|
NIST SP 800-90A
NIST SP 800-90A ("SP" stands for "''special publication''") is a publication by the National Institute of Standards and Technology with the title ''Recommendation for Random Number Generation Using Deterministic Random Bit Generators''. The publication contains the specification for three allegedly cryptographically secure pseudorandom number generators for use in cryptography: Hash DRBG (based on hash functions), HMAC DRBG (based on HMAC), and CTR DRBG (based on block ciphers in counter mode). Since June 24, 2015, the current version of the publication is Revision 1. Earlier versions included a fourth generator, Dual_EC_DRBG (based on elliptic curve cryptography). Dual_EC_DRBG was later reported to probably contain a kleptographic backdoor inserted by the United States National Security Agency (NSA), while the other three random number generators are accepted as uncontroversial and secure by multiple cryptographers. As a work of the US Federal Government, NIST SP 800-90A is i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Institute Of Standards And Technology
The National Institute of Standards and Technology (NIST) is an agency of the United States Department of Commerce whose mission is to promote American innovation and industrial competitiveness. NIST's activities are organized into physical science laboratory programs that include nanoscale science and technology, engineering, information technology, neutron research, material measurement, and physical measurement. From 1901 to 1988, the agency was named the National Bureau of Standards. History Background The Articles of Confederation, ratified by the colonies in 1781, provided: The United States in Congress assembled shall also have the sole and exclusive right and power of regulating the alloy and value of coin struck by their own authority, or by that of the respective states—fixing the standards of weights and measures throughout the United States. Article 1, section 8, of the Constitution of the United States, ratified in 1789, granted these powers to the new ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bullrun (decryption Program)
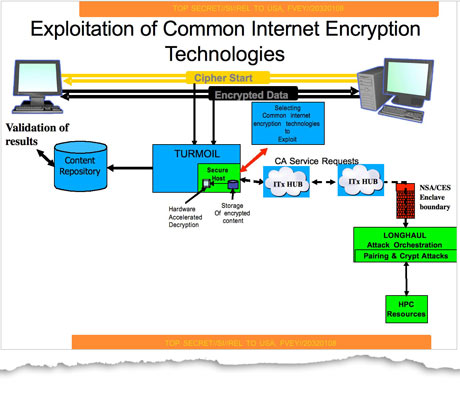
Bullrun (stylized BULLRUN) is a clandestine, highly classified program to crack encryption of online communications and data, which is run by the United States National Security Agency (NSA). The British Government Communications Headquarters (GCHQ) has a similar program codenamed Edgehill. According to the Bullrun classification guide published by ''The Guardian'', the program uses multiple methods including computer network exploitation, interdiction, industry relationships, collaboration with other intelligence community entities, and advanced mathematical techniques. Information about the program's existence was leaked in 2013 by Edward Snowden. Although Snowden's documents do not contain technical information on exact cryptanalytic capabilities because Snowden did not have clearance access to such information, they do contain a 2010 GCHQ presentation which claims that "vast amounts of encrypted Internet data which have up till now been discarded are now exploitable". A n ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographically Secure Pseudorandom Number Generators
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security ( data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymous wit ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Broken Cryptography Algorithms
Broken may refer to: Literature * ''Broken'' (Armstrong novel), a 2006 novel by Kelley Armstrong in the ''Women of the Otherworld'' series * ''Broken'' (Slaughter novel), a 2010 novel by Karin Slaughter Music Albums * '' Broken (And Other Rogue States)'', a 2005 album by Luke Doucet * ''Broken'' (MBLAQ EP) (2014) * ''Broken'' (Nine Inch Nails EP), (1992) * ''Broken'' (Soulsavers album) (2009) * ''Broken'' (Straight Faced album) (1996) Songs * "Broken" (Jake Bugg song) (2013) * "Broken" (Sam Clark song) (2009) * "Broken" (Coldplay song) (2019) * "Broken" (Elisa song) (2003) * "Broken" (Lifehouse song) (2008) * "Broken" (lovelytheband song) (2017) * "Broken" (Kate Ryan song) (2011) * "Broken" (Seether song) (2004) * "Broken" (Slander and Kompany song) (2019) * "Broken", by 12 Stones from ''12 Stones'' * "Broken", by All That Remains from ''Victim of the New Disease'' * "Broken", by David Archuleta from '' Begin'' * "Broken", by Bad Religion from ''The Proc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
NIST SP 800-90C
The National Institute of Standards and Technology (NIST) is an agency of the United States Department of Commerce whose mission is to promote American innovation and industrial competitiveness. NIST's activities are organized into physical science laboratory programs that include nanoscale science and technology, engineering, information technology, neutron research, material measurement, and physical measurement. From 1901 to 1988, the agency was named the National Bureau of Standards. History Background The Articles of Confederation, ratified by the colonies in 1781, provided: The United States in Congress assembled shall also have the sole and exclusive right and power of regulating the alloy and value of coin struck by their own authority, or by that of the respective states—fixing the standards of weights and measures throughout the United States. Article 1, section 8, of the Constitution of the United States, ratified in 1789, granted these powers to the new Congre ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
NIST SP 800-90B
NIST SP 800-90B ("SP" stands for "''special publication''") is a publication by the National Institute of Standards and Technology with the title ''Recommendation for the Entropy Sources Used for Random Bit Generation''. The publication specifies the design principles and requirements for the entropy sources used by random-bit generators, and the tests for the validation of entropy sources. These entropy sources are intended to be combined with deterministic random-bit generator mechanisms that are specified in NIST SP 800-90A to construct random-bit generators, as specified in NIST SP 800-90C. As a work of the US Federal Government, NIST SP 800-90B is in the public domain The public domain (PD) consists of all the creative work to which no exclusive intellectual property rights apply. Those rights may have expired, been forfeited, expressly waived, or may be inapplicable. Because those rights have expired ... and freely available. NIST SP 800-90B version history Re ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Triple DES
In cryptography, Triple DES (3DES or TDES), officially the Triple Data Encryption Algorithm (TDEA or Triple DEA), is a symmetric-key block cipher, which applies the DES cipher algorithm three times to each data block. The Data Encryption Standard's (DES) 56-bit key is no longer considered adequate in the face of modern cryptanalytic techniques and supercomputing power. A CVE released in 2016, CVE-2016-2183' disclosed a major security vulnerability in DES and 3DES encryption algorithms. This CVE, combined with the inadequate key size of DES and 3DES, NIST has deprecated DES and 3DES for ''new'' applications in 2017, and for ''all'' applications by the end of 2023. It has been replaced with the more secure, more robust AES. While the government and industry standards abbreviate the algorithm's name as TDES (Triple DES) and TDEA (Triple Data Encryption Algorithm), RFC 1851 referred to it as 3DES from the time it first promulgated the idea, and this namesake has since come into wi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ars Technica
''Ars Technica'' is a website covering news and opinions in technology, science, politics, and society, created by Ken Fisher and Jon Stokes in 1998. It publishes news, reviews, and guides on issues such as computer hardware and software, science, technology policy, and video games. ''Ars Technica'' was privately owned until May 2008, when it was sold to Condé Nast Digital, the online division of Condé Nast Publications. Condé Nast purchased the site, along with two others, for $25 million and added it to the company's ''Wired'' Digital group, which also includes '' Wired'' and, formerly, Reddit. The staff mostly works from home and has offices in Boston, Chicago, London, New York City, and San Francisco. The operations of ''Ars Technica'' are funded primarily by advertising, and it has offered a paid subscription service since 2001. History Ken Fisher, who serves as the website's current editor-in-chief, and Jon Stokes created ''Ars Technica'' in 1998. Its purpose ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wired News
''Wired'' (stylized as ''WIRED'') is a monthly American magazine, published in print and online editions, that focuses on how emerging technologies affect culture, the economy, and politics. Owned by Condé Nast, it is headquartered in San Francisco, California, and has been in publication since March/April 1993. Several spin-offs have been launched, including ''Wired UK'', ''Wired Italia'', ''Wired Japan'', and ''Wired Germany''. From its beginning, the strongest influence on the magazine's editorial outlook came from founding editor and publisher Louis Rossetto. With founding creative director John Plunkett, Rossetto in 1991 assembled a 12-page prototype, nearly all of whose ideas were realized in the magazine's first several issues. In its earliest colophons, ''Wired'' credited Canadian media theorist Marshall McLuhan as its "patron saint". ''Wired'' went on to chronicle the evolution of digital technology and its impact on society. ''Wired'' quickly became recognized as ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Niels Ferguson
Niels T. Ferguson (born 10 December 1965, Eindhoven) is a Dutch cryptographer and consultant who currently works for Microsoft. He has worked with others, including Bruce Schneier, designing cryptographic algorithms, testing algorithms and protocols, and writing papers and books. Among the designs Ferguson has contributed to is the AES finalist block cipher algorithm Twofish as well as the stream cipher Helix and the Skein hash function. In 1999, Niels Ferguson, together with Bruce Schneier and John Kelsey, developed the Yarrow algorithm, a Cryptographically-Secure Pseudorandom Number Generator (CSPRNG). Yarrow was later further developed by Niels Ferguson and Bruce Schneier into the Fortuna CSPRNG In 2001, he claimed to have broken the HDCP system that is incorporated into HD DVD and Blu-ray Disc The Blu-ray Disc (BD), often known simply as Blu-ray, is a digital optical disc data storage format. It was invented and developed in 2005 and released on June 20, 200 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dan Shumow
Dan Shumow is a cryptographer working at Microsoft Research. At the CRYPTO 2007 conference rump session, Dan Shumow and Niels Ferguson presented an informal paper describing a kleptographic backdoor in the NIST specified Dual_EC_DRBG cryptographically secure pseudorandom number generator. The backdoor was confirmed to be real in 2013 as part of the Edward Snowden leaks. Dan Shumow co-authored an algorithm for detecting SHA-1 collisions with Marc Stevens, prior to the demonstration of a SHA-1 In cryptography, SHA-1 (Secure Hash Algorithm 1) is a cryptographically broken but still widely used hash function which takes an input and produces a 160- bit (20- byte) hash value known as a message digest – typically rendered as 40 hexa ... collision.http://shattered.io References External links Dan Shumow- Microsoft Research Modern cryptographers Living people Year of birth missing (living people) Place of birth missing (living people) Microsoft Research people ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Reuters
Reuters ( ) is a news agency owned by Thomson Reuters Corporation. It employs around 2,500 journalists and 600 photojournalists in about 200 locations worldwide. Reuters is one of the largest news agencies in the world. The agency was established in London in 1851 by the German-born Paul Reuter. It was acquired by the Thomson Corporation of Canada in 2008 and now makes up the media division of Thomson Reuters. History 19th century Paul Reuter worked at a book-publishing firm in Berlin and was involved in distributing radical pamphlets at the beginning of the Revolutions in 1848. These publications brought much attention to Reuter, who in 1850 developed a prototype news service in Aachen using homing pigeons and electric telegraphy from 1851 on, in order to transmit messages between Brussels and Aachen, in what today is Aachen's Reuters House. Reuter moved to London in 1851 and established a news wire agency at the London Royal Exchange. Headquartered in London, R ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |