illegal opcode on:
[Wikipedia]
[Google]
[Amazon]
 An illegal opcode, also called an unimplemented operation, unintended opcode or undocumented instruction, is an instruction to a
An illegal opcode, also called an unimplemented operation, unintended opcode or undocumented instruction, is an instruction to a
https://web.archive.org/web/20190713083631/http://www.myquest.nl/z80undocumented/z80-documented.tex] (NB. Illegal opcodes on the Z80.) * {{cite web , editor-first=Ralf D. , editor-last=Brown , editor-link=Ralf D. Brown , url=https://www.cs.cmu.edu/~ralf/files.html , title=The x86 Interrupt List , edition=61 , date=2002-12-29 , orig-year=2000-07-17, 1985 , access-date=2011-10-14 , url-status=live , archive-url=https://web.archive.org/web/20170822194456/https://www.cs.cmu.edu/~ralf/files.html , archive-date=2017-08-22}
https://web.archive.org/web/20170902120420/https://www.cs.cmu.edu/~ralf/interrupt-list/inter61b.zi
https://web.archive.org/web/20170902120447/https://www.cs.cmu.edu/~ralf/interrupt-list/inter61d.zi
https://web.archive.org/web/20170902120507/https://www.cs.cmu.edu/~ralf/interrupt-list/inter61f.zi
(NB.
Christian Ludloff's site sandpile.org also contains info on undocumented opcodes
Machine code
 An illegal opcode, also called an unimplemented operation, unintended opcode or undocumented instruction, is an instruction to a
An illegal opcode, also called an unimplemented operation, unintended opcode or undocumented instruction, is an instruction to a CPU
A central processing unit (CPU), also called a central processor, main processor or just processor, is the electronic circuitry that executes instructions comprising a computer program. The CPU performs basic arithmetic, logic, controlling, and ...
that is not mentioned in any official documentation released by the CPU's designer or manufacturer, which nevertheless has an effect. Illegal opcodes were common on older CPUs designed during the 1970s, such as the MOS Technology
MOS Technology, Inc. ("MOS" being short for Metal Oxide Semiconductor), later known as CSG (Commodore Semiconductor Group) and GMT Microelectronics, was a semiconductor design and fabrication company based in Audubon, Pennsylvania. It is m ...
6502
The MOS Technology 6502 (typically pronounced "sixty-five-oh-two" or "six-five-oh-two") William Mensch and the moderator both pronounce the 6502 microprocessor as ''"sixty-five-oh-two"''. is an 8-bit microprocessor that was designed by a small te ...
, Intel
Intel Corporation is an American multinational corporation and technology company headquartered in Santa Clara, California. It is the world's largest semiconductor chip manufacturer by revenue, and is one of the developers of the x86 seri ...
8086
The 8086 (also called iAPX 86) is a 16-bit microprocessor chip designed by Intel between early 1976 and June 8, 1978, when it was released. The Intel 8088, released July 1, 1979, is a slightly modified chip with an external 8-bit data bus (allowi ...
, and the Zilog
Zilog, Inc. is an American manufacturer of microprocessors and 8-bit and 16-bit microcontrollers. It is also a supplier of application-specific embedded system-on-chip (SoC) products.
Its most famous product is the Z80 series of 8-bit microproc ...
Z80
The Z80 is an 8-bit microprocessor introduced by Zilog as the startup company's first product. The Z80 was conceived by Federico Faggin in late 1974 and developed by him and his 11 employees starting in early 1975. The first working samples we ...
. On these older processors, many exist as a side effect
In medicine, a side effect is an effect, whether therapeutic or adverse, that is secondary to the one intended; although the term is predominantly employed to describe adverse effects, it can also apply to beneficial, but unintended, consequenc ...
of the wiring of transistor
upright=1.4, gate (G), body (B), source (S) and drain (D) terminals. The gate is separated from the body by an insulating layer (pink).
A transistor is a semiconductor device used to Electronic amplifier, amplify or electronic switch, switch e ...
s in the CPU, and usually combine functions of the CPU that were not intended to be combined. On old and modern processors, there are also instructions intentionally included in the processor by the manufacturer, but that are not documented in any official specification.
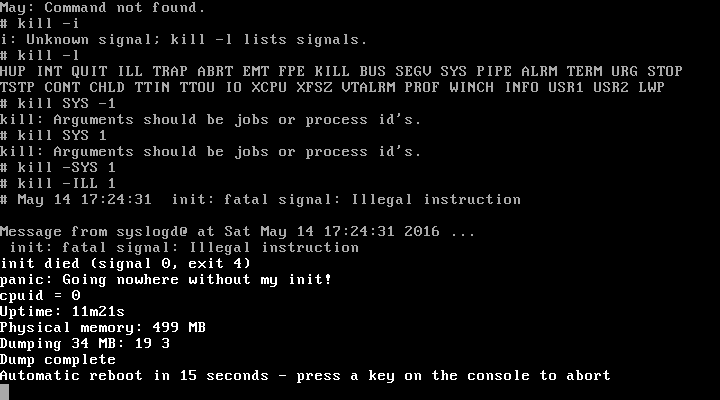
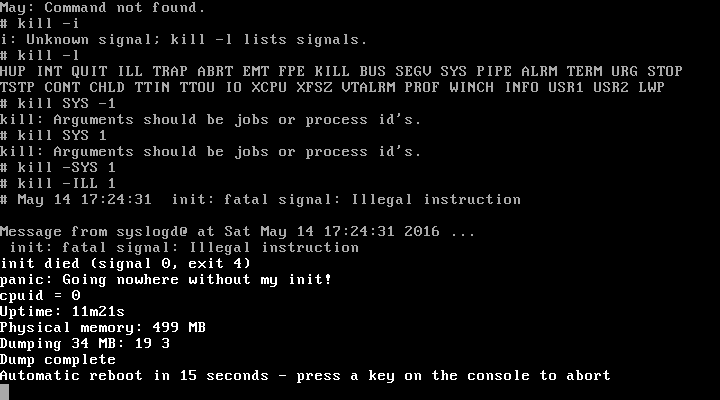
The effect of many illegal opcodes, on many processors, is just a trap to an error handler. However, some processors that trap for most illegal opcodes do not do so for some illegal opcodes, and some other processors do not check for illegal opcodes, and, instead, perform an undocumented operation.
Overview
While most accidental illegal instructions have useless or even highly undesirable effects (such as crashing the computer), some can have useful functions in certain situations. Such instructions were sometimes exploited incomputer game
Video games, also known as computer games, are electronic games that involves interaction with a user interface or input device such as a joystick, controller, keyboard, or motion sensing device to generate visual feedback. This feedback ...
s of the 1970s and 1980s to speed up certain time-critical sections. Another common use was in the ongoing battle between copy protection
Copy protection, also known as content protection, copy prevention and copy restriction, describes measures to enforce copyright by preventing the reproduction of software, films, music, and other media.
Copy protection is most commonly found o ...
implementations and cracking. Here, they were a form of security through obscurity
Security through obscurity (or security by obscurity) is the reliance in security engineering on design or implementation secrecy as the main method of providing security to a system or component.
History
An early opponent of security through obs ...
, and their secrecy usually did not last very long.
A danger associated with the use of illegal instructions was that, given the fact that the manufacturer does not guarantee their existence and function, they might disappear or behave differently with any change of the CPU internals or any new revision of the CPU, rendering programs that use them incompatible with the newer revisions. For example, a number of older Apple II
The Apple II (stylized as ) is an 8-bit home computer and one of the world's first highly successful mass-produced microcomputer products. It was designed primarily by Steve Wozniak; Jerry Manock developed the design of Apple II's foam-mol ...
games did not work correctly on the newer Apple IIc
The Apple IIc, the fourth model in the Apple II series of personal computers, is Apple Inc., Apple Computer's first endeavor to produce a portable computer. The result was a notebook-sized version of the Apple II that could be transported from ...
, because the latter used a newer CPU revision 65C02 that did away with illegal opcodes.
More recent CPUs, such as the 80186
The Intel 80186, also known as the iAPX 186, or just 186, is a microprocessor and microcontroller introduced in 1982. It was based on the Intel 8086 and, like it, had a 16-bit external data bus multiplexed with a 20-bit address bus. The 80188 ...
, 80286
The Intel 80286 (also marketed as the iAPX 286 and often called Intel 286) is a 16-bit microprocessor that was introduced on February 1, 1982. It was the first 8086-based CPU with separate, non- multiplexed address and data buses and also the ...
, 68000
The Motorola 68000 (sometimes shortened to Motorola 68k or m68k and usually pronounced "sixty-eight-thousand") is a 16/32-bit complex instruction set computer (CISC) microprocessor, introduced in 1979 by Motorola Semiconductor Products Sector ...
and its descendants, do not have illegal opcodes that are widely known/used. Ideally, the CPU will behave in a well-defined way when it finds an unknown opcode in the instruction stream, such as triggering a certain exception or fault condition. The operating system
An operating system (OS) is system software that manages computer hardware, software resources, and provides common daemon (computing), services for computer programs.
Time-sharing operating systems scheduler (computing), schedule tasks for ef ...
's exception or fault handler will then usually terminate the application that caused the fault, unless the program had previously established its own exception/fault handler, in which case that handler would receive control. Another, less common way of handling illegal instructions is by defining them to do nothing except taking up time and space (equivalent to the CPU's official NOP instruction); this method is used by the TMS9900
Introduced in June 1976, the TMS9900 was one of the first commercially available, single-chip 16-bit microprocessors. It implemented Texas Instruments' TI-990 minicomputer architecture in a single-chip format, and was initially used for low-end ...
and 65C02 processors, among others. Alternatively, unknown instructions can be emulated in software (e.g. LOADALL
LOADALL is the common name for two different, undocumented machine instructions of Intel 80286 and Intel 80386 processors, which allow access to areas of the internal processor state that are normally outside of the IA-32 API scope, like ''descri ...
), or even "new" pseudo-instructions can be implemented. Some BIOS
In computing, BIOS (, ; Basic Input/Output System, also known as the System BIOS, ROM BIOS, BIOS ROM or PC BIOS) is firmware used to provide runtime services for operating systems and programs and to perform hardware initialization during the b ...
es, memory managers, and operating systems take advantage of this, for example, to let V86 tasks communicate with the underlying system, i.e. BOP (from "BIOS Operation") utilized by the Windows NTVDM
Virtual DOS machines (VDM) refer to a technology that allows running 16-bit/32-bit DOS and 16-bit Windows programs when there is already another operating system running and controlling the hardware.
Overview
Virtual DOS machines can operate ei ...
.
In spite of Intel's guarantee against such instructions, research using techniques such as fuzzing
In programming and software development, fuzzing or fuzz testing is an automated software testing technique that involves providing invalid, unexpected, or random data as inputs to a computer program. The program is then monitored for exception ...
uncovered a vast number of undocumented instructions in x86 processors as late as 2018. Some of these instructions are shared across processor manufacturers, indicating that Intel and AMD
Advanced Micro Devices, Inc. (AMD) is an American multinational semiconductor company based in Santa Clara, California, that develops computer processors and related technologies for business and consumer markets. While it initially manufact ...
are both aware of the instruction and its purpose, despite it not appearing in any official specification. Other instructions are specific to manufacturers or specific product lines. The purpose of the majority of x86 undocumented instructions is unknown.
Today, the details of these instructions are mainly of interest for exact emulation
Emulation may refer to:
*Emulation (computing), imitation of behavior of a computer or other electronic system with the help of another type of system
:*Video game console emulator, software which emulates video game consoles
*Gaussian process em ...
of older systems.
See also
*Backdoor (computing)
A backdoor is a typically covert method of bypassing normal authentication or encryption in a computer, product, embedded device (e.g. a home router), or its embodiment (e.g. part of a cryptosystem, algorithm, chipset, or even a "homunculus com ...
* Don't care term
* Easter egg (media)
File:Carl Oswald Rostosky - Zwei Kaninchen und ein Igel 1861.jpg, 250px, An image that reveals an Easter egg when the hedgehog is clicked or tapped. Another Easter egg can be found in a tooltip when a mouse pointer is hovered over the hedgehog. ...
* Gadget (machine instruction sequence)
Return-oriented programming (ROP) is a computer security exploit technique that allows an attacker to execute code in the presence of security defenses such as executable space protection and code signing.
In this technique, an attacker gains con ...
* Halt and Catch Fire (computing)
In computer engineering, Halt and Catch Fire, known by the assembly mnemonic HCF, is an idiom referring to a computer machine code instruction that causes the computer's central processing unit (CPU) to cease meaningful operation, typically r ...
* Microcode
In processor design, microcode (μcode) is a technique that interposes a layer of computer organization between the central processing unit (CPU) hardware and the programmer-visible instruction set architecture of a computer. Microcode is a lay ...
* Pentium F00F bug
The Pentium F00F bug is a design flaw in the majority of Intel Pentium, Pentium MMX, and Pentium OverDrive processors (all in the P5 microarchitecture). Discovered in 1997, it can result in the processor ceasing to function until the computer ...
* Trap (computing)
In digital computers, an interrupt (sometimes referred to as a trap) is a request for the processor to ''interrupt'' currently executing code (when permitted), so that the event can be processed in a timely manner. If the request is accepted, ...
* Undocumented feature
An undocumented feature is an unintended or undocumented hardware operation, for example an undocumented instruction, or software feature found in computer hardware and software that is considered beneficial or useful. Sometimes the documentation ...
References
Further reading
* (NB. Illegal opcodes on the 6502.) * *https://web.archive.org/web/20190713083631/http://www.myquest.nl/z80undocumented/z80-documented.tex] (NB. Illegal opcodes on the Z80.) * {{cite web , editor-first=Ralf D. , editor-last=Brown , editor-link=Ralf D. Brown , url=https://www.cs.cmu.edu/~ralf/files.html , title=The x86 Interrupt List , edition=61 , date=2002-12-29 , orig-year=2000-07-17, 1985 , access-date=2011-10-14 , url-status=live , archive-url=https://web.archive.org/web/20170822194456/https://www.cs.cmu.edu/~ralf/files.html , archive-date=2017-08-22}
https://web.archive.org/web/20170902120420/https://www.cs.cmu.edu/~ralf/interrupt-list/inter61b.zi
https://web.archive.org/web/20170902120447/https://www.cs.cmu.edu/~ralf/interrupt-list/inter61d.zi
https://web.archive.org/web/20170902120507/https://www.cs.cmu.edu/~ralf/interrupt-list/inter61f.zi
(NB.
Ralf Brown's Interrupt List
Ralf Brown's Interrupt List (aka RBIL, x86 Interrupt List, MS-DOS Interrupt List or INTER) is a comprehensive list of interrupts, calls, hooks, interfaces, data structures, CMOS settings, memory and port addresses, as well as processor opcodes a ...
's also contains some information about undocumented processor opcodes and processor bugs: OPCODES.LST by Alex V. Potemkin and 86BUGS.LST by Harald Feldmann.)
External links
Christian Ludloff's site sandpile.org also contains info on undocumented opcodes
Machine code