|
Security Information Management
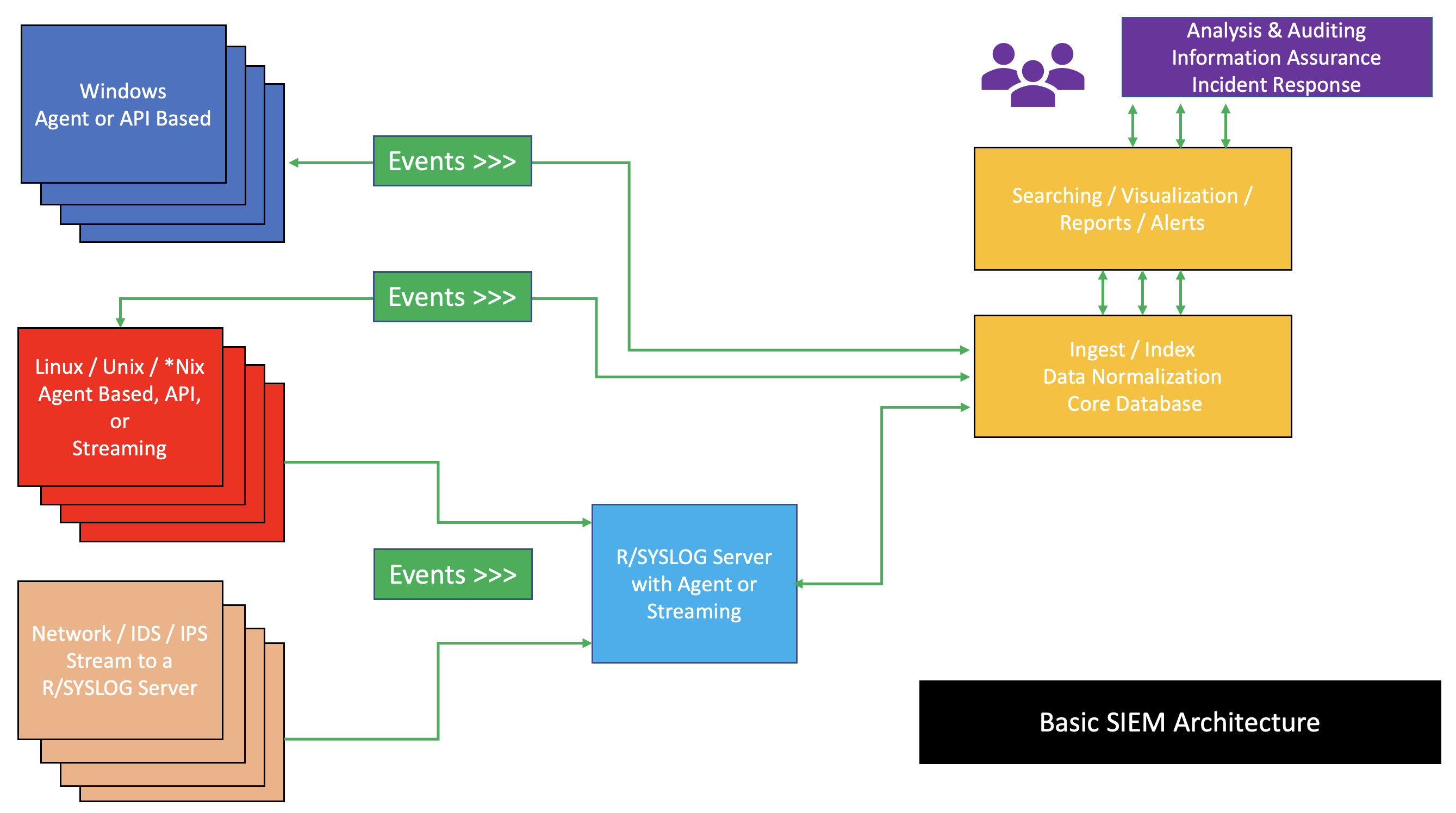
Security information management (SIM) is an information security industry term for the collection of data such as log files into a central repository for trend analysis. Overview SIM products generally are software agents running on the computer systems that are monitored. The recorded log information is then sent to a centralized server that acts as a "security console". The console typically displays reports, charts, and graphs of that information, often in real time. Some software agents can incorporate local filters to reduce and manipulate the data that they send to the server, although typically from a forensic point of view you would collect all audit and accounting logs to ensure you can recreate a security incident. The security console is monitored by an administrator who reviews the consolidated information and takes action in response to any alerts issued. The data that is sent to the server to be correlated and analyzed are normalized by the software agents into a c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Security
Information security is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorized or inappropriate access to data or the unlawful use, Data breach, disclosure, disruption, deletion, corruption, modification, inspection, recording, or devaluation of information. It also involves actions intended to reduce the adverse impacts of such incidents. Protected information may take any form, e.g., electronic or physical, tangible (e.g., Document, paperwork), or intangible (e.g., knowledge). Information security's primary focus is the balanced protection of data confidentiality, data integrity, integrity, and data availability, availability (also known as the 'CIA' triad) while maintaining a focus on efficient policy implementation, all without hampering organization productivity. This is largely achieved through a structured risk management process. To stand ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Logfile
In computing, logging is the act of keeping a log of events that occur in a computer system, such as problems, errors or broad information on current operations. These events may occur in the operating system or in other software. A message or ''log entry'' is recorded for each such event. These log messages can then be used to monitor and understand the operation of the system, to debug problems, or during an audit. Logging is particularly important in multi-user software, to have a central overview of the operation of the system. In the simplest case, messages are written to a file, called a ''log file''. Alternatively, the messages may be written to a dedicated logging system or to a log management software, where it is stored in a database or on a different computer system. Specifically, a ''transaction log'' is a log of the communications between a system and the users of that system, or a data collection method that automatically captures the type, content, or time of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Systems Audit And Control Association
ISACA is an international professional association focused on IT (information technology) governance. On its IRS filings, it is known as the Information Systems Audit and Control Association, although ISACA now goes by its acronym only. ISACA currently offers 8 certification programs, as well as other micro-certificates. History ISACA originated in United States in 1967, when a group of individuals working on auditing controls in computer systems started to become increasingly critical of the operations of their organizations. They identified a need for a centralized source of information and guidance in the field. In 1969, Stuart Tyrnauer, an employee of the (later) |
Information Security Management
Information security management (ISM) defines and manages controls that an organization needs to implement to ensure that it is sensibly protecting the confidentiality, availability, and integrity of assets from threats and vulnerabilities. The core of ISM includes information risk management, a process that involves the assessment of the risks an organization must deal with in the management and protection of assets, as well as the dissemination of the risks to all appropriate stakeholders. This requires proper asset identification and valuation steps, including evaluating the value of confidentiality, integrity, availability, and replacement of assets. As part of information security management, an organization may implement an information security management system and other best practices found in the ISO/IEC 27001, ISO/IEC 27002, and ISO/IEC 27035 standards on information security. Risk management and mitigation Managing information security in essence means managing a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security Event Manager
Security event management (SEM), and the related Security information management, SIM and SIEM, are computer security disciplines that use data inspection tools to centralize the storage and interpretation of logs or events generated by other software running on a network. Overview The acronyms ''SEM'', ''SIM,'' and ''SIEM'' have sometimes been used interchangeably, but generally refer to the different primary focus of products: * ''Log management'': Focus on simple collection and storage of data logging, log messages and audit trails * ''Security information management'' (Security information management, SIM): Long-term storage and analysis and reporting of log data. * ''Security event manager'' (SEM): Real-time monitoring, correlation of events, notifications, and console views. * ''Security information and event management'' (Security information and event management, SIEM): Combines SIM and SEM and provides real-time analysis of security alerts generated by network hardware and a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SIEM
Security information and event management (SIEM) is a field within computer security that combines security information management (SIM) and security event management (SEM) to enable real-time analysis of security alerts generated by applications and network hardware. SIEM systems are central to Security operations center, security operations centers (SOCs), where they are employed to detect, investigate, and respond to security incidents. SIEM technology collects and aggregates data from various systems, allowing organizations to meet compliance requirements while safeguarding against Cyberattack, threats. National Institute of Standards and Technology (NIST) definition for SIEM tool is application that provides the ability to gather security data from information system components and present that data as actionable information via a single interface. SIEM tools can be implemented as software, hardware, or managed services. SIEM systems log security events and generating reports to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Security Management
Information security management (ISM) defines and manages controls that an organization needs to implement to ensure that it is sensibly protecting the confidentiality, availability, and integrity of assets from threats and vulnerabilities. The core of ISM includes information risk management, a process that involves the assessment of the risks an organization must deal with in the management and protection of assets, as well as the dissemination of the risks to all appropriate stakeholders. This requires proper asset identification and valuation steps, including evaluating the value of confidentiality, integrity, availability, and replacement of assets. As part of information security management, an organization may implement an information security management system and other best practices found in the ISO/IEC 27001, ISO/IEC 27002, and ISO/IEC 27035 standards on information security. Risk management and mitigation Managing information security in essence means managing a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Security Management System
Information security management (ISM) defines and manages controls that an organization needs to implement to ensure that it is sensibly protecting the confidentiality, availability, and integrity of assets from threats and vulnerabilities. The core of ISM includes information risk management, a process that involves the assessment of the risks an organization must deal with in the management and protection of assets, as well as the dissemination of the risks to all appropriate stakeholders. This requires proper asset identification and valuation steps, including evaluating the value of confidentiality, integrity, availability, and replacement of assets. As part of information security management, an organization may implement an information security management system and other best practices found in the ISO/IEC 27001, ISO/IEC 27002, and ISO/IEC 27035 standards on information security. Risk management and mitigation Managing information security in essence means managing and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security Information And Event Management
Security information and event management (SIEM) is a field within computer security that combines security information management (SIM) and security event management (SEM) to enable real-time analysis of security alerts generated by applications and network hardware. SIEM systems are central to Security operations center, security operations centers (SOCs), where they are employed to detect, investigate, and respond to security incidents. SIEM technology collects and aggregates data from various systems, allowing organizations to meet compliance requirements while safeguarding against Cyberattack, threats. National Institute of Standards and Technology (NIST) definition for SIEM tool is application that provides the ability to gather security data from information system components and present that data as actionable information via a single interface. SIEM tools can be implemented as software, hardware, or managed services. SIEM systems log security events and generating reports to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security Event Manager
Security event management (SEM), and the related Security information management, SIM and SIEM, are computer security disciplines that use data inspection tools to centralize the storage and interpretation of logs or events generated by other software running on a network. Overview The acronyms ''SEM'', ''SIM,'' and ''SIEM'' have sometimes been used interchangeably, but generally refer to the different primary focus of products: * ''Log management'': Focus on simple collection and storage of data logging, log messages and audit trails * ''Security information management'' (Security information management, SIM): Long-term storage and analysis and reporting of log data. * ''Security event manager'' (SEM): Real-time monitoring, correlation of events, notifications, and console views. * ''Security information and event management'' (Security information and event management, SIEM): Combines SIM and SEM and provides real-time analysis of security alerts generated by network hardware and a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Gordon–Loeb Model
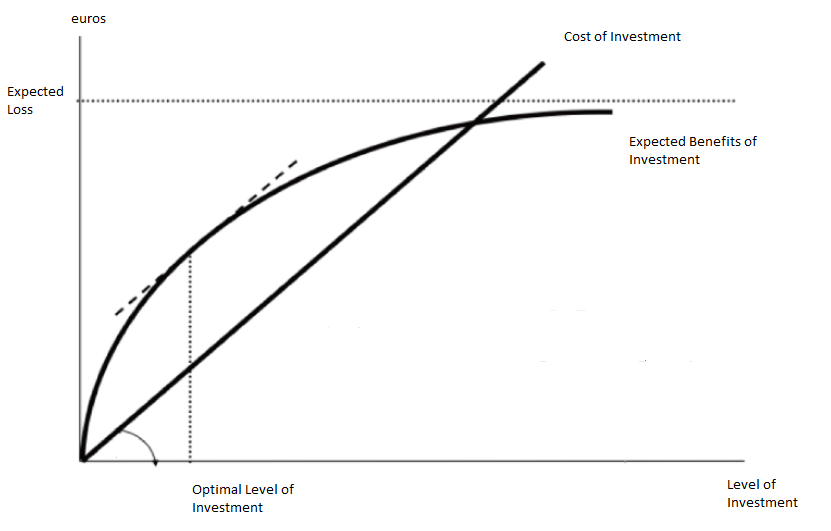
The Gordon–Loeb model is an economic model that analyzes the optimal level of investment in information security. The benefits of investing in cybersecurity stem from reducing the costs associated with cyber breaches. The Gordon-Loeb model provides a framework for determining how much to invest in cybersecurity, using a cost-benefit approach. The model includes the following key components: * Organizational data vulnerable to cyber-attacks, with vulnerability denoted by (), representing the probability of a breach occurring under current conditions. * The potential loss from a breach, represented by , which can be expressed in monetary terms. The expected loss is calculated as before additional cybersecurity investments. * Investment in cybersecurity, denoted as , reduces based on the effectiveness of the security measures, known as the security breach probability function. Gordon and Loeb demonstrated that the optimal level of security investment, , does not exceed 37% ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |