|
Stockade (software)
Stockade is a TCP-layer blocking tool written in C++. It denies TCP/IP access to registered IP addresses by using the ipfw packet filter. It targets spam prevention, but may also be used against other attackers (e.g. brute force password crackers.) The rate limiting approach This approach leverages the superior determination exhibited by legitimate senders. In this respect, it may be considered similar to greylisting. Originally, the authors conceived an ''MT Proxy'' to rate-limit the SMTP connections of messages believed to be spam. That worked by adding a ''dummynet'' rule for frequent senders who had been sending messages that triggered an unreliable statistical analysis. A key limitation of the original scheme was the consumption of local resources (in the SMTP proxy). Stockade approach introduces the notion that an inbound TCP connection may be rejected with some random probability proportional to the level of spam already seen from the connection’s originator over some ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Swinburne University Of Technology
The Swinburne University of Technology (or simply Swinburne) is a public university, public research university in Melbourne, Australia. It is the modern descendant of the Eastern Suburbs Technical College established in 1908, renamed Swinburne Technical College in 1913 after its co-founders George Swinburne, George and Ethel Swinburne. It has three campuses in metropolitan Melbourne: Hawthorn, Victoria, Hawthorn, where its main campus is located; Wantirna, Victoria, Wantirna; and Croydon, Victoria, Croydon, as well the Swinburne University of Technology Sarawak Campus in the East Malaysian state of Sarawak. It also offers courses online and through its partnered institutions in Australia and overseas. The university offers study programs in Bachelor of Commerce, commerce, Health care, healthcare, teacher education, Jurisprudence, law, engineering, Flight training, aviation, architecture, the performing arts and various other fields including in the arts and sciences. It also of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
FreeBSD
FreeBSD is a free-software Unix-like operating system descended from the Berkeley Software Distribution (BSD). The first version was released in 1993 developed from 386BSD, one of the first fully functional and free Unix clones on affordable home-class hardware, and has since continuously been the most commonly used BSD-derived operating system. FreeBSD maintains a complete system, delivering a kernel, device drivers, userland utilities, and documentation, as opposed to Linux only delivering a kernel and drivers, and relying on third-parties such as GNU for system software. The FreeBSD source code is generally released under a permissive BSD license, as opposed to the copyleft GPL used by Linux. The project includes a security team overseeing all software shipped in the base distribution. Third-party applications may be installed using the pkg package management system or from source via FreeBSD Ports. The project is supported and promoted by the FreeBSD Foundation ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
GNU General Public License
The GNU General Public Licenses (GNU GPL or simply GPL) are a series of widely used free software licenses, or ''copyleft'' licenses, that guarantee end users the freedom to run, study, share, or modify the software. The GPL was the first copyleft license available for general use. It was originally written by Richard Stallman, the founder of the Free Software Foundation (FSF), for the GNU Project. The license grants the recipients of a computer program the rights of the Free Software Definition. The licenses in the GPL series are all copyleft licenses, which means that any derivative work must be distributed under the same or equivalent license terms. The GPL is more restrictive than the GNU Lesser General Public License, and even more distinct from the more widely used permissive software licenses such as BSD, MIT, and Apache. Historically, the GPL license family has been one of the most popular software licenses in the free and open-source software (FOSS) domai ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
IP Address
An Internet Protocol address (IP address) is a numerical label such as that is assigned to a device connected to a computer network that uses the Internet Protocol for communication. IP addresses serve two main functions: network interface identification, and location addressing. Internet Protocol version 4 (IPv4) was the first standalone specification for the IP address, and has been in use since 1983. IPv4 addresses are defined as a 32-bit number, which became too small to provide enough addresses as the internet grew, leading to IPv4 address exhaustion over the 2010s. Its designated successor, IPv6, uses 128 bits for the IP address, giving it a larger address space. Although IPv6 deployment has been ongoing since the mid-2000s, both IPv4 and IPv6 are still used side-by-side . IP addresses are usually displayed in a human-readable notation, but systems may use them in various different computer number formats. CIDR notation can also be used to designate how much ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Ipfirewall
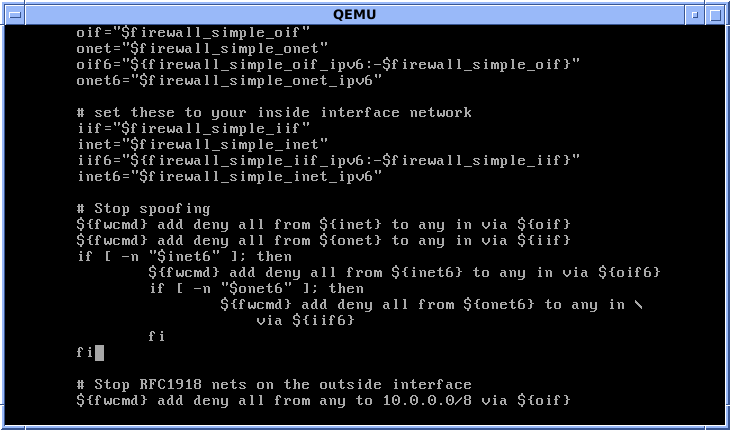
ipfirewall or ipfw is a FreeBSD IP, stateful firewall, packet filter and traffic accounting facility. Its ruleset logic is similar to many other packet filters except IPFilter. ipfw is authored and maintained by FreeBSD volunteer staff members. Its syntax enables use of sophisticated filtering capabilities and thus enables users to satisfy advanced requirements. It can either be used as a loadable kernel module or incorporated into the kernel; use as a loadable kernel module where possible is highly recommended. ipfw was the built-in firewall of Mac OS X until Mac OS X 10.7 Lion in 2011 when it was replaced with the OpenBSD project's PF. Like FreeBSD, ipfw is open source. It is used in many FreeBSD-based firewall products, including m0n0wall and FreeNAS. A port of an early version of ipfw was used since Linux 1.1 as the first implementation of firewall available for Linux, until it was replaced by ipchains. A modern port of ipfw and the ''dummynet'' traffic shaper is av ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Password Cracking
In cryptanalysis and computer security, password cracking is the process of guessing passwords protecting a computer system. A common approach (brute-force attack) is to repeatedly try guesses for the password and to check them against an available cryptographic hash of the password. Another type of approach is password spraying, which is often automated and occurs slowly over time in order to remain undetected, using a list of common passwords. The purpose of password cracking might be to help a user recover a forgotten password (due to the fact that installing an entirely new password would involve System Administration privileges), to gain unauthorized access to a system, or to act as a preventive measure whereby system administrators check for easily crackable passwords. On a file-by-file basis, password cracking is utilized to gain access to digital evidence to which a judge has allowed access, when a particular file's permissions restricted. Time needed for password searche ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Greylisting (email)
Greylisting is a method of defending e-mail users against spam. A mail transfer agent (MTA) using greylisting will "temporarily reject" any email from a sender it does not recognize. If the mail is legitimate, the originating server will try again after a delay, and if sufficient time has elapsed, the email will be accepted. Mechanism A server employing greylisting temporarily rejects email from unknown or suspicious sources by sending 4xx reply codes ("please call back later") as defined in the Simple Mail Transfer Protocol (SMTP). Fully capable SMTP implementations are expected to maintain queues for retrying message transmissions in such cases, and so while legitimate mail may be delayed, it should still get through. Temporary rejection can be issued at different stages of the SMTP dialogue, allowing for an implementation to store more or less data about the incoming message. The trade-off is more work and bandwidth for more exact matching of retries with original messages. Reje ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Simple Mail Transfer Protocol
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typically use SMTP only for sending messages to a mail server for relaying, and typically submit outgoing email to the mail server on port 465 or 587 per . For retrieving messages, IMAP (which replaced the older POP3) is standard, but proprietary servers also often implement proprietary protocols, e.g., Exchange ActiveSync. SMTP's origins began in 1980, building on concepts implemented on the ARPANET since 1971. It has been updated, modified and extended multiple times. The protocol version in common use today has extensible structure with various extensions for authentication, encryption, binary data transfer, and internationalized email addresses. SMTP servers commonly use the Transmission Control Protocol on port number 25 (between se ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Fail2ban
Fail2Ban is an intrusion prevention system, intrusion prevention software framework. Written in the Python (programming language), Python programming language, it is designed to prevent brute-force attacks. It is able to run on POSIX systems that have an interface to a packet-control system or firewall installed locally, such as iptables or TCP Wrapper. Functionality Fail2ban operates by monitoring Computer data logging, log files (e.g. , , etc.) for selected entries and running scripts based on them. Most commonly this is used to block selected IP addresses that may belong to Host (network), hosts that are trying to breach the system's security. It can ban any host IP address that makes too many login attempts or performs any other unwanted action within a time frame defined by the administrator. It includes support for both IPv4 and IPv6. Optionally longer bans can be custom-configured for "recidivist" abusers that keep coming back. Fail2Ban is typically set up to unban a block ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
DenyHosts
DenyHosts is a log-based intrusion-prevention security tool for SSH servers written in Python. It is intended to prevent brute-force attacks on SSH servers by monitoring invalid login attempts in the authentication log and blocking the originating IP addresses. DenyHosts is developed by Phil Schwartz, who is also the developer of Kodos Python Regular Expression Debugger. Operation DenyHosts checks the end of the authentication log for recent failed login attempts. It records information about their originating IP addresses and compares the number of invalid attempts to a user-specified threshold. If there have been too many invalid attempts it assumes a dictionary attack is occurring and prevents the IP address from making any further attempts by adding it to /etc/hosts.deny on the server. DenyHosts 2.0 and above support centralized synchronization, so that repeat offenders are blocked from many computers. The sitdenyhosts.netgathers statistics from computers running the software. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Secure Shell
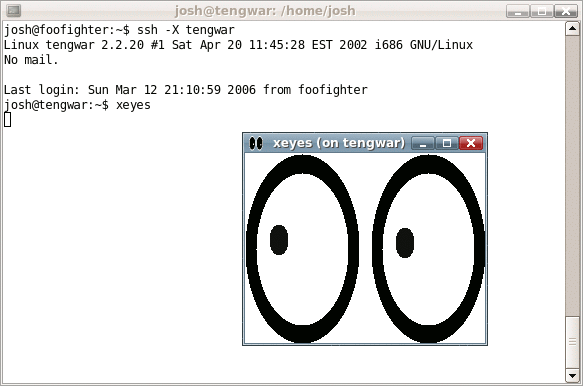
The Secure Shell Protocol (SSH Protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. Its most notable applications are remote login and command-line execution. SSH was designed for Unix-like operating systems as a replacement for Telnet and unsecured remote Unix shell protocols, such as the Berkeley Remote Shell (rsh) and the related rlogin and rexec protocols, which all use insecure, plaintext methods of authentication, like passwords. Since mechanisms like Telnet and Remote Shell are designed to access and operate remote computers, sending the authentication tokens (e.g. username and password) for this access to these computers across a public network in an unsecured way poses a great risk of 3rd parties obtaining the password and achieving the same level of access to the remote system as the telnet user. Secure Shell mitigates this risk through the use of encryption mechanisms that are intended to hide th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Computer Security Software
Computer security software or cybersecurity software is any computer program designed to influence information security. This is often taken in the context of defending computer systems or data, yet can incorporate programs designed specifically for subverting computer systems due to their significant overlap, and the adage that the best defense is a good offense. The defense of computers against intrusion and unauthorized use of resources is called ''computer security''. Similarly, the defense of computer networks is called '' network security''. The subversion of computers or their unauthorized use is referred to using the terms ''cyberwarfare'', ''cybercrime'', or '' security hacking'' (later shortened to ''hacking'' for further references in this article due to issues with ''hacker'', ''hacker culture'' and differences in white/grey/black 'hat' color identification). The computer security software products industry was launched in the second half of the 1970s when computer f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |