|
Twirl Whisk
In cryptography and number theory, TWIRL (The Weizmann Institute Relation Locator) is a hypothetical hardware device designed to speed up the sieving step of the general number field sieve integer factorization algorithm. During the sieving step, the algorithm searches for numbers with a certain mathematical relationship. In distributed factoring projects, this is the step that is parallelized to a large number of processors. TWIRL is still a hypothetical device — no implementation has been publicly reported. However, its designers, Adi Shamir and Eran Tromer, estimate that if TWIRL were built, it would be able to factor 1024-bit numbers in one year at the cost of "a few dozen million US dollars". TWIRL could therefore have enormous repercussions in cryptography and computer security — many high-security systems still use 1024-bit RSA keys, which TWIRL would be able to break in a reasonable amount of time and for reasonable costs. The security of some important cryptograph ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security (data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synony ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Number Theory
Number theory (or arithmetic or higher arithmetic in older usage) is a branch of pure mathematics devoted primarily to the study of the integers and integer-valued functions. German mathematician Carl Friedrich Gauss (1777–1855) said, "Mathematics is the queen of the sciences—and number theory is the queen of mathematics."German original: "Die Mathematik ist die Königin der Wissenschaften, und die Arithmetik ist die Königin der Mathematik." Number theorists study prime numbers as well as the properties of mathematical objects made out of integers (for example, rational numbers) or defined as generalizations of the integers (for example, algebraic integers). Integers can be considered either in themselves or as solutions to equations ( Diophantine geometry). Questions in number theory are often best understood through the study of analytical objects (for example, the Riemann zeta function) that encode properties of the integers, primes or other number-theoretic object ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Weizmann Institute
The Weizmann Institute of Science ( he, מכון ויצמן למדע ''Machon Vaitzman LeMada'') is a public research university in Rehovot, Israel, established in 1934, 14 years before the State of Israel. It differs from other Israeli universities in that it offers only postgraduate degrees in the natural and exact sciences. It is a multidisciplinary research center, with around 3,800 scientists, postdoctoral fellows, Ph.D. and M.Sc. students, and scientific, technical, and administrative staff working at the institute. As of 2019, six Nobel laureates and three Turing Award winners have been associated with the Weizmann Institute of Science. History Founded in 1934 by Chaim Weizmann and his first team, among them Benjamin M. Bloch, as the Daniel Sieff Research Institute. Weizmann had offered the post of director to Nobel Prize laureate Fritz Haber, but took over the directorship himself after Haber's death en route to Palestine. Before he became President of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
General Number Field Sieve
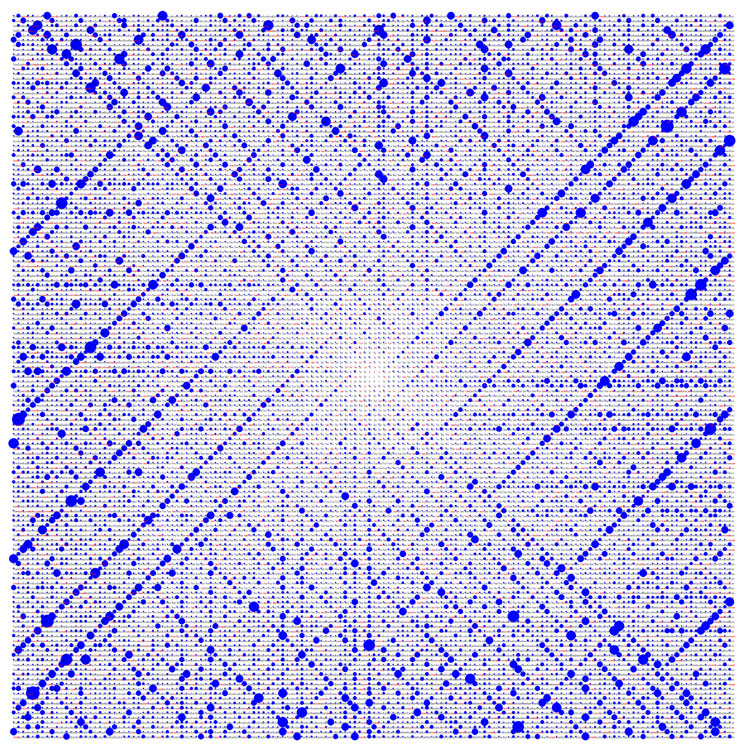
In number theory, the general number field sieve (GNFS) is the most efficient classical algorithm known for factoring integers larger than . Heuristically, its complexity for factoring an integer (consisting of bits) is of the form :\exp\left( \left(\sqrt + o(1)\right)(\ln n)^(\ln \ln n)^\right) =L_n\left frac,\sqrt[3right/math> (in L-notation">">frac,\sqrt[3<_a>right.html" ;"title=".html" ;"title="frac,\sqrt[3">frac,\sqrt[3right">.html" ;"title="frac,\sqrt[3">frac,\sqrt[3right/math> (in L-notation), where is the natural logarithm. It is a generalization of the special number field sieve: while the latter can only factor numbers of a certain special form, the general number field sieve can factor any number apart from prime powers (which are trivial to factor by taking roots). The principle of the number field sieve (both special and general) can be understood as an improvement to the simpler rational sieve or quadratic sieve. When using such algorithms ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Integer Factorization
In number theory, integer factorization is the decomposition of a composite number into a product of smaller integers. If these factors are further restricted to prime numbers, the process is called prime factorization. When the numbers are sufficiently large, no efficient non-quantum integer factorization algorithm is known. However, it has not been proven that such an algorithm does not exist. The presumed difficulty of this problem is important for the algorithms used in cryptography such as RSA public-key encryption and the RSA digital signature. Many areas of mathematics and computer science have been brought to bear on the problem, including elliptic curves, algebraic number theory, and quantum computing. In 2019, Fabrice Boudot, Pierrick Gaudry, Aurore Guillevic, Nadia Heninger, Emmanuel Thomé and Paul Zimmermann factored a 240-digit (795-bit) number ( RSA-240) utilizing approximately 900 core-years of computing power. The researchers estimated that a 1024- ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Adi Shamir
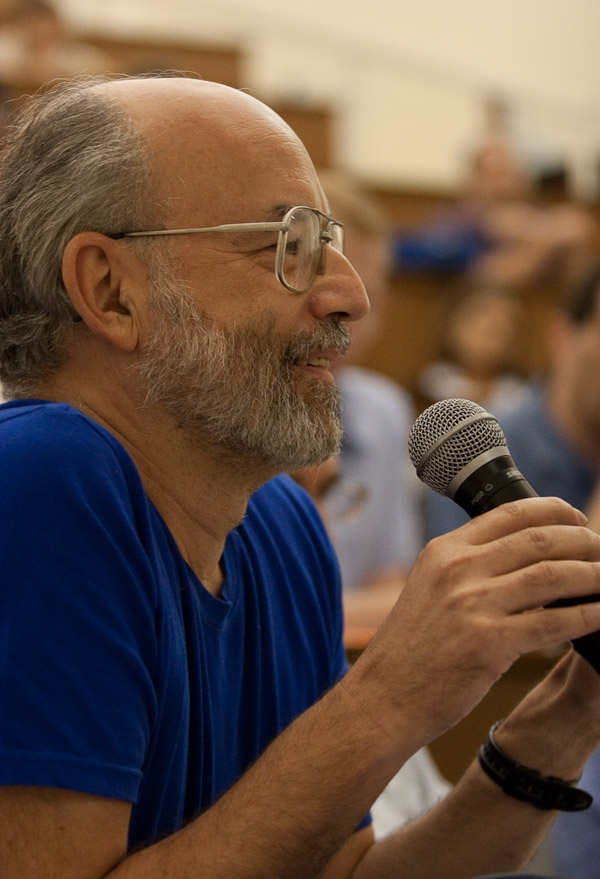
Adi Shamir ( he, עדי שמיר; born July 6, 1952) is an Israeli cryptographer. He is a co-inventor of the Rivest–Shamir–Adleman (RSA) algorithm (along with Ron Rivest and Len Adleman), a co-inventor of the Feige–Fiat–Shamir identification scheme (along with Uriel Feige and Amos Fiat), one of the inventors of differential cryptanalysis and has made numerous contributions to the fields of cryptography and computer science. Education Born in Tel Aviv, Shamir received a Bachelor of Science (BSc) degree in mathematics from Tel Aviv University in 1973 and obtained his Master of Science (MSc) and Doctor of Philosophy (PhD) degrees in Computer Science from the Weizmann Institute in 1975 and 1977 respectively. Career and research After a year as a postdoctoral researcher at the University of Warwick, he did research at Massachusetts Institute of Technology (MIT) from 1977 to 1980 before returning to be a member of the faculty of Mathematics and Computer Science at the Weiz ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Eran Tromer
Eran is an ancient town and archaeological site in the Sagar district of Madhya Pradesh, India. It was one of the ancient mints for Indian dynasties as evidenced by the diverse coins excavated here. The site has 5th and 6th-century Gupta era temples and monuments, particularly the colossal stone boar with sages and scholars depicted on the body of the sculpture. The inscription stones found at Eran are important to reconstructing the chronology of Gupta Empire history. Eran or Erakina was the capital of ''Erakina (Airikina) Pradesha'' or ''Airkina Vishaya'', an administrative division of the Gupta empire. Etymology The ancient name of Eran ( sa, ऐरण), ''Erakaina'', ''Erakanya'' or ''Erakina'' (as mentioned in the inscriptions); ''Airikina'' ( sa, ऐरिकिण, as mentioned in the inscription of Samudragupta) or ''Erikina'' (as mentioned in the inscription of Toramana) is derived from ''Eraka''. The word ''erakā'' probably refers to a tall grass commonly called the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
US Dollar
The United States dollar (symbol: $; code: USD; also abbreviated US$ or U.S. Dollar, to distinguish it from other dollar-denominated currencies; referred to as the dollar, U.S. dollar, American dollar, or colloquially buck) is the official currency of the United States and several other countries. The Coinage Act of 1792 introduced the U.S. dollar at par with the Spanish silver dollar, divided it into 100 cents, and authorized the minting of coins denominated in dollars and cents. U.S. banknotes are issued in the form of Federal Reserve Notes, popularly called greenbacks due to their predominantly green color. The monetary policy of the United States is conducted by the Federal Reserve System, which acts as the nation's central bank. The U.S. dollar was originally defined under a bimetallic standard of (0.7735 troy ounces) fine silver or, from 1837, fine gold, or $20.67 per troy ounce. The Gold Standard Act of 1900 linked the dollar solely to gold. From 1934, its ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Security
Computer security, cybersecurity (cyber security), or information technology security (IT security) is the protection of computer systems and networks from attack by malicious actors that may result in unauthorized information disclosure, theft of, or damage to hardware, software, or data, as well as from the disruption or misdirection of the services they provide. The field has become of significance due to the expanded reliance on computer systems, the Internet, and wireless network standards such as Bluetooth and Wi-Fi, and due to the growth of smart devices, including smartphones, televisions, and the various devices that constitute the Internet of things (IoT). Cybersecurity is one of the most significant challenges of the contemporary world, due to both the complexity of information systems and the societies they support. Security is of especially high importance for systems that govern large-scale systems with far-reaching physical effects, such as power distribu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
RSA (algorithm)
RSA (Rivest–Shamir–Adleman) is a public-key cryptosystem that is widely used for secure data transmission. It is also one of the oldest. The acronym "RSA" comes from the surnames of Ron Rivest, Adi Shamir and Leonard Adleman, who publicly described the algorithm in 1977. An equivalent system was developed secretly in 1973 at Government Communications Headquarters (GCHQ) (the British signals intelligence agency) by the English mathematician Clifford Cocks. That system was declassified in 1997. In a public-key cryptosystem, the encryption key is public and distinct from the decryption key, which is kept secret (private). An RSA user creates and publishes a public key based on two large prime numbers, along with an auxiliary value. The prime numbers are kept secret. Messages can be encrypted by anyone, via the public key, but can only be decoded by someone who knows the prime numbers. The security of RSA relies on the practical difficulty of factoring the produ ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Blum Blum Shub
Blum Blum Shub (B.B.S.) is a pseudorandom number generator proposed in 1986 by Lenore Blum, Manuel Blum and Michael Shub that is derived from Michael O. Rabin's one-way function. __TOC__ Blum Blum Shub takes the form :x_ = x_n^2 \bmod M, where ''M'' = ''pq'' is the product of two large primes ''p'' and ''q''. At each step of the algorithm, some output is derived from ''x''''n''+1; the output is commonly either the bit parity of ''x''''n''+1 or one or more of the least significant bits of ''x''''n''+1''. The seed ''x''0 should be an integer that is co-prime to ''M'' (i.e. ''p'' and ''q'' are not factors of ''x''0) and not 1 or 0. The two primes, ''p'' and ''q'', should both be congruent to 3 (mod 4) (this guarantees that each quadratic residue has one square root which is also a quadratic residue), and should be safe primes with a small gcd((''p-3'')''/2'', (''q-3'')''/2'') (this makes the cycle length large). An interesting characteristic of the Blum Blum Shub generator is ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Pseudorandom Number Generator
A pseudorandom number generator (PRNG), also known as a deterministic random bit generator (DRBG), is an algorithm for generating a sequence of numbers whose properties approximate the properties of sequences of random numbers. The PRNG-generated sequence is not truly random, because it is completely determined by an initial value, called the PRNG's ''seed'' (which may include truly random values). Although sequences that are closer to truly random can be generated using hardware random number generators, ''pseudorandom number generators'' are important in practice for their speed in number generation and their reproducibility. PRNGs are central in applications such as simulations (e.g. for the Monte Carlo method), electronic games (e.g. for procedural generation), and cryptography. Cryptographic applications require the output not to be predictable from earlier outputs, and more elaborate algorithms, which do not inherit the linearity of simpler PRNGs, are needed. Good statis ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |