic books. Common methods of storage, transmission and dispersion include r ...
systems such as the music-sharing application Napster
Napster was a peer-to-peer file sharing application. It originally launched on June 1, 1999, with an emphasis on digital audio file distribution. Audio songs shared on the service were typically encoded in the MP3 format. It was founded by Sh ...
(originally released in 1999). The peer-to-peer movement allowed millions of Internet users to connect "directly, forming groups and collaborating to become user-created search engines, virtual supercomputers, and filesystems." The basic concept of peer-to-peer computing was envisioned in earlier software systems and networking discussions, reaching back to principles stated in the first Request for Comments
A Request for Comments (RFC) is a publication in a series from the principal technical development and standards-setting bodies for the Internet, most prominently the Internet Engineering Task Force (IETF). An RFC is authored by individuals or ...
, RFC 1.
Tim Berners-Lee
Sir Timothy John Berners-Lee (born 8 June 1955), also known as TimBL, is an English computer scientist best known as the inventor of the World Wide Web. He is a Professorial Fellow of Computer Science at the University of Oxford and a profe ...
's vision for the World Wide Web
The World Wide Web (WWW), commonly known as the Web, is an information system enabling documents and other web resources to be accessed over the Internet.
Documents and downloadable media are made available to the network through web se ...
was close to a P2P network in that it assumed each user of the web would be an active editor and contributor, creating and linking content to form an interlinked "web" of links. The early Internet was more open than the present day, where two machines connected to the Internet could send packets to each other without firewalls and other security measures. This contrasts to the broadcasting
Broadcasting is the distribution of audio or video content to a dispersed audience via any electronic mass communications medium, but typically one using the electromagnetic spectrum (radio waves), in a one-to-many model. Broadcasting began ...
-like structure of the web as it has developed over the years. As a precursor to the Internet, ARPANET
The Advanced Research Projects Agency Network (ARPANET) was the first wide-area packet-switched network with distributed control and one of the first networks to implement the TCP/IP protocol suite. Both technologies became the technical foun ...
was a successful client-server network where "every participating node could request and serve content." However, ARPANET was not self-organized, and it lacked the ability to "provide any means for context or content-based routing beyond 'simple' address-based routing."
Therefore, Usenet
Usenet () is a worldwide distributed discussion system available on computers. It was developed from the general-purpose Unix-to-Unix Copy (UUCP) dial-up network architecture. Tom Truscott and Jim Ellis conceived the idea in 1979, and it was ...
, a distributed messaging system that is often described as an early peer-to-peer architecture, was established. It was developed in 1979 as a system that enforces a decentralized model of control. The basic model is a client–server model from the user or client perspective that offers a self-organizing approach to newsgroup servers. However, news servers communicate with one another as peers to propagate Usenet news articles over the entire group of network servers. The same consideration applies to SMTP
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typic ...
email in the sense that the core email-relaying network of mail transfer agents has a peer-to-peer character, while the periphery of Email client
An email client, email reader or, more formally, message user agent (MUA) or mail user agent is a computer program used to access and manage a user's email.
A web application which provides message management, composition, and reception functio ...
s and their direct connections is strictly a client-server relationship.
In May 1999, with millions more people on the Internet, Shawn Fanning introduced the music and file-sharing application called Napster. Napster was the beginning of peer-to-peer networks, as we know them today, where "participating users establish a virtual network, entirely independent from the physical network, without having to obey any administrative authorities or restrictions."
Architecture
A peer-to-peer network is designed around the notion of equal ''peer
Peer may refer to:
Sociology
* Peer, an equal in age, education or social class; see Peer group
* Peer, a member of the peerage; related to the term "peer of the realm"
Computing
* Peer, one of several functional units in the same layer of a net ...
'' nodes simultaneously functioning as both "clients" and "servers" to the other nodes on the network. This model of network arrangement differs from the client–server model where communication is usually to and from a central server. A typical example of a file transfer that uses the client-server model is the File Transfer Protocol (FTP) service in which the client and server programs are distinct: the clients initiate the transfer, and the servers satisfy these requests.
Routing and resource discovery
Peer-to-peer networks generally implement some form of virtual overlay network on top of the physical network topology, where the nodes in the overlay form asubset
In mathematics, set ''A'' is a subset of a set ''B'' if all elements of ''A'' are also elements of ''B''; ''B'' is then a superset of ''A''. It is possible for ''A'' and ''B'' to be equal; if they are unequal, then ''A'' is a proper subset o ...
of the nodes in the physical network. Data is still exchanged directly over the underlying TCP/IP network, but at the application layer
An application layer is an abstraction layer that specifies the shared communications protocols and interface methods used by hosts in a communications network. An ''application layer'' abstraction is specified in both the Internet Protocol ...
peers are able to communicate with each other directly, via the logical overlay links (each of which corresponds to a path through the underlying physical network). Overlays are used for indexing and peer discovery, and make the P2P system independent from the physical network topology. Based on how the nodes are linked to each other within the overlay network, and how resources are indexed and located, we can classify networks as ''unstructured'' or ''structured'' (or as a hybrid between the two).
Unstructured networks
 ''Unstructured peer-to-peer networks'' do not impose a particular structure on the overlay network by design, but rather are formed by nodes that randomly form connections to each other. ( Gnutella, Gossip, and Kazaa are examples of unstructured P2P protocols).
Because there is no structure globally imposed upon them, unstructured networks are easy to build and allow for localized optimizations to different regions of the overlay. Also, because the role of all peers in the network is the same, unstructured networks are highly robust in the face of high rates of "churn"—that is, when large numbers of peers are frequently joining and leaving the network.
However, the primary limitations of unstructured networks also arise from this lack of structure. In particular, when a peer wants to find a desired piece of data in the network, the search query must be flooded through the network to find as many peers as possible that share the data. Flooding causes a very high amount of signaling traffic in the network, uses more
''Unstructured peer-to-peer networks'' do not impose a particular structure on the overlay network by design, but rather are formed by nodes that randomly form connections to each other. ( Gnutella, Gossip, and Kazaa are examples of unstructured P2P protocols).
Because there is no structure globally imposed upon them, unstructured networks are easy to build and allow for localized optimizations to different regions of the overlay. Also, because the role of all peers in the network is the same, unstructured networks are highly robust in the face of high rates of "churn"—that is, when large numbers of peers are frequently joining and leaving the network.
However, the primary limitations of unstructured networks also arise from this lack of structure. In particular, when a peer wants to find a desired piece of data in the network, the search query must be flooded through the network to find as many peers as possible that share the data. Flooding causes a very high amount of signaling traffic in the network, uses more CPU
A central processing unit (CPU), also called a central processor, main processor or just processor, is the electronic circuitry that executes instructions comprising a computer program. The CPU performs basic arithmetic, logic, controlling, and ...
/memory (by requiring every peer to process all search queries), and does not ensure that search queries will always be resolved. Furthermore, since there is no correlation between a peer and the content managed by it, there is no guarantee that flooding will find a peer that has the desired data. Popular content is likely to be available at several peers and any peer searching for it is likely to find the same thing. But if a peer is looking for rare data shared by only a few other peers, then it is highly unlikely that search will be successful.
Structured networks
 In ''structured peer-to-peer networks'' the overlay is organized into a specific topology, and the protocol ensures that any node can efficiently search the network for a file/resource, even if the resource is extremely rare.
The most common type of structured P2P networks implement a distributed hash table (DHT), in which a variant of consistent hashing is used to assign ownership of each file to a particular peer. This enables peers to search for resources on the network using a
In ''structured peer-to-peer networks'' the overlay is organized into a specific topology, and the protocol ensures that any node can efficiently search the network for a file/resource, even if the resource is extremely rare.
The most common type of structured P2P networks implement a distributed hash table (DHT), in which a variant of consistent hashing is used to assign ownership of each file to a particular peer. This enables peers to search for resources on the network using a hash table
In computing, a hash table, also known as hash map, is a data structure that implements an associative array or dictionary. It is an abstract data type that maps keys to values. A hash table uses a hash function to compute an ''index'', ...
: that is, (''key'', ''value'') pairs are stored in the DHT, and any participating node can efficiently retrieve the value associated with a given key.
Storm botnet
The Storm botnet or Storm worm botnet (also known as Dorf botnet and Ecard malware) was a remotely controlled network of "zombie" computers (or "botnet") that had been linked by the Storm Worm, a Trojan horse spread through e-mail spam. At ...
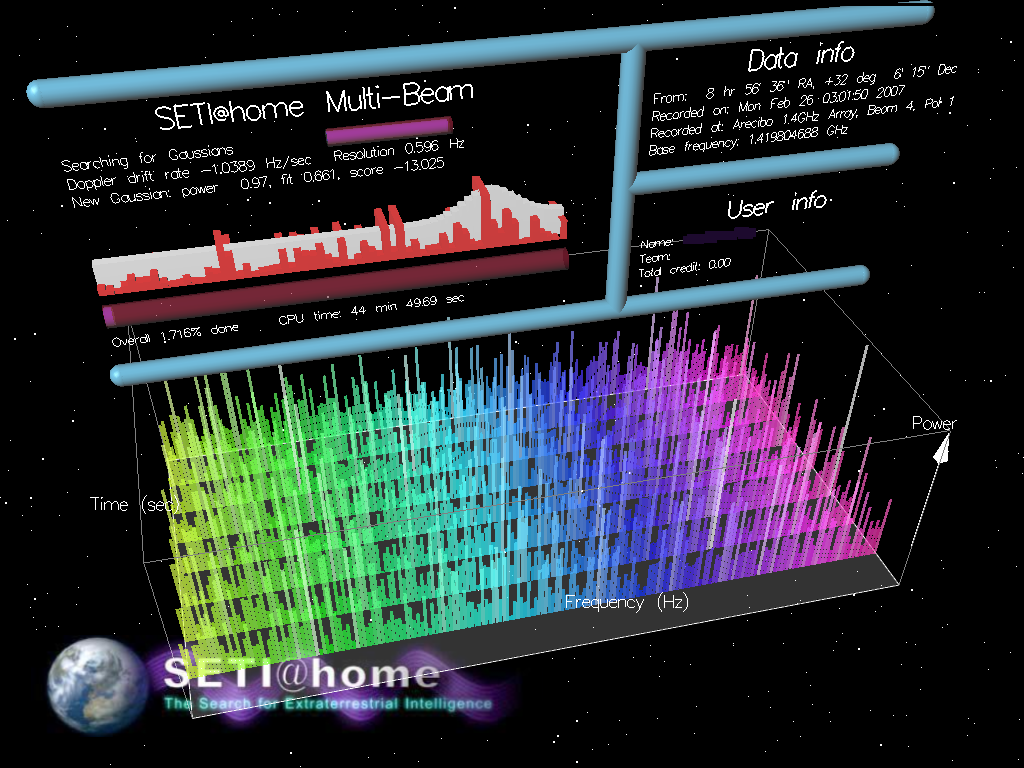
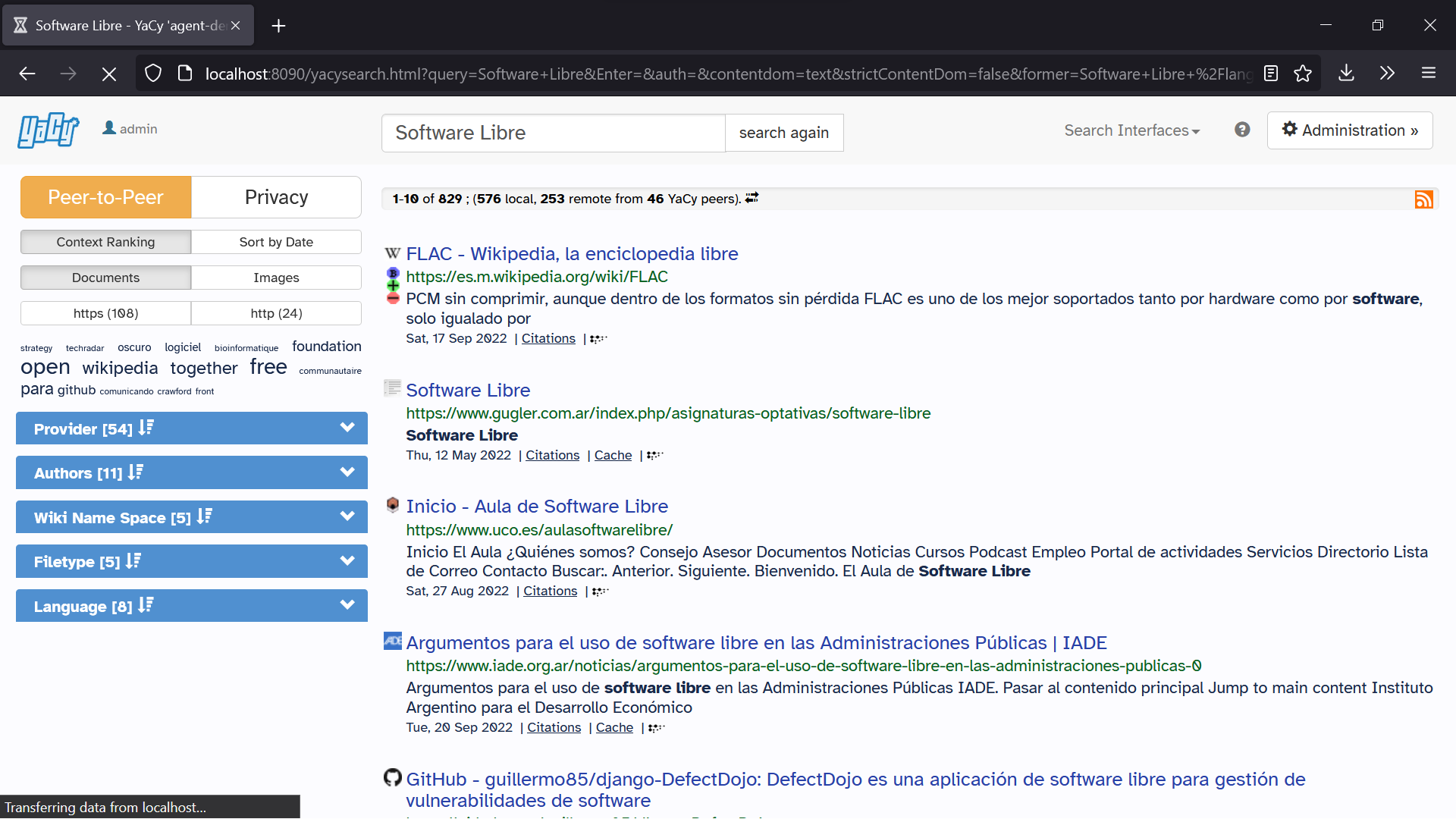
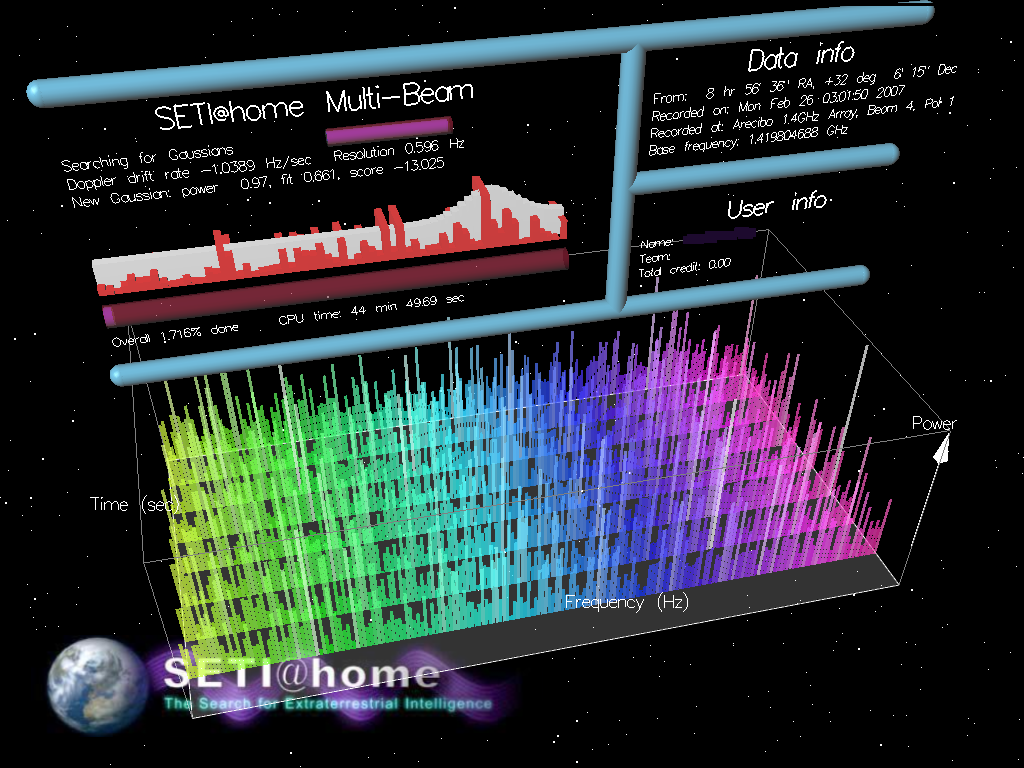
, and the YaCy. Some prominent research projects include the Chord project, Kademlia, PAST storage utility, P-Grid, a self-organized and emerging overlay network, and CoopNet content distribution system. DHT-based networks have also been widely utilized for accomplishing efficient resource discovery for grid computing
Grid computing is the use of widely distributed computer resources to reach a common goal. A computing grid can be thought of as a distributed system with non-interactive workloads that involve many files. Grid computing is distinguished from ...
systems, as it aids in resource management and scheduling of applications.
Hybrid models
Hybrid models are a combination of peer-to-peer and client–server models. A common hybrid model is to have a central server that helps peers find each other.Spotify
Spotify (; ) is a proprietary Swedish audio streaming and media services provider founded on 23 April 2006 by Daniel Ek and Martin Lorentzon. It is one of the largest music streaming service providers, with over 456 million monthly active us ...
was an example of a hybrid model ntil 2014 There are a variety of hybrid models, all of which make trade-offs between the centralized functionality provided by a structured server/client network and the node equality afforded by the pure peer-to-peer unstructured networks. Currently, hybrid models have better performance than either pure unstructured networks or pure structured networks because certain functions, such as searching, do require a centralized functionality but benefit from the decentralized aggregation of nodes provided by unstructured networks.
CoopNet content distribution system
CoopNet (Cooperative Networking) was a proposed system for off-loading serving to peers who have recentlydownload
In computer networks, download means to ''receive'' data from a remote system, typically a server such as a web server, an FTP server, an email server, or other similar system. This contrasts with uploading, where data is ''sent to'' a remo ...
ed content, proposed by computer scientists Venkata N. Padmanabhan and Kunwadee Sripanidkulchai, working at Microsoft Research and Carnegie Mellon University
Carnegie Mellon University (CMU) is a private research university in Pittsburgh, Pennsylvania. One of its predecessors was established in 1900 by Andrew Carnegie as the Carnegie Technical Schools; it became the Carnegie Institute of Technology ...
. When a server experiences an increase in load it redirects incoming peers to other peers who have agreed to mirror
A mirror or looking glass is an object that Reflection (physics), reflects an image. Light that bounces off a mirror will show an image of whatever is in front of it, when focused through the lens of the eye or a camera. Mirrors reverse the ...
the content, thus off-loading balance from the server. All of the information is retained at the server. This system makes use of the fact that the bottle-neck is most likely in the outgoing bandwidth than the CPU
A central processing unit (CPU), also called a central processor, main processor or just processor, is the electronic circuitry that executes instructions comprising a computer program. The CPU performs basic arithmetic, logic, controlling, and ...
, hence its server-centric design. It assigns peers to other peers who are 'close in IP' to its neighbors ame prefix range #REDIRECT AME #REDIRECT AME #REDIRECT AME
{{redirect category shell, {{R from other capitalisation{{R from ambiguous page ...
{{redirect category shell, {{R from other capitalisation{{R from ambiguous page ...
{{redirect category shell, ...Streaming media
Streaming media is multimedia that is delivered and consumed in a continuous manner from a source, with little or no intermediate storage in network elements. ''Streaming'' refers to the delivery method of content, rather than the content i ...
is transmitted by having clients cache the previous stream, and then transmit it piece-wise to new nodes.
Security and trust
Peer-to-peer systems pose unique challenges from acomputer security
Computer security, cybersecurity (cyber security), or information technology security (IT security) is the protection of computer systems and networks from attack by malicious actors that may result in unauthorized information disclosure, t ...
perspective.
Like any other form of software
Software is a set of computer programs and associated software documentation, documentation and data (computing), data. This is in contrast to Computer hardware, hardware, from which the system is built and which actually performs the work.
...
, P2P applications can contain vulnerabilities. What makes this particularly dangerous for P2P software, however, is that peer-to-peer applications act as servers as well as clients, meaning that they can be more vulnerable to remote exploits.
Routing attacks
Since each node plays a role in routing traffic through the network, malicious users can perform a variety of "routing attacks", or denial of service attacks. Examples of common routing attacks include "incorrect lookup routing" whereby malicious nodes deliberately forward requests incorrectly or return false results, "incorrect routing updates" where malicious nodes corrupt the routing tables of neighboring nodes by sending them false information, and "incorrect routing network partition" where when new nodes are joining they bootstrap via a malicious node, which places the new node in a partition of the network that is populated by other malicious nodes.Corrupted data and malware
The prevalence ofmalware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, de ...
varies between different peer-to-peer protocols. Studies analyzing the spread of malware on P2P networks found, for example, that 63% of the answered download requests on the gnutella network contained some form of malware, whereas only 3% of the content on OpenFT contained malware. In both cases, the top three most common types of malware accounted for the large majority of cases (99% in gnutella, and 65% in OpenFT). Another study analyzing traffic on the Kazaa network found that 15% of the 500,000 file sample taken were infected by one or more of the 365 different computer viruses that were tested for.
Corrupted data can also be distributed on P2P networks by modifying files that are already being shared on the network. For example, on the FastTrack network, the RIAA
The Recording Industry Association of America (RIAA) is a trade organization that represents the music recording industry in the United States. Its members consist of record labels and distributors that the RIAA says "create, manufacture, and/ ...
managed to introduce faked chunks into downloads and downloaded files (mostly MP3
MP3 (formally MPEG-1 Audio Layer III or MPEG-2 Audio Layer III) is a coding format for digital audio developed largely by the Fraunhofer Society in Germany, with support from other digital scientists in the United States and elsewhere. Orig ...
files). Files infected with the RIAA virus were unusable afterwards and contained malicious code. The RIAA is also known to have uploaded fake music and movies to P2P networks in order to deter illegal file sharing. Consequently, the P2P networks of today have seen an enormous increase of their security and file verification mechanisms. Modern hashing, chunk verification and different encryption methods have made most networks resistant to almost any type of attack, even when major parts of the respective network have been replaced by faked or nonfunctional hosts.
Resilient and scalable computer networks
The decentralized nature of P2P networks increases robustness because it removes thesingle point of failure
A single point of failure (SPOF) is a part of a system that, if it fails, will stop the entire system from working. SPOFs are undesirable in any system with a goal of high availability or reliability, be it a business practice, software appl ...
that can be inherent in a client–server based system. As nodes arrive and demand on the system increases, the total capacity of the system also increases, and the likelihood of failure decreases. If one peer on the network fails to function properly, the whole network is not compromised or damaged. In contrast, in a typical client–server architecture, clients share only their demands with the system, but not their resources. In this case, as more clients join the system, fewer resources are available to serve each client, and if the central server fails, the entire network is taken down.
Distributed storage and search
 There are both advantages and disadvantages in P2P networks related to the topic of data backup, recovery, and availability. In a centralized network, the system administrators are the only forces controlling the availability of files being shared. If the administrators decide to no longer distribute a file, they simply have to remove it from their servers, and it will no longer be available to users. Along with leaving the users powerless in deciding what is distributed throughout the community, this makes the entire system vulnerable to threats and requests from the government and other large forces. For example,
There are both advantages and disadvantages in P2P networks related to the topic of data backup, recovery, and availability. In a centralized network, the system administrators are the only forces controlling the availability of files being shared. If the administrators decide to no longer distribute a file, they simply have to remove it from their servers, and it will no longer be available to users. Along with leaving the users powerless in deciding what is distributed throughout the community, this makes the entire system vulnerable to threats and requests from the government and other large forces. For example, YouTube
YouTube is a global online video sharing and social media platform headquartered in San Bruno, California. It was launched on February 14, 2005, by Steve Chen, Chad Hurley, and Jawed Karim. It is owned by Google, and is the second most ...
has been pressured by the RIAA
The Recording Industry Association of America (RIAA) is a trade organization that represents the music recording industry in the United States. Its members consist of record labels and distributors that the RIAA says "create, manufacture, and/ ...
, MPAA, and entertainment industry to filter out copyrighted content. Although server-client networks are able to monitor and manage content availability, they can have more stability in the availability of the content they choose to host. A client should not have trouble accessing obscure content that is being shared on a stable centralized network. P2P networks, however, are more unreliable in sharing unpopular files because sharing files in a P2P network requires that at least one node in the network has the requested data, and that node must be able to connect to the node requesting the data. This requirement is occasionally hard to meet because users may delete or stop sharing data at any point.
In this sense, the community of users in a P2P network is completely responsible for deciding what content is available. Unpopular files will eventually disappear and become unavailable as more people stop sharing them. Popular files, however, will be highly and easily distributed. Popular files on a P2P network actually have more stability and availability than files on central networks. In a centralized network, a simple loss of connection between the server and clients is enough to cause a failure, but in P2P networks, the connections between every node must be lost in order to cause a data sharing failure. In a centralized system, the administrators are responsible for all data recovery and backups, while in P2P systems, each node requires its own backup system. Because of the lack of central authority in P2P networks, forces such as the recording industry, RIAA
The Recording Industry Association of America (RIAA) is a trade organization that represents the music recording industry in the United States. Its members consist of record labels and distributors that the RIAA says "create, manufacture, and/ ...
, MPAA, and the government are unable to delete or stop the sharing of content on P2P systems.
Applications
Content delivery
In P2P networks, clients both provide and use resources. This means that unlike client–server systems, the content-serving capacity of peer-to-peer networks can actually ''increase'' as more users begin to access the content (especially with protocols such as Bittorrent that require users to share, refer a performance measurement study). This property is one of the major advantages of using P2P networks because it makes the setup and running costs very small for the original content distributor.File-sharing networks
Manypeer-to-peer file sharing
Peer-to-peer file sharing is the distribution and sharing of digital media using peer-to-peer (P2P) networking technology. P2P file sharing allows users to access media files such as books, music, movies, and games using a P2P software program th ...
networks, such as Gnutella, G2, and the eDonkey network popularized peer-to-peer technologies.
* Peer-to-peer content delivery networks.
* Peer-to-peer content services, e.g. caches for improved performance such as Correli Caches
* Software publication and distribution (Linux distribution
A Linux distribution (often abbreviated as distro) is an operating system made from a software collection that includes the Linux kernel and, often, a package management system. Linux users usually obtain their operating system by downloading on ...
, several games); via file sharing
File sharing is the practice of distributing or providing access to digital media, such as computer programs, multimedia (audio, images and video), documents or electronic books. Common methods of storage, transmission and dispersion include r ...
networks.
Copyright infringements
Peer-to-peer networking involves data transfer from one user to another without using an intermediate server. Companies developing P2P applications have been involved in numerous legal cases, primarily in the United States, over conflicts withcopyright
A copyright is a type of intellectual property that gives its owner the exclusive right to copy, distribute, adapt, display, and perform a creative work, usually for a limited time. The creative work may be in a literary, artistic, education ...
law. Two major cases are '' Grokster vs RIAA'' and ''MGM Studios, Inc. v. Grokster, Ltd.
''MGM Studios, Inc. v. Grokster, Ltd.'', 545 U.S. 913 (2005), is a United States Supreme Court decision in which the Court ruled unanimously that the defendants, peer-to-peer file sharing companies Grokster and Streamcast (maker of Morpheus), cou ...
''. In the last case, the Court unanimously held that defendant peer-to-peer file sharing companies Grokster and Streamcast could be sued for inducing copyright infringement.
Multimedia
* The P2PTV and PDTP protocols. * Some proprietary multimedia applications use a peer-to-peer network along with streaming servers to stream audio and video to their clients. * Peercasting for multicasting streams. *Pennsylvania State University
The Pennsylvania State University (Penn State or PSU) is a public state-related land-grant research university with campuses and facilities throughout Pennsylvania. Founded in 1855 as the Farmers' High School of Pennsylvania, Penn State becam ...
, MIT and Simon Fraser University
Simon Fraser University (SFU) is a public research university in British Columbia, Canada, with three campuses, all in Greater Vancouver: Burnaby (main campus), Surrey, and Vancouver. The main Burnaby campus on Burnaby Mountain, located ...
are carrying on a project called LionShare designed for facilitating file sharing among educational institutions globally.
* Osiris
Osiris (, from Egyptian ''wsjr'', cop, ⲟⲩⲥⲓⲣⲉ , ; Phoenician: 𐤀𐤎𐤓, romanized: ʾsr) is the god of fertility, agriculture, the afterlife, the dead, resurrection, life, and vegetation in ancient Egyptian religion. He ...
is a program that allows its users to create anonymous and autonomous web portals distributed via P2P network.
Other P2P applications
 *
* Bitcoin
Bitcoin ( abbreviation: BTC; sign: ₿) is a decentralized digital currency that can be transferred on the peer-to-peer bitcoin network. Bitcoin transactions are verified by network nodes through cryptography and recorded in a public di ...
and additional such as Ether
In organic chemistry, ethers are a class of compounds that contain an ether group—an oxygen atom connected to two alkyl or aryl groups. They have the general formula , where R and R′ represent the alkyl or aryl groups. Ethers can again b ...
, Nxt and Peercoin are peer-to-peer-based digital cryptocurrencies.
* Dat, a distributed version-controlled publishing platform.
* Filecoin is an open source
Open source is source code that is made freely available for possible modification and redistribution. Products include permission to use the source code, design documents, or content of the product. The open-source model is a decentralized sof ...
, public, cryptocurrency
A cryptocurrency, crypto-currency, or crypto is a digital currency designed to work as a medium of exchange through a computer network that is not reliant on any central authority, such as a government or bank, to uphold or maintain it. It ...
and digital payment system intended to be a blockchain
A blockchain is a type of distributed ledger technology (DLT) that consists of growing lists of records, called ''blocks'', that are securely linked together using cryptography. Each block contains a cryptographic hash of the previous block, ...
-based cooperative digital storage and data retrieval method.
* I2P, an overlay network used to browse the Internet anonymously.
* Unlike the related I2P, the Tor network
Tor, short for The Onion Router, is free and open-source software for enabling anonymous communication. It directs Internet traffic through a free, worldwide, volunteer overlay network, consisting of more than seven thousand relays, to co ...
is not itself peer-to-peer; however, it can enable peer-to-peer applications to be built on top of it via onion services.
* The InterPlanetary File System (IPFS) is a protocol and network designed to create a content-addressable, peer-to-peer method of storing and sharing hypermedia
Hypermedia, an extension of the term hypertext, is a nonlinear medium of information that includes graphics, audio, video, plain text and hyperlinks. This designation contrasts with the broader term ''multimedia'', which may include non-interact ...
distribution protocol. Nodes in the IPFS network form a distributed file system.
* Jami
Nūr ad-Dīn 'Abd ar-Rahmān Jāmī ( fa, نورالدین عبدالرحمن جامی; 7 November 1414 – 9 November 1492), also known as Mawlanā Nūr al-Dīn 'Abd al-Rahmān or Abd-Al-Rahmān Nur-Al-Din Muhammad Dashti, or simply as J ...
, a peer-to-peer chat and SIP app.
* JXTA
JXTA (Juxtapose) was an open-source peer-to-peer protocol specification begun by Sun Microsystems in 2001. The JXTA protocols were defined as a set of XML messages which allow any device connected to a network to exchange messages and collabor ...
, a peer-to-peer protocol designed for the Java platform
Java is a set of computer software and specifications developed by James Gosling at Sun Microsystems, which was later acquired by the Oracle Corporation, that provides a system for developing application software and deploying it in a cro ...
.
* Netsukuku, a Wireless community network designed to be independent from the Internet.
* Open Garden, connection sharing application that shares Internet access with other devices using Wi-Fi or Bluetooth.
* Resilio Sync, a directory-syncing app.
* Research like the Chord project, the PAST storage utility, the P-Grid, and the CoopNet content distribution system.
* Syncthing, a directory-syncing app.
* Tradepal and M-commerce applications that power real-time marketplaces.
* The U.S. Department of Defense is conducting research on P2P networks as part of its modern network warfare strategy. In May, 2003, Anthony Tether, then director of DARPA
The Defense Advanced Research Projects Agency (DARPA) is a research and development agency of the United States Department of Defense responsible for the development of emerging technologies for use by the military.
Originally known as the Ad ...
, testified that the United States military uses P2P networks.
* WebTorrent
WebTorrent is a peer-to-peer (P2P) streaming torrent client written in JavaScript, from the same author, Feross Aboukhadijeh, of YouTube Instant, and the team at WebTorrent and on GitHub, for use in web browsers, as well as a WebTorrent De ...
is a P2P streaming torrent client
The following is a general comparison of BitTorrent clients, which are computer programs designed for peer-to-peer file sharing using the BitTorrent protocol.
The BitTorrent protocol coordinates segmented file transfer among peers connected in ...
in JavaScript
JavaScript (), often abbreviated as JS, is a programming language that is one of the core technologies of the World Wide Web, alongside HTML and CSS. As of 2022, 98% of Website, websites use JavaScript on the Client (computing), client side ...
for use in web browser
A web browser is application software for accessing websites. When a user requests a web page from a particular website, the browser retrieves its files from a web server and then displays the page on the user's screen. Browsers are used on ...
s, as well as in the WebTorrent Desktop stand alone version that bridges WebTorrent and BitTorrent serverless networks.
* Microsoft
Microsoft Corporation is an American multinational corporation, multinational technology company, technology corporation producing Software, computer software, consumer electronics, personal computers, and related services headquartered at th ...
in Windows 10
Windows 10 is a major release of Microsoft's Windows NT operating system. It is the direct successor to Windows 8.1, which was released nearly two years earlier. It was released to manufacturing on July 15, 2015, and later to retail on ...
uses a proprietary peer to peer technology called "Delivery Optimization" to deploy operating system updates using end-users PCs either on the local network or other PCs. According to Microsoft's Channel 9 it led to a 30%-50% reduction in Internet bandwidth usage.
* Artisoft's LANtastic was built as a peer-to-peer operating system. Machines can be both servers and workstations at the same time.
* Hotline Communications
Hotline Communications Limited (HCL) was a software company founded in 1997, based in Toronto, Canada, with employees also in the United States and Australia. Hotline Communications' main activity was the publishing and distribution of a multi-purp ...
Hotline Client was built as decentralized servers with tracker software dedicated to any type of files and still operates today
Social implications
Incentivizing resource sharing and cooperation
 Cooperation among a community of participants is key to the continued success of P2P systems aimed at casual human users; these reach their full potential only when large numbers of nodes contribute resources. But in current practice, P2P networks often contain large numbers of users who utilize resources shared by other nodes, but who do not share anything themselves (often referred to as the "freeloader problem"). Freeloading can have a profound impact on the network and in some cases can cause the community to collapse. In these types of networks "users have natural disincentives to cooperate because cooperation consumes their own resources and may degrade their own performance."Feldman, M., Lai, K., Stoica, I., & Chuang, J. (2004, May). Robust incentive techniques for peer-to-peer networks. In Proceedings of the 5th ACM conference on Electronic commerce (pp. 102-111). ACM. Studying the social attributes of P2P networks is challenging due to large populations of turnover, asymmetry of interest and zero-cost identity. A variety of incentive mechanisms have been implemented to encourage or even force nodes to contribute resources.
Some researchers have explored the benefits of enabling virtual communities to self-organize and introduce incentives for resource sharing and cooperation, arguing that the social aspect missing from today's P2P systems should be seen both as a goal and a means for self-organized virtual communities to be built and fostered. Ongoing research efforts for designing effective incentive mechanisms in P2P systems, based on principles from game theory, are beginning to take on a more psychological and information-processing direction.
Cooperation among a community of participants is key to the continued success of P2P systems aimed at casual human users; these reach their full potential only when large numbers of nodes contribute resources. But in current practice, P2P networks often contain large numbers of users who utilize resources shared by other nodes, but who do not share anything themselves (often referred to as the "freeloader problem"). Freeloading can have a profound impact on the network and in some cases can cause the community to collapse. In these types of networks "users have natural disincentives to cooperate because cooperation consumes their own resources and may degrade their own performance."Feldman, M., Lai, K., Stoica, I., & Chuang, J. (2004, May). Robust incentive techniques for peer-to-peer networks. In Proceedings of the 5th ACM conference on Electronic commerce (pp. 102-111). ACM. Studying the social attributes of P2P networks is challenging due to large populations of turnover, asymmetry of interest and zero-cost identity. A variety of incentive mechanisms have been implemented to encourage or even force nodes to contribute resources.
Some researchers have explored the benefits of enabling virtual communities to self-organize and introduce incentives for resource sharing and cooperation, arguing that the social aspect missing from today's P2P systems should be seen both as a goal and a means for self-organized virtual communities to be built and fostered. Ongoing research efforts for designing effective incentive mechanisms in P2P systems, based on principles from game theory, are beginning to take on a more psychological and information-processing direction.
Privacy and anonymity
Some peer-to-peer networks (e.g. Freenet) place a heavy emphasis onprivacy
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively.
The domain of privacy partially overlaps with security, which can include the concepts of a ...
and anonymity—that is, ensuring that the contents of communications are hidden from eavesdroppers, and that the identities/locations of the participants are concealed. Public key cryptography can be used to provide encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can dec ...
, data validation, authorization, and authentication for data/messages. Onion routing
Onion routing is a technique for anonymous communication over a computer network. In an onion network, messages are encapsulated in layers of encryption, analogous to layers of an onion. The encrypted data is transmitted through a series of net ...
and other mix network protocols (e.g. Tarzan) can be used to provide anonymity.
Perpetrators of live streaming sexual abuse and other cybercrimes have used peer-to-peer platforms to carry out activities with anonymity.
Political implications
Intellectual property law and illegal sharing
Although peer-to-peer networks can be used for legitimate purposes, rights holders have targeted peer-to-peer over the involvement with sharing copyrighted material. Peer-to-peer networking involves data transfer from one user to another without using an intermediate server. Companies developing P2P applications have been involved in numerous legal cases, primarily in the United States, primarily over issues surroundingcopyright
A copyright is a type of intellectual property that gives its owner the exclusive right to copy, distribute, adapt, display, and perform a creative work, usually for a limited time. The creative work may be in a literary, artistic, education ...
law. Two major cases are '' Grokster vs RIAA'' and ''MGM Studios, Inc. v. Grokster, Ltd.
''MGM Studios, Inc. v. Grokster, Ltd.'', 545 U.S. 913 (2005), is a United States Supreme Court decision in which the Court ruled unanimously that the defendants, peer-to-peer file sharing companies Grokster and Streamcast (maker of Morpheus), cou ...
'' In both of the cases the file sharing technology was ruled to be legal as long as the developers had no ability to prevent the sharing of the copyrighted material. To establish criminal liability for the copyright infringement on peer-to-peer systems, the government must prove that the defendant infringed a copyright willingly for the purpose of personal financial gain or commercial advantage. Fair use
Fair use is a doctrine in United States law that permits limited use of copyrighted material without having to first acquire permission from the copyright holder. Fair use is one of the limitations to copyright intended to balance the intere ...
exceptions allow limited use of copyrighted material to be downloaded without acquiring permission from the rights holders. These documents are usually news reporting or under the lines of research and scholarly work. Controversies have developed over the concern of illegitimate use of peer-to-peer networks regarding public safety and national security. When a file is downloaded through a peer-to-peer network, it is impossible to know who created the file or what users are connected to the network at a given time. Trustworthiness of sources is a potential security threat that can be seen with peer-to-peer systems.
A study ordered by the European Union
The European Union (EU) is a supranational political and economic union of member states that are located primarily in Europe. The union has a total area of and an estimated total population of about 447million. The EU has often been ...
found that illegal downloading ''may'' lead to an increase in overall video game sales because newer games charge for extra features or levels. The paper concluded that piracy had a negative financial impact on movies, music, and literature. The study relied on self-reported data about game purchases and use of illegal download sites. Pains were taken to remove effects of false and misremembered responses.
Network neutrality
Peer-to-peer applications present one of the core issues in the network neutrality controversy. Internet service providers ( ISPs) have been known to throttle P2P file-sharing traffic due to its high- bandwidth usage.Janko Roettgers, 5 Ways to Test Whether your ISP throttles P2P, http://newteevee.com/2008/04/02/5-ways-to-test-if-your-isp-throttles-p2p/ Compared to Web browsing, e-mail or many other uses of the internet, where data is only transferred in short intervals and relative small quantities, P2P file-sharing often consists of relatively heavy bandwidth usage due to ongoing file transfers and swarm/network coordination packets. In October 2007,Comcast
Comcast Corporation (formerly known as American Cable Systems and Comcast Holdings),Before the AT&T merger in 2001, the parent company was Comcast Holdings Corporation. Comcast Holdings Corporation now refers to a subsidiary of Comcast Corpora ...
, one of the largest broadband Internet providers in the United States, started blocking P2P applications such as BitTorrent. Their rationale was that P2P is mostly used to share illegal content, and their infrastructure is not designed for continuous, high-bandwidth traffic. Critics point out that P2P networking has legitimate legal uses, and that this is another way that large providers are trying to control use and content on the Internet, and direct people towards a client–server-based application architecture. The client–server model provides financial barriers-to-entry to small publishers and individuals, and can be less efficient for sharing large files. As a reaction to this bandwidth throttling, several P2P applications started implementing protocol obfuscation, such as the BitTorrent protocol encryption. Techniques for achieving "protocol obfuscation" involves removing otherwise easily identifiable properties of protocols, such as deterministic byte sequences and packet sizes, by making the data look as if it were random. The ISP's solution to the high bandwidth is P2P caching, where an ISP stores the part of files most accessed by P2P clients in order to save access to the Internet.
Current research
Researchers have used computer simulations to aid in understanding and evaluating the complex behaviors of individuals within the network. "Networking research often relies on simulation in order to test and evaluate new ideas. An important requirement of this process is that results must be reproducible so that other researchers can replicate, validate, and extend existing work."Basu, A., Fleming, S., Stanier, J., Naicken, S., Wakeman, I., & Gurbani, V. K. (2013). The state of peer-to-peer network simulators. ACM Computing Surveys, 45(4), 46. If the research cannot be reproduced, then the opportunity for further research is hindered. "Even though new simulators continue to be released, the research community tends towards only a handful of open-source simulators. The demand for features in simulators, as shown by our criteria and survey, is high. Therefore, the community should work together to get these features in open-source software. This would reduce the need for custom simulators, and hence increase repeatability and reputability of experiments." Besides all the above stated facts, there has also been work done on ns-2 open source network simulators. One research issue related to free rider detection and punishment has been explored using ns-2 simulator here.A Bhakuni, P Sharma, R Kausha"Free-rider detection and punishment in BitTorrent based P2P networks"
International Advanced Computing Conference, 2014.
See also
References
External links
* Ghosh Debjani, Rajan Payas, Pandey MayanP2P-VoD Streaming: Design Issues & User Experience Challenges
Springer Proceedings, June 2014
of P2P terminology
Foundation of Peer-to-Peer Computing
Special Issue, Elsevier Journal of Computer Communication, (Ed) Javed I. Khan and Adam Wierzbicki, Volume 31, Issue 2, February 2008 * * Marling Engle & J. I. Khan
Vulnerabilities of P2P systems and a critical look at their solutions
May 2006 * Stephanos Androutsellis-Theotokis and Diomidis Spinellis
ACM Computing Surveys, 36(4):335–371, December 2004. * Biddle, Peter, Paul England, Marcus Peinado, and Bryan Willman
The Darknet and the Future of Content Distribution
In ''2002 ACM Workshop on Digital Rights Management'', November 2002. * John F. Buford, Heather Yu, Eng Keong Lu
P2P Networking and Applications
, Morgan Kaufmann, December 2008 * Djamal-Eddine Meddour, Mubashar Mushtaq, and Toufik Ahmed,
Open Issues in P2P Multimedia Streaming
, in the proceedings of the 1st Multimedia Communications Workshop MULTICOMM 2006 held in conjunction with IEEE ICC 2006 pp 43–48, June 2006, Istanbul, Turkey. * Detlef Schoder and Kai Fischbach,
Core Concepts in Peer-to-Peer (P2P) Networking
. In: Subramanian, R.; Goodman, B. (eds.): ''P2P Computing: The Evolution of a Disruptive Technology'', Idea Group Inc, Hershey. 2005 * Ramesh Subramanian and Brian Goodman (eds),
Peer-to-Peer Computing: Evolution of a Disruptive Technology
', , Idea Group Inc., Hershey, PA, United States, 2005. *
Shuman Ghosemajumder
Shuman Ghosemajumder (born 1974) is a Canadian technologist, entrepreneur, and author. He is the former click fraud czar at Google, the author of works on technology and business including the Open Music Model, and co-founder of TeachAids. He w ...
Advanced Peer-Based Technology Business Models
MIT Sloan School of Management
The MIT Sloan School of Management (MIT Sloan or Sloan) is the business school of the Massachusetts Institute of Technology, a private university in Cambridge, Massachusetts.
MIT Sloan offers bachelor's, master's, and doctoral degree programs, a ...
, 2002.
* Silverthorne, Sean. Music Downloads: Pirates- or Customers?
'. Harvard Business School Working Knowledge, 2004.
Glasnost
test P2P traffic shaping ( Max Planck Institute for Software Systems) {{DEFAULTSORT:Peer-To-Peer File sharing networks File sharing Software engineering terminology