Softethervpn Trans on:
[Wikipedia]
[Google]
[Amazon]
SoftEther VPN is free 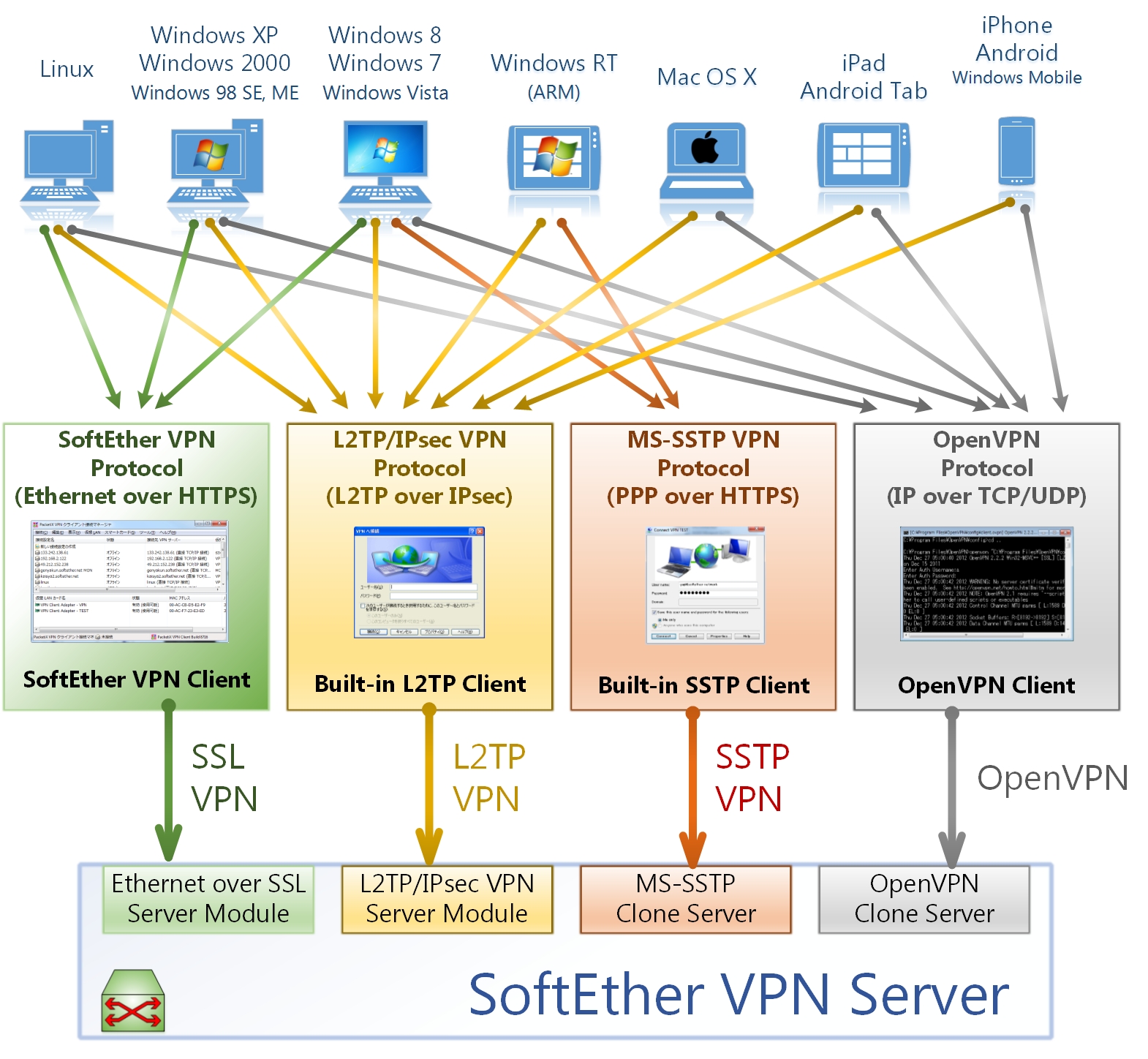
 A Virtual Hub is the software-emulated virtual Ethernet switch. It learns and maintains its own forwarding-database table inside. While traditional physical Ethernet switches implement this function by hardware, SoftEther VPN implements the same function by software. A VPN Server can have several Virtual Hubs. Each Virtual Hub is isolated. A Virtual Hub performs the packet-switching between concurrently connected VPN sessions to realize the communication between VPN Clients and VPN Bridges.
When there are several Virtual Hubs in a single instance of VPN Server, these Virtual Hubs are isolated for security. Each different administrator can have the delegated privilege for each correspondent Virtual Hub. An administrator for a Virtual Hub can define user-objects and ACLs, limited only the delegated Virtual Hub.
A Virtual Hub is the software-emulated virtual Ethernet switch. It learns and maintains its own forwarding-database table inside. While traditional physical Ethernet switches implement this function by hardware, SoftEther VPN implements the same function by software. A VPN Server can have several Virtual Hubs. Each Virtual Hub is isolated. A Virtual Hub performs the packet-switching between concurrently connected VPN sessions to realize the communication between VPN Clients and VPN Bridges.
When there are several Virtual Hubs in a single instance of VPN Server, these Virtual Hubs are isolated for security. Each different administrator can have the delegated privilege for each correspondent Virtual Hub. An administrator for a Virtual Hub can define user-objects and ACLs, limited only the delegated Virtual Hub.
 One of the key features of SoftEther VPN is the transparency for firewalls, proxy servers, and NATs (Network Address Translators). To do this, SoftEther VPN supports SSL-VPN and NAT Traversal.
SoftEther VPN uses HTTPS protocol in order to establish a VPN tunnel. HTTPS (HTTP over SSL) protocol uses the TCP/IP port 443 (may vary) as destination.
One of the key features of SoftEther VPN is the transparency for firewalls, proxy servers, and NATs (Network Address Translators). To do this, SoftEther VPN supports SSL-VPN and NAT Traversal.
SoftEther VPN uses HTTPS protocol in order to establish a VPN tunnel. HTTPS (HTTP over SSL) protocol uses the TCP/IP port 443 (may vary) as destination.
VPN Gate
{{VPN Virtual private networks Free security software 2014 software
open-source
Open source is source code that is made freely available for possible modification and redistribution. Products include permission to use the source code, design documents, or content of the product. The open-source model is a decentralized sof ...
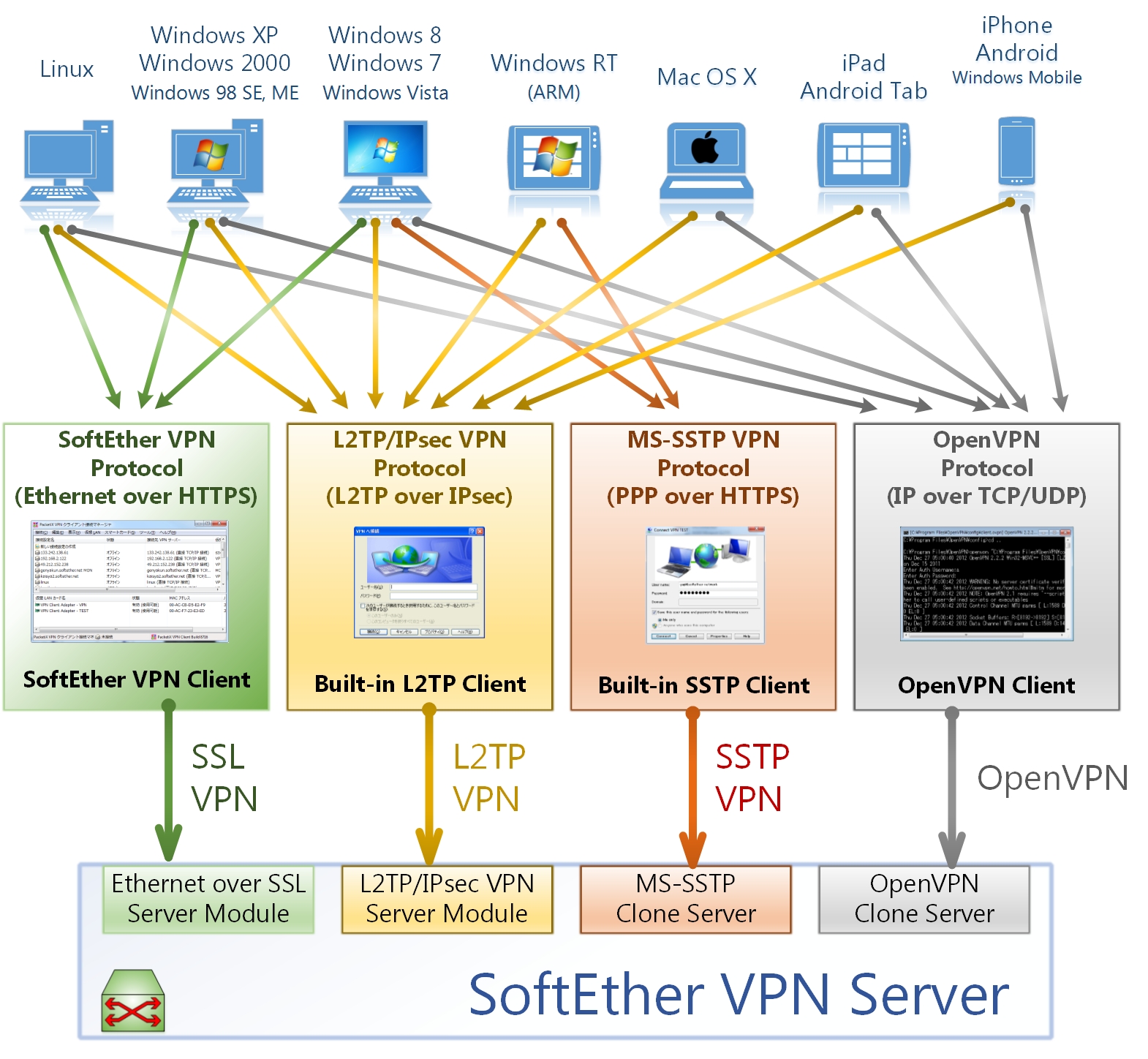
, cross-platform, multi-protocol VPN
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. The be ...
client and VPN server software, developed as part of Daiyuu Nobori's master's thesis research at the University of Tsukuba
is a public research university located in Tsukuba, Ibaraki, Japan. It is a top 10 Designated National University, and was ranked Type A by the Japanese government as part of the Top Global University Project.
The university has 28 colle ...
. VPN protocols such as SSL VPN, L2TP In computer networking, Layer 2 Tunneling Protocol (L2TP) is a tunneling protocol used to support virtual private networks (VPNs) or as part of the delivery of services by ISPs. It uses encryption ('hiding') only for its own control messages (usin ...
/IPsec
In computing, Internet Protocol Security (IPsec) is a secure network protocol suite that authenticates and encrypts packets of data to provide secure encrypted communication between two computers over an Internet Protocol network. It is used in ...
, OpenVPN
OpenVPN is a virtual private network (VPN) system that implements techniques to create secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It implements both client-server architect ...
, and Microsoft Secure Socket Tunneling Protocol
Secure Socket Tunneling Protocol (SSTP) is a form of virtual private network (VPN) tunnel that provides a mechanism to transport PPP traffic through an SSL/TLS channel. SSL/TLS provides transport-level security with key negotiation, encryption a ...
are provided in a single VPN server. It was released using the GPLv2
The GNU General Public License (GNU GPL or simply GPL) is a series of widely used free software licenses that guarantee end users the four freedoms to run, study, share, and modify the software. The license was the first copyleft for general u ...
license on January 4, 2014. The license was switched to Apache License 2.0 on January 21, 2019.
SoftEther VPN supports NAT traversal
Network address translation traversal is a computer networking technique of establishing and maintaining Internet protocol connections across gateways that implement network address translation (NAT).
NAT traversal techniques are required for m ...
, making it useful to run VPN servers on computers that are behind residential gateway
A residential gateway is a small consumer-grade gateway which bridges network access between connected local area network (LAN) hosts to a wide area network (WAN) (such as the Internet) via a modem, or directly connects to a WAN (as in EttH), whi ...
s, facility routers, and firewall
Firewall may refer to:
* Firewall (computing), a technological barrier designed to prevent unauthorized or unwanted communications between computer networks or hosts
* Firewall (construction), a barrier inside a building, designed to limit the spre ...
s. Firewalls performing deep packet inspection
Deep packet inspection (DPI) is a type of data processing that inspects in detail the data being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep packet inspection is oft ...
are unable to detect SoftEther's VPN transport packets as a VPN tunnel because HTTPS is used to camouflage the connection.
SoftEther VPN optimizes performance by using full Ethernet frame utilization, reducing memory copy operations, parallel transmission, and clustering. Together, these reduce latency normally associated with VPN connections while increasing throughput.
Interoperability
SoftEther VPN Server and VPN Bridge run onWindows
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry. For example, Windows NT for consumers, Windows Server for ...
, Linux
Linux ( or ) is a family of open-source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically packaged as a Linux distribution, which i ...
, OS X
macOS (; previously OS X and originally Mac OS X) is a Unix operating system developed and marketed by Apple Inc. since 2001. It is the primary operating system for Apple's Mac computers. Within the market of desktop and la ...
up to OS X 10.8
OS X Mountain Lion (version 10.8) is the ninth software versioning, major release of macOS, Apple Inc.'s desktop and Server (computing), server operating system for Macintosh computers. OS X Mountain Lion was released on July 25, 2012, for purch ...
, FreeBSD
FreeBSD is a free and open-source Unix-like operating system descended from the Berkeley Software Distribution (BSD), which was based on Research Unix. The first version of FreeBSD was released in 1993. In 2005, FreeBSD was the most popular ...
, and Solaris operating systems. SoftEther VPN Client runs on Windows
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry. For example, Windows NT for consumers, Windows Server for ...
, Linux
Linux ( or ) is a family of open-source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically packaged as a Linux distribution, which i ...
, and macOS
macOS (; previously OS X and originally Mac OS X) is a Unix operating system developed and marketed by Apple Inc. since 2001. It is the primary operating system for Apple's Mac (computer), Mac computers. Within the market of ...
.
SoftEther VPN Server serves the SoftEther VPN protocol, but it also serves OpenVPN
OpenVPN is a virtual private network (VPN) system that implements techniques to create secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It implements both client-server architect ...
, Microsoft Secure Socket Tunneling Protocol
Secure Socket Tunneling Protocol (SSTP) is a form of virtual private network (VPN) tunnel that provides a mechanism to transport PPP traffic through an SSL/TLS channel. SSL/TLS provides transport-level security with key negotiation, encryption a ...
(SSTP), SSL VPN, EtherIP, L2TPv3
Layer 2 Tunnelling Protocol version 3 is an IETF standard related to L2TP that can be used as an alternative protocol to Multiprotocol Label Switching (MPLS) for encapsulation of multiprotocol Layer 2 communications traffic over IP networks. ...
, and IPsec
In computing, Internet Protocol Security (IPsec) is a secure network protocol suite that authenticates and encrypts packets of data to provide secure encrypted communication between two computers over an Internet Protocol network. It is used in ...
. It serves mobile devices running iOS
iOS (formerly iPhone OS) is a mobile operating system created and developed by Apple Inc. exclusively for its hardware. It is the operating system that powers many of the company's mobile devices, including the iPhone; the term also include ...
, Android
Android may refer to:
Science and technology
* Android (robot), a humanoid robot or synthetic organism designed to imitate a human
* Android (operating system), Google's mobile operating system
** Bugdroid, a Google mascot sometimes referred to ...
, and Windows Phone via L2TP In computer networking, Layer 2 Tunneling Protocol (L2TP) is a tunneling protocol used to support virtual private networks (VPNs) or as part of the delivery of services by ISPs. It uses encryption ('hiding') only for its own control messages (usin ...
/IPsec
In computing, Internet Protocol Security (IPsec) is a secure network protocol suite that authenticates and encrypts packets of data to provide secure encrypted communication between two computers over an Internet Protocol network. It is used in ...
.
VPN clients and endpoints supporting other VPN protocols may also be used; this includes many routers from Cisco, Juniper, Linksys (with DD-WRT
DD-WRT is Linux-based firmware for wireless routers and Wireless access point, access points. Originally designed for the Linksys WRT54G series, it now runs on a wide variety of models. DD-WRT is one of a handful of List of router firmware proj ...
), Asus, and others.
VPN Server
SoftEther VPN Server implements the VPN server function. It listens and accepts connections from VPN Client or VPN Bridge with several VPN protocols. A VPN Server can have several Virtual Hubs and Virtual Layer-3 Switches. A Virtual Hub has full layer-2 Ethernet packet-switching functions like a physical Ethernet switch. Additionally, a Virtual Hub can be configured to define IP packet filter entries to filter the packets through the Virtual Hub. A Virtual Layer-3 Switch has layer-3 IP static routing functions like a physical router. A VPN Server can have local bridges. A local bridge is the layer-2 packet-switching fabric between a physical Ethernet network-adapter and a Virtual Hub. The administrator defines a local bridge between the Virtual Hub and the existing corporate network to build a remote-access VPN server or a site-to-site VPN server.VPN Client
SoftEther VPN Client is a VPN client program which has the virtualized function of an Ethernet network adapter. A computer with installed SoftEther VPN Client can establish a VPN connection to the VPN Server. Since the VPN Server has the support for multiple VPN protocols such as L2TP/IPsec or MS-SSTP VPN, VPN users are not required to install SoftEther VPN Client on client computers. When a user uses L2TP/IPsec or MS-SSTP VPN to connect to the VPN Server, the built-in VPN client programs on the operating system can be used to establish a VPN to the VPN Server. However, SoftEther VPN Client has advanced functions (e.g. more detailed VPN communication settings) than OS built-in VPN clients. To exploit the full performance of SoftEther VPN Server, it is recommended to install SoftEther VPN Client on each client computer.VPN Bridge
SoftEther VPN Bridge is a VPN program for building a site-to-site VPN. To build a site-to-site VPN network, the system administrator has to install SoftEther VPN Server on the central site, and has to install SoftEther VPN Bridge on one or more remote sites. A VPN Bridge connects to the central VPN Server by cascade connection. A cascade connection is similar to, but a virtualization of, an uplink connection (cross-cable connection) between two physical Ethernet switches.VPN Server Manager for Windows
The GUI Tool is the administrative tool for SoftEther VPN Server and SoftEther VPN Bridge. It is a program that runs on both Windows and Linux with WINE. A system administrator installs the GUI Tool on his laptop PC, and makes it connect to the remote VPN Server or VPN Bridge for administration. The connection is made by SSL session, and management commands are transported as RPC over SSL.Command-line admin utility
vpncmd is the CUI administrative tool for SoftEther VPN Server, Client and Bridge. It is a program that runs on consoles of every supported operating systems. When a user is unable to use Windows or Linux with WINE, the user can alternatively use vpncmd to manage the VPN programs. vpncmd is also useful to execute a batch operation, such as creating many users on the Virtual Hub, or creating many Virtual Hubs on the VPN Server.Architecture
Some parts of the architecture of SoftEther VPN are different from typical traditional IPsec-based VPN systems.Virtual Hub
 A Virtual Hub is the software-emulated virtual Ethernet switch. It learns and maintains its own forwarding-database table inside. While traditional physical Ethernet switches implement this function by hardware, SoftEther VPN implements the same function by software. A VPN Server can have several Virtual Hubs. Each Virtual Hub is isolated. A Virtual Hub performs the packet-switching between concurrently connected VPN sessions to realize the communication between VPN Clients and VPN Bridges.
When there are several Virtual Hubs in a single instance of VPN Server, these Virtual Hubs are isolated for security. Each different administrator can have the delegated privilege for each correspondent Virtual Hub. An administrator for a Virtual Hub can define user-objects and ACLs, limited only the delegated Virtual Hub.
A Virtual Hub is the software-emulated virtual Ethernet switch. It learns and maintains its own forwarding-database table inside. While traditional physical Ethernet switches implement this function by hardware, SoftEther VPN implements the same function by software. A VPN Server can have several Virtual Hubs. Each Virtual Hub is isolated. A Virtual Hub performs the packet-switching between concurrently connected VPN sessions to realize the communication between VPN Clients and VPN Bridges.
When there are several Virtual Hubs in a single instance of VPN Server, these Virtual Hubs are isolated for security. Each different administrator can have the delegated privilege for each correspondent Virtual Hub. An administrator for a Virtual Hub can define user-objects and ACLs, limited only the delegated Virtual Hub.
Virtual Network Adapter
A Virtual Network Adapter is the software-emulated virtual Ethernet adapter. A VPN Client can create several Virtual Network Adapters on the client computer. A VPN user can establish a VPN session between the Virtual Network Adapter and the destination Virtual Hub of the remote VPN Server. While the VPN session is established, the VPN user can communicate to the remote VPN network through the Virtual Network Adapter. Since the Virtual Network Adapter works as if it were the physical one, any applications or operating system components can be used without any modification.Virtual Layer-3 Switch
A Virtual Layer-3 Switch is the software-emulated virtual IP router. Several Virtual Layer-3 Switches can be created on a single VPN Server instance. A Virtual Layer-3 Switch has virtual IP interfaces connected to Virtual Hubs. It also has several static routing table entries. The Virtual Layer-3 Switch is useful to make a large-scale site-to-site VPN network. Although the easy way to make a site-to-site VPN network is to build the layer-2 bridging based VPN, if the number of computers is huge the number of broadcasting packets will increase to load the inter-site links. To prevent that scaling problem, the VPN administrator isolates IP networks by Virtual Layer-3 switch.Cascade Connection between Virtual Hubs
The administrator can define a cascade connection between local or remote Virtual Hubs. After the cascade connection has been established, the originally-isolated two Ethernet segments are combined to the single Ethernet segment. Therefore, the cascade connection function is used to build the site-to-site layer-2 Ethernet bridging.Local Bridge between Virtual Hubs and physical Ethernet segment
Since Virtual Hubs and Virtual Network Adapters are only software-emulated virtual Ethernet devices, the Ethernet packets through these virtual devices cannot communicate with physical Ethernet devices. Therefore, a bridge between the virtual and the physical is necessary to build a remote-access VPN or site-to-site VPN. To make a bridge, the Local Bridge function exchanges the Ethernet packets between a Virtual Hub and a physical Ethernet network adapter to combine both isolated Ethernet segments into a single Ethernet segment. After defining the Local Bridge on SoftEther VPN Server, any VPN Client can connect to the VPN Server and communicate to all existing Ethernet devices (e.g. servers or network equipment) through the Local Bridge. This is called a remote-access VPN. If the network administrator sets up the remote-site VPN Bridge, and defines two Local Bridges on both VPN Server and VPN Bridge, and defines a cascade connection between VPN Server and VPN Bridge, then the remote two Ethernet segments are connected directly in layer-2 Ethernet level. This is called a site-to-site VPN.Firewall, proxy, and NAT transparency
 One of the key features of SoftEther VPN is the transparency for firewalls, proxy servers, and NATs (Network Address Translators). To do this, SoftEther VPN supports SSL-VPN and NAT Traversal.
SoftEther VPN uses HTTPS protocol in order to establish a VPN tunnel. HTTPS (HTTP over SSL) protocol uses the TCP/IP port 443 (may vary) as destination.
One of the key features of SoftEther VPN is the transparency for firewalls, proxy servers, and NATs (Network Address Translators). To do this, SoftEther VPN supports SSL-VPN and NAT Traversal.
SoftEther VPN uses HTTPS protocol in order to establish a VPN tunnel. HTTPS (HTTP over SSL) protocol uses the TCP/IP port 443 (may vary) as destination.
Parallel transmission mechanism of multiple SSL-VPN tunnels
When the user chooses SSL-VPN protocol between the VPN Client and VPN Server, SoftEther VPN Server and VPN Client use a parallel transmission mechanism to improve the throughput of the SSL-VPN tunnel. A user can set up the number of concurrent parallel transmission channels from 1 to 32. In an environment such as a slow and delaying network, this performance tuning will result in a faster throughput. When this function is enabled, the logical VPN Session will consist of several TCP (HTTPS) connections. All packets will be added to one of the appropriate TCP connections with calculations of optimizing modules. If some packet losses have been detected on a TCP connection of the logical VPN Session, then the new packet will use another healthy VPN connection. This fast-switching optimization to determine the processing TCP connection enables high throughput.NAT traversal
Traditional VPN systems require the user to ask the firewall's administrator of the company to open an endpoint (TCP or UDP port) on the firewall or NAT on the border between the company and the Internet. In order to reduce the necessity to open an endpoint on the firewall, SoftEther VPN Server has the NAT Traversal function. NAT Traversal is enabled by default. As long as it is enabled, SoftEther VPN Client computers can connect to your VPN Server behind the firewall or NAT. No special settings on the firewall or NAT are necessary.VPN over ICMP, and VPN over DNS
A few very-restricted networks only permit to pass ICMP orDNS
The Domain Name System (DNS) is a hierarchical and distributed naming system for computers, services, and other resources in the Internet or other Internet Protocol (IP) networks. It associates various information with domain names assigned to ...
packets. On such a network, TCP or UDP are filtered. Only ICMP and DNS are permitted. In order to make it possible to establish a SoftEther VPN client-server session via such a very-restricted network, SoftEther VPN has the " VPN over ICMP" and the "VPN over DNS" function.
This function is very powerful to penetrate such a restricted firewall. All VPN packets are encapsulated into ICMP or DNS packets to transmit over the firewall. The receiver-side endpoint extracts the inner packet from the capsuled packet. This is useful for exploiting public Wi-Fi
Wi-Fi () is a family of wireless network protocols, based on the IEEE 802.11 family of standards, which are commonly used for local area networking of devices and Internet access, allowing nearby digital devices to exchange data by radio w ...
. Some public Wi-Fi can pass only ICMP or DNS packets. They filter TCP or UDP packets. If you have a VPN Server installed on your home or office in advance of going outdoors, you can enjoy protocol-free network communication by using such a restricted network.
VPN Gate
VPN Gate is a plugin for SoftEther VPN, which allows users to connect to free VPN servers, run by volunteers who use SoftEther to host their VPN servers. Volunteers use personal computers as "servers". VPN Gate is sponsored by theUniversity of Tsukuba
is a public research university located in Tsukuba, Ibaraki, Japan. It is a top 10 Designated National University, and was ranked Type A by the Japanese government as part of the Top Global University Project.
The university has 28 colle ...
.
See also
*OpenVPN
OpenVPN is a virtual private network (VPN) system that implements techniques to create secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It implements both client-server architect ...
, an open-source VPN program
*UDP hole punching
UDP hole punching is a commonly used technique employed in network address translation (NAT) applications for maintaining User Datagram Protocol (UDP) packet streams that traverse the NAT. NAT traversal techniques are typically required for cli ...
, a technique for establishing UDP "connections" between firewalled/NATed network nodes
*Secure Socket Tunneling Protocol
Secure Socket Tunneling Protocol (SSTP) is a form of virtual private network (VPN) tunnel that provides a mechanism to transport PPP traffic through an SSL/TLS channel. SSL/TLS provides transport-level security with key negotiation, encryption a ...
(SSTP) Microsoft method for implementing PPP over SSL VPN
References
External links
*VPN Gate
{{VPN Virtual private networks Free security software 2014 software