Signals intelligence in modern history on:
[Wikipedia]
[Google]
[Amazon]
Before the development of
 Electronic interception appeared as early as 1900, during the
Electronic interception appeared as early as 1900, during the
 By the start of the
By the start of the  A similar organisation had begun in the Military Intelligence department of the
A similar organisation had begun in the Military Intelligence department of the
 The use of radio receiving equipment to pinpoint the location of the transmitter was also developed during the war.
Captain
The use of radio receiving equipment to pinpoint the location of the transmitter was also developed during the war.
Captain
 Room 40 played an important role in several naval engagements during the war, notably in detecting major German sorties into the
Room 40 played an important role in several naval engagements during the war, notably in detecting major German sorties into the
 The British
The British
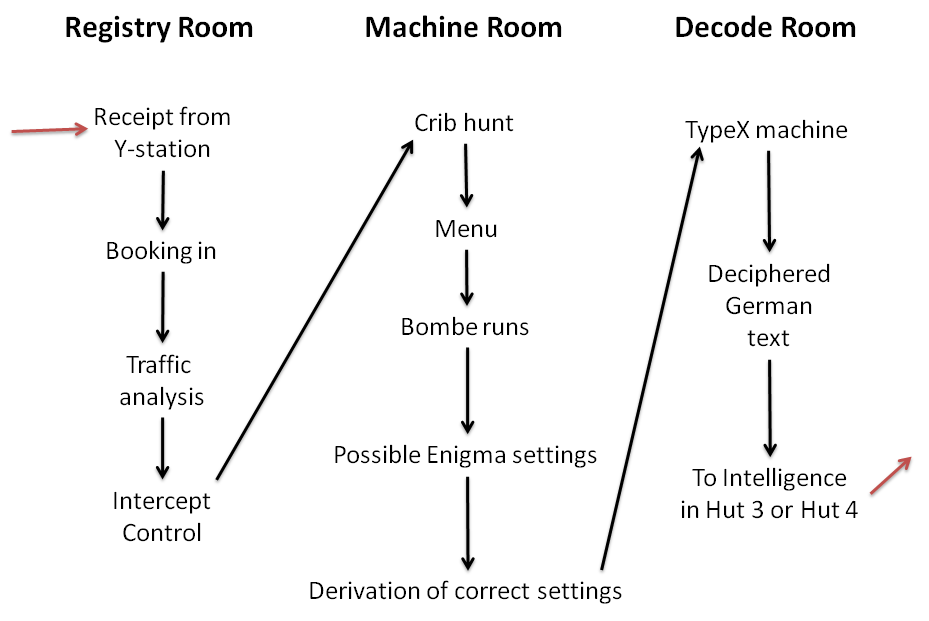
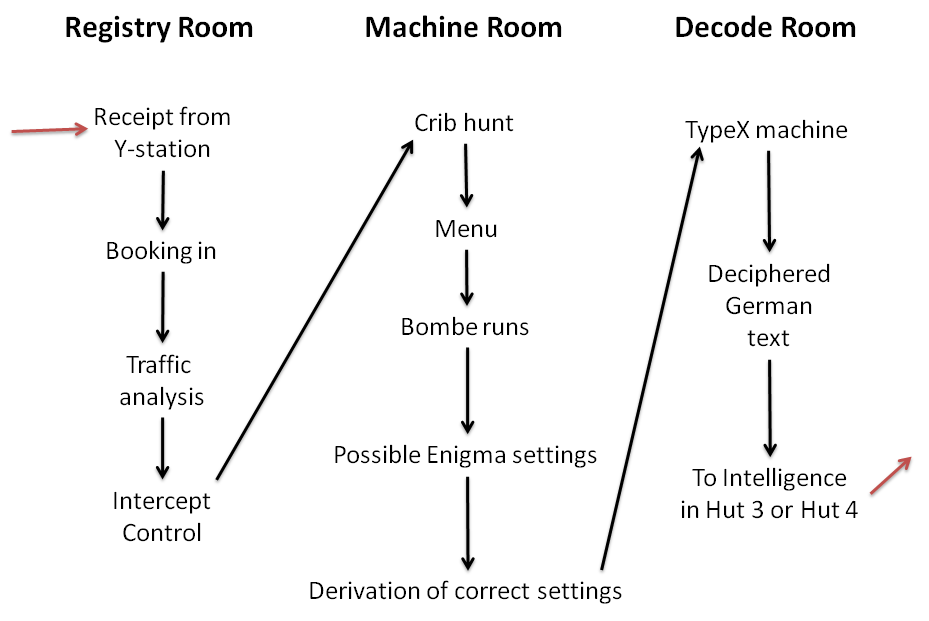
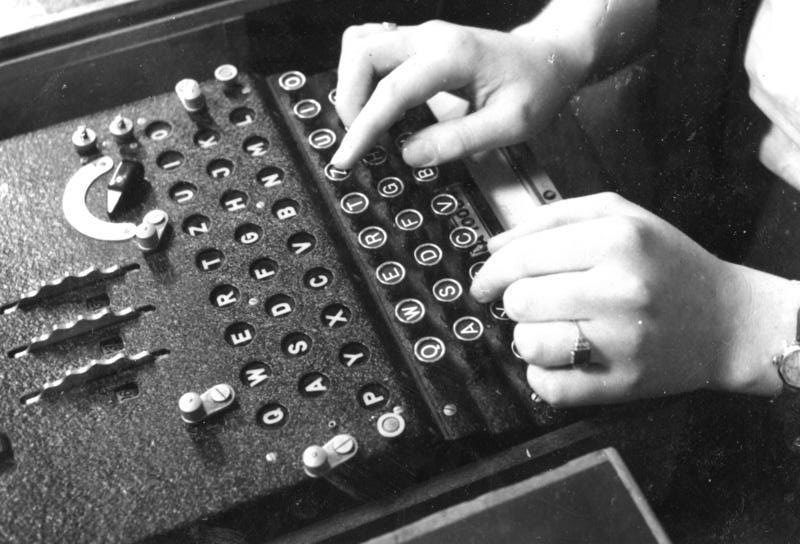 Most German messages decrypted at Bletchley were produced by one or another version of the
Most German messages decrypted at Bletchley were produced by one or another version of the  It is unclear why the German submarine command believed that frequent radio communications were not a hazard to their boats, although they seemed confident in the security of their Enigma ciphers, both in the initial three-rotor and subsequent four-rotor versions (known as Triton to the Germans and Shark to the Allies). There was an apparent, mutually reinforcing belief that wolfpack attacks by groups of submarines were much more deadly than individual operations, and confidence the communications were secure. Arguably, the Germans underestimated HF/DF even more than they did British cryptanalysis. Apparently, the Germans did not realize that the Allies were not limited to slow, manually operated direction finders, and also underestimated the number of direction finders at sea. On the other hand, the introduction of a new secure communication system would have interrupted submarine operations for a long time since a gradual shift to a new system was out of the question.
The Lorenz messages were codenamed '' Tunny'' at Bletchley Park. They were only sent in quantity from mid-1942. The Tunny networks were used for high-level messages between German High Command and field commanders. With the help of German operator errors, the cryptanalysts in the
It is unclear why the German submarine command believed that frequent radio communications were not a hazard to their boats, although they seemed confident in the security of their Enigma ciphers, both in the initial three-rotor and subsequent four-rotor versions (known as Triton to the Germans and Shark to the Allies). There was an apparent, mutually reinforcing belief that wolfpack attacks by groups of submarines were much more deadly than individual operations, and confidence the communications were secure. Arguably, the Germans underestimated HF/DF even more than they did British cryptanalysis. Apparently, the Germans did not realize that the Allies were not limited to slow, manually operated direction finders, and also underestimated the number of direction finders at sea. On the other hand, the introduction of a new secure communication system would have interrupted submarine operations for a long time since a gradual shift to a new system was out of the question.
The Lorenz messages were codenamed '' Tunny'' at Bletchley Park. They were only sent in quantity from mid-1942. The Tunny networks were used for high-level messages between German High Command and field commanders. With the help of German operator errors, the cryptanalysts in the
 An outpost of the Government Code and Cypher School was set up in Hong Kong in 1935, the
An outpost of the Government Code and Cypher School was set up in Hong Kong in 1935, the
 The
The
 As evidenced by the
As evidenced by the
radar
Radar is a detection system that uses radio waves to determine the distance (''ranging''), angle, and radial velocity of objects relative to the site. It can be used to detect aircraft, ships, spacecraft, guided missiles, motor vehicles, w ...
and other electronics techniques, signals intelligence
Signals intelligence (SIGINT) is intelligence-gathering by interception of ''signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication ( ...
(SIGINT) and communications intelligence
Signals intelligence (SIGINT) is list of intelligence gathering disciplines, intelligence-gathering by interception of ''Signal, signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from ele ...
(COMINT) were essentially synonymous. Sir Francis Walsingham
Sir Francis Walsingham ( – 6 April 1590) was principal secretary to Queen Elizabeth I of England from 20 December 1573 until his death and is popularly remembered as her "spymaster".
Born to a well-connected family of gentry, Wals ...
ran a postal interception bureau with some cryptanalytic capability during the reign of Elizabeth I
Elizabeth I (7 September 153324 March 1603) was Queen of England and Ireland from 17 November 1558 until her death in 1603. Elizabeth was the last of the five House of Tudor monarchs and is sometimes referred to as the "Virgin Queen".
El ...
, but the technology was only slightly less advanced than men with shotguns, during World War I, who jammed pigeon post
Pigeon post is the use of homing pigeons to carry messages. Pigeons are effective as messengers due to their natural homing abilities. The pigeons are transported to a destination in cages, where they are attached with messages, then the pigeo ...
communications and intercepted the messages carried.
Flag signals
Flag signals can mean any of various methods of using flags or pennants to send signals. Flags may have individual significance as signals, or two or more flags may be manipulated so that their relative positions convey symbols. Flag signals allo ...
were sometimes intercepted, and efforts to impede them made . The middle 19th century rise of the telegraph
Telegraphy is the long-distance transmission of messages where the sender uses symbolic codes, known to the recipient, rather than a physical exchange of an object bearing the message. Thus flag semaphore is a method of telegraphy, whereas p ...
allowed more scope for interception and spoofing of signals, as shown at Chancellorsville.
Signals intelligence became far more central to military (and to some extent diplomatic) intelligence generally with the mechanization of armies, development of blitzkrieg
Blitzkrieg ( , ; from 'lightning' + 'war') is a word used to describe a surprise attack using a rapid, overwhelming force concentration that may consist of armored and motorized or mechanized infantry formations, together with close air su ...
tactics, use of submarine
A submarine (or sub) is a watercraft capable of independent operation underwater. It differs from a submersible, which has more limited underwater capability. The term is also sometimes used historically or colloquially to refer to remotely op ...
and commerce raiders warfare, and the development of practicable radio communications
Radio is the technology of signaling and communicating using radio waves. Radio waves are electromagnetic waves of frequency between 30 hertz (Hz) and 300 gigahertz (GHz). They are generated by an electronic device called a transmit ...
. Even measurement and signature intelligence
Measurement and signature intelligence (MASINT) is a technical branch of intelligence gathering, which serves to detect, track, identify or describe the distinctive characteristics (signatures) of fixed or dynamic target sources. This often incl ...
(MASINT) preceded electronic intelligence
Signals intelligence (SIGINT) is intelligence-gathering by interception of ''signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication ( ...
(ELINT), with sound ranging
In land warfare, artillery sound ranging is a method of determining the coordinates of a hostile battery using data derived from the sound of its guns (or mortar or rockets) firing. The same methods can also be used to direct artillery fire at ...
techniques for artillery location. SIGINT is the analysis of intentional signals for both communications and non-communications (e.g., radar) systems, while MASINT is the analysis of unintentional information, including, but not limited to, the electromagnetic signals that are the main interest in SIGINT.
Origins
 Electronic interception appeared as early as 1900, during the
Electronic interception appeared as early as 1900, during the Boer Wars
The military history of South Africa chronicles a vast time period and complex events from the dawn of history until the present time. It covers civil wars and wars of aggression and of self-defence both within South Africa and against it. It in ...
. The Royal Navy
The Royal Navy (RN) is the United Kingdom's naval warfare force. Although warships were used by English and Scottish kings from the early medieval period, the first major maritime engagements were fought in the Hundred Years' War against F ...
had installed wireless sets produced by Marconi on board their ships in the late 1890s and some limited wireless signalling was used by the British Army
The British Army is the principal land warfare force of the United Kingdom, a part of the British Armed Forces along with the Royal Navy and the Royal Air Force. , the British Army comprises 79,380 regular full-time personnel, 4,090 Gurk ...
. Some wireless sets were captured by the Boers
Boers ( ; af, Boere ()) are the descendants of the Dutch-speaking Free Burghers of the eastern Cape frontier in Southern Africa during the 17th, 18th, and 19th centuries. From 1652 to 1795, the Dutch East India Company controlled this area ...
, and were used to make vital transmissions. Since the British were the only people transmitting at the time, no special interpretation of the signals was necessary.
The Imperial Russian Navy
The Imperial Russian Navy () operated as the navy of the Russian Tsardom and later the Russian Empire from 1696 to 1917. Formally established in 1696, it lasted until dissolved in the wake of the February Revolution of 1917. It developed from a ...
also experimented with wireless communications under the guidance of Alexander Popov, who first installed a wireless set on a grounded battleship in 1900. The birth of signals intelligence in a modern sense dates to the Russo-Japanese War
The Russo-Japanese War ( ja, 日露戦争, Nichiro sensō, Japanese-Russian War; russian: Ру́сско-япóнская войнá, Rússko-yapónskaya voyná) was fought between the Empire of Japan and the Russian Empire during 1904 and 1 ...
.
As the Russian fleet prepared for conflict with Japan in 1904, the British ship HMS ''Diana'' stationed in the Suez canal
The Suez Canal ( arz, قَنَاةُ ٱلسُّوَيْسِ, ') is an artificial sea-level waterway in Egypt, connecting the Mediterranean Sea to the Red Sea through the Isthmus of Suez and dividing Africa and Asia. The long canal is a popular ...
was able to intercept Russian naval wireless signals being sent out for the mobilization of the fleet, for the first time in history.
"An intelligence report on signals intercepted by HMS ''Diana'' at Suez shows that the rate of working was extremely slow by British standards, while the Royal Navy interpreters were particularly critical of the poor standard of grammar and spelling among the Russian operators".
The Japanese also developed a wireless interception capability and succeeded in listening in to the then primitive Russian communications. Their successes emphasized the importance of this new source of military intelligence, and facilities for the exploitation of this information resource were established by all the major powers in the following years.
The Austro-Hungarian
Austria-Hungary, often referred to as the Austro-Hungarian Empire,, the Dual Monarchy, or Austria, was a constitutional monarchy and great power in Central Europe between 1867 and 1918. It was formed with the Austro-Hungarian Compromise of ...
Evidenzbureau
The k.u.k. Evidenzbureau (modernized spelling ''Evidenzbüro'') was the directorate of military intelligence of the Austro-Hungarian Empire, headquartered in Vienna, Austria.
Foundation
Founded in 1850 as the first permanent military intell ...
was able to comprehensively monitor the progress of the Italian army during the Italo-Turkish War
The Italo-Turkish or Turco-Italian War ( tr, Trablusgarp Savaşı, "Tripolitanian War", it, Guerra di Libia, "War of Libya") was fought between the Kingdom of Italy and the Ottoman Empire from 29 September 1911, to 18 October 1912. As a result o ...
of 1911 by monitoring the signals that were sent by a series of relay stations from Tripoli
Tripoli or Tripolis may refer to:
Cities and other geographic units Greece
*Tripoli, Greece, the capital of Arcadia, Greece
* Tripolis (region of Arcadia), a district in ancient Arcadia, Greece
* Tripolis (Larisaia), an ancient Greek city in ...
to Rome
, established_title = Founded
, established_date = 753 BC
, founder = King Romulus (legendary)
, image_map = Map of comune of Rome (metropolitan city of Capital Rome, region Lazio, Italy).svg
, map_caption ...
. In France, Deuxième Bureau
The Deuxième Bureau de l'État-major général ("Second Bureau of the General Staff") was France's external military intelligence agency from 1871 to 1940. It was dissolved together with the Third Republic upon the armistice with Germany. Howeve ...
of the Military General Staff was tasked with radio interception.
World War I
It was over the course of the War that the new method of intelligence collection -signals intelligence
Signals intelligence (SIGINT) is intelligence-gathering by interception of ''signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication ( ...
- reached maturity. The British in particular built up great expertise in the newly emerging field of signals intelligence and codebreaking.
Failure to properly protect its communications fatally compromised the Russian Army
The Russian Ground Forces (russian: Сухопутные войска �В Sukhoputnyye voyska V, also known as the Russian Army (, ), are the Army, land forces of the Russian Armed Forces.
The primary responsibilities of the Russian Gro ...
in its advance early in World War I and led to their disastrous defeat by the Germans under Ludendorff and Hindenburg at the Battle of Tannenberg
The Battle of Tannenberg, also known as the Second Battle of Tannenberg, was fought between Russia and Germany between 26 and 30 August 1914, the first month of World War I. The battle resulted in the almost complete destruction of the Russi ...
.
France had significant signals intelligence in World War I. Commandant Cartier developed a system of wireless masts, including one on the Eiffel Tower
The Eiffel Tower ( ; french: links=yes, tour Eiffel ) is a wrought-iron lattice tower on the Champ de Mars in Paris, France. It is named after the engineer Gustave Eiffel, whose company designed and built the tower.
Locally nicknamed "'' ...
to intercept German communications. The first such station was built as early as 1908, although was destroyed by flooding a few years afterward. In the early stages of the war, French intercepts were invaluable for military planning and provided the crucial intelligence to commander-in-chief Joseph Joffre
Joseph Jacques Césaire Joffre (12 January 1852 – 3 January 1931) was a French general who served as Commander-in-Chief of French forces on the Western Front from the start of World War I until the end of 1916. He is best known for regroupi ...
that enabled him to carry out the successful counterattack against the Germans at the Marne
The First Battle of the Marne was a battle of the First World War fought from 5 to 12 September 1914. It was fought in a collection of skirmishes around the Marne River Valley. It resulted in an Entente victory against the German armies in the ...
in September 1914.
In 1918, French intercept personnel captured a message written in the new ADFGVX cipher
In cryptography, the ADFGVX cipher was a manually applied field cipher used by the Imperial German Army during World War I. It was used to transmit messages secretly using wireless telegraphy. ADFGVX was in fact an extension of an earlier cipher ca ...
, which was cryptanalyzed by Georges Painvin
Georges Jean Painvin (; 28 January 1886 – 21 January 1980) was a French geologist and industrialist, best known as the cryptanalyst who broke the ADFGX/ADFGVX cipher used by the Germans during the First World War.
Early life
Painvin was born i ...
. This gave the Allies advance warning of the German 1918 Spring Offensive.
US communications monitoring of naval signals started in 1918, but was used first as an aid to naval and merchant navigation. In October 1918, just before the end of the war, the US Navy installed its first DF installation at its station at Bar Harbor, Maine
Bar Harbor is a resort town on Mount Desert Island in Hancock County, Maine, United States. As of the 2020 census, its population is 5,089. During the summer and fall seasons, it is a popular tourist destination and, until a catastrophic fire i ...
, soon joined by five other Atlantic coast stations, and then a second group of 14 installations. These stations, after the end of World War I, were not used immediately for intelligence. While there were 52 Navy medium wave (MF) DF stations in 1924, most of them had deteriorated.
Cracking the German naval codes
 By the start of the
By the start of the First World War
World War I (28 July 1914 11 November 1918), often abbreviated as WWI, was one of the deadliest global conflicts in history. Belligerents included much of Europe, the Russian Empire, the United States, and the Ottoman Empire, with fightin ...
, a worldwide commercial undersea communication cable
A submarine communications cable is a cable laid on the sea bed between land-based stations to carry telecommunication signals across stretches of ocean and sea. The first submarine communications cables laid beginning in the 1850s carried tel ...
network had been built up over the previous half-century, allowing nations to transmit information and instructions around the world. Techniques for intercepting these messages through ground returns were developed, so all cables running through hostile territory could in theory be intercepted.
On the declaration of war, one of Britain's first acts was to cut all German undersea cables. On the night of 3 August 1914, the cable ship ''Alert'' located and cut Germany's five trans-Atlantic cables, which ran down the English Channel
The English Channel, "The Sleeve"; nrf, la Maunche, "The Sleeve" (Cotentinais) or ( Jèrriais), (Guernésiais), "The Channel"; br, Mor Breizh, "Sea of Brittany"; cy, Môr Udd, "Lord's Sea"; kw, Mor Bretannek, "British Sea"; nl, Het Kana ...
. Soon after, the six cables running between Britain and Germany were cut. This forced the Germans to use either a telegraph line that connected through the British network and could be tapped, or through radio which the British could then intercept. The destruction of more secure wired communications, to improve the intelligence take, has been a regular practice since then. While one side may be able to jam the other's radio communications, the intelligence value of poorly secured radio may be so high that there is a deliberate decision not to interfere with enemy transmissions.
Although Britain could now intercept German communications, codes and ciphers were used to hide the meaning of the messages. Neither Britain nor Germany had any established organisations to decode and interpret the messages at the start of the war - the Royal Navy
The Royal Navy (RN) is the United Kingdom's naval warfare force. Although warships were used by English and Scottish kings from the early medieval period, the first major maritime engagements were fought in the Hundred Years' War against F ...
had only one wireless station for intercepting messages, at Stockton-on-Tees
Stockton-on-Tees, often simply referred to as Stockton, is a market town in the Borough of Stockton-on-Tees in County Durham, England. It is on the northern banks of the River Tees, part of the Teesside built-up area. The town had an estimated ...
.
However, installations belonging to the Post Office and the Marconi Company
The Marconi Company was a British telecommunications and engineering company that did business under that name from 1963 to 1987. Its roots were in the Wireless Telegraph & Signal Company founded by Italian inventor Guglielmo Marconi in 1897 ...
, as well as private individuals who had access to radio equipment, began recording messages from Germany. Realizing that the strange signals they were receiving were German naval communications, they brought them to the Admiralty. Rear-Admiral Henry Oliver
Admiral of the Fleet Sir Henry Francis Oliver, (22 January 1865 – 15 October 1965) was a Royal Navy officer. After serving in the Second Boer War as a navigating officer in a cruiser on the Cape of Good Hope and West Coast of Africa Station ...
appointed Sir Alfred Ewing to establish an interception and decryption service. Among its early recruits were Alastair Denniston
Commander Alexander "Alastair" Guthrie Denniston (1 December 1881 – 1 January 1961) was a Scottish codebreaker in Room 40, deputy head of the Government Code and Cypher School (GC&CS) and hockey player. Denniston was appointed operational he ...
, Frank Adcock
Sir Frank Ezra Adcock, (15 April 1886 – 22 February 1968) was a British classical historian who was Professor of Ancient History at the University of Cambridge between 1925 and 1951. In addition to his academic work, he also served as a c ...
, John Beazley
Sir John Davidson Beazley, (; 13 September 1885 – 6 May 1970) was a British classical archaeologist and art historian, known for his classification of Attic vases by artistic style. He was Professor of Classical Archaeology and Art at the Un ...
, Francis Birch, Walter Horace Bruford
Walter Horace Bruford, FBA (14 July 1894 – 28 June 1988) was a British scholar of German literature.
Walter Horace Bruford was born in Manchester in 1894. He was educated at Manchester Grammar School and then at St. John's College, Cambr ...
, William ''Nobby'' Clarke, Frank Cyril Tiarks
Frank Cyril Tiarks OBE (also known as F. C. Tiarks) (9 July 1874 – 7 April 1952) was an English banker.
Family
He was son of Henry Frederick Tiarks (23 December 1832 - 18 October 1911), banker, partner in J. Henry Schröder & Co. in Lond ...
and Dilly Knox
Alfred Dillwyn "Dilly" Knox, CMG (23 July 1884 – 27 February 1943) was a British classics scholar and papyrologist at King's College, Cambridge and a codebreaker. As a member of the Room 40 codebreaking unit he helped decrypt the Zimm ...
. In early November 1914 Captain William Hall was appointed as the new Director of the Intelligence division to replace Oliver.
 A similar organisation had begun in the Military Intelligence department of the
A similar organisation had begun in the Military Intelligence department of the War Office
The War Office was a department of the British Government responsible for the administration of the British Army between 1857 and 1964, when its functions were transferred to the new Ministry of Defence (MoD). This article contains text from ...
, which become known as MI1b
MI1 or British ''Military Intelligence, Section 1'' was a department of the British Directorate of Military Intelligence, part of the War Office. It was set up during World War I. It contained "C&C", which was responsible for code breaking.
I ...
, and Colonel Macdonagh proposed that the two organisations should work together. Little success was achieved except to organise a system for collecting and filing messages until the French obtained copies of German military ciphers. The two organisations operated in parallel, decoding messages concerning the Western Front. A friend of Ewing's, a barrister by the name of Russell Clarke, plus a friend of his, Colonel Hippisley, approached Ewing to explain that they had been intercepting German messages. Ewing arranged for them to operate from the coastguard station at Hunstanton in Norfolk
Norfolk () is a ceremonial and non-metropolitan county in East Anglia in England. It borders Lincolnshire to the north-west, Cambridgeshire to the west and south-west, and Suffolk to the south. Its northern and eastern boundaries are the No ...
. They formed the core of the interception service known as 'Y' service, together with the post office
A post office is a public facility and a retailer that provides mail services, such as accepting letters and parcels, providing post office boxes, and selling postage stamps, packaging, and stationery. Post offices may offer additional serv ...
and Marconi stations, which grew rapidly to the point it could intercept almost all official German messages.
In a stroke of luck, the SKM codebook was obtained from the German Light cruiser ''Magdeburg'', which ran aground on the island of Odensholm
Osmussaar ( sv, Odensholm, german: Odinsholm) is an Estonian island situated in the mouth of the Gulf of Finland in the Baltic Sea, 7.5 km off the Estonian mainland. Administratively the island is part of Lääne-Nigula Parish in Lääne ...
off the coast of Russian-controlled Estonia
Estonia, formally the Republic of Estonia, is a country by the Baltic Sea in Northern Europe. It is bordered to the north by the Gulf of Finland across from Finland, to the west by the sea across from Sweden, to the south by Latvia, a ...
. The books were formally handed over to the First Lord, Winston Churchill, on 13 October. The SKM by itself was incomplete as a means of decoding messages since they were normally enciphered as well as coded, and those that could be understood were mostly weather reports. An entry into solving the problem was found from a series of messages transmitted from the German Norddeich transmitter, which were all numbered sequentially and then re-enciphered. The cipher was broken, in fact broken twice as it was changed a few days after it was first solved, and a general procedure for interpreting the messages determined.
A second important code - the Handelsverkehrsbuch (HVB) codebook used by the German navy - was captured at the very start of the war from the German-Australian steamer ''Hobart'', seized off Port Philip Heads near Melbourne on 11 August 1914. The code was used particularly by light forces such as patrol boats, and for routine matters such as leaving and entering harbour. The code was used by U-boats, but with a more complex key. A third codebook was recovered following the sinking of German destroyer SMS ''S119'' in a battle off Texel island. It contained a copy of the Verkehrsbuch (VB) codebook, intended for use in cables sent overseas to warships and naval attachés, embassies and consulates. Its greatest importance during the war was that it allowed access to communications between naval attachés in Berlin, Madrid, Washington, Buenos Aires, Peking, and Constantinople.
The German fleet was in the habit each day of wirelessing the exact position of each ship and giving regular position reports when at sea. It was possible to build up a precise picture of the normal operation of the High Seas Fleet
The High Seas Fleet (''Hochseeflotte'') was the battle fleet of the German Imperial Navy and saw action during the First World War. The formation was created in February 1907, when the Home Fleet (''Heimatflotte'') was renamed as the High Seas ...
, indeed to infer from the routes they chose where defensive minefields had been place and where it was safe for ships to operate. Whenever a change to the normal pattern was seen, it immediately signalled that some operation was about to take place and a warning could be given. Detailed information about submarine movements was also available.
Direction finding
 The use of radio receiving equipment to pinpoint the location of the transmitter was also developed during the war.
Captain
The use of radio receiving equipment to pinpoint the location of the transmitter was also developed during the war.
Captain H.J. Round
Captain Henry Joseph Round (2 June 1881 – 17 August 1966) was an English engineer and one of the early pioneers of radio. He was the first to report observation of electroluminescence from a solid state diode, leading to the discovery of the ...
working for Marconi, began carrying out experiments with direction finding radio equipment for the army in France in 1915. Hall
In architecture, a hall is a relatively large space enclosed by a roof and walls. In the Iron Age and early Middle Ages in northern Europe, a mead hall was where a lord and his retainers ate and also slept. Later in the Middle Ages, the gr ...
instructed him to build a direction finding system for the navy. This was sited at Lowestoft
Lowestoft ( ) is a coastal town and civil parish in the East Suffolk district of Suffolk, England.OS Explorer Map OL40: The Broads: (1:25 000) : . As the most easterly UK settlement, it is north-east of London, north-east of Ipswich and sou ...
and other stations were built at Lerwick
Lerwick (; non, Leirvik; nrn, Larvik) is the main town and port of the Shetland archipelago, Scotland. Shetland's only burgh, Lerwick had a population of about 7,000 residents in 2010.
Centred off the north coast of the Scottish mainland ...
, Aberdeen
Aberdeen (; sco, Aiberdeen ; gd, Obar Dheathain ; la, Aberdonia) is a city in North East Scotland, and is the third most populous city in the country. Aberdeen is one of Scotland's 32 local government council areas (as Aberdeen City), and ...
, York
York is a cathedral city with Roman origins, sited at the confluence of the rivers Ouse and Foss in North Yorkshire, England. It is the historic county town of Yorkshire. The city has many historic buildings and other structures, such as a ...
, Flamborough Head
Flamborough Head () is a promontory, long on the Yorkshire coast of England, between the Filey and Bridlington bays of the North Sea. It is a chalk headland, with sheer white cliffs. The cliff top has two standing lighthouse towers, the olde ...
and Birchington
Birchington-on-Sea is a village in the Thanet district in Kent, England, with a population of 9,961.
The village forms part of the civil parish of Birchington. It lies on the coast facing the North Sea, east of the Thames Estuary, between the ...
and by May 1915 the Admiralty was able to track German submarines crossing the North Sea. Some of these stations also acted as 'Y' stations to collect German messages, but a new section was created within Room 40 to plot the positions of ships from the directional reports.
Room 40 had very accurate information on the positions of German ships, but the Admiralty priority remained to keep the existence of this knowledge secret. From June 1915 the regular intelligence reports of ship positions ceased to be passed to all flag officers, but only to Admiral Jellicoe himself. Similarly, he was the only person to receive accurate charts of German minefields prepared from Room 40 information. No attempts were made by the German fleet to restrict its use of wireless until 1917, and then only in response to perceived British use of direction finding, not because it believed messages were being decoded.
It became increasingly clear, that as important as the decrypts were, it was of equal importance to accurately analyse the information provided. An illustration of this was provided by someone at the Admiralty who knew a little too much detail about SIGINT without fully understanding it. He asked the analysts where call sign "DK" was located, which was that used by the German commander when in harbour. The analysts answered his question precisely, telling him that it was "in the Jade River". Unfortunately the High Seas Fleet commander used a different identifier ''when at sea'', going so far as to transfer the same wireless operator ashore so the messages from the harbour would sound the same. The misinformation was passed to Jellicoe commanding the British fleet, who acted accordingly and proceeded at a slower speed to preserve fuel. The battle of Jutland
The Battle of Jutland (german: Skagerrakschlacht, the Battle of the Skagerrak) was a naval battle fought between Britain's Royal Navy Grand Fleet, under Admiral John Jellicoe, 1st Earl Jellicoe, Sir John Jellicoe, and the Imperial German Navy ...
was eventually fought but its lateness in the day allowed the enemy to escape.
Jellicoe's faith in cryptographic intelligence was also shaken by a decrypted report that placed the German cruiser SMS Regensburg
SMS ''Regensburg'' was a light cruiser of the built by the German ''Kaiserliche Marine'' (Imperial Navy). She had one sister ship, . The ship was built by the AG Weser shipyard in Bremen, laid down in 1912, launched in April 1914, and commiss ...
near him, during the Battle of Jutland
The Battle of Jutland (german: Skagerrakschlacht, the Battle of the Skagerrak) was a naval battle fought between Britain's Royal Navy Grand Fleet, under Admiral John Jellicoe, 1st Earl Jellicoe, Sir John Jellicoe, and the Imperial German Navy ...
. It turned out that the navigator on the Ravensburg was off by in his position calculation. During Jutland, there was limited use of direction finding on fleet vessels, but most information came from shore stations. A whole string of messages were intercepted during the night indicating with high reliability how the German fleet intended to make good its escape, but the brief summary which was passed to Jellicoe failed to convince him of its accuracy in light of the other failures during the day.
Zimmermann Telegram & Other Successes
 Room 40 played an important role in several naval engagements during the war, notably in detecting major German sorties into the
Room 40 played an important role in several naval engagements during the war, notably in detecting major German sorties into the North Sea
The North Sea lies between Great Britain, Norway, Denmark, Germany, the Netherlands and Belgium. An epeiric sea on the European continental shelf, it connects to the Atlantic Ocean through the English Channel in the south and the Norwegian S ...
. The battle of Dogger Bank was won in no small part due to the intercepts that allowed the Navy to position its ships in the right place. "Warned of a new German raid n England
N, or n, is the fourteenth letter in the Latin alphabet, used in the modern English alphabet, the alphabets of other western European languages and others worldwide. Its name in English is ''en'' (pronounced ), plural ''ens''.
History
...
on the night of 23–24 January, by radio intercepts, dmiral Sir DavidBeatty’s force made a rendezvous off the Dogger Bank... The outnumbered Germans turned in flight. ... the Kaiser, fearful of losing capital ships, ordered his navy to avoid all further risks."
It played a vital role in subsequent naval clashes, including at the Battle of Jutland
The Battle of Jutland (german: Skagerrakschlacht, the Battle of the Skagerrak) was a naval battle fought between Britain's Royal Navy Grand Fleet, under Admiral John Jellicoe, 1st Earl Jellicoe, Sir John Jellicoe, and the Imperial German Navy ...
as the British fleet was sent out to intercept them. The direction-finding capability allowed for the tracking and location of German ships, submarines and Zeppelin
A Zeppelin is a type of rigid airship named after the German inventor Count Ferdinand von Zeppelin () who pioneered rigid airship development at the beginning of the 20th century. Zeppelin's notions were first formulated in 1874Eckener 1938, pp ...
s. Intercepts were also able to prove beyond doubt that the German high command had authorized the sinking of the ''Lusitania
Lusitania (; ) was an ancient Iberian Roman province located where modern Portugal (south of the Douro river) and
a portion of western Spain (the present Extremadura and the province of Salamanca) lie. It was named after the Lusitani or Lusita ...
'' in May 1915, despite the vociferous German denials at the time. The system was so successful, that by the end of the war over 80 million words, comprising the totality of German wireless transmission over the course of the war had been intercepted by the operators of the Y-stations
The "Y" service was a network of British signals intelligence collection sites, the Y-stations. The service was established during the First World War and used again during the Second World War. The sites were operated by a range of agencies inc ...
and decrypted. However its most astonishing success was in decrypting the Zimmermann Telegram, a telegram
Telegraphy is the long-distance transmission of messages where the sender uses symbolic codes, known to the recipient, rather than a physical exchange of an object bearing the message. Thus flag semaphore is a method of telegraphy, whereas p ...
from the German Foreign Office sent via Washington to its ambassador
An ambassador is an official envoy, especially a high-ranking diplomat who represents a state and is usually accredited to another sovereign state or to an international organization as the resident representative of their own government or sov ...
Heinrich von Eckardt
Heinrich von Eckardt (20 July 1861, in Riga, Russian Empire – 3 March 1944, in Jena, Germany) was a Baltic German diplomat in the service of the German Empire.
Life and work
After studying jurisprudence at the University of Jena from 1881 to 18 ...
in Mexico
Mexico (Spanish: México), officially the United Mexican States, is a country in the southern portion of North America. It is bordered to the north by the United States; to the south and west by the Pacific Ocean; to the southeast by Guatema ...
.
In the telegram's plaintext
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. This usually refers to data that is transmitted or stored unencrypted.
Overview
With the advent of comp ...
, Nigel de Grey
Nigel de Grey (27 March 1886 – 25 May 1951) was a British codebreaker. Son of the rector of Copdock, Suffolk, and grandson of the 5th Lord Walsingham, he was educated at Eton College and became fluent in French and German. In 1907 he ...
and William Montgomery learned of the German Foreign Minister Arthur Zimmermann
Arthur Zimmermann (5 October 1864 – 6 June 1940) was State Secretary for Foreign Affairs of the German Empire from 22 November 1916 until his resignation on 6 August 1917. His name is associated with the Zimmermann Telegram during World War ...
's offer to Mexico of United States
The United States of America (U.S.A. or USA), commonly known as the United States (U.S. or US) or America, is a country primarily located in North America. It consists of 50 states, a federal district, five major unincorporated territorie ...
' territories of Arizona, New Mexico, and Texas as an enticement to join the war as a German ally. The telegram was passed to the U.S. by Captain Hall, and a scheme was devised (involving a still unknown agent in Mexico and a burglary) to conceal how its plaintext
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. This usually refers to data that is transmitted or stored unencrypted.
Overview
With the advent of comp ...
had become available and also how the U.S. had gained possession of a copy. The telegram was made public by the United States, which declared war on Germany on 6 April 1917, entering the war on the Allied side.
Interwar period
With the importance of interception and decryption firmly established by the wartime experience, countries established permanent agencies dedicated to this task in the interwar period. These agencies carried out substantial SIGINT work between the World Wars, although the secrecy surrounding it was extreme. While the work carried out was primarily COMINT,ELINT
Signals intelligence (SIGINT) is intelligence-gathering by interception of ''signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication ( ...
also emerged, with the development of radar
Radar is a detection system that uses radio waves to determine the distance (''ranging''), angle, and radial velocity of objects relative to the site. It can be used to detect aircraft, ships, spacecraft, guided missiles, motor vehicles, w ...
in the 1930s.
United Kingdom
In 1919, the British Cabinet's Secret Service Committee, chaired byLord Curzon
George Nathaniel Curzon, 1st Marquess Curzon of Kedleston, (11 January 1859 – 20 March 1925), styled Lord Curzon of Kedleston between 1898 and 1911 and then Earl Curzon of Kedleston between 1911 and 1921, was a British Conservative statesman ...
, recommended that a peace-time codebreaking agency should be created, a task given to the then- Director of Naval Intelligence, Hugh Sinclair
Admiral Sir Hugh Francis Paget Sinclair, (18 August 1873 – 4 November 1939), known as Quex Sinclair, was a British intelligence officer. He was Director of British Naval Intelligence between 1919 and 1921, and he subsequently helped to set ...
. Sinclair merged staff from the British Army's MI1b
MI1 or British ''Military Intelligence, Section 1'' was a department of the British Directorate of Military Intelligence, part of the War Office. It was set up during World War I. It contained "C&C", which was responsible for code breaking.
I ...
and Royal Navy's Room 40
Room 40, also known as 40 O.B. (old building; officially part of NID25), was the cryptanalysis section of the British Admiralty during the First World War.
The group, which was formed in October 1914, began when Rear-Admiral Henry Oliver, the ...
into the first peace-time codebreaking agency: the Government Code and Cypher School
Government Communications Headquarters, commonly known as GCHQ, is an intelligence and security organisation responsible for providing signals intelligence (SIGINT) and information assurance (IA) to the government and armed forces of the Uni ...
(GC&CS). The organization initially consisted of around 25–30 officers and a similar number of clerical staff. It was titled the "Government Code and Cypher School", a cover-name chosen by Victor Forbes of the Foreign Office
Foreign may refer to:
Government
* Foreign policy, how a country interacts with other countries
* Ministry of Foreign Affairs, in many countries
** Foreign Office, a department of the UK government
** Foreign office and foreign minister
* Unit ...
.
Alastair Denniston
Commander Alexander "Alastair" Guthrie Denniston (1 December 1881 – 1 January 1961) was a Scottish codebreaker in Room 40, deputy head of the Government Code and Cypher School (GC&CS) and hockey player. Denniston was appointed operational he ...
, who had been a leading member of Room 40, was appointed as its operational head. It was initially under the control of the Admiralty
Admiralty most often refers to:
*Admiralty, Hong Kong
*Admiralty (United Kingdom), military department in command of the Royal Navy from 1707 to 1964
*The rank of admiral
*Admiralty law
Admiralty can also refer to:
Buildings
* Admiralty, Traf ...
, and located in Watergate House, Adelphi, London. Its public function was "to advise as to the security of codes and cyphers used by all Government departments and to assist in their provision", but also had a secret directive to "study the methods of cypher communications used by foreign powers". GC&CS officially formed on 1 November 1919, and produced its first decrypt on 19 October.
By 1922, the main focus of GC&CS was on diplomatic traffic, with "no service traffic ever worth circulating" and so, at the initiative of Lord Curzon, it was transferred from the Admiralty to the Foreign Office
Foreign may refer to:
Government
* Foreign policy, how a country interacts with other countries
* Ministry of Foreign Affairs, in many countries
** Foreign Office, a department of the UK government
** Foreign office and foreign minister
* Unit ...
. GC&CS came under the supervision of Hugh Sinclair, who by 1923 was both the Chief of SIS and Director of GC&CS. In 1925, both organisations were co-located on different floors of Broadway Buildings, opposite St. James's Park
St James's Park is a park in the City of Westminster, central London. It is at the southernmost tip of the St James's area, which was named after a leper hospital dedicated to St James the Less. It is the most easterly of a near-continuous ch ...
. Messages decrypted by GC&CS were distributed in blue-jacketed files that became known as "BJs".
In the 1920s, GC&CS was successfully reading Soviet Union diplomatic ciphers. However, in May 1927, during a row over clandestine Soviet support for the General Strike
A general strike refers to a strike action in which participants cease all economic activity, such as working, to strengthen the bargaining position of a trade union or achieve a common social or political goal. They are organised by large co ...
and the distribution of subversive propaganda, Prime Minister Stanley Baldwin
Stanley Baldwin, 1st Earl Baldwin of Bewdley, (3 August 186714 December 1947) was a British Conservative Party politician who dominated the government of the United Kingdom between the world wars, serving as prime minister on three occasions, ...
made details from the decrypts public.
By 1940, GC&CS was working on the diplomatic codes and ciphers of 26 countries, tackling over 150 diplomatic cryptosystems.
Germany
From the mid-twenties, German Military IntelligenceAbwehr
The ''Abwehr'' (German for ''resistance'' or ''defence'', but the word usually means ''counterintelligence'' in a military context; ) was the German military-intelligence service for the ''Reichswehr'' and the ''Wehrmacht'' from 1920 to 1944. A ...
began intercepting and cryptanalyzing diplomatic traffic. Under Hermann Göring
Hermann Wilhelm Göring (or Goering; ; 12 January 1893 – 15 October 1946) was a German politician, military leader and convicted war criminal. He was one of the most powerful figures in the Nazi Party, which ruled Germany from 1933 to 1 ...
, the Nazi Research Bureau (''Forschungsamt'' or "FA") had units for intercepting domestic and international communications. The FA was penetrated by a French spy in the 1930s, but the traffic grew to a point that it could not easily be forwarded.
In addition to intercept stations in Germany, the FA established an intercept station in Berne, Switzerland. German code breaking penetrated most cryptosystems, other than the UK and US. German Condor Legion
The Condor Legion (german: Legion Condor) was a unit composed of military personnel from the air force and army of Nazi Germany, which served with the Nationalist faction during the Spanish Civil War of July 1936 to March 1939. The Condor Legio ...
personnel in the Spanish Civil War ran COMINT against their opponents.
United States
The US Cipher Bureau was established in 1919 and achieved some success at theWashington Naval Conference
The Washington Naval Conference was a disarmament conference called by the United States and held in Washington, DC from November 12, 1921 to February 6, 1922. It was conducted outside the auspices of the League of Nations. It was attended by nine ...
in 1921, through cryptanalysis by Herbert Yardley. Secretary of War Henry L. Stimson
Henry Lewis Stimson (September 21, 1867 – October 20, 1950) was an American statesman, lawyer, and Republican Party politician. Over his long career, he emerged as a leading figure in U.S. foreign policy by serving in both Republican and D ...
closed the US Cipher Bureau in 1929 with the words "Gentlemen do not read each other's mail."
Luckily for US COMINT, the Army offered a home to William Friedman
William Frederick Friedman (September 24, 1891 – November 12, 1969) was a US Army cryptographer who ran the research division of the Army's Signal Intelligence Service (SIS) in the 1930s, and parts of its follow-on services into the 1950s. In ...
after Stimson closed the Yardley operation. There, largely manual cylindrical and strip ciphers were developed, but, as a result of Friedman's advances in cryptanalysis, machine ciphers became a priority, such as the M134, also known as the SIGABA
In the history of cryptography, the ECM Mark II was a cipher machine used by the United States for message encryption from World War II until the 1950s. The machine was also known as the SIGABA or Converter M-134 by the Army, or CSP-888/889 by th ...
. While the SIGABA was a rotor machine
In cryptography, a rotor machine is an electro-mechanical stream cipher device used for encrypting and decrypting messages. Rotor machines were the cryptographic state-of-the-art for much of the 20th century; they were in widespread use in the 19 ...
like the German Enigma machine, it was never known to be cracked. It was replaced by electronic encryption devices.
The American Sigint effort began in the early 1930s with mounting tensions with the Japanese. The Navy
A navy, naval force, or maritime force is the branch of a nation's armed forces principally designated for naval warfare, naval and amphibious warfare; namely, lake-borne, riverine, littoral zone, littoral, or ocean-borne combat operations and ...
started implementing high frequency
High frequency (HF) is the ITU designation for the range of radio frequency electromagnetic waves (radio waves) between 3 and 30 megahertz (MHz). It is also known as the decameter band or decameter wave as its wavelengths range from one to ten ...
DF (HF/DF) at eleven planned locations, primarily on the Atlantic Coast. The first operational intercept came from what would later be called Station CAST Station CAST was the United States Navy signals monitoring and cryptographic intelligence fleet radio unit at Cavite Navy Yard in the Philippines, until Cavite was captured by the Japanese forces in 1942, during World War II. It was an important p ...
, at Cavite
Cavite, officially the Province of Cavite ( tl, Lalawigan ng Kabite; Chavacano: ''Provincia de Cavite''), is a province in the Philippines located in the Calabarzon region in Luzon. Located on the southern shores of Manila Bay and southwest ...
in the Philippines. In July 1939, the function turned from training and R&D to operations, and the Navy officially established a Strategic Tracking Organization under a Direction Finder Policy.
By December 1940, the Navy's communication organization, OP-20-G
OP-20-G or "Office of Chief Of Naval Operations (OPNAV), 20th Division of the Office of Naval Communications, G Section / Communications Security", was the U.S. Navy's signals intelligence and cryptanalysis group during World War II. Its mission ...
, had used HF/DF on German surface vessels and submarines. Training continued and cooperation with the British began. In April 1941, the British gave the US Navy a sample of their best HF/DF set from Marconi.
World War II
The use of SIGINT had even greater implications duringWorld War II
World War II or the Second World War, often abbreviated as WWII or WW2, was a world war that lasted from 1939 to 1945. It involved the vast majority of the world's countries—including all of the great powers—forming two opposin ...
. The combined effort of intercepts and cryptanalysis for the whole of the British forces in World War II came under the code name "Ultra" managed from Government Code and Cypher School
Government Communications Headquarters, commonly known as GCHQ, is an intelligence and security organisation responsible for providing signals intelligence (SIGINT) and information assurance (IA) to the government and armed forces of the Uni ...
at Bletchley Park
Bletchley Park is an English country house and estate in Bletchley, Milton Keynes ( Buckinghamshire) that became the principal centre of Allied code-breaking during the Second World War. The mansion was constructed during the years following ...
. By 1943, such was the extent of penetration of Axis communications and the speed and efficiency of distribution of the resulting intelligence, messages sometimes reached allied commanders in the field before their intended recipients. This advantage failed only when the German ground forces retreated within their own borders and they began using secure landline communications. For this reason, the Battle of the Bulge
The Battle of the Bulge, also known as the Ardennes Offensive, was the last major German offensive (military), offensive military campaign, campaign on the Western Front (World War II), Western Front during World War II. The battle lasted fr ...
took the allies completely by surprise.
A true world war, SIGINT still tended to be separate in the various theaters. Communications security, on the part of the Allies, was more centralized. From the Allied perspective, the critical theater-level perspectives were the Ultra SIGINT against the Germans in the European theater (including the Battle of the Atlantic
The Battle of the Atlantic, the longest continuous military campaign in World War II, ran from 1939 to the defeat of Nazi Germany in 1945, covering a major part of the naval history of World War II. At its core was the Allied naval blockade ...
, the Mediterranean Theater of Operations
The Mediterranean Theater of Operations, United States Army (MTOUSA), originally called the North African Theater of Operations, United States Army (NATOUSA), was a military formation of the United States Army that supervised all U.S. Army forc ...
, and MAGIC
Magic or Magick most commonly refers to:
* Magic (supernatural), beliefs and actions employed to influence supernatural beings and forces
* Ceremonial magic, encompasses a wide variety of rituals of magic
* Magical thinking, the belief that unrela ...
against the Japanese in the Pacific Theater and the China-Burma-India theater.
The entire German system of high command suffered from Hitler
Adolf Hitler (; 20 April 188930 April 1945) was an Austrian-born German politician who was dictator of Germany from 1933 until his death in 1945. He rose to power as the leader of the Nazi Party, becoming the chancellor in 1933 and then ...
's deliberate fragmenting of authority, with Party, State, and military organizations competing for power. Hermann Göring
Hermann Wilhelm Göring (or Goering; ; 12 January 1893 – 15 October 1946) was a German politician, military leader and convicted war criminal. He was one of the most powerful figures in the Nazi Party, which ruled Germany from 1933 to 1 ...
also sought power for its own sake, but was much less effective as the war went on and he became more focused on personal status and pleasure.
Germany enjoyed some SIGINT success against the Allies, especially with the Merchant Code and, early in the war, reading American attaché traffic. German air intelligence, during the Battle of Britain
The Battle of Britain, also known as the Air Battle for England (german: die Luftschlacht um England), was a military campaign of the Second World War, in which the Royal Air Force (RAF) and the Fleet Air Arm (FAA) of the Royal Navy defende ...
, suffered from the structural problem that subordinated intelligence to operations. Operations officers often made conclusions that best fit their plans, rather than fitting conclusions to information.
In contrast, British air intelligence was systematic, from the highest-level, most sensitive Ultra to significant intelligence product from traffic analysis and cryptanalysis of low-level systems. Fortunately for the British, German aircraft communications discipline was poor, and the Germans rarely changed call signs, allowing the British to draw accurate inferences about the air order of battle.
Japan
Japan ( ja, 日本, or , and formally , ''Nihonkoku'') is an island country in East Asia. It is situated in the northwest Pacific Ocean, and is bordered on the west by the Sea of Japan, while extending from the Sea of Okhotsk in the north ...
was the least effective of the major powers in SIGINT. In addition to the official Allies and Axis battle of signals, there was a growing interest in Soviet espionage communications, which continued after the war.
British SIGINT
 The British
The British Government Code and Cypher School
Government Communications Headquarters, commonly known as GCHQ, is an intelligence and security organisation responsible for providing signals intelligence (SIGINT) and information assurance (IA) to the government and armed forces of the Uni ...
moved to Bletchley Park
Bletchley Park is an English country house and estate in Bletchley, Milton Keynes ( Buckinghamshire) that became the principal centre of Allied code-breaking during the Second World War. The mansion was constructed during the years following ...
, in Milton Keynes
Milton Keynes ( ) is a city and the largest settlement in Buckinghamshire, England, about north-west of London. At the 2021 Census, the population of its urban area was over . The River Great Ouse forms its northern boundary; a tributary ...
, Buckinghamshire
Buckinghamshire (), abbreviated Bucks, is a ceremonial county in South East England that borders Greater London to the south-east, Berkshire to the south, Oxfordshire to the west, Northamptonshire to the north, Bedfordshire to the north-ea ...
, at the beginning of the Second World War
World War II or the Second World War, often abbreviated as WWII or WW2, was a world war that lasted from 1939 to 1945. It involved the vast majority of the world's countries—including all of the great powers—forming two opposin ...
. A key advantage was Bletchley's geographical centrality.
Commander Alastair Denniston
Commander Alexander "Alastair" Guthrie Denniston (1 December 1881 – 1 January 1961) was a Scottish codebreaker in Room 40, deputy head of the Government Code and Cypher School (GC&CS) and hockey player. Denniston was appointed operational he ...
was operational head of GC&CS. Key GC&CS cryptanalysts
Cryptanalysis (from the Greek ''kryptós'', "hidden", and ''analýein'', "to analyze") refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic s ...
who moved from London to Bletchley Park included John Tiltman
Brigadier John Hessell Tiltman, (25 May 1894 – 10 August 1982) was a British Army officer who worked in intelligence, often at or with the Government Code and Cypher School (GC&CS) starting in the 1920s. His intelligence work was largely conn ...
, Dillwyn "Dilly" Knox, Josh Cooper, and Nigel de Grey
Nigel de Grey (27 March 1886 – 25 May 1951) was a British codebreaker. Son of the rector of Copdock, Suffolk, and grandson of the 5th Lord Walsingham, he was educated at Eton College and became fluent in French and German. In 1907 he ...
. These people had a variety of backgroundslinguists, chess champions, and crossword experts were common, and in Knox's case papyrology
Papyrology is the study of manuscripts of ancient literature, correspondence, legal archives, etc., preserved on portable media from antiquity, the most common form of which is papyrus, the principal writing material in the ancient civilizations ...
. In one 1941 recruiting stratagem ''The Daily Telegraph
''The Daily Telegraph'', known online and elsewhere as ''The Telegraph'', is a national British daily broadsheet newspaper published in London by Telegraph Media Group and distributed across the United Kingdom and internationally.
It was fo ...
'' was asked to organise a crossword competition, after which promising contestants were discreetly approached about "a particular type of work as a contribution to the war effort".
Denniston recognised, however, that the enemy's use of electromechanical cipher machines meant that formally trained mathematicians would be needed as well; Oxford's Peter Twinn
Peter Frank George Twinn (9 January 1916 – 29 October 2004Dan van der Vat, "Obituary: Peter Twinn", ''The Guardian'', 20 November 2004) was a British mathematician, Second World War Cryptanalysis, codebreaker and entomologist. The first prof ...
joined GC&CS in February 1939; Cambridge's Alan Turing
Alan Mathison Turing (; 23 June 1912 – 7 June 1954) was an English mathematician, computer scientist, logician, cryptanalyst, philosopher, and theoretical biologist. Turing was highly influential in the development of theoretical com ...
and Gordon Welchman
William Gordon Welchman (15 June 1906 – 8 October 1985) was a British mathematician. During World War II, he worked at Britain's secret codebreaking centre, "Station X" at Bletchley Park, where he was one of the most important contributors. ...
began training in 1938 and reported to Bletchley the day after war was declared, along with John Jeffreys. Later-recruited cryptanalysts included the mathematicians Derek Taunt
Derek Roy Taunt (16 November 1917 (Note 1) – 15 July 2004) was a British mathematician who worked as a codebreaker during World War II at Bletchley Park.
Taunt attended Enfield Grammar, then the City of London School. He studied mathemat ...
, Jack Good, Bill Tutte
William Thomas Tutte OC FRS FRSC (; 14 May 1917 – 2 May 2002) was an English and Canadian codebreaker and mathematician. During the Second World War, he made a brilliant and fundamental advance in cryptanalysis of the Lorenz cipher, a majo ...
, and Max Newman
Maxwell Herman Alexander Newman, FRS, (7 February 1897 – 22 February 1984), generally known as Max Newman, was a British mathematician and codebreaker. His work in World War II led to the construction of Colossus, the world's first operatio ...
; historian Harry Hinsley
Sir Francis Harry Hinsley, (26 November 1918 – 16 February 1998) was an English historian and cryptanalyst. He worked at Bletchley Park during the Second World War and wrote widely on the history of international relations and British Int ...
, and chess champions Hugh Alexander and Stuart Milner-Barry
Sir Philip Stuart Milner-Barry (20 September 1906 – 25 March 1995) was a British chess player, chess writer, World War II codebreaker and civil servant. He represented England in chess both before and after World War II. He worked at Bletch ...
.
Joan Clarke
Joan Elisabeth Lowther Murray, MBE (''née'' Clarke; 24 June 1917 – 4 September 1996) was an English cryptanalyst and numismatist best known for her work as a code-breaker at Bletchley Park during the Second World War. Although she did not ...
(eventually deputy head of Hut 8
Hut 8 was a section in the Government Code and Cypher School (GC&CS) at Bletchley Park (the British World War II codebreaking station, located in Buckinghamshire) tasked with solving German naval (Kriegsmarine) Enigma messages. The section was l ...
) was one of the few women employed at Bletchley as a full-fledged cryptanalyst.
Properly used, the German Enigma and Lorenz cipher
The Lorenz SZ40, SZ42a and SZ42b were German rotor stream cipher machines used by the German Army during World War II. They were developed by C. Lorenz AG in Berlin. The model name ''SZ'' was derived from ''Schlüssel-Zusatz'', meaning ''cipher ...
s should have been virtually unbreakable, but flaws in German cryptographic procedures, and poor discipline among the personnel carrying them out, created vulnerabilities which made Bletchley's attacks just barely feasible.
These vulnerabilities, however, could have been remedied by relatively simple improvements in enemy procedures,
and such changes would certainly have been implemented had Germany any hint of Bletchley's success.
Thus the intelligence Bletchley produced was considered wartime Britain's "Ultra
adopted by British military intelligence in June 1941 for wartime signals intelligence obtained by breaking high-level encrypted enemy radio and teleprinter communications at the Government Code and Cypher School (GC&CS) at Bletchley Park. '' ...
secret"higher even than the normally highest classification ''Most Secret''and security was paramount.
Initially, a wireless
Wireless communication (or just wireless, when the context allows) is the transfer of information between two or more points without the use of an electrical conductor, optical fiber or other continuous guided medium for the transfer. The most ...
room was established at Bletchley Park.
It was set up in the mansion's water tower under the code name "Station X", a term now sometimes applied to the codebreaking efforts at Bletchley as a whole.
Due to the long radio aerials stretching from the wireless room, the radio station was moved from Bletchley Park to nearby Whaddon Hall
Whaddon Hall is a country house in Whaddon, Buckinghamshire. It is a Grade II listed building.
History
The first manor house was built on the site in the 11th century. The present house was built in 1820, replacing a house which was demolished i ...
to avoid drawing attention to the site.
Subsequently, other listening stationsthe Y-stations
The "Y" service was a network of British signals intelligence collection sites, the Y-stations. The service was established during the First World War and used again during the Second World War. The sites were operated by a range of agencies inc ...
, such as the ones at Chicksands
Chicksands is a village in the Central Bedfordshire district of Bedfordshire, England, and part of the civil parish of Campton and Chicksands, whose population in 2007 was estimated to be 2,510. By the 2011 census the figure was accurately place ...
in Bedfordshire, Beaumanor Hall
Beaumanor Hall is a stately home with a park in the small village of Woodhouse on the edge of the Charnwood Forest, near the town of Loughborough in Leicestershire, England. The present hall was built in 1842–8 by architect William Railton ...
, Leicestershire (where the headquarters of the War Office "Y" Group was located) and Beeston Hill Y Station in Norfolkgathered raw signals for processing at Bletchley.
Coded messages were taken down by hand and sent to Bletchley on paper by motorcycle despatch rider
A despatch rider (or dispatch) is a military messenger, mounted on horse or motorcycle (and occasionally in Egypt during World War I, on camels).
In the UK 'despatch rider' is also a term used for a motorcycle courier.
Despatch riders were use ...
s or (later) by teleprinter.
Bletchley's work was essential to defeating the U-boat
U-boats were naval submarines operated by Germany, particularly in the First and Second World Wars. Although at times they were efficient fleet weapons against enemy naval warships, they were most effectively used in an economic warfare role ...
s in the Battle of the Atlantic
The Battle of the Atlantic, the longest continuous military campaign in World War II, ran from 1939 to the defeat of Nazi Germany in 1945, covering a major part of the naval history of World War II. At its core was the Allied naval blockade ...
, and to the British naval victories in the Battle of Cape Matapan
The Battle of Cape Matapan ( el, Ναυμαχία του Ταινάρου) was a naval battle during the Second World War between the Allies, represented by the navies of the United Kingdom and Australia, and the Royal Italian navy, from 27 ...
and the Battle of North Cape
The Battle of the North Cape was a Second World War naval battle that occurred on 26 December 1943, as part of the Arctic campaign. The , on an operation to attack Arctic Convoys of war materiel from the Western Allies to the Soviet Union, was ...
. In 1941, Ultra exerted a powerful effect on the North African desert campaign against German forces under General Erwin Rommel
Johannes Erwin Eugen Rommel () (15 November 1891 – 14 October 1944) was a German field marshal during World War II. Popularly known as the Desert Fox (, ), he served in the ''Wehrmacht'' (armed forces) of Nazi Germany, as well as servi ...
. General Sir Claude Auchinleck
Field Marshal Sir Claude John Eyre Auchinleck, (21 June 1884 – 23 March 1981), was a British Army commander during the Second World War. He was a career soldier who spent much of his military career in India, where he rose to become Commande ...
wrote that were it not for Ultra, "Rommel would have certainly got through to Cairo". "Ultra
adopted by British military intelligence in June 1941 for wartime signals intelligence obtained by breaking high-level encrypted enemy radio and teleprinter communications at the Government Code and Cypher School (GC&CS) at Bletchley Park. '' ...
" decrypts featured prominently in the story of Operation SALAM
Operation Salam was a 1942 World War II military operation organised by the ''Abwehr'' under the command of the Hungarian desert explorer László Almásy. The mission was conceived in order to assist Panzer Army Africa by delivering two German ...
, László Almásy
László Ede Almásy de Zsadány et Törökszentmiklós ( hu, Almásy László Ede; ; 22 August/3 November 1895 – 22 March 1951) was a Hungarian aristocrat, motorist, desert explorer, aviator, Scout-leader and sportsman who served as the ...
's daring mission across the Libyan Desert
The Libyan Desert (not to be confused with the Libyan Sahara) is a geographical region filling the north-eastern Sahara Desert, from eastern Libya to the Western Desert of Egypt and far northwestern Sudan. On medieval maps, its use predates t ...
behind enemy lines in 1942. Prior to the Normandy landings
The Normandy landings were the landing operations and associated airborne operations on Tuesday, 6 June 1944 of the Allied invasion of Normandy in Operation Overlord during World War II. Codenamed Operation Neptune and often referred to as ...
on D-Day in June 1944, the Allies knew the locations of all but two of Germany's fifty-eight Western-front divisions.
Winston Churchill
Sir Winston Leonard Spencer Churchill (30 November 187424 January 1965) was a British statesman, soldier, and writer who served as Prime Minister of the United Kingdom twice, from 1940 to 1945 Winston Churchill in the Second World War, dur ...
was reported to have told King George VI
George VI (Albert Frederick Arthur George; 14 December 1895 – 6 February 1952) was King of the United Kingdom and the Dominions of the British Commonwealth from 11 December 1936 until his death in 1952. He was also the last Emperor of Ind ...
: "It is thanks to the secret weapon of General Menzies, put into use on all the fronts, that we won the war!" Supreme Allied Commander, Dwight D. Eisenhower
Dwight David "Ike" Eisenhower (born David Dwight Eisenhower; ; October 14, 1890 – March 28, 1969) was an American military officer and statesman who served as the 34th president of the United States from 1953 to 1961. During World War II, ...
, at the end of the war, described Ultra as having been "decisive" to Allied victory. Official historian of British Intelligence in World War II Sir Harry Hinsley, argued that Ultra shortened the war "by not less than two years and probably by four years"; and that, in the absence of Ultra, it is uncertain how the war would have ended.
German codes
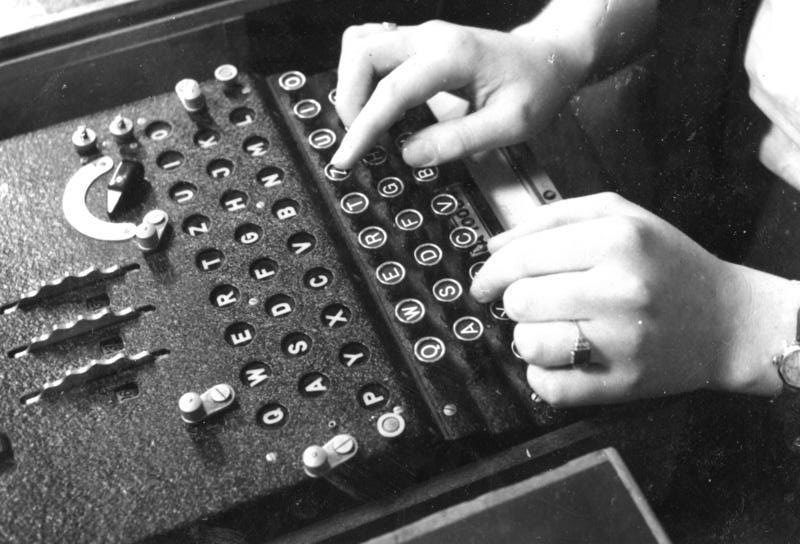 Most German messages decrypted at Bletchley were produced by one or another version of the
Most German messages decrypted at Bletchley were produced by one or another version of the Enigma
Enigma may refer to:
*Riddle, someone or something that is mysterious or puzzling
Biology
*ENIGMA, a class of gene in the LIM domain
Computing and technology
* Enigma (company), a New York-based data-technology startup
* Enigma machine, a family ...
cipher machine, but an important minority were produced by the even more complicated twelve-rotor Lorenz SZ42 on-line teleprinter cipher machine.
Five weeks before the outbreak of war, in Warsaw, Poland's Cipher Bureau revealed its achievements in breaking Enigma to astonished French and British personnel. The British used the Poles' information and techniques, and the Enigma clone sent to them in August 1939, which greatly increased their (previously very limited) success in decrypting Enigma messages.
The bombe
The bombe () was an electro-mechanical device used by British cryptologists to help decipher German Enigma-machine-encrypted secret messages during World War II. The US Navy and US Army later produced their own machines to the same functiona ...
was an electromechanical device whose function was to discover some of the daily settings of the Enigma machines on the various German military networks
Network, networking and networked may refer to:
Science and technology
* Network theory, the study of graphs as a representation of relations between discrete objects
* Network science, an academic field that studies complex networks
Mathematics
...
.
Its pioneering design was developed by Alan Turing
Alan Mathison Turing (; 23 June 1912 – 7 June 1954) was an English mathematician, computer scientist, logician, cryptanalyst, philosopher, and theoretical biologist. Turing was highly influential in the development of theoretical com ...
(with an important contribution from Gordon Welchman) and the machine was engineered by Harold 'Doc' Keen of the British Tabulating Machine Company
__NOTOC__
The British Tabulating Machine Company (BTM) was a firm which manufactured and sold Hollerith unit record equipment and other data-processing equipment. During World War II, BTM constructed some 200 "bombes", machines used at Bletchley P ...
.
Each machine was about high and wide, deep and weighed about a ton.
At its peak, GC&CS was reading approximately 4,000 messages per day. As a hedge against enemy attack most bombes were dispersed to installations at Adstock
''For the municipality in Quebec, see Adstock, Quebec''
Adstock is a village and civil parish about northwest of Winslow and southeast of Buckingham in the Aylesbury Vale district of Buckinghamshire. The 2001 Census recorded a parish populati ...
and Wavendon
Wavendon is a village and civil parish in the south east of the Milton Keynes urban area, in Buckinghamshire, England.
History and geography
The village name is an Old English language word, and means 'Wafa's hill'. In the '' Anglo-Saxon Chron ...
(both later supplanted by installations at Stanmore
Stanmore is part of the London Borough of Harrow in London. It is centred northwest of Charing Cross, lies on the outskirts of the London urban area and includes Stanmore Hill, one of the highest points of London, at high. The district, which ...
and Eastcote
Eastcote is a suburban area in the London Borough of Hillingdon, in northwest London.
In the Middle Ages, Eastcote was one of the three areas that made up the parish of Ruislip, under the name of Ascot. The name came from its position to the e ...
), and Gayhurst
Gayhurst is a village and civil parish in the unitary authority area of the City of Milton Keynes, Buckinghamshire, England. It is about two and a half miles NNW of Newport Pagnell.
The village name is an Old English language word meaning ...
.
Luftwaffe
The ''Luftwaffe'' () was the aerial-warfare branch of the German ''Wehrmacht'' before and during World War II. Germany's military air arms during World War I, the ''Luftstreitkräfte'' of the Imperial Army and the '' Marine-Fliegerabtei ...
messages were the first to be read in quantity. The German navy had much tighter procedures, and the capture of code books was needed before they could be broken. When, in February 1942, the German navy introduced the four-rotor Enigma for communications with its Atlantic U-boats, this traffic became unreadable for a period of ten months. Britain produced modified bombes, but it was the success of the US Navy bombe that was the main source of reading messages from this version of Enigma for the rest of the war.
Messages were sent to and fro across the Atlantic by enciphered teleprinter links.
SIGINT played a most important role for the Royal Navy
The Royal Navy (RN) is the United Kingdom's naval warfare force. Although warships were used by English and Scottish kings from the early medieval period, the first major maritime engagements were fought in the Hundred Years' War against F ...
, in its protection of merchant ships during the Battle of the Atlantic
The Battle of the Atlantic, the longest continuous military campaign in World War II, ran from 1939 to the defeat of Nazi Germany in 1945, covering a major part of the naval history of World War II. At its core was the Allied naval blockade ...
. While Ultra cryptanalysis certainly played a role in dealing with German submarines, HF/DF
High-frequency direction finding, usually known by its abbreviation HF/DF or nickname huff-duff, is a type of radio direction finder (RDF) introduced in World War II. High frequency (HF) refers to a radio band that can effectively communicate ov ...
and traffic analysis were complementary.
 It is unclear why the German submarine command believed that frequent radio communications were not a hazard to their boats, although they seemed confident in the security of their Enigma ciphers, both in the initial three-rotor and subsequent four-rotor versions (known as Triton to the Germans and Shark to the Allies). There was an apparent, mutually reinforcing belief that wolfpack attacks by groups of submarines were much more deadly than individual operations, and confidence the communications were secure. Arguably, the Germans underestimated HF/DF even more than they did British cryptanalysis. Apparently, the Germans did not realize that the Allies were not limited to slow, manually operated direction finders, and also underestimated the number of direction finders at sea. On the other hand, the introduction of a new secure communication system would have interrupted submarine operations for a long time since a gradual shift to a new system was out of the question.
The Lorenz messages were codenamed '' Tunny'' at Bletchley Park. They were only sent in quantity from mid-1942. The Tunny networks were used for high-level messages between German High Command and field commanders. With the help of German operator errors, the cryptanalysts in the
It is unclear why the German submarine command believed that frequent radio communications were not a hazard to their boats, although they seemed confident in the security of their Enigma ciphers, both in the initial three-rotor and subsequent four-rotor versions (known as Triton to the Germans and Shark to the Allies). There was an apparent, mutually reinforcing belief that wolfpack attacks by groups of submarines were much more deadly than individual operations, and confidence the communications were secure. Arguably, the Germans underestimated HF/DF even more than they did British cryptanalysis. Apparently, the Germans did not realize that the Allies were not limited to slow, manually operated direction finders, and also underestimated the number of direction finders at sea. On the other hand, the introduction of a new secure communication system would have interrupted submarine operations for a long time since a gradual shift to a new system was out of the question.
The Lorenz messages were codenamed '' Tunny'' at Bletchley Park. They were only sent in quantity from mid-1942. The Tunny networks were used for high-level messages between German High Command and field commanders. With the help of German operator errors, the cryptanalysts in the Testery
The Testery was a section at Bletchley Park, the British codebreaking station during World War II. It was set up in July 1942 as the "FISH Subsection" under Major Ralph Tester, hence its alternative name. Four founder members were Tester himself ...
(named after Ralph Tester
Ralph Paterson Tester (2 June 1902 – May 1998) was an administrator at Bletchley Park, the British codebreaking station during World War II. He founded and supervised a section named the ''Testery'' for breaking Tunny (a Fish cipher).
Backgroun ...
, its head) worked out the logical structure of the machine despite not knowing its physical form. They devised automatic machinery to help with decryption, which culminated in Colossus
Colossus, Colossos, or the plural Colossi or Colossuses, may refer to:
Statues
* Any exceptionally large statue
** List of tallest statues
** :Colossal statues
* ''Colossus of Barletta'', a bronze statue of an unidentified Roman emperor
* ''Col ...
, the world's first programmable digital electronic computer. This was designed and built by Tommy Flowers
Thomas Harold Flowers MBE (22 December 1905 – 28 October 1998) was an English engineer with the British General Post Office. During World War II, Flowers designed and built Colossus, the world's first programmable electronic computer, to help ...
and his team at the Post Office Research Station
The Post Office Research Station was first established as a separate section of the General Post Office in 1909.
In 1921, the Research Station moved to Dollis Hill, north west London, initially in ex-army huts.
The main permanent buildings at ...
at Dollis Hill
Dollis Hill is an area in northwest London, which consists of the streets surrounding the 35 hectares (86 acres) Gladstone Park. It is served by a London Underground station, Dollis Hill, on the Jubilee line, providing good links to central Lo ...
. The first was delivered to Bletchley Park in December 1943 and commissioned the following February. Enhancements were developed for the Mark 2 Colossus, the first of which was working at Bletchley Park on the morning of D-day
The Normandy landings were the landing operations and associated airborne operations on Tuesday, 6 June 1944 of the Allied invasion of Normandy in Operation Overlord during World War II. Codenamed Operation Neptune and often referred to as D ...
in June. Flowers then produced one Colossus a month for the rest of the war, making a total of ten with an eleventh part-built. The machines were operated mainly by Wrens in a section named the Newmanry
The Newmanry was a section at Bletchley Park, the British codebreaking station during World War II. Its job was to develop and employ statistical and machine methods in cryptanalysis of the Lorenz cipher. It worked very closely with the Testery wh ...
after its head Max Newman
Maxwell Herman Alexander Newman, FRS, (7 February 1897 – 22 February 1984), generally known as Max Newman, was a British mathematician and codebreaker. His work in World War II led to the construction of Colossus, the world's first operatio ...
.
The "Radio Security Service" was established by MI8
MI8, or ''Military Intelligence, Section 8'' was a British Military Intelligence group responsible for signals intelligence and was created in 1914. It originally consisted of four sections: MI8(a), which dealt with wireless policy; MI8(b), b ...
in 1939 to control a network of Direction Finding and intercept stations to locate illicit transmissions coming from German spies in Britain. This service was soon intercepting a network of German Secret Service transmissions across Europe. Successful decryption was achieved at an early stage with the help of codes obtained from the British XX (Double Cross) System that "turned" German agents and used them to misdirect German intelligence. The combination of double agents and extensive penetration of German intelligence transmissions facilitated a series of highly successful strategic deception programmes throughout WWII.
Italian codes
Breakthroughs were also made with Italian signals. During theSpanish Civil War
The Spanish Civil War ( es, Guerra Civil Española)) or The Revolution ( es, La Revolución, link=no) among Nationalists, the Fourth Carlist War ( es, Cuarta Guerra Carlista, link=no) among Carlists, and The Rebellion ( es, La Rebelión, lin ...
the Italian Navy
"Fatherland and Honour"
, patron =
, colors =
, colors_label =
, march = ( is the return of soldiers to their barrack, or sailors to their ship after a ...
used the K model of the commercial Enigma without a plugboard; this was solved by Knox in 1937. When Italy entered the war in 1940 an improved version of the machine was used, though little traffic was sent by it and there were "wholesale changes" in Italian codes and cyphers. Knox was given a new section for work on Enigma variations, which he staffed with women ("Dilly's girls") who included Margaret Rock, Jean Perrin, Clare Harding, Rachel Ronald, Elisabeth Granger; and Mavis Leverwho made the first break into the Italian naval traffic. She solved the signals revealing the Italian Navy's operational plans before the Battle of Cape Matapan
The Battle of Cape Matapan ( el, Ναυμαχία του Ταινάρου) was a naval battle during the Second World War between the Allies, represented by the navies of the United Kingdom and Australia, and the Royal Italian navy, from 27 ...
in 1941, leading to a British victory.
On entering World War II in June 1940, the Italians
, flag =
, flag_caption = The national flag of Italy
, population =
, regions = Italy 55,551,000
, region1 = Brazil
, pop1 = 25–33 million
, ref1 =
, region2 ...
were using book codes for most of their military messages.
The exception was the Italian Navy
"Fatherland and Honour"
, patron =
, colors =
, colors_label =
, march = ( is the return of soldiers to their barrack, or sailors to their ship after a ...
, which after the Battle of Cape Matapan started using the C-38 version of the Boris Hagelin rotor-based cipher machine
In cryptography, a cipher (or cypher) is an algorithm for performing encryption or decryption—a series of well-defined steps that can be followed as a procedure. An alternative, less common term is ''encipherment''. To encipher or encode i ...
, particularly to route their navy and merchant marine convoys to the conflict in North Africa.
As a consequence, JRM Butler recruited his former student Bernard Willson
Harold Bernard Willson (25 February 1919–1994) was a British linguist and noted academic, who during the Second World War was the first person to decrypt the Italian Navy Hagelin C-38 code machine. He was the father of television presente ...
to join a team with two others in Hut4. In June 1941, Willson became the first of the team to decode the Hagelin system, thus enabling military commanders to direct the Royal Navy
The Royal Navy (RN) is the United Kingdom's naval warfare force. Although warships were used by English and Scottish kings from the early medieval period, the first major maritime engagements were fought in the Hundred Years' War against F ...
and Royal Air Force
The Royal Air Force (RAF) is the United Kingdom's air and space force. It was formed towards the end of the First World War on 1 April 1918, becoming the first independent air force in the world, by regrouping the Royal Flying Corps (RFC) and ...
to sink enemy ships carrying supplies from Europe to Rommel's Afrika Korps
The Afrika Korps or German Africa Corps (, }; DAK) was the German expeditionary force in Africa during the North African Campaign of World War II. First sent as a holding force to shore up the Italian defense of its African colonies, the ...
. This led to increased shipping losses and, from reading the intercepted traffic, the team learnt that between May and September 1941 the stock of fuel for the Luftwaffe
The ''Luftwaffe'' () was the aerial-warfare branch of the German ''Wehrmacht'' before and during World War II. Germany's military air arms during World War I, the ''Luftstreitkräfte'' of the Imperial Army and the '' Marine-Fliegerabtei ...
in North Africa reduced by 90%.
After an intensive language course, in March 1944 Willson switched to Japanese language-based codes.
Japanese codes
 An outpost of the Government Code and Cypher School was set up in Hong Kong in 1935, the
An outpost of the Government Code and Cypher School was set up in Hong Kong in 1935, the Far East Combined Bureau
The Far East Combined Bureau, an outstation of the British Government Code and Cypher School, was set up in Hong Kong in March 1935, to monitor Japanese, and also Chinese and Russian (Soviet) intelligence and radio traffic. Later it moved to Sing ...
(FECB), to study Japanese signals. The FECB naval staff moved in 1940 to Singapore, then Colombo
Colombo ( ; si, කොළඹ, translit=Koḷam̆ba, ; ta, கொழும்பு, translit=Koḻumpu, ) is the executive and judicial capital and largest city of Sri Lanka by population. According to the Brookings Institution, Colombo me ...
, Ceylon
Sri Lanka (, ; si, ශ්රී ලංකා, Śrī Laṅkā, translit-std=ISO (); ta, இலங்கை, Ilaṅkai, translit-std=ISO ()), formerly known as Ceylon and officially the Democratic Socialist Republic of Sri Lanka, is an ...
, then Kilindini
Kilindini Harbour is a large, natural deep-water inlet extending inland from Mombasa, Kenya. It is at its deepest center, although the controlling depth is the outer channel in the port approaches with a dredged depth of . It serves as the harbo ...
, Mombasa
Mombasa ( ; ) is a coastal city in southeastern Kenya along the Indian Ocean. It was the first capital of the British East Africa, before Nairobi was elevated to capital city status. It now serves as the capital of Mombasa County. The town is ...
, Kenya. They succeeded in deciphering Japanese codes with a mixture of skill and good fortune. The Army and Air Force staff went from Singapore to the Wireless Experimental Centre
The Wireless Experimental Centre (WEC) was one of two overseas outposts of Station X, Bletchley Park, the British signals analysis centre during World War II. The other outpost was the Far East Combined Bureau. Codebreakers Wilfred Noyce and Mauric ...
at Delhi
Delhi, officially the National Capital Territory (NCT) of Delhi, is a city and a union territory of India containing New Delhi, the capital of India. Straddling the Yamuna river, primarily its western or right bank, Delhi shares borders w ...
, India.
In early 1942, a six-month crash course in Japanese, for 20 undergraduates from Oxford and Cambridge, was started by the Inter-Services Special Intelligence School in Bedford, in a building across from the main Post Office. This course was repeated every six months until war's end. Most of those completing these courses worked on decoding Japanese naval messages in Hut 7, under John Tiltman
Brigadier John Hessell Tiltman, (25 May 1894 – 10 August 1982) was a British Army officer who worked in intelligence, often at or with the Government Code and Cypher School (GC&CS) starting in the 1920s. His intelligence work was largely conn ...
. By mid-1945 well over 100 personnel were involved with this operation, which co-operated closely with the FECB and the US Signal intelligence Service at Arlington Hall
Arlington Hall (also called Arlington Hall Station) is a historic building in Arlington, Virginia, originally a girls' school and later the headquarters of the United States Army's Signal Intelligence Service (SIS) cryptography effort during Wor ...
, Virginia. Because of these joint efforts, by August of that year the Japanese merchant navy was suffering 90% losses at sea. In 1999, Michael Smith wrote that: "Only now are the British codebreakers (like John Tiltman
Brigadier John Hessell Tiltman, (25 May 1894 – 10 August 1982) was a British Army officer who worked in intelligence, often at or with the Government Code and Cypher School (GC&CS) starting in the 1920s. His intelligence work was largely conn ...
, Hugh Foss
Hugh Rose Foss (13 May 1902 – 23 December 1971) was a British cryptanalyst. At Bletchley Park during World War II he made significant contributions both to the breaking of the German Enigma code and headed the section tasked with breaking Japan ...
, and Eric Nave
Captain Eric Nave (18 March 1899 – 23 June 1993) was an Australian cryptographer and intelligence officer in the Royal Australian Navy (RAN) and Royal Navy, noted for his work with joint Allied intelligence units during World War II. He serve ...
) beginning to receive the recognition they deserve for breaking Japanese codes and cyphers".
US SIGINT
During the Second World War, theUS Army
The United States Army (USA) is the land service branch of the United States Armed Forces. It is one of the eight U.S. uniformed services, and is designated as the Army of the United States in the U.S. Constitution.Article II, section 2, cla ...
and US Navy
The United States Navy (USN) is the maritime service branch of the United States Armed Forces and one of the eight uniformed services of the United States. It is the largest and most powerful navy in the world, with the estimated tonnage of ...
ran independent SIGINT organizations, with limited coordination, first on a pure personal basis, and then through committees.
After the Normandy landings, Army SIGINT units accompanied major units, with traffic analysis as - or more - important than the tightly compartmented cryptanalytic information. General Bradley
Bradley is an English surname derived from a place name meaning "broad wood" or "broad meadow" in Old English.
Like many English surnames Bradley can also be used as a given name and as such has become popular.
It is also an Anglicisation of t ...
's Army Group, created on August 1, 1944, had SIGINT including access to Ultra. Patton
George Smith Patton Jr. (November 11, 1885 – December 21, 1945) was a general in the United States Army who commanded the Seventh United States Army in the Mediterranean Theater of World War II, and the Third United States Army in Franc ...
's subordinate Third Army had a double-sized Signal Radio Intelligence Company attached to his headquarters, and two regular companies were assigned to the XV and VIII Corps.
The US Navy used SIGINT in its anti-submarine warfare
Anti-submarine warfare (ASW, or in older form A/S) is a branch of underwater warfare that uses surface warships, aircraft, submarines, or other platforms, to find, track, and deter, damage, or destroy enemy submarines. Such operations are t ...
, using shore or ship-based SIGINT to vectored long-range patrol aircraft to U-boats.
Allied cooperation in the Pacific Theater
The Pacific Ocean is the largest and deepest of Earth's five oceanic divisions. It extends from the Arctic Ocean in the north to the Southern Ocean (or, depending on definition, to Antarctica) in the south, and is bounded by the continen ...
included the joint RAN/USN Fleet Radio Unit, Melbourne (FRUMEL), and the Central Bureau The Central Bureau was one of two Allied signals intelligence (SIGINT) organisations in the South West Pacific area (SWPA) during World War II. Central Bureau was attached to the headquarters of the Allied Commander of the South West Pacific area ...
which was attached to the HQ of the Allied Commander of the South-West Pacific area.
At first, Central Bureau was made up of 50% American, 25% Australian Army
The Australian Army is the principal Army, land warfare force of Australia, a part of the Australian Defence Force (ADF) along with the Royal Australian Navy and the Royal Australian Air Force. The Army is commanded by the Chief of Army (Austral ...
and 25% Royal Australian Air Force
"Through Adversity to the Stars"
, colours =
, colours_label =
, march =
, mascot =
, anniversaries = RAAF Anniversary Commemoration ...
(RAAF) personnel, but additional Australian staff joined. In addition, RAAF operators, trained in Townsville, Queensland
Townsville is a city on the north-eastern coast of Queensland, Australia. With a population of 180,820 as of June 2018, it is the largest settlement in North Queensland; it is unofficially considered its capital. Estimated resident population, 3 ...
in intercepting Japanese telegraphic katakana
is a Japanese syllabary, one component of the Japanese writing system along with hiragana, kanji and in some cases the Latin script (known as rōmaji). The word ''katakana'' means "fragmentary kana", as the katakana characters are derived fr ...
were integrated into the new Central Bureau.
Until Central Bureau received replacement data processing equipment for that which was lost in the Philippines
The Philippines (; fil, Pilipinas, links=no), officially the Republic of the Philippines ( fil, Republika ng Pilipinas, links=no),
* bik, Republika kan Filipinas
* ceb, Republika sa Pilipinas
* cbk, República de Filipinas
* hil, Republ ...
, as of January 1942, U.S. Navy stations in Hawaii
Hawaii ( ; haw, Hawaii or ) is a state in the Western United States, located in the Pacific Ocean about from the U.S. mainland. It is the only U.S. state outside North America, the only state that is an archipelago, and the only stat ...
(Hypo), Corregidor (Cast) and OP-20-G (Washington) decrypted Japanese traffic well before the U.S. Army or Central Bureau in Australia. Cast, of course, closed with the evacuation of SIGINT personnel from the Philippines. Central Bureau broke into two significant Japanese Army cryptosystems in mid-1943.
Japanese codes
 The
The US Army
The United States Army (USA) is the land service branch of the United States Armed Forces. It is one of the eight U.S. uniformed services, and is designated as the Army of the United States in the U.S. Constitution.Article II, section 2, cla ...
shared with the US Navy the Purple
Purple is any of a variety of colors with hue between red and blue. In the RGB color model used in computer and television screens, purples are produced by mixing red and blue light. In the RYB color model historically used by painters, pu ...
attack on Japanese diplomatic cryptosystems. After the creation of the Army Signal Security Agency, the cryptographic school at Vint Hill Farms Station
Vint Hill Farms Station (VHFS) was a United States Army and National Security Agency (NSA) signals intelligence and electronic warfare facility located in Fauquier County, Virginia, near Warrenton. VHFS was closed in 1997 and the land was sold of ...
, Warrenton, Virginia
Warrenton is a town in Fauquier County, Virginia, of which it is the seat of government. The population was 9,611 at the 2010 census, up from 6,670 at the 2000 census. The estimated population in 2019 was 10,027. It is at the junction of U.S. R ...
, trained analysts. As a real-world training exercise, the new analysts first solved the message center identifier system for the Japanese Army. Until Japanese Army cryptosystems were broken later in 1943, the order of battle and movement information on the Japanese came purely from direction finding and traffic analysis.
Traffic analysts began tracking Japanese units in near real time. A critical result was the identification of the movement, by sea, of two Japanese infantry divisions from Shanghai
Shanghai (; , , Standard Mandarin pronunciation: ) is one of the four direct-administered municipalities of the People's Republic of China (PRC). The city is located on the southern estuary of the Yangtze River, with the Huangpu River flow ...
to New Guinea
New Guinea (; Hiri Motu
Hiri Motu, also known as Police Motu, Pidgin Motu, or just Hiri, is a language of Papua New Guinea, which is spoken in surrounding areas of Port Moresby (Capital of Papua New Guinea).
It is a simplified version of ...
. Their convoy was intercepted by US submarines, causing almost complete destruction of these units.
Army units in the Pacific included the US 978th Signal Company based at the Allied Intelligence Bureau's secret "Camp X", near Beaudesert, Queensland
Beaudesert is a rural town and locality in the Scenic Rim Region, Queensland, Australia. In the , Beaudesert had a population of 6,395 people.
Beaudesert is the administrative centre for the Scenic Rim Region.
Geography
Beaudesert is south of ...
south of Brisbane. This unit was a key part of operations behind Japanese lines, including communicating with guerillas and the Coastwatcher
The Coastwatchers, also known as the Coast Watch Organisation, Combined Field Intelligence Service or Section C, Allied Intelligence Bureau, were Allied military intelligence operatives stationed on remote Pacific islands during World War II t ...
organization. It also sent radio operators to the guerillas, and then moved with the forces invading the Philippines.
US Navy strategic stations targeted against Japanese sources at the outbreak of the war, included Station HYPO in Hawaii, Station CAST in the Philippines, station BAKER on Guam
Guam (; ch, Guåhan ) is an organized, unincorporated territory of the United States in the Micronesia subregion of the western Pacific Ocean. It is the westernmost point and territory of the United States (reckoned from the geographic cent ...
, and other locations including Puget Sound
Puget Sound ( ) is a sound of the Pacific Northwest, an inlet of the Pacific Ocean, and part of the Salish Sea. It is located along the northwestern coast of the U.S. state of Washington. It is a complex estuarine system of interconnected ma ...
, and Bainbridge Island
Bainbridge Island is a city and island in Kitsap County, Washington. It is located in Puget Sound. The population was 23,025 at the 2010 census and an estimated 25,298 in 2019, making Bainbridge Island the second largest city in Kitsap County.
...
. US COMINT recognized the growing threat before the Pearl Harbor
Pearl Harbor is an American lagoon harbor on the island of Oahu, Hawaii, west of Honolulu. It was often visited by the Naval fleet of the United States, before it was acquired from the Hawaiian Kingdom by the U.S. with the signing of the Re ...
attack, but a series of errors, as well as priorities that were incorrect in hindsight, prevented any operational preparation against the attack. Nevertheless, that attack gave much higher priority to COMINT, both in Washington, D.C.
)
, image_skyline =
, image_caption = Clockwise from top left: the Washington Monument and Lincoln Memorial on the National Mall, United States Capitol, Logan Circle, Jefferson Memorial, White House, Adams Morgan, ...
and at the Pacific Fleet Headquarters in Honolulu
Honolulu (; ) is the capital and largest city of the U.S. state of Hawaii, which is in the Pacific Ocean. It is an unincorporated county seat of the consolidated City and County of Honolulu, situated along the southeast coast of the island ...
. Organizational tuning corrected many prewar competitions between the Army and Navy.
Perhaps most dramatically, intercepts of Japanese naval communications yielded information that gave Admiral Nimitz the upper hand in the ambush that resulted in the Japanese Navy's defeat at the Battle of Midway
The Battle of Midway was a major naval battle in the Pacific Theater of World War II that took place on 4–7 June 1942, six months after Japan's attack on Pearl Harbor and one month after the Battle of the Coral Sea. The U.S. Navy under Adm ...
, six months after the Pearl Harbor
Pearl Harbor is an American lagoon harbor on the island of Oahu, Hawaii, west of Honolulu. It was often visited by the Naval fleet of the United States, before it was acquired from the Hawaiian Kingdom by the U.S. with the signing of the Re ...
attack.
The US Army Air Force
The United States Army Air Forces (USAAF or AAF) was the major land-based aerial warfare service component of the United States Army and ''de facto'' aerial warfare service branch of the United States during and immediately after World War II ...
also had its own SIGINT capability. Soon after the Pearl Harbor attack, Lieutenant Howard Brown, of the 2nd Signal Service Company in Manila
Manila ( , ; fil, Maynila, ), officially the City of Manila ( fil, Lungsod ng Maynila, ), is the capital of the Philippines, and its second-most populous city. It is highly urbanized and, as of 2019, was the world's most densely populate ...
, ordered the unit to change its intercept targeting from Japanese diplomatic to air force communications. The unit soon was analyzing Japanese tactical networks and developing order of battle intelligence.
They learned the Japanese air-to-ground network was Sama, Hainan Island
Hainan (, ; ) is the smallest and southernmost province of the People's Republic of China (PRC), consisting of various islands in the South China Sea. , the largest and most populous island in China,The island of Taiwan, which is slightly l ...
, with one station in Indochina
Mainland Southeast Asia, also known as the Indochinese Peninsula or Indochina, is the continental portion of Southeast Asia. It lies east of the Indian subcontinent and south of Mainland China and is bordered by the Indian Ocean to the west an ...
, one station near Hong Kong
Hong Kong ( (US) or (UK); , ), officially the Hong Kong Special Administrative Region of the People's Republic of China ( abbr. Hong Kong SAR or HKSAR), is a city and special administrative region of China on the eastern Pearl River Delt ...
, and the other 12 unlocated. Two Japanese naval stations were in the Army net, and it handled both operations and ferrying of aircraft for staging new operations. Traffic analysis of still-encrypted traffic helped MacArthur predict Japanese moves as the Fil-American forces retreated in Bataan.
An Australian-American intercept station was later built at Townsville
Townsville is a city on the north-eastern coast of Queensland, Australia. With a population of 180,820 as of June 2018, it is the largest settlement in North Queensland; it is unofficially considered its capital. Estimated resident population, 3 ...
, Queensland
)
, nickname = Sunshine State
, image_map = Queensland in Australia.svg
, map_caption = Location of Queensland in Australia
, subdivision_type = Country
, subdivision_name = Australia
, established_title = Before federation
, established_ ...
. US Air Force Far East, and its subordinate 5th Air Force, took control of the 126th in June 1943. The 126th was eventually placed under operational control of U.S. Air Force Far East in June 1943 to support 5th Air Force. Interception and traffic analysis from the company supported the attack into Dutch New Guinea in 1944.
Cold War
After the end of World War II, the Western allies began a rapid drawdown. At the end of WWII, the US still had a COMINT organization split between the Army and Navy. A 1946 plan listed Russia, China, and a edactedcountry as high-priority targets. From 1943 to 1980, theVenona project
The Venona project was a United States counterintelligence program initiated during World War II by the United States Army's Signal Intelligence Service (later absorbed by the National Security Agency), which ran from February 1, 1943, until Octob ...
, principally a US activity with support from Australia and the UK, recovered information, some tantalizingly only in part, from Soviet espionage traffic. While the Soviets had originally used theoretically unbreakable one-time pad
In cryptography, the one-time pad (OTP) is an encryption technique that cannot be cracked, but requires the use of a single-use pre-shared key that is not smaller than the message being sent. In this technique, a plaintext is paired with a ran ...
s for the traffic, some of their operations violated communications security rules and reused some of the pads. This reuse caused the vulnerability that was exploited.
Venona gave substantial information on the scope of Soviet espionage against the West, but critics claim some messages have been interpreted incorrectly, or are even false. Part of the problem is that certain persons, even in the encrypted traffic, were identified only by code names such as "Quantum". Quantum was a source on US nuclear weapons, and is often considered to be Julius Rosenberg
Julius Rosenberg (May 12, 1918 – June 19, 1953) and Ethel Rosenberg (; September 28, 1915 – June 19, 1953) were American citizens who were convicted of spying on behalf of the Soviet Union. The couple were convicted of providing top-secret i ...
. The name, however, could refer to any of a number of spies.
US Tactical SIGINT
After the Beirut deployment, Lieutenant GeneralAlfred M. Gray, Jr.
Alfred Mason Gray Jr. (born June 22, 1928) is a retired United States Marine Corps four-star general who served as the 29th Commandant of the Marine Corps from 1 July 1987 until his retirement on 30 June 1991 after 41 years of service.
Early li ...
did an after-action review of the 2nd Radio Battalion
Radio Battalions are tactical signals intelligence units of Marine Corps Intelligence. There are currently three operational Radio Battalions in the Marine Corps organization: 1st, 2nd, and 3rd. In fleet operations, teams from Radio Battalions are ...
detachment that went with that force. Part of the reason for this was that the irregular units that presented the greatest threat did not follow conventional military signal operating procedures, and used nonstandard frequencies and callsigns. Without NSA information on these groups, the detachment had to acquire this information from their own resources.
Recognizing that national sources simply might not have information on a given environment, or that they might not make it available to warfighters, Lieutenant General Gray directed that a SIGINT function be created that could work with the elite Force Reconnaissance Marines who search out potential enemies. At first, neither the Force Reconnaissance nor Radio Battalion commanders thought this was viable, but had orders to follow.
Initially, they attached a single Radio Battalion Marine, with an AN/GRR-8 intercept receiver, to a Force Reconnaissance team during an exercise. A respected Radio Marine, Corporal Kyle O'Malley was sent to the team, without any guidance for what he was to do. The exercise did not demonstrate that a one-man attachment, not Force Recon qualified, was useful.
In 1984, Captain E.L. Gillespie, assigned to the Joint Special Operations Command
The Joint Special Operations Command (JSOC) is a joint component command of the United States Special Operations Command (USSOCOM) and is charged with studying special operations requirements and techniques to ensure interoperability and equip ...
, was alerted that he was to report to 2nd Radio Battalion, to develop a concept of operations for integrating SIGINT capabilities with Force Recon, using his joint service experience with special operations. Again, the immediate commanders were not enthusiastic.
Nevertheless, a mission statement was drafted: "To conduct limited communications intelligence and specified electronic warfare operations in support of Force Reconnaissance operations during advance force or special operations missions." It was decided that a 6-man SIGINT team, with long/short range independent communications and SIGINT/EW equipment, was the minimum practical unit. It was not practical to attach this to the smallest 4-man Force Recon team.
General Gray directed that the unit would be called a Radio Reconnaissance Team (RRT), and that adequate planning and preparation were done for the advance force operations part of the upcoming Exercise Solid Shield-85. Two six-man teams would be formed, from Marines assigned from the Radio Battalion, without great enthusiasm for the assignment. One Marine put it"There is nothing that the Marine Corps can do to me that I can't take."
Force Recon required that the RRT candidates pass their selection course, and, to the surprise of Force Recon, they passed with honors. Both teams were assigned to the exercise, and the RRTs successfully maintained communications connectivity for Force Recon and SEAL
Seal may refer to any of the following:
Common uses
* Pinniped, a diverse group of semi-aquatic marine mammals, many of which are commonly called seals, particularly:
** Earless seal, or "true seal"
** Fur seal
* Seal (emblem), a device to impr ...
s, collected meaningful intelligence, disrupted opposing force communications, and were extracted without being compromised.
From 1986 on, RRTs accompanied MEU(SOC) deployments. Their first combat role was in Operation Earnest Will
Operation Earnest Will (24 July 1987 – 26 September 1988) was the American military protection of Kuwaiti-owned tankers from Iranian attacks in 1987 and 1988, three years into the Tanker War phase of the Iran–Iraq War. It was the largest nav ...
, then Operation Praying Mantis
Operation Praying Mantis was an attack on 18 April 1988, by the United States Armed Forces within Iranian territorial waters in retaliation for the Iranian naval mining of the Persian Gulf during the Iran–Iraq War and the subsequent damage t ...
, followed by participation in the 1989 United States invasion of Panama
The United States invasion of Panama, codenamed Operation Just Cause, lasted over a month between mid-December 1989 and late January 1990. It occurred during the administration of President George H. W. Bush and ten years after the Torrijos– ...
Recent history
 As evidenced by the
As evidenced by the Hainan Island incident
The Hainan Island incident occurred on April 1, 2001, when a United States Navy EP-3E ARIES II signals intelligence aircraft and a People's Liberation Army Navy (PLAN) J-8II interceptor fighter jet collided in mid-air, resulting in an inte ...
, even while China and the US may cooperate on matters of mutual concern towards Russia, the Cold War has not completely disappeared.
There was more regional cooperation, often driven by concerns about transnational terrorism. European countries also are finding that by sharing the cost, they can acquire SIGINT, IMINT, and MASINT capabilities independent of the US.
In the US, both communications security and COMINT policies have been evolving, some with challenges. The adoption of a Belgian-developed encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decip ...
algorithm , approved in a public process, and accepted both for sensitive but unclassified traffic, as well as for classified information sent with NSA-generated and maintained keys, redraws the cryptologic environment as no longer NSA or not-NSA. Controversy continues on various types of COMINT justified as not requiring warrants, under the wartime authority of the President of the United States.
Technologically, there was much greater use of UAVs
An unmanned aerial vehicle (UAV), commonly known as a drone, is an aircraft without any human pilot, crew, or passengers on board. UAVs are a component of an unmanned aircraft system (UAS), which includes adding a ground-based controlle ...
as SIGINT collection platforms.
Threat from terrorism
Terrorism from foreign groups became an increasingly major concern, as with the 1992 al-Qaeda attack in Yemen, the 1993 truck bombing of the World Trade Center, the 1995 Khobar Towers bombing in Saudi Arabia and the 1998 bombings of the US embassies in Dar es Salaam, Tanzania and Nairobi, Kenya. Third world and non-national groups, with modern communications technology, in many ways are a harder SIGINT target than a nation that sends out large amounts of traffic. According to the retired Commandant of the US Marines,Alfred M. Gray, Jr.
Alfred Mason Gray Jr. (born June 22, 1928) is a retired United States Marine Corps four-star general who served as the 29th Commandant of the Marine Corps from 1 July 1987 until his retirement on 30 June 1991 after 41 years of service.
Early li ...
, some of the significant concerns of these targets are:
:*Inherently low probability of intercept/detection (LPI/LPD) because off-the-shelf radios can be frequency agile, spread spectrum, and transmit in bursts.
:*Additional frequencies, not normally monitored, can be used. These include citizens band
Citizens band radio (also known as CB radio), used in many countries, is a land mobile radio system, a system allowing short-distance person-to-many persons bidirectional voice communication among individuals, using two way radios operating on ...
, marine (MF, HF, VHF) bands, personal radio services such as MURS
Murs may refer to:
People
* Marc Athanase Parfait Œillet des Murs (1804-1878), French ornithologist
* Olly Murs (born 1984), English singer-songwriter
* Murs (rapper) (born 1978), American rapper
Places
* Murs, Indre, France
* Murs, Vaucluse, ...
, FRS/GMRS
The General Mobile Radio Service (GMRS) is a land-mobile FM UHF radio service designed for short-distance two-way communication and authorized under part 95 of 47 USC. It requires a license in the United States, but some GMRS compatible equipme ...
and higher frequencies for short-range communications
:*Extensive use of telephones, almost always digital. Cellular and satellite telephones, while wireless, are challenging to intercept, as is Voice over IP (VoIP)
:*Commercial strong encryption for voice and data
:*"Extremely wide variety and complexity of potential targets, creating a "needle in the haystack" problem"
As a result of the 9/11 attacks, intensification of US intelligence efforts, domestic and foreign, were to be expected. A key question, of course, was whether US intelligence could have prevented or mitigated the attacks, and how it might prevent future attacks. There is a continuing clash between advocates for civil liberties and those who assert that their loss is an agreeable exchange for enhanced safety.
Under the George W. Bush
George Walker Bush (born July 6, 1946) is an American politician who served as the 43rd president of the United States from 2001 to 2009. A member of the Republican Party, Bush family, and son of the 41st president George H. W. Bush, he ...
administration, there was a large-scale and controversial capture and analysis of domestic and international telephone calls, claimed to be targeted against terrorism. It is generally accepted that warrants have not been obtained for this activity, sometimes called Room 641A
Room 641A is a telecommunication interception facility operated by AT&T for the U.S. National Security Agency, as part of its warrantless surveillance program as authorized by the Patriot Act. The facility commenced operations in 2003 and its ...
after a location, in San Francisco, where AT&T provides NSA access. While very little is known about this system, it may be focused more on the signaling channel and Call detail record
A call detail record (CDR) is a data record produced by a telephone exchange or other telecommunications equipment that documents the details of a telephone call or other telecommunications transactions (e.g., text message) that passes through that ...
s than the actual content of conversations.
Another possibility is the use of software tools that do high-performance deep packet inspection
Deep packet inspection (DPI) is a type of data processing that inspects in detail the data being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep packet inspection is oft ...
. According to the marketing VP of Narus, "Narus has little control over how its products are used after they're sold. For example, although its lawful-intercept application has a sophisticated system for making sure the surveillance complies with the terms of a warrant, it's up to the operator whether to type those terms into the system...
"That legal eavesdropping application was launched in February 2005, well after whistle-blower Klein allegedly learned that AT&T was installing Narus boxes in secure, NSA-controlled rooms in switching centers around the country. But that doesn't mean the government couldn't write its own code to do the dirty work. Narus even offers software-development kits to customers ". The same type of tools with legitimate ISP security applications also have COMINT interception and analysis capability.
Former AT&T technician Mark Klein
Mark Klein is a former AT&T technician and whistleblower who revealed details of the company's cooperation with the United States National Security Agency in installing network hardware at a site known as Room 641A to monitor, capture and proce ...
, who revealed AT&T was giving NSA access,
said in a statement, said a Narus STA 6400 was in the NSA room to which AT&T allegedly copied traffic. The Narus device was "known to be used particularly by government intelligence agencies because of its ability to sift through large amounts of data looking for preprogrammed targets."
European Space Systems cooperation
French initiatives, along with French and Russian satellite launching, have led to cooperative continental European arrangements for intelligence sensors in space. In contrast, the UK has reinforced cooperation under the UKUSA agreement. France launched Helios 1A as a military photo-reconnaissance satellite on 7 July 1995. TheCerise (satellite)
Cerise (French for "cherry") was a French military reconnaissance satellite. Its main purpose was to intercept HF radio signals for French intelligence services.
With a mass of 50 kg, it was launched by an Ariane rocket from Kourou in French ...
SIGINT technology demonstrator also was launched in 1995. A radio propagation experiment, S80-T, was launched in 1992, as a predecessor of the ELINT experiments. Clementine, the second-generation ELINT technology demonstrator, was launched in 1999.
Financial pressures in 1994-1995 caused France to seek Spanish and Italian cooperation for Hélios 1B
Hélios 1A and Hélios 1B were French military photo-reconnaissance satellites in which Italy and Spain also participated. Hélios 1A was launched from the Guiana Space Centre, French Guiana on 3 December 1999 at 16:22:00 UTC. The spacecraft r ...
and German contributions to Helios 2. Helios 2A was launched on 18 December 2004. Built by EADS
Airbus SE (; ; ; ) is a European multinational aerospace corporation. Airbus designs, manufactures and sells civil and military aerospace products worldwide and manufactures aircraft throughout the world. The company has three divisions: '' ...
-Astrium
Astrium was an aerospace manufacturer subsidiary of the European Aeronautic Defence and Space Company (EADS) that provided civil and military space systems and services from 2006 to 2013. In 2012, Astrium had a turnover of €5.8 billion and 18 ...
for the French Space Agency (CNES), it was launched into a Sun-synchronous polar orbit at an altitude of about 680 kilometers.
The same launcher carried French and Spanish scientific satellites and four Essaim ("Swarm") experimental ELINT satellites
Germany launched their first reconnaissance satellite system, SAR-Lupe
SAR-Lupe is Germany's first reconnaissance satellite system and is used for military purposes. SAR is an abbreviation for synthetic-aperture radar, and "Lupe" is German for magnifying glass. The SAR-Lupe program consists of five identical (770&nb ...
, on December 19, 2006. Further satellites were launched at roughly six-month intervals, and the entire system of this five-satellite synthetic aperture radar
Synthetic-aperture radar (SAR) is a form of radar that is used to create two-dimensional images or three-dimensional reconstructions of objects, such as landscapes. SAR uses the motion of the radar antenna over a target region to provide fine ...
constellation achieved full operational readiness on 22 July 2008. SAR is usually considered a MASINT
Measurement and signature intelligence (MASINT) is a technical branch of intelligence gathering, which serves to detect, track, identify or describe the distinctive characteristics (signatures) of fixed or dynamic target sources. This often incl ...
sensor, but the significance here is that Germany obtains access to French satellite ELINT.
The joint French-Italian Orfeo Programme
The Orfeo programme is an agreement to implement co-operation for setting up an Earth observation capability using optical and radar sensors, and mainly to define the context in which the dual-purpose system (military and civilian) is to be devel ...
, a dual-use civilian and military satellite system, launched its first satellite on June 8, 2007. Italy is developing the Cosmo-Skymed X-band polarimetric SAR, to fly on two of the satellites. The other two will have complementary French electro-optical payloads. The second Orfeo is scheduled to launch in early 2008.
While this is not an explicit SIGINT system, the French-Italian cooperation may suggest that Italy can get data from the French Essaim ELINT microsatellites.
See also
*Signals intelligence by alliances, nations and industries
Signals intelligence by alliances, nations and industries comprises signals intelligence (SIGINT) gathering activities by national and non-national entities; these entities are commonly responsible for communications security (COMSEC) as well.
...
References
Bibliography
* * * * * * * * {{DEFAULTSORT:Signals Intelligence In Modern History Signals intelligence Military history by topic