Fast-flux DNS on:
[Wikipedia]
[Google]
[Amazon]
 Fast flux is a
Fast flux is a
 Fast-fluxing is generally classified into two types: single fluxing and double fluxing, a build-on implementation over single fluxing. The phraseologies involved in fast-fluxing includes "flux-herder mothership nodes" and "fast-flux agent nodes", referred to the backend
Fast-fluxing is generally classified into two types: single fluxing and double fluxing, a build-on implementation over single fluxing. The phraseologies involved in fast-fluxing includes "flux-herder mothership nodes" and "fast-flux agent nodes", referred to the backend
 Fast flux is a
Fast flux is a domain name system
The Domain Name System (DNS) is a hierarchical and distributed naming system for computers, services, and other resources in the Internet or other Internet Protocol (IP) networks. It associates various information with domain names assigned ...
(DNS) based evasion technique used by cyber criminals to hide phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious softwar ...
and malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, de ...
delivery websites behind an ever-changing network of compromised hosts acting as reverse proxies
In computer networks, a reverse proxy is the application that sits in front of back-end applications and forwards client (e.g. browser) requests to those applications. Reverse proxies help increase scalability, performance, resilience and securi ...
to the backend botnet master—a bulletproof
Bulletproofing is the process of making an object capable of stopping a bullet or similar high velocity projectiles (e.g. shrapnel). The term bullet resistance is often preferred because few, if any, practical materials provide complete protectio ...
autonomous system Autonomous system may refer to:
* Autonomous system (Internet), a collection of IP networks and routers under the control of one entity
* Autonomous system (mathematics), a system of ordinary differential equations which does not depend on the inde ...
s. It can also refer to the combination of peer-to-peer networking, distributed command and control
Command and control (abbr. C2) is a "set of organizational and technical attributes and processes ... hatemploys human, physical, and information resources to solve problems and accomplish missions" to achieve the goals of an organization or e ...
, web-based load balancing and proxy redirection used to make malware networks more resistant to discovery and counter-measures.
The fundamental idea behind fast-flux is to have numerous IP address
An Internet Protocol address (IP address) is a numerical label such as that is connected to a computer network that uses the Internet Protocol for communication.. Updated by . An IP address serves two main functions: network interface ident ...
es associated with a single fully qualified domain name
A fully qualified domain name (FQDN), sometimes also referred to as an ''absolute domain name'', is a domain name that specifies its exact location in the tree hierarchy of the Domain Name System (DNS). It specifies all domain levels, including th ...
, where the IP addresses are swapped in and out with extremely high frequency, through changing DNS resource records, thus the authoritative name servers of the said fast-fluxing domain name
A domain name is a string that identifies a realm of administrative autonomy, authority or control within the Internet. Domain names are often used to identify services provided through the Internet, such as websites, email services and more. ...
is—in most cases—hosted by the criminal actor.
Depending on the configuration and complexity of the infrastructure, fast-fluxing is generally classified into single, double, and domain fast-flux networks. Fast-fluxing remains an intricate problem in network security
Network security consists of the policies, processes and practices adopted to prevent, detect and monitor unauthorized access, misuse, modification, or denial of a computer network and network-accessible resources. Network security involves th ...
and current countermeasures remain ineffective.
History
Fast-fluxing was first reported by the security researchers William Salusky and Robert Danford of The Honeynet Project in 2007; the following year, they released a systematic study of fast-flux service networks in 2008. Rock Phish (2004) and Storm Worm (2007) were two notable fast-flux service networks which were used for malware distribution and phishing.Fast-flux service network
A fast-flux service network (FFSN) is a network infrastructure resultant of the fast-fluxed network of compromised hosts; the technique is also used by legitimate service providers such as content distribution networks (CDNs) where the dynamic IP address is converted to match the domain name of theinternet host
A network host is a computer or other device connected to a computer network. A host may work as a server offering information resources, services, and applications to users or other hosts on the network. Hosts are assigned at least one networ ...
, usually for the purpose of load balancing using round-robin domain name system (RR-DNS). The purpose of using FFSN infrastructure for the botnets is to relay network requests and act as a proxy to the backend bulletproof
Bulletproofing is the process of making an object capable of stopping a bullet or similar high velocity projectiles (e.g. shrapnel). The term bullet resistance is often preferred because few, if any, practical materials provide complete protectio ...
content server which function as an "origin server
In computer networking, upstream server refers to a server that provides service to another server. In other words, upstream server is a server that is located higher in a hierarchy of servers. The highest server in the hierarchy is sometimes ca ...
".
The frontend bots, which act as an ephemeral host affixed to a control master, are called flux-agents whose network availability is indeterminate due to the dynamic nature of fast-fluxing. The backend motherships do not establish direct communication with the user agent
In computing, a user agent is any software, acting on behalf of a user, which "retrieves, renders and facilitates end-user interaction with Web content". A user agent is therefore a special kind of software agent.
Some prominent examples of u ...
s, rather every actions are reverse proxied through compromised frontend nodes, effectively making the attack long-lasting and resilient against take down attempts.
Types
 Fast-fluxing is generally classified into two types: single fluxing and double fluxing, a build-on implementation over single fluxing. The phraseologies involved in fast-fluxing includes "flux-herder mothership nodes" and "fast-flux agent nodes", referred to the backend
Fast-fluxing is generally classified into two types: single fluxing and double fluxing, a build-on implementation over single fluxing. The phraseologies involved in fast-fluxing includes "flux-herder mothership nodes" and "fast-flux agent nodes", referred to the backend bulletproof
Bulletproofing is the process of making an object capable of stopping a bullet or similar high velocity projectiles (e.g. shrapnel). The term bullet resistance is often preferred because few, if any, practical materials provide complete protectio ...
botnet controller and the compromised host nodes involved in reverse proxying the traffic back-and-forth between the origin
Origin(s) or The Origin may refer to:
Arts, entertainment, and media
Comics and manga
* ''Origin'' (comics), a Wolverine comic book mini-series published by Marvel Comics in 2002
* ''The Origin'' (Buffy comic), a 1999 ''Buffy the Vampire Sl ...
and clients respectively. The compromised hosts used by the fast-flux herders typically includes residential broadband access circuits, such as DSL and cable modems.
Single-flux network
In single-flux network, theauthoritative name server
A name server refers to the server component of the Domain Name System (DNS), one of the two principal namespaces of the Internet. The most important function of DNS servers is the translation (resolution) of human-memorable domain names (example. ...
of a fast-fluxing domain name repeatedly permutes the DNS resource records with low time to live
Time to live (TTL) or hop limit is a mechanism which limits the lifespan or lifetime of data in a computer or network. TTL may be implemented as a counter or timestamp attached to or embedded in the data. Once the prescribed event count or times ...
(TTL) values, conventionally between 180 and 600 seconds. The permuted record within the zone file
A Domain Name System (DNS) zone file is a text file that describes a DNS zone. A DNS zone is a subset, often a single domain, of the hierarchical domain name structure of the DNS. The zone file contains mappings between domain names and IP ...
includes A, AAAA and CNAME record, the disposition is usually done by means of round robin from a registry of exploited host's IP addresses and DDNS names. Although HTTP
The Hypertext Transfer Protocol (HTTP) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web, ...
and DNS
The Domain Name System (DNS) is a hierarchical and distributed naming system for computers, services, and other resources in the Internet or other Internet Protocol (IP) networks. It associates various information with domain names assigned to ...
remain commonly proxied application protocols by the frontend flux-agents, protocols such as SMTP
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typic ...
, IMAP
In computing, the Internet Message Access Protocol (IMAP) is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. IMAP is defined by .
IMAP was designed with the goal of pe ...
and POP
Pop or POP may refer to:
Arts, entertainment, and media Music
* Pop music, a musical genre Artists
* POP, a Japanese idol group now known as Gang Parade
* Pop!, a UK pop group
* Pop! featuring Angie Hart, an Australian band
Albums
* ''Pop'' (G ...
can also be delivered through transport layer
In computer networking, the transport layer is a conceptual division of methods in the layered architecture of protocols in the network stack in the Internet protocol suite and the OSI model. The protocols of this layer provide end-to-end ...
(L4) TCP and UDP level port binding techniques between flux-agents and backend flux-herder nodes.
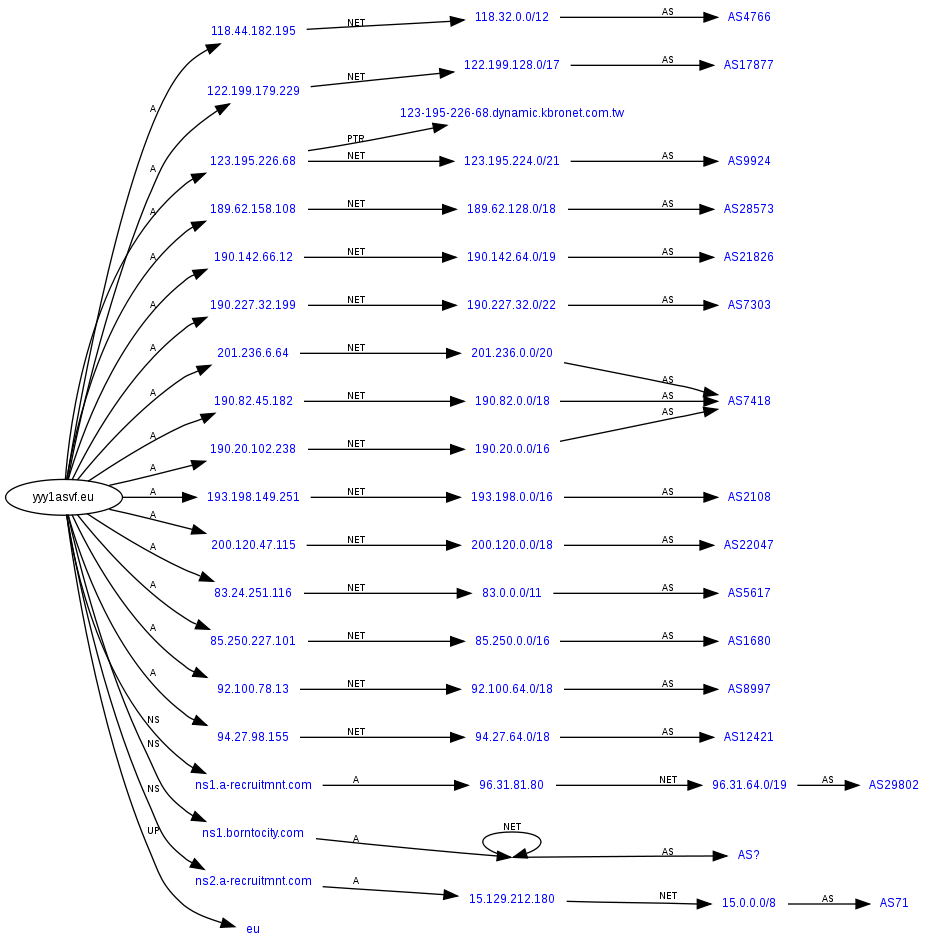
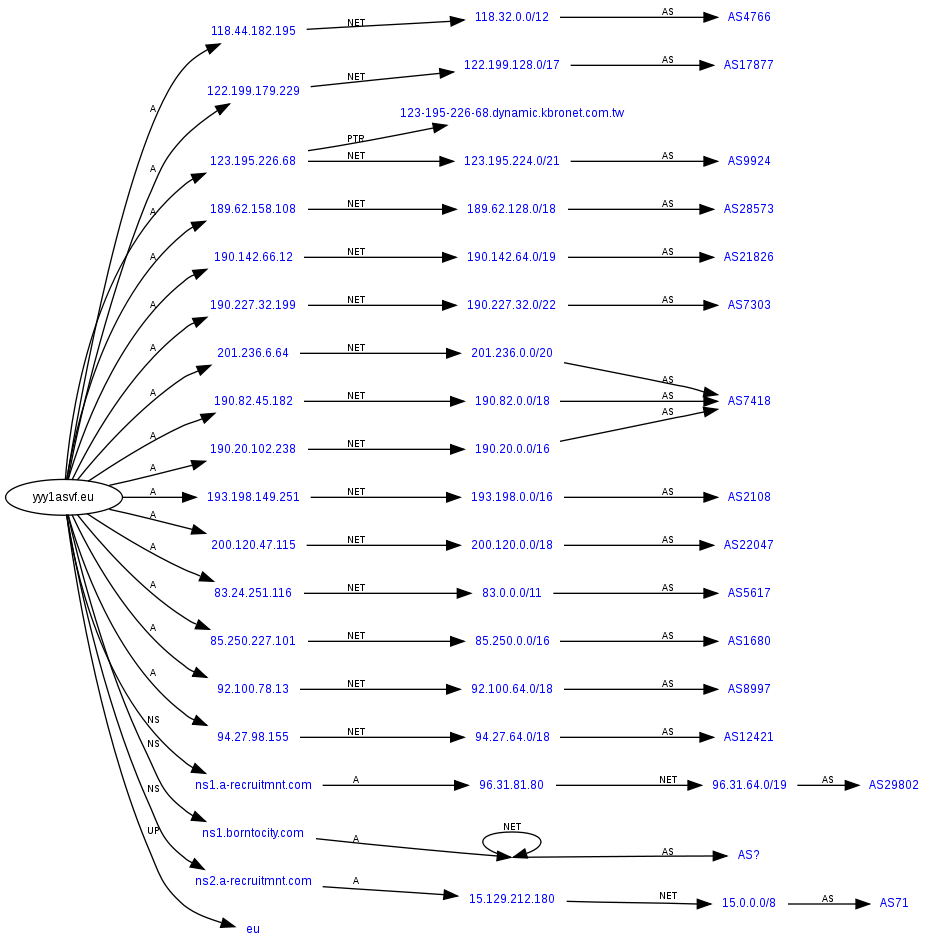
Double-flux network
Double-fluxing networks involve high-frequency permutation of the fluxing domain's authoritative name servers, along with DNS resource records such as A, AAAA, or CNAME pointing to frontend proxies. In this infrastructure, the authoritative name server of the fluxing domain points to a frontend redirector node, which forwards the DNS datagram to a backend mothership node that resolve the query. The DNS resource records, including the NS record, are set with a lower TTL value, therefore resulting in an additional level indirection. The NS records in a double-fluxing network usually point to a referrer host that listens onport 53
The Domain Name System (DNS) is a hierarchical and distributed naming system for computers, services, and other resources in the Internet or other Internet Protocol (IP) networks. It associates various information with domain names assigned ...
, which forwards the query to a backend DNS resolver that is authoritative for the fluxing domain. Advanced level of resilience and redundancy is achieved through blind proxy redirection techniques of the frontend nodes; Fast-fluxing domains also abuse domain wildcarding specification for spam delivery and phishing, and use DNS covert channels for transferring application layer payloads of protocols such as HTTP, SFTP, and FTP encapsulated within a DNS datagram query.
Domain-flux network
Domain-flux network involves keeping a fast-fluxing network operational through continuously rotating the domain name of the flux-herder mothership nodes. The domain names are dynamically generated using a selectedpseudorandom
A pseudorandom sequence of numbers is one that appears to be statistically random, despite having been produced by a completely deterministic and repeatable process.
Background
The generation of random numbers has many uses, such as for random ...
domain generation algorithm (DGA), and the flux operator mass-registers the domain names. An infected host repeatedly tries to initiate a flux-agent handshake by spontaneous generating, resolving and connecting to an IP address until an acknowledgment, to register itself to the flux-herder mothership node. A notable example includes Conficker
Conficker, also known as Downup, Downadup and Kido, is a computer worm targeting the Microsoft Windows operating system that was first detected in November 2008. It uses flaws in Windows OS software and dictionary attacks on administrator pas ...
, a botnet which was operational by generating 50,000 different domains in 110 top-level domains
A top-level domain (TLD) is one of the domains at the highest level in the hierarchical Domain Name System of the Internet after the root domain. The top-level domain names are installed in the root zone of the name space. For all domains in ...
(TLDs).
Security countermeasures
The detection and mitigation of fast-fluxing domain names remain an intricate challenge in network security due to the robust nature of fast-fluxing. Althoughfingerprinting
A fingerprint is an impression left by the friction ridges of a human finger. The recovery of partial fingerprints from a crime scene is an important method of forensic science. Moisture and grease on a finger result in fingerprints on surfac ...
the backend fast-flux mothership node remains increasingly difficult, service providers could detect the upstream mothership nodes through probing the frontend flux-agents in a special way by sending a crafted HTTP request that would trigger an out-of-band network request from the backend fast-flux mothership node to the client in an independent channel, such that the client could deduce the mothership node's IP address by analyzing the logs of its network traffic. Various security researchers suggests that the effective measure against fast-fluxing is to take down the domain name from its use. However, the domain name registrar
A domain name registrar is a company that manages the reservation of Internet domain names. A domain name registrar must be accredited by a generic top-level domain (gTLD) registry or a country code top-level domain (ccTLD) registry. A registr ...
s are reluctant in doing so, since there aren't jurisdiction independent terms of service agreements that must be observed; in most cases, fast-flux operators and cybersquatters are the main source of income to those registrars.
Other countermeasures against fast-fluxing domains include deep packet inspection
Deep packet inspection (DPI) is a type of data processing that inspects in detail the data being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep packet inspection is oft ...
(DPI), host-based firewall
In computing, a firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. A firewall typically establishes a barrier between a trusted network and an untrusted ...
, and IP-based access control lists
In computer security, an access-control list (ACL) is a list of permissions associated with a system resource (object). An ACL specifies which users or system processes are granted access to objects, as well as what operations are allowed on gi ...
(ACLs), although there are serious limitations in these approaches due to the dynamic nature of fast-fluxing.
See also
* Avalanche (phishing group)References
Bibliography
* * * * * * * {{DEFAULTSORT:Fast Flux Domain Name System Botnets