Secure Shell on:
[Wikipedia]
[Google]
[Amazon]
The Secure Shell Protocol (SSH Protocol) is a
/ref> This version offers improved security and new features, but is not compatible with SSH-1. For example, it introduces new key-exchange mechanisms like Diffie–Hellman key exchange, improved
/ref> New features of SSH-2 include the ability to run any number of
 SSH is a protocol that can be used for many applications across many platforms including most
SSH is a protocol that can be used for many applications across many platforms including most
 The SSH protocol has a layered architecture with three separate components:
* The ''transport layer'' () typically uses the
The SSH protocol has a layered architecture with three separate components:
* The ''transport layer'' () typically uses the
draft-gerhards-syslog-transport-ssh
– ''SSH transport mapping for SYSLOG'' (July 2006)
draft-ietf-secsh-filexfer
– ''SSH File Transfer Protocol'' (July 2006)
draft-ietf-sshm-ssh-agent
- SSH Agent Protocol (March 2025) In addition, the OpenSSH project includes several vendor protocol specifications/extensions:
OpenSSH PROTOCOL overview
OpenSSH certificate/key overview
OpenSSH FIDO/u2f support
SSH Protocols
*
Original SSH source tarball
{{Authority control Application layer protocols Finnish inventions Software developed in Finland
cryptographic
Cryptography, or cryptology (from "hidden, secret"; and ''graphein'', "to write", or '' -logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More gen ...
network protocol for operating network service
In computer networking, a network service is an application running at the network layer and above, that provides data storage, manipulation, presentation, communication or other capability which is often implemented using a client–server or pe ...
s securely over an unsecured network. Its most notable applications are remote login
In computer security, logging in (or logging on, signing in, or signing on) is the process by which an individual gains access to a computer system or program by identifying and authenticating themselves.
Typically, user credential ...
and command-line execution.
SSH was designed for Unix-like
A Unix-like (sometimes referred to as UN*X, *nix or *NIX) operating system is one that behaves in a manner similar to a Unix system, although not necessarily conforming to or being certified to any version of the Single UNIX Specification. A Uni ...
operating systems as a replacement for Telnet and unsecured remote Unix shell
A Unix shell is a Command-line_interface#Command-line_interpreter, command-line interpreter or shell (computing), shell that provides a command line user interface for Unix-like operating systems. The shell is both an interactive command languag ...
protocols, such as the Berkeley Remote Shell (rsh) and the related rlogin and rexec protocols, which all use insecure, plaintext methods of authentication, like passwords.
Since mechanisms like Telnet and Remote Shell are designed to access and operate remote computers, sending the authentication tokens (e.g. username and password
A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services t ...
) for this access to these computers across a public network in an unsecured way poses a great risk of 3rd parties obtaining the password and achieving the same level of access to the remote system as the telnet user. Secure Shell mitigates this risk through the use of encryption mechanisms that are intended to hide the contents of the transmission from an observer, even if the observer has access to the entire data stream.
Finnish computer scientist Tatu Ylönen designed SSH in 1995 and provided an implementation in the form of two commands, and , as secure replacements for and , respectively. Subsequent development of the protocol suite proceeded in several developer groups, producing several variants of implementation. The protocol specification distinguishes two major versions, referred to as SSH-1 and SSH-2. The most commonly implemented software stack is OpenSSH, released in 1999 as open-source software by the OpenBSD developers. Implementations are distributed for all types of operating systems in common use, including embedded systems.
SSH applications are based on a client–server architecture, connecting an SSH client instance with an SSH server. SSH operates as a layered protocol suite comprising three principal hierarchical components: the ''transport layer'' provides server authentication, confidentiality, and integrity; the ''user authentication protocol'' validates the user to the server; and the ''connection protocol'' multiplexes the encrypted tunnel into multiple logical communication channels.
Definition
SSH usespublic-key cryptography
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public key and a corresponding private key. Key pairs are generated with cryptographic alg ...
to authenticate the remote computer and allow it to authenticate the user, if necessary.
SSH may be used in several methodologies. In the simplest manner, both ends of a communication channel use automatically generated public-private key pairs to encrypt a network connection, and then use a password
A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services t ...
to authenticate the user.
When the public-private key pair is generated by the user manually, the authentication is essentially performed when the key pair is created, and a session may then be opened automatically without a password prompt. In this scenario, the public key is placed on all computers that must allow access to the owner of the matching private key, which the owner keeps private. While authentication is based on the private key, the key is never transferred through the network during authentication. SSH only verifies that the same person offering the public key also owns the matching private key.
In all versions of SSH it is important to verify unknown public keys, i.e. associate the public keys with identities, before accepting them as valid. Accepting an attacker's public key without validation will authorize an unauthorized attacker as a valid user.
Authentication: OpenSSH key management
OnUnix-like
A Unix-like (sometimes referred to as UN*X, *nix or *NIX) operating system is one that behaves in a manner similar to a Unix system, although not necessarily conforming to or being certified to any version of the Single UNIX Specification. A Uni ...
systems, the list of authorized public keys is typically stored in the home directory of the user that is allowed to log in remotely, in the file ~/.ssh/authorized_keys. This file is respected by SSH only if it is not writable by anything apart from the owner and root. When the public key is present on the remote end and the matching private key is present on the local end, typing in the password is no longer required. However, for additional security the private key itself can be locked with a passphrase.
The private key can also be looked for in standard places, and its full path can be specified as a command line setting (the option -i for ssh). The ssh-keygen utility produces the public and private keys, always in pairs.
Use
SSH is typically used to log into a remote computer'sshell
Shell may refer to:
Architecture and design
* Shell (structure), a thin structure
** Concrete shell, a thin shell of concrete, usually with no interior columns or exterior buttresses
Science Biology
* Seashell, a hard outer layer of a marine ani ...
or command-line interface
A command-line interface (CLI) is a means of interacting with software via command (computing), commands each formatted as a line of text. Command-line interfaces emerged in the mid-1960s, on computer terminals, as an interactive and more user ...
(CLI) and to execute commands on a remote server. It also supports mechanisms for tunneling, forwarding of TCP ports and X11 connections and it can be used to transfer files using the associated SSH File Transfer Protocol
In computing, the SSH File Transfer Protocol, also known as Secure File Transfer Protocol (SFTP), is a network protocol that provides file access, file transfer, and file management over any reliable data stream. It was designed by the Inte ...
(SFTP) or Secure Copy Protocol (SCP).
SSH uses the client–server model
The client–server model is a distributed application structure that partitions tasks or workloads between the providers of a resource or service, called servers, and service requesters, called clients. Often clients and servers communicate ov ...
. An SSH client program is typically used for establishing connections to an SSH daemon, such as sshd, accepting remote connections. Both are commonly present on most modern operating systems, including macOS
macOS, previously OS X and originally Mac OS X, is a Unix, Unix-based operating system developed and marketed by Apple Inc., Apple since 2001. It is the current operating system for Apple's Mac (computer), Mac computers. With ...
, most distributions of Linux
Linux ( ) is a family of open source Unix-like operating systems based on the Linux kernel, an kernel (operating system), operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically package manager, pac ...
, OpenBSD, FreeBSD
FreeBSD is a free-software Unix-like operating system descended from the Berkeley Software Distribution (BSD). The first version was released in 1993 developed from 386BSD, one of the first fully functional and free Unix clones on affordable ...
, NetBSD
NetBSD is a free and open-source Unix-like operating system based on the Berkeley Software Distribution (BSD). It was the first open-source BSD descendant officially released after 386BSD was fork (software development), forked. It continues to ...
, Solaris and OpenVMS
OpenVMS, often referred to as just VMS, is a multi-user, multiprocessing and virtual memory-based operating system. It is designed to support time-sharing, batch processing, transaction processing and workstation applications. Customers using Op ...
. Notably, versions of Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sec ...
prior to Windows 10 version 1709 do not include SSH by default, but proprietary, freeware and open source
Open source is source code that is made freely available for possible modification and redistribution. Products include permission to use and view the source code, design documents, or content of the product. The open source model is a decentrali ...
versions of various levels of complexity and completeness did and do exist (see Comparison of SSH clients). In 2018 Microsoft
Microsoft Corporation is an American multinational corporation and technology company, technology conglomerate headquartered in Redmond, Washington. Founded in 1975, the company became influential in the History of personal computers#The ear ...
began porting the OpenSSH source code to Windows and in Windows 10 version 1709, an official Win32 port of OpenSSH is now available.
File managers for UNIX-like systems (e.g. Konqueror) can use the FISH
A fish (: fish or fishes) is an aquatic animal, aquatic, Anamniotes, anamniotic, gill-bearing vertebrate animal with swimming fish fin, fins and craniate, a hard skull, but lacking limb (anatomy), limbs with digit (anatomy), digits. Fish can ...
protocol to provide a split-pane GUI with drag-and-drop. The open source Windows program WinSCP provides similar file management (synchronization, copy, remote delete) capability using PuTTY as a back-end. Both WinSCP and PuTTY are available packaged to run directly off a USB drive, without requiring installation on the client machine. Crostini on ChromeOS comes with OpenSSH by default. Setting up an SSH server in Windows typically involves enabling a feature in the Settings app.
SSH is important in cloud computing
Cloud computing is "a paradigm for enabling network access to a scalable and elastic pool of shareable physical or virtual resources with self-service provisioning and administration on-demand," according to International Organization for ...
to solve connectivity problems, avoiding the security issues of exposing a cloud-based virtual machine directly on the Internet. An SSH tunnel can provide a secure path over the Internet, through a firewall to a virtual machine.
The IANA has assigned TCP port
A port is a maritime facility comprising one or more wharves or loading areas, where ships load and discharge cargo and passengers. Although usually situated on a sea coast or estuary, ports can also be found far inland, such as Hamburg, Manch ...
22, UDP port 22 and SCTP
The Stream Control Transmission Protocol (SCTP) is a computer networking communications protocol in the transport layer of the Internet protocol suite. Originally intended for Signaling System 7 (SS7) message transport in telecommunication, the ...
port 22 for this protocol. IANA had listed the standard TCP port 22 for SSH servers as one of the well-known ports as early as 2001. SSH can also be run using SCTP
The Stream Control Transmission Protocol (SCTP) is a computer networking communications protocol in the transport layer of the Internet protocol suite. Originally intended for Signaling System 7 (SS7) message transport in telecommunication, the ...
rather than TCP as the connection oriented transport layer protocol.
Historical development
Version 1
In 1995, Tatu Ylönen, a researcher at Helsinki University of Technology in Finland designed the first version of the protocol (now called SSH-1) prompted by a password- sniffing attack at his university network. The goal of SSH was to replace the earlier rlogin, TELNET,FTP
The File Transfer Protocol (FTP) is a standard communication protocol used for the transfer of computer files from a server to a client on a computer network. FTP is built on a client–server model architecture using separate control and dat ...
and rsh protocols, which did not provide strong authentication nor guarantee confidentiality. He chose the port number 22 because it is between telnet (port 23) and ftp (port 21).
Ylönen released his implementation as freeware in July 1995, and the tool quickly gained in popularity. Towards the end of 1995, the SSH user base had grown to 20,000 users in fifty countries.
In December 1995, Ylönen founded SSH Communications Security to market and develop SSH. The original version of the SSH software used various pieces of free software
Free software, libre software, libreware sometimes known as freedom-respecting software is computer software distributed open-source license, under terms that allow users to run the software for any purpose as well as to study, change, distribut ...
, such as GNU libgmp, but later versions released by SSH Communications Security evolved into increasingly proprietary software
Proprietary software is computer software, software that grants its creator, publisher, or other rightsholder or rightsholder partner a legal monopoly by modern copyright and intellectual property law to exclude the recipient from freely sharing t ...
.
It was estimated that by 2000 the number of users had grown to 2 million.
Version 2
In 2006, after being discussed in a working group named "secsh", a revised version of the SSH protocol, SSH-2 was adopted as a standard.RFC4252: The Secure Shell (SSH) Authentication Protocol, Jan 2006/ref> This version offers improved security and new features, but is not compatible with SSH-1. For example, it introduces new key-exchange mechanisms like Diffie–Hellman key exchange, improved
data integrity
Data integrity is the maintenance of, and the assurance of, data accuracy and consistency over its entire Information Lifecycle Management, life-cycle. It is a critical aspect to the design, implementation, and usage of any system that stores, proc ...
checking via message authentication codes like MD5 or SHA-1, which can be negotiated between client and server. SSH-2 also adds stronger encryption methods like AES which eventually replaced weaker and compromised ciphers from the previous standard like 3DES.RFC4252: The Secure Shell (SSH) Authentication Protocol, Jan 2006/ref> New features of SSH-2 include the ability to run any number of
shell
Shell may refer to:
Architecture and design
* Shell (structure), a thin structure
** Concrete shell, a thin shell of concrete, usually with no interior columns or exterior buttresses
Science Biology
* Seashell, a hard outer layer of a marine ani ...
sessions over a single SSH connection. Due to SSH-2's superiority and popularity over SSH-1, some implementations such as libssh (v0.8.0+), Lsh and Dropbear eventually supported only the SSH-2 protocol.
Version 1.99
In January 2006, well after version 2.1 was established, specified that an SSH server supporting 2.0 as well as prior versions should identify its protocol version as 1.99. This version number does not reflect a historical software revision, but a method to identifybackward compatibility
In telecommunications and computing, backward compatibility (or backwards compatibility) is a property of an operating system, software, real-world product, or technology that allows for interoperability with an older legacy system, or with Input ...
.
OpenSSH and OSSH
In 1999, developers, desiring availability of a free software version, restarted software development from the 1.2.12 release of the original SSH program, which was the last released under an open source license. This served as a code base for Björn Grönvall's OSSH software. Shortly thereafter, OpenBSD developers forked Grönvall's code and created OpenSSH, which shipped with Release 2.6 of OpenBSD. From this version, a "portability" branch was formed to port OpenSSH to other operating systems. , OpenSSH was the single most popular SSH implementation, being the default version in a large number of operating system distributions. OSSH meanwhile has become obsolete. OpenSSH continues to be maintained and supports the SSH-2 protocol, having expunged SSH-1 support from the codebase in the OpenSSH 7.6 release.Future
In 2023, an alternative to traditional SSH was proposed under the name SSH3 by PhD student François Michel and Professor Olivier Bonaventure and its code has been made open source. This new version implements the original SSH Connection Protocol but operates on top of HTTP/3, which runs on QUIC. It offers multiple features such as: * Faster session establishment, reducing the number of Round-trip delays from 5-7 to 3. * High security: while SSHv2 relies on its own protocols, SSH3 leverages TLS 1.3, QUIC, andHTTP
HTTP (Hypertext Transfer Protocol) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web, wher ...
.
* UDP port forwarding
* X.509 certificates
* OpenID Connect
However, the name SSH3 is under discussion, and the project aims to rename itself to a more suitable name. The discussion stems from the fact that this new implementation significantly revises the SSH protocol, suggesting it should not be called SSH3.
Uses
 SSH is a protocol that can be used for many applications across many platforms including most
SSH is a protocol that can be used for many applications across many platforms including most Unix
Unix (, ; trademarked as UNIX) is a family of multitasking, multi-user computer operating systems that derive from the original AT&T Unix, whose development started in 1969 at the Bell Labs research center by Ken Thompson, Dennis Ritchie, a ...
variants (Linux
Linux ( ) is a family of open source Unix-like operating systems based on the Linux kernel, an kernel (operating system), operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically package manager, pac ...
, the BSDs including Apple
An apple is a round, edible fruit produced by an apple tree (''Malus'' spp.). Fruit trees of the orchard or domestic apple (''Malus domestica''), the most widely grown in the genus, are agriculture, cultivated worldwide. The tree originated ...
's macOS
macOS, previously OS X and originally Mac OS X, is a Unix, Unix-based operating system developed and marketed by Apple Inc., Apple since 2001. It is the current operating system for Apple's Mac (computer), Mac computers. With ...
, and Solaris), as well as Microsoft Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sec ...
. Some of the applications below may require features that are only available or compatible with specific SSH clients or servers. For example, using the SSH protocol to implement a VPN is possible, but presently only with the OpenSSH server and client implementation.
* For login to a shell on a remote host (replacing Telnet and rlogin)
* For executing a single command on a remote host (replacing rsh)
* For setting up automatic (passwordless) login to a remote server (for example, using OpenSSH)
* In combination with rsync to back up, copy and mirror files efficiently and securely
* For forwarding a port
* For tunneling (not to be confused with a VPN, which routes packets between different networks, or bridges
A bridge is a structure built to span a physical obstacle (such as a body of water, valley, road, or railway) without blocking the path underneath. It is constructed for the purpose of providing passage over the obstacle, which is usually somet ...
two broadcast domain
A broadcast domain is a logical division of a computer network, in which all nodes can reach each other by broadcast at the data link layer. A broadcast domain can be within the same LAN segment or it can be bridged to other LAN segments.
In te ...
s into one).
* For using as a full-fledged encrypted VPN. Note that only OpenSSH server and client supports this feature.
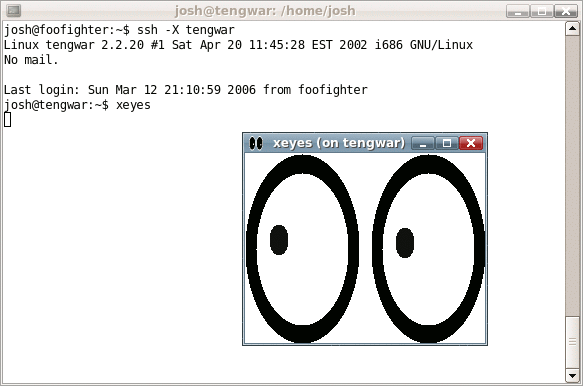
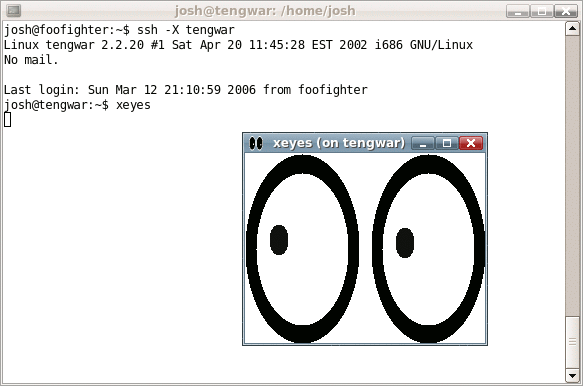
* For forwarding X from a remote host (possible through multiple intermediate hosts)
* For browsing the web through an encrypted proxy connection with SSH clients that support the SOCKS protocol.
* For securely mounting a directory on a remote server as a filesystem on a local computer using SSHFS.
* For automated remote monitoring and management of servers through one or more of the mechanisms discussed above.
* For development on a mobile or embedded device that supports SSH.
* For securing file transfer protocols.
File transfer protocols
The Secure Shell protocols are used in several file transfer mechanisms. * Secure copy (SCP), which evolved from RCP protocol over SSH * rsync, intended to be more efficient than SCP. Generally runs over an SSH connection. *SSH File Transfer Protocol
In computing, the SSH File Transfer Protocol, also known as Secure File Transfer Protocol (SFTP), is a network protocol that provides file access, file transfer, and file management over any reliable data stream. It was designed by the Inte ...
(SFTP), a secure alternative to FTP
The File Transfer Protocol (FTP) is a standard communication protocol used for the transfer of computer files from a server to a client on a computer network. FTP is built on a client–server model architecture using separate control and dat ...
(not to be confused with FTP over SSH or FTPS
FTPS (also known as FTP-SSL and FTP Secure) is an extension to the commonly used File Transfer Protocol (FTP) that adds support for the Transport Layer Security (TLS) and, formerly, the Secure Sockets Layer (SSL, which is now prohibited by RFC756 ...
)
* Files transferred over shell protocol (FISH), released in 1998, which evolved from Unix shell
A Unix shell is a Command-line_interface#Command-line_interpreter, command-line interpreter or shell (computing), shell that provides a command line user interface for Unix-like operating systems. The shell is both an interactive command languag ...
commands over SSH
* Fast and Secure Protocol (FASP), aka ''Aspera'', uses SSH for control and UDP ports for data transfer.
Architecture
Transmission Control Protocol
The Transmission Control Protocol (TCP) is one of the main communications protocol, protocols of the Internet protocol suite. It originated in the initial network implementation in which it complemented the Internet Protocol (IP). Therefore, th ...
(TCP) of TCP/IP
The Internet protocol suite, commonly known as TCP/IP, is a framework for organizing the communication protocols used in the Internet and similar computer networks according to functional criteria. The foundational protocols in the suite are ...
, reserving port number 22 as a server listening port. This layer handles initial key exchange as well as server authentication, and sets up encryption, compression, and integrity verification. It exposes to the upper layer an interface for sending and receiving plaintext packets with a size of up to 32,768 bytes each, but more can be allowed by each implementation. The transport layer also arranges for key re-exchange, usually after 1 GB of data has been transferred or after one hour has passed, whichever occurs first.
* The ''user authentication layer'' () handles client authentication, and provides a suite of authentication algorithms. Authentication is ''client-driven'': when one is prompted for a password, it may be the SSH client prompting, not the server. The server merely responds to the client's authentication requests. Widely used user-authentication methods include the following:
** ''password'': a method for straightforward password authentication, including a facility allowing a password to be changed. Not all programs implement this method.
** ''publickey'': a method for public-key-based authentication, usually supporting at least DSA, ECDSA or RSA keypairs, with other implementations also supporting X.509 certificates.
** ''keyboard-interactive'' (): a versatile method where the server sends one or more prompts to enter information and the client displays them and sends back responses keyed-in by the user. Used to provide one-time password authentication such as S/Key or SecurID. Used by some OpenSSH configurations when PAM is the underlying host-authentication provider to effectively provide password authentication, sometimes leading to inability to log in with a client that supports just the plain ''password'' authentication method.
** GSSAPI authentication methods which provide an extensible scheme to perform SSH authentication using external mechanisms such as Kerberos 5 or NTLM, providing single sign-on capability to SSH sessions. These methods are usually implemented by commercial SSH implementations for use in organizations, though OpenSSH does have a working GSSAPI implementation.
* The ''connection layer'' () defines the concept of channels, channel requests, and global requests, which define the SSH services provided. A single SSH connection can be multiplexed into multiple logical channels simultaneously, each transferring data bidirectionally. Channel requests are used to relay out-of-band channel-specific data, such as the changed size of a terminal window, or the exit code of a server-side process. Additionally, each channel performs its own flow control using the receive window size. The SSH client requests a server-side port to be forwarded using a global request. Standard channel types include:
** ''shell'' for terminal shells, SFTP and exec requests (including SCP transfers)
** ''direct-tcpip'' for client-to-server forwarded connections
** ''forwarded-tcpip'' for server-to-client forwarded connections
* The SSHFP DNS record (RFC 4255) provides the public host key fingerprints in order to aid in verifying the authenticity of the host.
This open architecture provides considerable flexibility, allowing the use of SSH for a variety of purposes beyond a secure shell. The functionality of the transport layer alone is comparable to Transport Layer Security
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network, such as the Internet. The protocol is widely used in applications such as email, instant messaging, and voice over ...
(TLS); the user-authentication layer is highly extensible with custom authentication methods; and the connection layer provides the ability to multiplex many secondary sessions into a single SSH connection, a feature comparable to BEEP and not available in TLS.
Algorithms
* EdDSA, ECDSA, RSA and DSA forpublic-key cryptography
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public key and a corresponding private key. Key pairs are generated with cryptographic alg ...
.
* ECDH and Diffie–Hellman for key exchange.
* HMAC, AEAD and UMAC for MAC.
* AES (and deprecated RC4, 3DES, DES) for symmetric encryption.
* AES-GCM and ChaCha20-Poly1305 for AEAD encryption.
* SHA (and deprecated MD5) for key fingerprint.
Vulnerabilities
SSH-1
In 1998, a vulnerability was described in SSH 1.5 which allowed the unauthorized insertion of content into an encrypted SSH stream due to insufficient data integrity protection from CRC-32 used in this version of the protocol. A fix known as SSH Compensation Attack Detector was introduced into most implementations. Many of these updated implementations contained a newinteger overflow
In computer programming, an integer overflow occurs when an arithmetic operation on integers attempts to create a numeric value that is outside of the range that can be represented with a given number of digits – either higher than the maximu ...
vulnerability that allowed attackers to execute arbitrary code with the privileges of the SSH daemon, typically root.
In January 2001 a vulnerability was discovered that allows attackers to modify the last block of an IDEA
In philosophy and in common usage, an idea (from the Greek word: ἰδέα (idea), meaning 'a form, or a pattern') is the results of thought. Also in philosophy, ideas can also be mental representational images of some object. Many philosophe ...
-encrypted session. The same month, another vulnerability was discovered that allowed a malicious server to forward a client authentication to another server.
Since SSH-1 has inherent design flaws which make it vulnerable, it is now generally considered obsolete and should be avoided by explicitly disabling fallback to SSH-1. Most modern servers and clients support SSH-2.
CBC plaintext recovery
In November 2008, a theoretical vulnerability was discovered for all versions of SSH which allowed recovery of up to 32 bits of plaintext from a block of ciphertext that was encrypted using what was then the standard default encryption mode, CBC. The most straightforward solution is to use CTR, counter mode, instead of CBC mode, since this renders SSH resistant to the attack.Suspected decryption by NSA
On December 28, 2014 ''Der Spiegel
(, , stylized in all caps) is a German weekly news magazine published in Hamburg. With a weekly circulation of about 724,000 copies in 2022, it is one of the largest such publications in Europe. It was founded in 1947 by John Seymour Chaloner ...
'' published classified information leaked by whistleblower Edward Snowden which suggests that the National Security Agency
The National Security Agency (NSA) is an intelligence agency of the United States Department of Defense, under the authority of the director of national intelligence (DNI). The NSA is responsible for global monitoring, collection, and proces ...
may be able to decrypt some SSH traffic. The technical details associated with such a process were not disclosed. A 2017 analysis of the CIA hacking tools ''BothanSpy'' and ''Gyrfalcon'' suggested that the SSH protocol was not compromised.
Terrapin attack
A novel man-in-the-middle attack against most current ssh implementations was discovered in 2023. It was named the Terrapin attack by its discoverers. However, the risk is mitigated by the requirement to intercept a genuine ssh session, and that the attack is restricted in its scope, fortuitously resulting mostly in failed connections. The ssh developers have stated that the major impact of the attack is to degrade the keystroke timing obfuscation features of ssh. The vulnerability was fixed in OpenSSH 9.6, but requires both client and server to be upgraded for the fix to be fully effective.Standards documentation
The following RFC publications by theIETF
The Internet Engineering Task Force (IETF) is a standards organization for the Internet standard, Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster ...
"secsh" working group
A working group is a group of experts working together to achieve specified goals. Such groups are domain-specific and focus on discussion or activity around a specific subject area. The term can sometimes refer to an interdisciplinary collab ...
document SSH-2 as a proposed Internet standard
In computer network engineering, an Internet Standard is a normative specification of a technology or methodology applicable to the Internet. Internet Standards are created and published by the Internet Engineering Task Force (IETF). They allow ...
.
* – ''The Secure Shell (SSH) Protocol Assigned Numbers''
* – ''The Secure Shell (SSH) Protocol Architecture''
* – ''The Secure Shell (SSH) Authentication Protocol''
* – ''The Secure Shell (SSH) Transport Layer Protocol''
* – ''The Secure Shell (SSH) Connection Protocol''
* – ''Using DNS to Securely Publish Secure Shell (SSH) Key Fingerprints''
* – ''Generic Message Exchange Authentication for the Secure Shell Protocol (SSH)''
* – ''The Secure Shell (SSH) Session Channel Break Extension''
* – ''The Secure Shell (SSH) Transport Layer Encryption Modes''
* – ''Improved Arcfour Modes for the Secure Shell (SSH) Transport Layer Protocol''
The protocol specifications were later updated by the following publications:
* – ''Diffie-Hellman Group Exchange for the Secure Shell (SSH) Transport Layer Protocol'' (March 2006)
* – ''RSA Key Exchange for the Secure Shell (SSH) Transport Layer Protocol'' (March 2006)
* – ''Generic Security Service Application Program Interface (GSS-API) Authentication and Key Exchange for the Secure Shell (SSH) Protocol'' (May 2006)
* – ''The Secure Shell (SSH) Public Key File Format'' (November 2006)
* – ''Secure Shell Public Key Subsystem'' (March 2007)
* – ''AES Galois Counter Mode for the Secure Shell Transport Layer Protocol'' (August 2009)
* – ''Elliptic Curve Algorithm Integration in the Secure Shell Transport Layer'' (December 2009)
* – ''X.509v3 Certificates for Secure Shell Authentication'' (March 2011)
* – ''Suite B Cryptographic Suites for Secure Shell (SSH)'' (May 2011)
* – ''Use of the SHA-256 Algorithm with RSA, Digital Signature Algorithm (DSA), and Elliptic Curve DSA (ECDSA) in SSHFP Resource Records'' (April 2012)
* – ''SHA-2 Data Integrity Verification for the Secure Shell (SSH) Transport Layer Protocol'' (July 2012)
* – '' Ed25519 SSHFP Resource Records'' (March 2015)
* – ''Secure Shell Transport Model for the Simple Network Management Protocol (SNMP)'' (June 2009)
* – ''Using the NETCONF Protocol over Secure Shell (SSH)'' (June 2011)
* – ''Use of RSA Keys with SHA-256 and SHA-512 in the Secure Shell (SSH) Protocol'' (March 2018)
* – ''Ed25519 and Ed448 Public Key Algorithms for the Secure Shell (SSH) Protocol'' (February 2020)
draft-gerhards-syslog-transport-ssh
– ''SSH transport mapping for SYSLOG'' (July 2006)
draft-ietf-secsh-filexfer
– ''SSH File Transfer Protocol'' (July 2006)
draft-ietf-sshm-ssh-agent
- SSH Agent Protocol (March 2025) In addition, the OpenSSH project includes several vendor protocol specifications/extensions:
OpenSSH PROTOCOL overview
OpenSSH certificate/key overview
OpenSSH FIDO/u2f support
See also
* Brute-force attack * Comparison of SSH clients * Comparison of SSH servers * Corkscrew * Ident * OpenSSH * Secure Shell tunneling * Web-based SSHReferences
Further reading
* * * Original announcement of Ssh *External links
SSH Protocols
*
Original SSH source tarball
{{Authority control Application layer protocols Finnish inventions Software developed in Finland