Freenet Project on:
[Wikipedia]
[Google]
[Amazon]
Freenet is a
, ''Freenet: The Free network official website''.Taylor, Ian J. ''From P2P to Web Services and Grids: Peers in a Client/Server World''. London: Springer, 2005. Both Freenet and some of its associated tools were originally designed by Ian Clarke, who defined Freenet's goal as providing
The Guardian writes about Freenet (Ian Clarke's response)Archived at WebCite
/ref> The distributed data store of Freenet is used by many third-party programs and plugins to provide microblogging and media sharing,, German article, 2010 anonymous and decentralised version tracking, blogging, a generic web of trust for decentralized spam resistance, Shoeshop for using Freenet over sneakernet, and many more.
Freenet: A Distributed Anonymous Information Storage and Retrieval System
. In: Proceedings of the International Workshop on Designing Privacy Enhancing Technologies: Design Issues in Anonymity and Unobservability. New York, NY: Springer-Verlag, 2001, p. 46-66. According to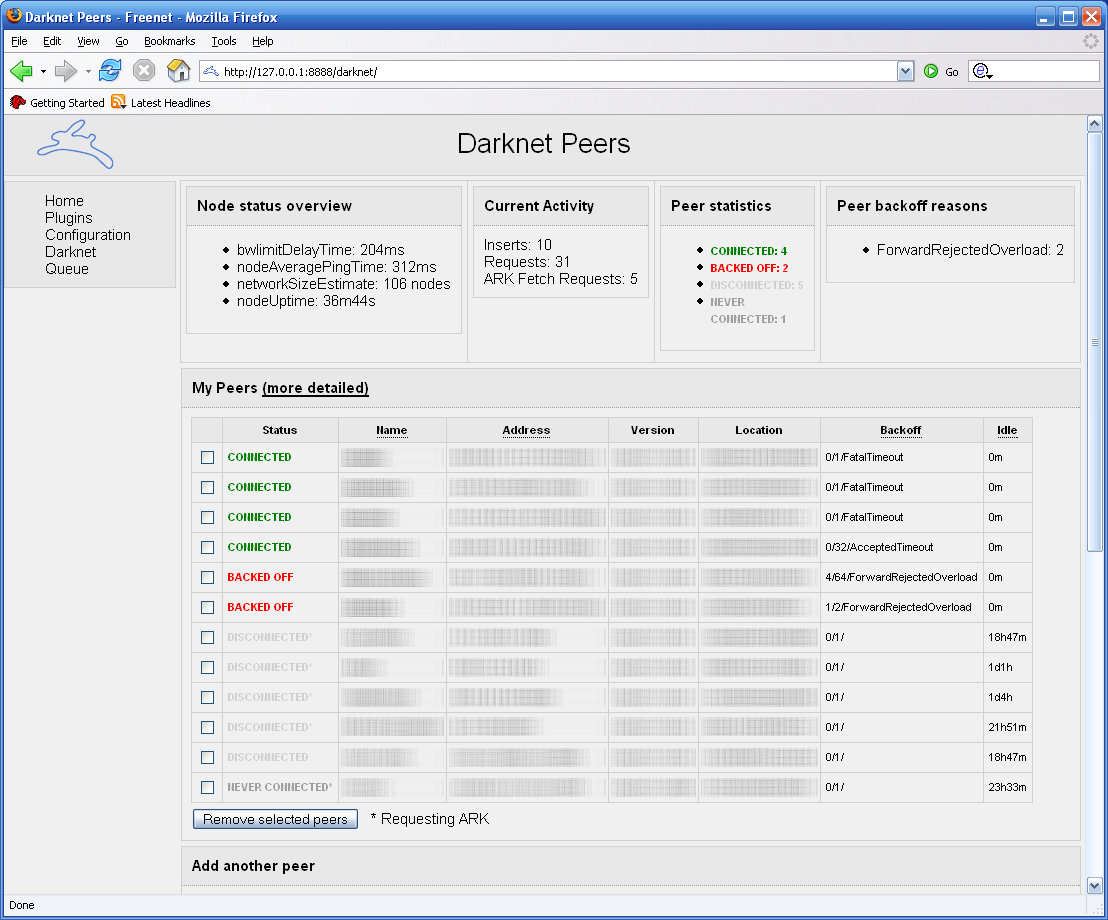 Freenet has been under continuous development since 2000.
Freenet 0.7, released on 8 May 2008, is a major re-write incorporating a number of fundamental changes. The most fundamental change is support for
Freenet has been under continuous development since 2000.
Freenet 0.7, released on 8 May 2008, is a major re-write incorporating a number of fundamental changes. The most fundamental change is support for
, 11 February 2015.recording of the SUMA Award Ceremony 2015
, published on 14 April 2015.
Jo Bager in Heise online, 2015
 The Freenet protocol uses a
The Freenet protocol uses a
 Initially, the locations in darknet are distributed randomly. This means that routing of requests is essentially random. In opennet connections are established by a join request which provides an optimized network structure if the existing network is already optimized. So the data in a newly started Freenet will be distributed somewhat randomly.
As location swapping (on darknet) and path folding (on opennet) progress, nodes which are close to one another will increasingly have close locations, and nodes which are far away will have distant locations. Data with similar keys will be stored on the same node.
The result is that the network will self-organize into a distributed, clustered structure where nodes tend to hold data items that are close together in key space. There will probably be multiple such clusters throughout the network, any given document being replicated numerous times, depending on how much it is used. This is a kind of " spontaneous symmetry breaking", in which an initially symmetric state (all nodes being the same, with random initial keys for each other) leads to a highly asymmetric situation, with nodes coming to specialize in data that has closely related keys.
There are forces which tend to cause clustering (shared closeness data spreads throughout the network), and forces that tend to break up clusters (local caching of commonly used data). These forces will be different depending on how often data is used, so that seldom-used data will tend to be on just a few nodes which specialize in providing that data, and frequently used items will be spread widely throughout the network. This automatic mirroring counteracts the times when
Initially, the locations in darknet are distributed randomly. This means that routing of requests is essentially random. In opennet connections are established by a join request which provides an optimized network structure if the existing network is already optimized. So the data in a newly started Freenet will be distributed somewhat randomly.
As location swapping (on darknet) and path folding (on opennet) progress, nodes which are close to one another will increasingly have close locations, and nodes which are far away will have distant locations. Data with similar keys will be stored on the same node.
The result is that the network will self-organize into a distributed, clustered structure where nodes tend to hold data items that are close together in key space. There will probably be multiple such clusters throughout the network, any given document being replicated numerous times, depending on how much it is used. This is a kind of " spontaneous symmetry breaking", in which an initially symmetric state (all nodes being the same, with random initial keys for each other) leads to a highly asymmetric situation, with nodes coming to specialize in data that has closely related keys.
There are forces which tend to cause clustering (shared closeness data spreads throughout the network), and forces that tend to break up clusters (local caching of commonly used data). These forces will be different depending on how often data is used, so that seldom-used data will tend to be on just a few nodes which specialize in providing that data, and frequently used items will be spread widely throughout the network. This automatic mirroring counteracts the times when
 Unlike many other P2P applications Freenet does not provide comprehensive functionality itself. Freenet is modular and features an
Unlike many other P2P applications Freenet does not provide comprehensive functionality itself. Freenet is modular and features an
The dark side of the internet
Andy Beckett in ''The Guardian'' 2009 and elsewhere.
Freenet received the SUMA-Award 2014 for "protection against total surveillance".
peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network. They are said to form a peer-to-peer n ...
platform for censorship
Censorship is the suppression of speech, public communication, or other information. This may be done on the basis that such material is considered objectionable, harmful, sensitive, or "inconvenient". Censorship can be conducted by governments ...
-resistant, anonymous
Anonymous may refer to:
* Anonymity, the state of an individual's identity, or personally identifiable information, being publicly unknown
** Anonymous work, a work of art or literature that has an unnamed or unknown creator or author
* Anonym ...
communication. It uses a decentralized distributed data store to keep and deliver information, and has a suite of free software
Free software or libre software is computer software distributed under terms that allow users to run the software for any purpose as well as to study, change, and distribute it and any adapted versions. Free software is a matter of liberty, no ...
for publishing and communicating on the Web without fear of censorship.What is Freenet?, ''Freenet: The Free network official website''.Taylor, Ian J. ''From P2P to Web Services and Grids: Peers in a Client/Server World''. London: Springer, 2005. Both Freenet and some of its associated tools were originally designed by Ian Clarke, who defined Freenet's goal as providing
freedom of speech
Freedom of speech is a principle that supports the freedom of an individual or a community to articulate their opinions and ideas without fear of retaliation, censorship, or legal sanction. The right to freedom of expression has been recogni ...
on the Internet with strong anonymity protection.The Guardian writes about Freenet (Ian Clarke's response)
/ref> The distributed data store of Freenet is used by many third-party programs and plugins to provide microblogging and media sharing,, German article, 2010 anonymous and decentralised version tracking, blogging, a generic web of trust for decentralized spam resistance, Shoeshop for using Freenet over sneakernet, and many more.
History
The origin of Freenet can be traced to Ian Clarke's student project at theUniversity of Edinburgh
The University of Edinburgh ( sco, University o Edinburgh, gd, Oilthigh Dhùn Èideann; abbreviated as ''Edin.'' in post-nominals) is a public research university based in Edinburgh, Scotland. Granted a royal charter by King James VI in 15 ...
, which he completed as a graduation requirement in the summer of 1999. Ian Clarke's resulting unpublished report "A distributed decentralized information storage and retrieval system" (1999) provided foundation for the seminal paper written in collaboration with other researchers, "Freenet: A Distributed Anonymous Information Storage and Retrieval System" (2001).Ian Clarke, Oskar Sandberg, Brandon Wiley, and Theodore W. HongFreenet: A Distributed Anonymous Information Storage and Retrieval System
. In: Proceedings of the International Workshop on Designing Privacy Enhancing Technologies: Design Issues in Anonymity and Unobservability. New York, NY: Springer-Verlag, 2001, p. 46-66. According to
CiteSeer
CiteSeerX (formerly called CiteSeer) is a public search engine and digital library for scientific and academic papers, primarily in the fields of computer and information science.
CiteSeer's goal is to improve the dissemination and access of ac ...
, it became one of the most frequently cited computer science
Computer science is the study of computation, automation, and information. Computer science spans theoretical disciplines (such as algorithms, theory of computation, information theory, and automation) to Applied science, practical discipli ...
articles in 2002.
Freenet can provide anonymity on the Internet by storing small encrypted snippets of content distributed on the computers of its users and connecting only through intermediate computers which pass on requests for content and sending them back without knowing the contents of the full file. This is similar to how routers on the Internet route packets without knowing anything about files —except Freenet has caching, a layer of strong encryption, and no reliance on centralized structures. This allows users to publish anonymously or retrieve various kinds of information.
 Freenet has been under continuous development since 2000.
Freenet 0.7, released on 8 May 2008, is a major re-write incorporating a number of fundamental changes. The most fundamental change is support for
Freenet has been under continuous development since 2000.
Freenet 0.7, released on 8 May 2008, is a major re-write incorporating a number of fundamental changes. The most fundamental change is support for darknet
A dark net or darknet is an overlay network within the Internet that can only be accessed with specific software, configurations, or authorization, and often uses a unique customized communication protocol. Two typical darknet types are social ne ...
operation. Version 0.7 offered two modes of operation: a mode in which it connects only to friends, and an opennet-mode in which it connects to any other Freenet user. Both modes can be run simultaneously. When a user switches to pure darknet operation, Freenet becomes very difficult to detect from the outside. The transport layer
In computer networking, the transport layer is a conceptual division of methods in the layered architecture of protocols in the network stack in the Internet protocol suite and the OSI model. The protocols of this layer provide end-to-end ...
created for the darknet mode allows communication over restricted routes as commonly found in mesh networks, as long as these connections follow a small-world structure. Other modifications include switching from TCP
TCP may refer to:
Science and technology
* Transformer coupled plasma
* Tool Center Point, see Robot end effector
Computing
* Transmission Control Protocol, a fundamental Internet standard
* Telephony control protocol, a Bluetooth communication s ...
to UDP, which allows UDP hole punching
UDP hole punching is a commonly used technique employed in network address translation (NAT) applications for maintaining User Datagram Protocol (UDP) packet streams that traverse the NAT. NAT traversal techniques are typically required for clie ...
along with faster transmission of messages between peers in the network.
Freenet 0.7.5, released on 12 June 2009, offers a variety of improvements over 0.7. These include reduced memory usage, faster insert and retrieval of content, significant improvements to the FProxy web interface used for browsing freesites, and a large number of smaller bugfixes, performance enhancements, and usability improvements. Version 0.7.5 also shipped with a new version of the Windows installer.
As of build 1226, released on 30 July 2009, features that have been written include significant security improvements against both attackers acting on the network and physical seizure of the computer running the node.
As of build 1468, released on 11 July 2015, the Freenet core stopped using the db4o
db4o (database for objects) was an embeddable open-source object database for Java and .NET developers. It was developed, commercially licensed and supported by Actian. In October 2014, Actian declined to continue to actively pursue and promote ...
database and laid the foundation for an efficient interface to the Web of Trust plugin which provides spam resistance.
Freenet has always been free software, but until 2011 it required users to install Java
Java (; id, Jawa, ; jv, ꦗꦮ; su, ) is one of the Greater Sunda Islands in Indonesia. It is bordered by the Indian Ocean to the south and the Java Sea to the north. With a population of 151.6 million people, Java is the world's List ...
. This problem was solved by making Freenet compatible with OpenJDK, a free and open source implementation of the Java Platform.
On 11 February 2015, Freenet received the SUMA-Award for "protection against total surveillance".SUMA Award, 11 February 2015.recording of the SUMA Award Ceremony 2015
, published on 14 April 2015.
Jo Bager in Heise online, 2015
Features and user interface
Freenet served as the model for the Japanese peer to peer file-sharing programs Winny, Share andPerfect Dark
''Perfect Dark'' is a first-person shooter developed and published by Rare for the Nintendo 64 video game console in 2000. The first game of the ''Perfect Dark'' series, it follows Joanna Dark, an agent of the Carrington Institute research c ...
, but this model differs from p2p networks such as Bittorrent and emule
eMule is a free peer-to-peer file sharing application for Microsoft Windows. Started in May 2002 as an alternative to eDonkey2000, eMule now connects to both the eDonkey network and the Kad network. The distinguishing features of eMule are ...
. Freenet separates the underlying network structure and protocol from how users interact with the network; as a result, there are a variety of ways to access content on the Freenet network. The simplest is via FProxy, which is integrated with the node software and provides a web interface to content on the network. Using FProxy, a user can browse freesites (websites that use normal HTML
The HyperText Markup Language or HTML is the standard markup language for documents designed to be displayed in a web browser. It can be assisted by technologies such as Cascading Style Sheets (CSS) and scripting languages such as JavaScri ...
and related tools, but whose content is stored within Freenet rather than on a traditional web server). The web interface is also used for most configuration and node management tasks. Through the use of separate applications or plugins loaded into the node software, users can interact with the network in other ways, such as forums similar to web forums or Usenet or interfaces more similar to traditional P2P "filesharing" interfaces.
While Freenet provides an HTTP
The Hypertext Transfer Protocol (HTTP) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web, ...
interface for browsing freesites, it is not a proxy
Proxy may refer to:
* Proxy or agent (law), a substitute authorized to act for another entity or a document which authorizes the agent so to act
* Proxy (climate), a measured variable used to infer the value of a variable of interest in climate re ...
for the World Wide Web
The World Wide Web (WWW), commonly known as the Web, is an information system enabling documents and other web resources to be accessed over the Internet.
Documents and downloadable media are made available to the network through web se ...
; Freenet can be used to access only the content that has been previously inserted into the Freenet network. In this way, it is more similar to Tor's onion services than to anonymous proxy software like Tor's proxy.
Freenet's focus lies on free speech
Freedom of speech is a principle that supports the freedom of an individual or a community to articulate their opinions and ideas without fear of retaliation, censorship, or legal sanction. The rights, right to freedom of expression has been ...
and anonymity. Because of that, Freenet acts differently at certain points that are (directly or indirectly) related to the anonymity part. Freenet attempts to protect the anonymity of both people inserting data into the network (uploading) and those retrieving data from the network (downloading). Unlike file sharing systems, there is no need for the uploader to remain on the network after uploading a file or group of files. Instead, during the upload process, the files are broken into chunks and stored on a variety of other computers on the network. When downloading, those chunks are found and reassembled. Every node on the Freenet network contributes storage space to hold files and bandwidth that it uses to route requests from its peers.
As a direct result of the anonymity requirements, the node requesting content does not normally connect directly to the node that has it; instead, the request is routed across several intermediaries, none of which know which node made the request or which one had it. As a result, the total bandwidth required by the network to transfer a file is higher than in other systems, which can result in slower transfers, especially for infrequently accessed content.
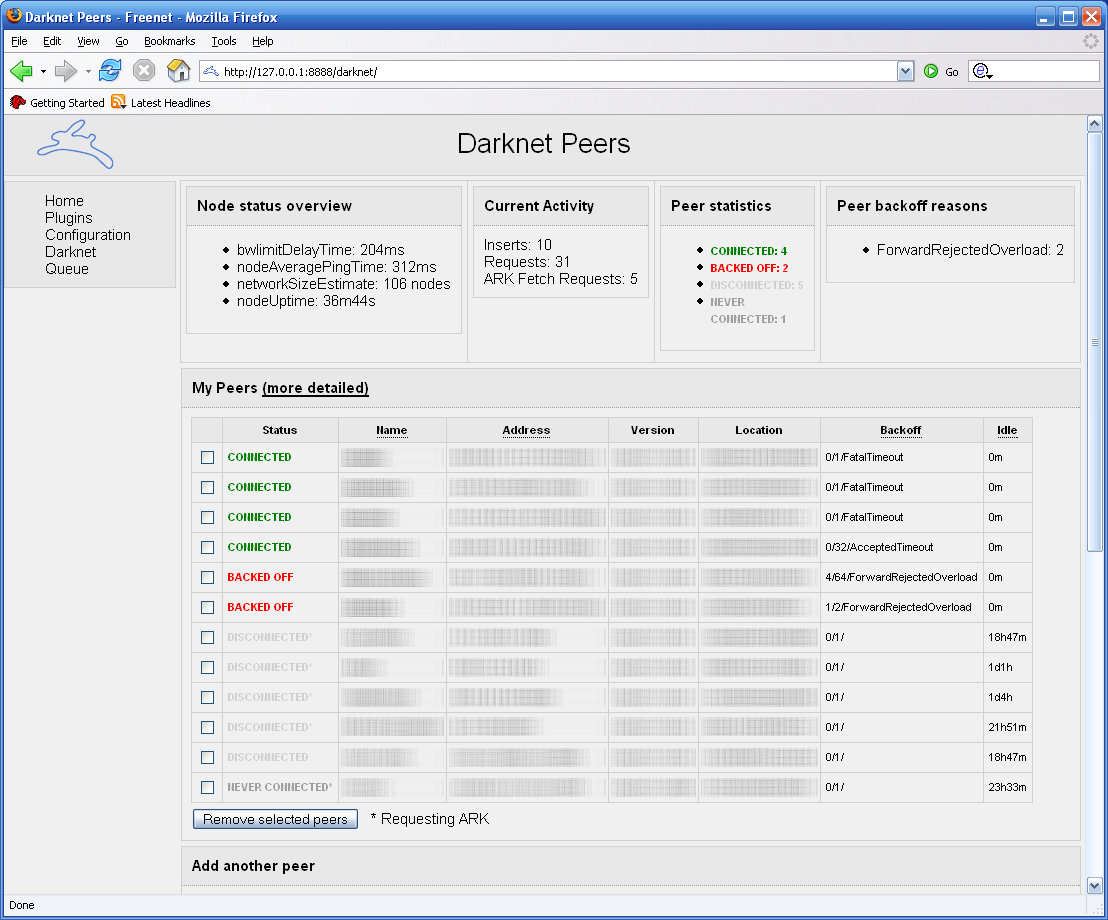
Since version 0.7, Freenet offers two different levels of security: opennet and darknet. With opennet, users connect to arbitrary other users. With darknet, users connect only to "friends" with whom they previously exchanged public keys, named node-references. Both modes can be used together.
Content
Freenet's founders argue that true freedom of speech comes only with true anonymity and that the beneficial uses of Freenet outweigh its negative uses. Their view is that free speech, in itself, is not in contradiction with any other consideration—the information is not the crime. Freenet attempts to remove the possibility of any group imposing its beliefs or values on any data. Although many states censor communications to different extents, they all share one commonality in that a body must decide what information to censor and what information to allow. What may be acceptable to one group of people may be considered offensive or even dangerous to another. In essence, the purpose of Freenet is to ensure that no one is allowed to decide what is acceptable. Reports of Freenet's use in authoritarian nations is difficult to track due to the very nature of Freenet's goals. One group, ''Freenet China'', used to introduce the Freenet software toChinese
Chinese can refer to:
* Something related to China
* Chinese people, people of Chinese nationality, citizenship, and/or ethnicity
**''Zhonghua minzu'', the supra-ethnic concept of the Chinese nation
** List of ethnic groups in China, people of va ...
users starting from 2001 and distribute it within China through e-mails and on disks after the group's website was blocked by the Chinese authorities on the mainland. It was reported that in 2002 ''Freenet China'' had several thousand dedicated users. However, Freenet opennet traffic was blocked in China around the 2010s.
Technical design
The Freenet file sharing network stores documents and allows them to be retrieved later by an associated key, as is now possible with protocols such asHTTP
The Hypertext Transfer Protocol (HTTP) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web, ...
. The network is designed to be highly survivable. The system has no central servers and is not subject to the control of any one individual or organization, including the designers of Freenet. The codebase size is over 192.000 lines of code. Information stored on Freenet is distributed around the network and stored on several different nodes. Encryption of data and relaying of requests makes it difficult to determine who inserted content into Freenet, who requested that content, or where the content was stored. This protects the anonymity of participants, and also makes it very difficult to censor specific content. Content is stored encrypted, making it difficult for even the operator of a node to determine what is stored on that node. This provides plausible deniability
Plausible deniability is the ability of people, typically senior officials in a formal or informal chain of command, to denial, deny knowledge of or responsibility for any damnable actions committed by members of their organizational hierarchy. Th ...
; which, in combination with request relaying, means that safe harbor
A safe harbor or harbour is literally a "place of shelter and safety, esp. for ships". It is used in many contexts:
Film and television
* Safe harbor (broadcasting), established in 1978 in the US, the time period in a television schedule during wh ...
laws that protect service providers may also protect Freenet node operators. When asked about the topic, Freenet developers defer to the EFF discussion which says that not being able to filter anything is a safe choice.
Distributed storage and caching of data
Like Winny, Share andPerfect Dark
''Perfect Dark'' is a first-person shooter developed and published by Rare for the Nintendo 64 video game console in 2000. The first game of the ''Perfect Dark'' series, it follows Joanna Dark, an agent of the Carrington Institute research c ...
, Freenet not only transmits data between nodes but actually stores them, working as a huge distributed cache. To achieve this, each node allocates some amount of disk space to store data; this is configurable by the node operator, but is typically several GB (or more).
Files on Freenet are typically split into multiple small blocks, with duplicate blocks created to provide redundancy. Each block is handled independently, meaning that a single file may have parts stored on many different nodes.
Information flow in Freenet is different from networks like eMule
eMule is a free peer-to-peer file sharing application for Microsoft Windows. Started in May 2002 as an alternative to eDonkey2000, eMule now connects to both the eDonkey network and the Kad network. The distinguishing features of eMule are ...
or BitTorrent; in Freenet:
# A user wishing to share a file or update a freesite "inserts" the file "to the network"
# After "insertion" is finished, the publishing node is free to shut down, because the file is stored in the network. It will remain available for other users whether or not the original publishing node is online. No single node is responsible for the content; instead, it is replicated to many different nodes.
Two advantages of this design are high reliability and anonymity. Information remains available even if the publisher node goes offline, and is anonymously spread over many hosting nodes as encrypted blocks, not entire files.
The key disadvantage of the storage method is that no one node is responsible for any chunk of data. If a piece of data is not retrieved for some time and a node keeps getting new data, it will drop the old data sometime when its allocated disk space is fully used. In this way Freenet tends to 'forget' data which is not retrieved regularly (see also Effect
Effect may refer to:
* A result or change of something
** List of effects
** Cause and effect, an idiom describing causality
Pharmacy and pharmacology
* Drug effect, a change resulting from the administration of a drug
** Therapeutic effect, a ...
).
While users can insert data into the network, there is no way to delete data. Due to Freenet's anonymous nature the original publishing node or owner of any piece of data is unknown. The only way data can be removed is if users don't request it.
Network
Typically, a host computer on the network runs the software that acts as a node, and it connects to other hosts running that same software to form a large distributed, variable-size network of peer nodes. Some nodes are end user nodes, from which documents are requested and presented to human users. Other nodes serve only to route data. All nodes communicate with each other identically – there are no dedicated "clients" or "servers". It is not possible for a node to rate another node except by its capacity to insert and fetch data associated with a key. This is unlike most other P2P networks where node administrators can employ a ratio system, where users have to share a certain amount of content before they can download. Freenet may also be considered asmall world network
A small-world network is a type of mathematical graph in which most nodes are not neighbors of one another, but the neighbors of any given node are likely to be neighbors of each other and most nodes can be reached from every other node by a sm ...
.
The Freenet protocol is intended to be used on a network of complex topology, such as the Internet (Internet Protocol
The Internet Protocol (IP) is the network layer communications protocol in the Internet protocol suite for relaying datagrams across network boundaries. Its routing function enables internetworking, and essentially establishes the Internet.
IP h ...
). Each node knows only about some number of other nodes that it can reach directly (its conceptual "neighbors"), but any node can be a neighbor to any other; no hierarchy or other structure is intended. Each message is routed through the network by passing from neighbor to neighbor until it reaches its destination. As each node passes a message to a neighbor, it does not know whether the neighbor will forward the message to another node, or is the final destination or original source of the message. This is intended to protect the anonymity of users and publishers.
Each node maintains a data store containing documents associated with keys, and a routing table associating nodes with records of their performance in retrieving different keys.
Protocol
key-based routing
Key-based routing (KBR) is a lookup method used in conjunction with distributed hash tables (DHTs) and certain other overlay networks. While DHTs provide a method to find a host responsible for a certain piece of data, KBR provides a method to fi ...
protocol, similar to distributed hash tables. The routing algorithm changed significantly in version 0.7. Prior to version 0.7, Freenet used a heuristic routing algorithm where each node had no fixed location, and routing was based on which node had served a key closest to the key being fetched (in version 0.3) or which is estimated to serve it faster (in version 0.5). In either case, new connections were sometimes added to downstream nodes (i.e. the node that answered the request) when requests succeeded, and old nodes were discarded in least recently used order (or something close to it). Oskar Sandberg's research (during the development of version 0.7) shows that this "path folding" is critical, and that a very simple routing algorithm will suffice provided there is path folding.
The disadvantage of this is that it is very easy for an attacker to find Freenet nodes, and connect to them, because every node is continually attempting to find new connections. In version 0.7, Freenet supports both "opennet" (similar to the old algorithms, but simpler), and "darknet" (all node connections are set up manually, so only your friends know your node's IP address). Darknet is less convenient, but much more secure against a distant attacker.
This change required major changes in the routing algorithm. Every node has a location, which is a number between 0 and 1. When a key is requested, first the node checks the local data store. If it's not found, the key's hash is turned into another number in the same range, and the request is routed to the node whose location is closest to the key. This goes on until some number of hops is exceeded, there are no more nodes to search, or the data is found. If the data is found, it is cached on each node along the path. So there is no one source node for a key, and attempting to find where it is currently stored will result in it being cached more widely. Essentially the same process is used to insert a document into the network: the data is routed according to the key until it runs out of hops, and if no existing document is found with the same key, it is stored on each node. If older data is found, the older data is propagated and returned to the originator, and the insert "collides".
But this works only if the locations are clustered in the right way. Freenet assumes that the darknet (a subset of the global social network) is a small-world network, and nodes constantly attempt to swap locations (using the Metropolis–Hastings algorithm
In statistics and statistical physics, the Metropolis–Hastings algorithm is a Markov chain Monte Carlo (MCMC) method for obtaining a sequence of random samples from a probability distribution from which direct sampling is difficult. This seque ...
) in order to minimize their distance to their neighbors. If the network actually is a small-world network, Freenet should find data reasonably quickly; ideally on the order of hops in Big O notation
Big ''O'' notation is a mathematical notation that describes the limiting behavior of a function when the argument tends towards a particular value or infinity. Big O is a member of a family of notations invented by Paul Bachmann, Edmund Lan ...
. However, it does not guarantee that data will be found at all.
Eventually, either the document is found or the hop limit is exceeded. The terminal node sends a reply that makes its way back to the originator along the route specified by the intermediate nodes' records of pending requests. The intermediate nodes may choose to cache the document along the way. Besides saving bandwidth, this also makes documents harder to censor as there is no one "source node".
Effect
 Initially, the locations in darknet are distributed randomly. This means that routing of requests is essentially random. In opennet connections are established by a join request which provides an optimized network structure if the existing network is already optimized. So the data in a newly started Freenet will be distributed somewhat randomly.
As location swapping (on darknet) and path folding (on opennet) progress, nodes which are close to one another will increasingly have close locations, and nodes which are far away will have distant locations. Data with similar keys will be stored on the same node.
The result is that the network will self-organize into a distributed, clustered structure where nodes tend to hold data items that are close together in key space. There will probably be multiple such clusters throughout the network, any given document being replicated numerous times, depending on how much it is used. This is a kind of " spontaneous symmetry breaking", in which an initially symmetric state (all nodes being the same, with random initial keys for each other) leads to a highly asymmetric situation, with nodes coming to specialize in data that has closely related keys.
There are forces which tend to cause clustering (shared closeness data spreads throughout the network), and forces that tend to break up clusters (local caching of commonly used data). These forces will be different depending on how often data is used, so that seldom-used data will tend to be on just a few nodes which specialize in providing that data, and frequently used items will be spread widely throughout the network. This automatic mirroring counteracts the times when
Initially, the locations in darknet are distributed randomly. This means that routing of requests is essentially random. In opennet connections are established by a join request which provides an optimized network structure if the existing network is already optimized. So the data in a newly started Freenet will be distributed somewhat randomly.
As location swapping (on darknet) and path folding (on opennet) progress, nodes which are close to one another will increasingly have close locations, and nodes which are far away will have distant locations. Data with similar keys will be stored on the same node.
The result is that the network will self-organize into a distributed, clustered structure where nodes tend to hold data items that are close together in key space. There will probably be multiple such clusters throughout the network, any given document being replicated numerous times, depending on how much it is used. This is a kind of " spontaneous symmetry breaking", in which an initially symmetric state (all nodes being the same, with random initial keys for each other) leads to a highly asymmetric situation, with nodes coming to specialize in data that has closely related keys.
There are forces which tend to cause clustering (shared closeness data spreads throughout the network), and forces that tend to break up clusters (local caching of commonly used data). These forces will be different depending on how often data is used, so that seldom-used data will tend to be on just a few nodes which specialize in providing that data, and frequently used items will be spread widely throughout the network. This automatic mirroring counteracts the times when web traffic
Web traffic is the data sent and received by visitors to a website. Since the mid-1990s, web traffic has been the largest portion of Internet traffic. Sites monitor the incoming and outgoing traffic to see which parts or pages of their site are ...
becomes overloaded, and due to a mature network's intelligent routing, a network of size ''n'' should require only log(''n'') time to retrieve a document on average.
Keys
Keys are hashes: there is no notion of semantic closeness when speaking of key closeness. Therefore, there will be no correlation between key closeness and similar popularity of data as there might be if keys did exhibit some semantic meaning, thus avoiding bottlenecks caused by popular subjects. There are two main varieties of keys in use on Freenet, the Content Hash Key (CHK) and the Signed Subspace Key (SSK). A subtype of SSKs is the Updatable Subspace Key (USK) which adds versioning to allow secure updating of content. A CHK is a SHA-256 hash of a document (after encryption, which itself depends on the hash of the plaintext) and thus a node can check that the document returned is correct by hashing it and checking the digest against the key. This key contains the meat of the data on Freenet. It carries all the binary data building blocks for the content to be delivered to the client for reassembly and decryption. The CHK is unique by nature and provides tamperproof content. A hostile node altering the data under a CHK will immediately be detected by the next node or the client. CHKs also reduce the redundancy of data since the same data will have the same CHK and when multiple sites reference the same large files, they can reference to the same CHK. SSKs are based on public-key cryptography. Currently Freenet uses the DSA algorithm. Documents inserted under SSKs are signed by the inserter, and this signature can be verified by every node to ensure that the data is not tampered with. SSKs can be used to establish a verifiable pseudonymous identity on Freenet, and allow for multiple documents to be inserted securely by a single person. Files inserted with an SSK are effectivelyimmutable
In object-oriented and functional programming, an immutable object (unchangeable object) is an object whose state cannot be modified after it is created.Goetz et al. ''Java Concurrency in Practice''. Addison Wesley Professional, 2006, Section 3.4 ...
, since inserting a second file with the same name can cause collisions. USKs resolve this by adding a version number to the keys which is also used for providing update notification for keys registered as bookmarks in the web interface. Another subtype of the SSK is the Keyword Signed Key, or KSK, in which the key pair is generated in a standard way from a simple human-readable string. Inserting a document using a KSK allows the document to be retrieved and decrypted if and only if the requester knows the human-readable string; this allows for more convenient (but less secure) URIs for users to refer to.
Scalability
Anetwork
Network, networking and networked may refer to:
Science and technology
* Network theory, the study of graphs as a representation of relations between discrete objects
* Network science, an academic field that studies complex networks
Mathematics
...
is said to be scalable if its performance does not deteriorate even if the network is very large. The scalability of Freenet is being evaluated, but similar architectures have been shown to scale logarithmically. This work indicates that Freenet can find data in hops on a small-world network (which includes both opennet and darknet style Freenet networks), when ignoring the caching which could improve the scalability for popular content. However, this scalability is difficult to test without a very large network. Furthermore, the security features inherent to Freenet make detailed performance analysis (including things as simple as determining the size of the network) difficult to do accurately. As of now, the scalability of Freenet has yet to be tested.
Darknet versus opennet
As of version 0.7, Freenet supports both "darknet" and "opennet" connections. Opennet connections are made automatically by nodes with opennet enabled, while darknet connections are manually established between users that know and trust each other. Freenet developers describe the trust needed as "will not crack their Freenet node". Opennet connections are easy to use, but darknet connections are more secure against attackers on the network, and can make it difficult for an attacker (such as an oppressive government) to even determine that a user is running Freenet in the first place. The core innovation in Freenet 0.7 is to allow a globally scalable darknet, capable (at least in theory) of supporting millions of users. Previous darknets, such asWASTE
Waste (or wastes) are unwanted or unusable materials. Waste is any substance discarded after primary use, or is worthless, defective and of no use. A by-product, by contrast is a joint product of relatively minor economic value. A waste prod ...
, have been limited to relatively small disconnected networks. The scalability of Freenet is made possible by the fact that human relationships tend to form small-world networks, a property that can be exploited to find short paths between any two people. The work is based on a speech given at DEF CON 13 by Ian Clarke and Swedish mathematician Oskar Sandberg. Furthermore, the routing algorithm is capable of routing over a mixture of opennet and darknet connections, allowing people who have only a few friends using the network to get the performance from having sufficient connections while still receiving some of the security benefits of darknet connections. This also means that small darknets where some users also have opennet connections are fully integrated into the whole Freenet network, allowing all users access to all content, whether they run opennet, darknet, or a hybrid of the two, except for darknet pockets connected only by a single hybrid node.
Tools and applications
 Unlike many other P2P applications Freenet does not provide comprehensive functionality itself. Freenet is modular and features an
Unlike many other P2P applications Freenet does not provide comprehensive functionality itself. Freenet is modular and features an API
An application programming interface (API) is a way for two or more computer programs to communicate with each other. It is a type of software Interface (computing), interface, offering a service to other pieces of software. A document or standa ...
called Freenet Client Protocol (FCP) for other programs to use to implement services such as message boards
An Internet forum, or message board, is an online discussion site where people can hold conversations in the form of posted messages. They differ from chat rooms in that messages are often longer than one line of text, and are at least temporar ...
, file sharing, or online chat.
Communication
Freenet Messaging System (FMS) :FMS was designed to address problems with Frost such asdenial of service
In computing, a denial-of-service attack (DoS attack) is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connect ...
attacks and spam. Users publish trust lists, and each user downloads messages only from identities they trust and identities trusted by identities they trust. FMS is developed anonymously and can be downloaded from ''the FMS freesite'' within Freenet. It does not have an official site on the normal Internet. It features random post delay, support for many identities, and a distinction between trusting a user's posts and trusting their trust list. It is written in C++ and is a separate application from Freenet which uses the Freenet Client Protocol (FCP) to interface with Freenet.
Frost
:Frost includes support for convenient file sharing, but its design is inherently vulnerable to spam and denial of service
In computing, a denial-of-service attack (DoS attack) is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connect ...
attacks. Frost can be downloaded from the Frost home page on SourceForge, or from ''the Frost freesite'' within Freenet. It is not endorsed by the Freenet developers. Frost is written in Java and is a separate application from Freenet.
Sone
:Sone provides a simpler interface inspired by Facebook with public anonymous discussions and image galleries. It provides an API for control from other programs is also used to implement a comment system for static websites in the regular internet.
Utilities
jSite :jSite is a tool to upload websites. It handles keys and manages uploading files. Infocalypse :Infocalypse is an extension for the distributed revision control system Mercurial. It uses an optimized structure to minimize the number of requests to retrieve new data, and allows supporting a repository by securely reuploading most parts of the data without requiring the owner's private keys.Libraries
FCPLib :FCPLib (Freenet Client Protocol Library) aims to be across-platform
In computing, cross-platform software (also called multi-platform software, platform-agnostic software, or platform-independent software) is computer software that is designed to work in several computing platforms. Some cross-platform software r ...
natively compiled
In computing, a compiler is a computer program that translates computer code written in one programming language (the ''source'' language) into another language (the ''target'' language). The name "compiler" is primarily used for programs that ...
set of C++-based functions for storing and retrieving information to and from Freenet. FCPLib supports Windows NT/2K/XP, Debian
Debian (), also known as Debian GNU/Linux, is a Linux distribution composed of free and open-source software, developed by the community-supported Debian Project, which was established by Ian Murdock on August 16, 1993. The first version of D ...
, BSD
The Berkeley Software Distribution or Berkeley Standard Distribution (BSD) is a discontinued operating system based on Research Unix, developed and distributed by the Computer Systems Research Group (CSRG) at the University of California, Berk ...
, Solaris
Solaris may refer to:
Arts and entertainment Literature, television and film
* ''Solaris'' (novel), a 1961 science fiction novel by Stanisław Lem
** ''Solaris'' (1968 film), directed by Boris Nirenburg
** ''Solaris'' (1972 film), directed by ...
, and macOS
macOS (; previously OS X and originally Mac OS X) is a Unix operating system developed and marketed by Apple Inc. since 2001. It is the primary operating system for Apple's Mac computers. Within the market of desktop and lapt ...
.
lib-pyFreenet
:lib-pyFreenet exposes Freenet functionality to Python
Python may refer to:
Snakes
* Pythonidae, a family of nonvenomous snakes found in Africa, Asia, and Australia
** ''Python'' (genus), a genus of Pythonidae found in Africa and Asia
* Python (mythology), a mythical serpent
Computing
* Python (pro ...
programs. Infocalypse uses it.
Vulnerabilities
Law enforcement agencies have claimed to have successfully infiltrated Freenet opennet in order to deanonymize users but no technical details have been given to support these allegations. One report stated that, "A child-porn investigation focused on ...he suspect
He or HE may refer to:
Language
* He (pronoun), an English pronoun
* He (kana), the romanization of the Japanese kana へ
* He (letter), the fifth letter of many Semitic alphabets
* He (Cyrillic), a letter of the Cyrillic script called ''He'' in ...
when the authorities were monitoring the online network, Freenet." A different report indicated arrests may have been based on the BlackICE project leaks, that are debunked for using bad math and for using an incorrectly calculated false positives rate and a false model.
A court case in the Peel Region of Ontario, ''Canada R. v. Owen'', 2017 ONCJ 729 (CanLII), illustrated that law enforcement do in fact have a presence, after Peel Regional Police located who had been downloading illegal material on the Freenet network. The court decision indicates that a Canadian Law Enforcement agency operates nodes running modified Freenet software in the hope of determining who is requesting illegal material.
*Routing Table Insertion (RTI) Attack
Notability
Freenet has had significant publicity in the mainstream press, including articles in ''The New York Times
''The New York Times'' (''the Times'', ''NYT'', or the Gray Lady) is a daily newspaper based in New York City with a worldwide readership reported in 2020 to comprise a declining 840,000 paid print subscribers, and a growing 6 million paid ...
'', and coverage on CNN
CNN (Cable News Network) is a multinational cable news channel headquartered in Atlanta, Georgia, U.S. Founded in 1980 by American media proprietor Ted Turner and Reese Schonfeld as a 24-hour cable news channel, and presently owned by the M ...
, ''60 Minutes II
''60 Minutes II'' (also known as ''60 Minutes Wednesday'' and ''60 Minutes'') is an American weekly primetime news magazine television program that was intended to replicate the "signature style, journalistic quality and integrity" of the origina ...
'', the BBC #REDIRECT BBC #REDIRECT BBC #REDIRECT BBC
Here i going to introduce about the best teacher of my life b BALAJI sir. He is the precious gift that I got befor 2yrs . How has helped and thought all the concept and made my success in the 10th board ex ...
, ''The Guardian
''The Guardian'' is a British daily newspaper. It was founded in 1821 as ''The Manchester Guardian'', and changed its name in 1959. Along with its sister papers ''The Observer'' and ''The Guardian Weekly'', ''The Guardian'' is part of the Gu ...
'',Andy Beckett in ''The Guardian'' 2009
Freesite
A "freesite" is a site hosted on the Freenet network. Because it contains only static content, it cannot contain any active content like server-side scripts or databases. Freesites are coded in HTML and support as many features as the browser viewing the page allows; however, there are some exceptions where the Freenet software will remove parts of the code that may be used to reveal the identity of the person viewing the page (making a page access something on the internet, for example).See also
* Peer-to-peer web hosting * Rendezvous protocol *Anonymous P2P
An anonymous P2P communication system is a peer-to-peer distributed application in which the nodes, which are used to share resources, or participants are anonymous or pseudonymous. Anonymity of participants is usually achieved by special routi ...
* Crypto-anarchism
* Cypherpunk
A cypherpunk is any individual advocating widespread use of strong cryptography and privacy-enhancing technologies as a route to social and political change. Originally communicating through the Cypherpunks electronic mailing list, informal g ...
* Distributed file system
* Freedom of information
Freedom of information is freedom of a person or people to publish and consume information. Access to information is the ability for an individual to seek, receive and impart information effectively. This sometimes includes "scientific, indigeno ...
* Friend-to-friend
Comparable software
*GNUnet
GNUnet is a software framework for decentralized, peer-to-peer networking and an official GNU package. The framework offers link encryption, peer discovery, resource allocation, communication over many transports (such as TCP, UDP, HTTP, ...
* I2P
The Invisible Internet Project (I2P) is an anonymous network layer (implemented as a mix network) that allows for censorship-resistant, peer-to-peer communication. Anonymous connections are achieved by encrypting the user's traffic (by using ...
* InterPlanetary File System
The InterPlanetary File System (IPFS) is a protocol, hypermedia and file sharing peer-to-peer network for storing and sharing data in a distributed file system. IPFS uses content-addressing to uniquely identify each file in a global namespace ...
* Java Anon Proxy
Java Anon Proxy (JAP) also known as JonDonym, was a proxy server, proxy system designed to allow browsing the World Wide Web, Web with revocable pseudonymity.
(also known as JonDonym)
* Osiris
Osiris (, from Egyptian ''wsjr'', cop, ⲟⲩⲥⲓⲣⲉ , ; Phoenician: 𐤀𐤎𐤓, romanized: ʾsr) is the god of fertility, agriculture, the afterlife, the dead, resurrection, life, and vegetation in ancient Egyptian religion. He was ...
* Perfect Dark
''Perfect Dark'' is a first-person shooter developed and published by Rare for the Nintendo 64 video game console in 2000. The first game of the ''Perfect Dark'' series, it follows Joanna Dark, an agent of the Carrington Institute research c ...
– also creates a distributed data store shared by anonymous nodes; the successor to Share, which itself is the successor of Winny
* Tahoe-LAFS
Tahoe-LAFS (Tahoe Least-Authority File Store) is a free and open, secure, decentralized, fault-tolerant, distributed data store and distributed file system. It can be used as an online backup system, or to serve as a file or Web host similar to ...
* ZeroNet
ZeroNet is a decentralized web-like network of peer-to-peer users, created by Tamas Kocsis in 2015, programming for the network was based in Budapest, Hungary; is built in Python; and is fully open source. Instead of having an IP address, sites ...
References
Further reading
* * * * * * * *External links
* {{Internet censorship circumvention technologies Free file transfer software Free file sharing software Distributed file systems Anonymous file sharing networks Anonymity networks Application layer protocols Distributed data storage systems Distributed data storage Distributed data structures File sharing Free software programmed in Java (programming language) Cross-platform software Beta software 2000 introductions Key-based routing Overlay networks Mix networks