|
Clock (cryptography)
In cryptography, the clock was a method devised by Polish mathematician-cryptologist Jerzy Różycki, at the Polish General Staff's Cipher Bureau, to facilitate decrypting German Enigma ciphers. The method determined the rightmost rotor in the German Enigma by exploiting the different turnover positions. For the Poles, learning the rightmost rotor reduced the rotor-order search space by a factor of 3 (the number of rotors). The British improved the method, and it allowed them to use their limited number of bombes more effectively (the British confronted 5 to 8 rotors). Method This method sometimes made it possible to determine which of the Enigma machine's rotors was at the far right, that is, in the position where the rotor always revolved at every depression of a key. The clock method was developed by Jerzy Różycki during 1933–1935. Marian Rejewski's grill method could determine the right-hand rotor, but that involved trying each possible rotor permutation (there wer ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security (data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synony ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bletchley Park
Bletchley Park is an English country house and estate in Bletchley, Milton Keynes (Buckinghamshire) that became the principal centre of Allied code-breaking during the Second World War. The mansion was constructed during the years following 1883 for the financier and politician Sir Herbert Leon in the Victorian Gothic, Tudor, and Dutch Baroque styles, on the site of older buildings of the same name. During World War II, the estate housed the Government Code and Cypher School (GC&CS), which regularly penetrated the secret communications of the Axis Powersmost importantly the German Enigma and Lorenz ciphers. The GC&CS team of codebreakers included Alan Turing, Gordon Welchman, Hugh Alexander, Bill Tutte, and Stuart Milner-Barry. The nature of the work at Bletchley remained secret until many years after the war. According to the official historian of British Intelligence, the "Ultra" intelligence produced at Bletchley shortened the war by two to four years, and withou ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptanalytic Devices
Cryptanalysis (from the Greek ''kryptós'', "hidden", and ''analýein'', "to analyze") refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown. In addition to mathematical analysis of cryptographic algorithms, cryptanalysis includes the study of side-channel attacks that do not target weaknesses in the cryptographic algorithms themselves, but instead exploit weaknesses in their implementation. Even though the goal has been the same, the methods and techniques of cryptanalysis have changed drastically through the history of cryptography, adapting to increasing cryptographic complexity, ranging from the pen-and-paper methods of the past, through machines like the British Bombes and Colossus computers at Bletchley Park in World War II, to the mathematically advanced comput ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Warsaw
Warsaw ( pl, Warszawa, ), officially the Capital City of Warsaw,, abbreviation: ''m.st. Warszawa'' is the capital and largest city of Poland. The metropolis stands on the River Vistula in east-central Poland, and its population is officially estimated at 1.86 million residents within a greater metropolitan area of 3.1 million residents, which makes Warsaw the 7th most-populous city in the European Union. The city area measures and comprises 18 districts, while the metropolitan area covers . Warsaw is an Alpha global city, a major cultural, political and economic hub, and the country's seat of government. Warsaw traces its origins to a small fishing town in Masovia. The city rose to prominence in the late 16th century, when Sigismund III decided to move the Polish capital and his royal court from Kraków. Warsaw served as the de facto capital of the Polish–Lithuanian Commonwealth until 1795, and subsequently as the seat of Napoleon's Duchy of Warsaw. Th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Birthday Problem
In probability theory, the birthday problem asks for the probability that, in a set of randomly chosen people, at least two will share a birthday. The birthday paradox is that, counterintuitively, the probability of a shared birthday exceeds 50% in a group of only 23 people. The birthday paradox is a veridical paradox: it appears wrong, but is in fact true. While it may seem surprising that only 23 individuals are required to reach a 50% probability of a shared birthday, this result is made more intuitive by considering that the comparisons of birthdays will be made between every possible pair of individuals. With 23 individuals, there are (23 × 22) / 2 = 253 pairs to consider, much more than half the number of days in a year. Real-world applications for the birthday problem include a cryptographic attack called the birthday attack, which uses this probabilistic model to reduce the complexity of finding a collision for a hash function, as well a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Letter Frequency
Letter frequency is the number of times letters of the alphabet appear on average in written language. Letter frequency analysis dates back to the Arab mathematician Al-Kindi (c. 801–873 AD), who formally developed the method to break ciphers. Letter frequency analysis gained importance in Europe with the development of movable type in 1450 AD, where one must estimate the amount of type required for each letterform. Linguists use letter frequency analysis as a rudimentary technique for language identification, where it is particularly effective as an indication of whether an unknown writing system is alphabetic, syllabic, or ideographic. The use of letter frequencies and frequency analysis plays a fundamental role in cryptograms and several word puzzle games, including Hangman, ''Scrabble'', '' Wordle'' and the television game show '' Wheel of Fortune''. One of the earliest descriptions in classical literature of applying the knowledge of English letter frequen ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Discrete Uniform Distribution
In probability theory and statistics, the discrete uniform distribution is a symmetric probability distribution wherein a finite number of values are equally likely to be observed; every one of ''n'' values has equal probability 1/''n''. Another way of saying "discrete uniform distribution" would be "a known, finite number of outcomes equally likely to happen". A simple example of the discrete uniform distribution is throwing a fair dice. The possible values are 1, 2, 3, 4, 5, 6, and each time the die is thrown the probability of a given score is 1/6. If two dice are thrown and their values added, the resulting distribution is no longer uniform because not all sums have equal probability. Although it is convenient to describe discrete uniform distributions over integers, such as this, one can also consider discrete uniform distributions over any finite set. For instance, a random permutation is a permutation generated uniformly from the permutations of a given length, and a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Index Of Coincidence
In cryptography, coincidence counting is the technique (invented by William F. Friedman) of putting two texts side-by-side and counting the number of times that identical letters appear in the same position in both texts. This count, either as a ratio of the total or normalized by dividing by the expected count for a random source model, is known as the index of coincidence, or IC for short. Because letters in a natural language are not distributed evenly, the IC is higher for such texts than it would be for uniformly random text strings. What makes the IC especially useful is the fact that its value does not change if both texts are scrambled by the same single-alphabet substitution cipher, allowing a cryptanalyst to quickly detect that form of encryption. Calculation The index of coincidence provides a measure of how likely it is to draw two matching letters by randomly selecting two letters from a given text. The chance of drawing a given letter in the text is (number of t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
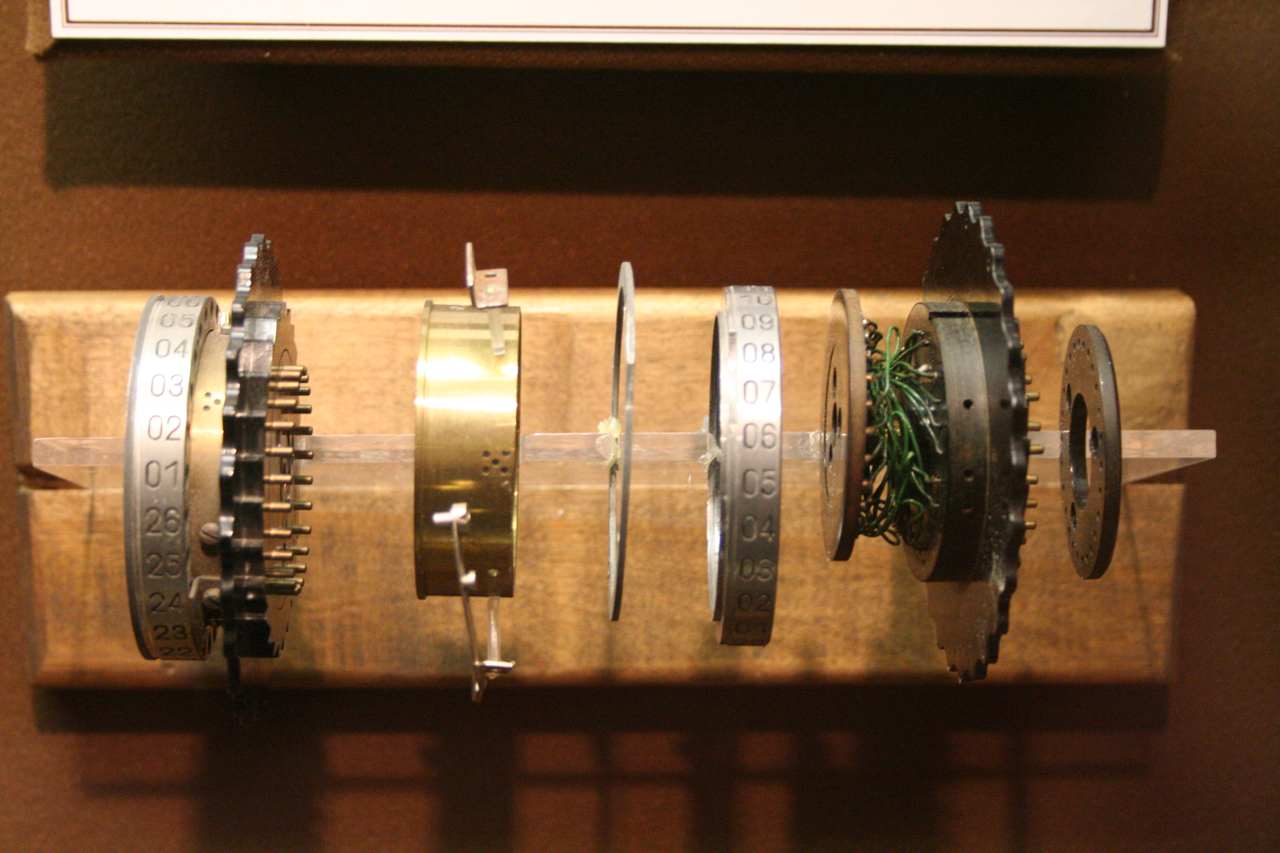
Enigma Rotor
This article contains technical details about the rotors of the Enigma machine. Understanding the way the machine encrypts requires taking into account the current position of each rotor, the ring setting and its internal wiring. Physical design of rotors Image:Enigma-rotor-pin-contacts.jpg, The right side of a rotor, showing the pin electrical contacts. The Roman numeral V identifies the wiring of the rotor. Image:Enigma-rotor-flat-contacts.jpg, The left side of an Enigma rotor, showing the flat (plate) electrical contacts. A single turnover notch is visible on the left edge of the rotor. Rotor electrical view No letter can map to itself, a cryptographic weakness caused by the same wires being used for forwards and backwards legs. Rotor offset The effect of rotation on the rotors can be demonstrated with some examples. As an example, let us take rotor type I of Enigma I (see table below) without any ring setting offset. It can be seen that an is encoded as an , ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Banburismus
Banburismus was a cryptanalytic process developed by Alan Turing at Bletchley Park in Britain during the Second World War. It was used by Bletchley Park's Hut 8 to help break German ''Kriegsmarine'' (naval) messages enciphered on Enigma machines. The process used sequential conditional probability to infer information about the likely settings of the Enigma machine. It gave rise to Turing's invention of the ''ban'' as a measure of the weight of evidence in favour of a hypothesis. This concept was later applied in Turingery and all the other methods used for breaking the Lorenz cipher. Overview The aim of Banburismus was to reduce the time required of the electromechanical Bombe machines by identifying the most likely right-hand and middle wheels of the Enigma. Hut 8 performed the procedure continuously for two years, stopping only in 1943 when sufficient bombe time became readily available. Banburismus was a development of the " clock method" invented by the Polish cryptanaly ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Alan Turing
Alan Mathison Turing (; 23 June 1912 – 7 June 1954) was an English mathematician, computer scientist, logician, cryptanalyst, philosopher, and theoretical biologist. Turing was highly influential in the development of theoretical computer science, providing a formalisation of the concepts of algorithm and computation with the Turing machine, which can be considered a model of a general-purpose computer. He is widely considered to be the father of theoretical computer science and artificial intelligence. Born in Maida Vale, London, Turing was raised in southern England. He graduated at King's College, Cambridge, with a degree in mathematics. Whilst he was a fellow at Cambridge, he published a proof demonstrating that some purely mathematical yes–no questions can never be answered by computation and defined a Turing machine, and went on to prove that the halting problem for Turing machines is undecidable. In 1938, he obtained his PhD from the Department of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Poland
Poland, officially the Republic of Poland, , is a country in Central Europe. Poland is divided into Voivodeships of Poland, sixteen voivodeships and is the fifth most populous member state of the European Union (EU), with over 38 million people, and the List of European countries by area, seventh largest EU country, covering a combined area of . It extends from the Baltic Sea in the north to the Sudetes and Carpathian Mountains in the south, bordering seven countries. The territory is characterised by a varied landscape, diverse ecosystems, and Temperate climate, temperate transitional climate. The capital and List of cities and towns in Poland, largest city is Warsaw; other major cities include Kraków, Wrocław, Łódź, Poznań, and Gdańsk. Prehistory and protohistory of Poland, Humans have been present on Polish soil since the Lower Paleolithic, with continuous settlement since the end of the Last Glacial Period over 12,000 years ago. Culturally diverse throughout ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |