|
Network Management Software
Network management software is software that is used to provision, discover, monitor and maintain computer networks. Purpose With the expansion of the World Wide Web and the Internet, computer networks have become very large and complex, making them impossible to manage manually. In response, a suite of network management software was developed to help reduce the burden of managing the growing complexity of computer networks. Network management software usually collects information about network devices (which are called Nodes) using protocols like SNMP, ICMP, CDP etc. This information is then presented to network administrators in an easy to understand and accessible manner to help them quickly identify and remediate problems. Problems may present itself in the form of network faults, performance bottlenecks, compliance issues etc. Some advanced network management software may rectify network problems automatically. Network management software may also help with tasks involved ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Software
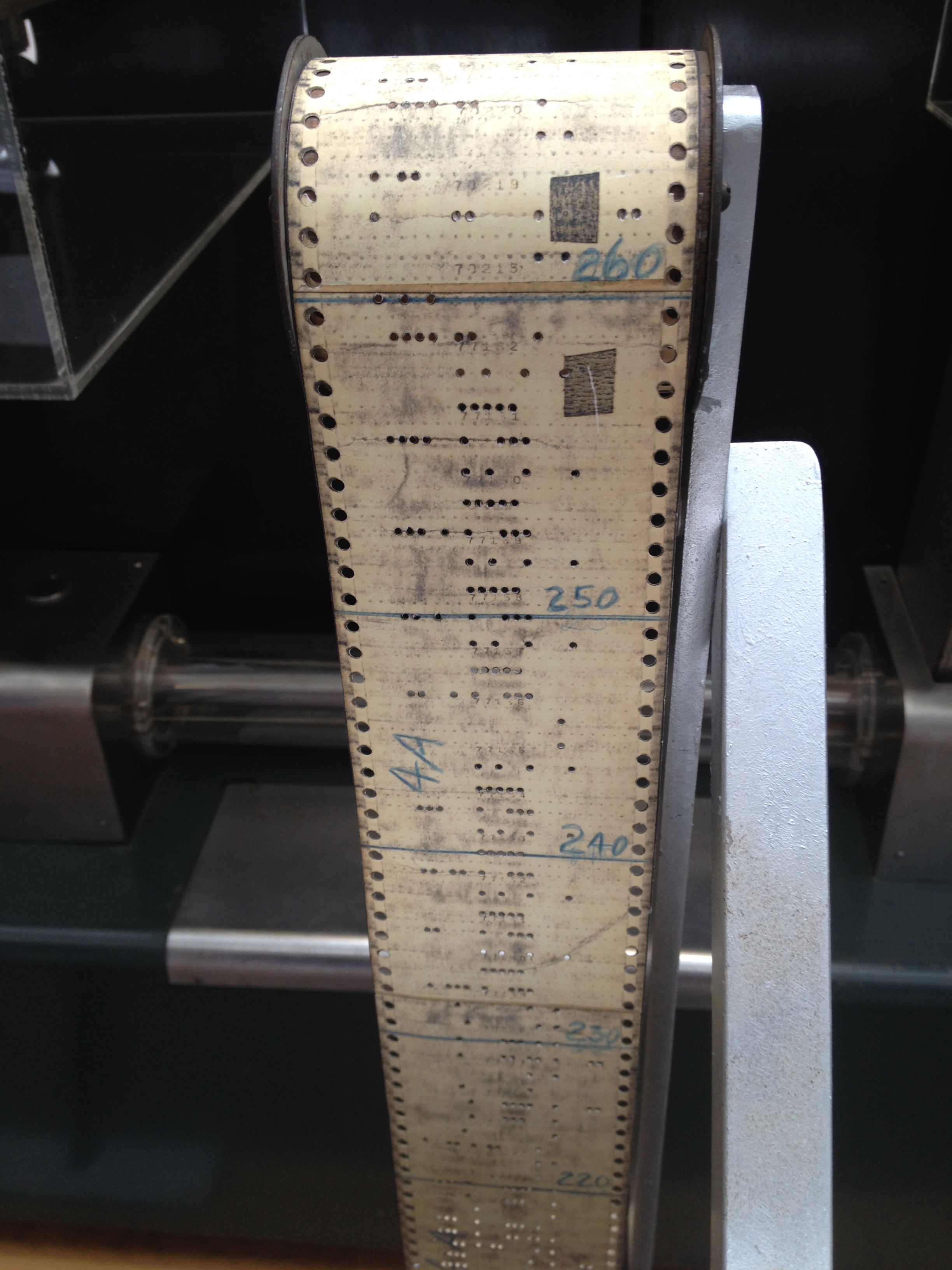
Software is a set of computer programs and associated software documentation, documentation and data (computing), data. This is in contrast to Computer hardware, hardware, from which the system is built and which actually performs the work. At the low level language, lowest programming level, executable code consists of Machine code, machine language instructions supported by an individual Microprocessor, processor—typically a central processing unit (CPU) or a graphics processing unit (GPU). Machine language consists of groups of Binary number, binary values signifying Instruction set architecture, processor instructions that change the state of the computer from its preceding state. For example, an instruction may change the value stored in a particular storage location in the computer—an effect that is not directly observable to the user. An instruction System call, may also invoke one of many Input/output, input or output operations, for example displaying some text on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Configuration Management
Configuration management (CM) is a process for establishing and maintaining consistency of a product's performance, functional, and physical attributes with its requirements, design, and operational information throughout its life. The CM process is widely used by military engineering organizations to manage changes throughout the system lifecycle of complex systems, such as weapon systems, military vehicles, and information systems. Outside the military, the CM process is also used with IT service management as defined by ITIL, and with other domain models in the civil engineering and other industrial engineering segments such as roads, bridges, canals, dams, and buildings. Introduction CM applied over the life cycle of a system provides visibility and control of its performance, functional, and physical attributes. CM verifies that a system performs as intended, and is identified and documented in sufficient detail to support its projected life cycle. The CM process f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Patch-management
A patch is a set of changes to a computer program or its supporting data designed to update, fix, or improve it. This includes fixing security vulnerabilities and other bugs, with such patches usually being called bugfixes or bug fixes. Patches are often written to improve the functionality, usability, or performance of a program. The majority of patches are provided by software vendors for operating system and application updates. Patches may be installed either under programmed control or by a human programmer using an editing tool or a debugger. They may be applied to program files on a storage device, or in computer memory. Patches may be permanent (until patched again) or temporary. Patching makes possible the modification of compiled and machine language object programs when the source code is unavailable. This demands a thorough understanding of the inner workings of the object code by the person creating the patch, which is difficult without close study of the source ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Software Deployment
Software deployment is all of the activities that make a software system available for use. The general deployment process consists of several interrelated activities with possible transitions between them. These activities can occur on the producer side or on the consumer side or both. Because every software system is unique, the precise processes or procedures within each activity can hardly be defined. Therefore, "deployment" should be interpreted as a ''general process'' that has to be customized according to specific requirements or characteristics. History When computers were extremely large, expensive, and bulky (mainframes and minicomputers), the software was often bundled together with the hardware by manufacturers. If business software needed to be installed on an existing computer, this might require an expensive, time-consuming visit by a systems architect or a consultant. For complex, on-premises installation of enterprise software today, this can still someti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Trespass
Computer trespass is a computer crime in the United States involving unlawful access to computers. It is defined under the Computer Fraud and Abuse act. ( U.S.C 18 § 1030) Definition A computer trespass is defined as accessing a computer without proper authorization and gaining financial information, information from a department or agency from any protected computer. Each state has its own laws regarding computer trespassing but they all echo the federal act in some manner. Examples of state legislation New York To be found guilty of computer trespass in New York one must knowingly use a computer, computer service, or computer network without authorization ''and'' commit (or attempt) some further crime. Ohio (A) No person shall knowingly use or operate the property of another without the consent of the owner or person authorized to give consent. (B) No person, in any manner and by any means, including, but not limited to, computer hacking, shall knowingly gain access to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Digital Forensics
Digital forensics (sometimes known as digital forensic science) is a branch of forensic science encompassing the recovery, investigation, examination and analysis of material found in digital devices, often in relation to mobile devices and computer crime. The term digital forensics was originally used as a synonym for computer forensics but has expanded to cover investigation of all devices capable of storing digital data. With roots in the personal computing revolution of the late 1970s and early 1980s, the discipline evolved in a haphazard manner during the 1990s, and it was not until the early 21st century that national policies emerged. Digital forensics investigations have a variety of applications. The most common is to support or refute a hypothesis before criminal or civil courts. Criminal cases involve the alleged breaking of laws that are defined by legislation and that are enforced by the police and prosecuted by the state, such as murder, theft and assault against ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Audit Trail
An audit trail (also called audit log) is a security-relevant chronological record, set of records, and/or destination and source of records that provide documentary evidence of the sequence of activities that have affected at any time a specific operation, procedure, event, or device. Audit records typically result from activities such as financial transactions, scientific research and health care data transactions, or communications by individual people, systems, accounts, or other entities. The process that creates an audit trail is typically required to always run in a privileged mode, so it can access and supervise all actions from all users; a normal user should not be allowed to stop/change it. Furthermore, for the same reason, the trail file or database table with a trail should not be accessible to normal users. Another way of handling this issue is through the use of a role-based security model in the software. The software can operate with the closed-looped controls, or ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Change Control
Within quality management systems (QMS) and information technology (IT) systems, change control is a process—either formal or informal—used to ensure that changes to a product or system are introduced in a controlled and coordinated manner. It reduces the possibility that unnecessary changes will be introduced to a system without forethought, introducing faults into the system or undoing changes made by other users of software. The goals of a change control procedure usually include minimal disruption to services, reduction in back-out activities, and cost-effective utilization of resources involved in implementing change. Change control is used in various industries, including in IT, software development, the pharmaceutical industry, the medical device industry, and other engineering/manufacturing industries. For the IT and software industries, change control is a major aspect of the broader discipline of change management. Typical examples from the computer and network en ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Regulatory Compliance
In general, compliance means conforming to a rule, such as a specification, policy, standard or law. Compliance has traditionally been explained by reference to the deterrence theory, according to which punishing a behavior will decrease the violations both by the wrongdoer (specific deterrence) and by others (general deterrence). This view has been supported by economic theory, which has framed punishment in terms of costs and has explained compliance in terms of a cost-benefit equilibrium (Becker 1968). However, psychological research on motivation provides an alternative view: granting rewards (Deci, Koestner and Ryan, 1999) or imposing fines (Gneezy Rustichini 2000) for a certain behavior is a form of extrinsic motivation that weakens intrinsic motivation and ultimately undermines compliance. Regulatory compliance describes the goal that organizations aspire to achieve in their efforts to ensure that they are aware of and take steps to comply with relevant laws, policies, a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Simple Network Management Protocol
Simple Network Management Protocol (SNMP) is an Internet Standard protocol for collecting and organizing information about managed devices on IP networks and for modifying that information to change device behaviour. Devices that typically support SNMP include cable modems, routers, switches, servers, workstations, printers, and more. SNMP is widely used in network management for network monitoring. SNMP exposes management data in the form of variables on the managed systems organized in a management information base (MIB) which describe the system status and configuration. These variables can then be remotely queried (and, in some circumstances, manipulated) by managing applications. Three significant versions of SNMP have been developed and deployed. SNMPv1 is the original version of the protocol. More recent versions, SNMPv2c and SNMPv3, feature improvements in performance, flexibility and security. SNMP is a component of the Internet Protocol Suite as defined by the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Network Monitoring
Network monitoring is the use of a system that constantly monitors a computer network for slow or failing components and that notifies the network administrator (via email, SMS or other alarms) in case of outages or other trouble. Network monitoring is part of network management. Details While an intrusion detection system monitors a network threats from the outside, a network monitoring system monitors the network for problems caused by overloaded or crashed servers, network connections or other devices. For example, to determine the status of a web server, monitoring software may periodically send an HTTP request to fetch a page. For email servers, a test message might be sent through SMTP and retrieved by IMAP or POP3. Commonly measured metrics are response time, availability and uptime, although both consistency and reliability metrics are starting to gain popularity. The widespread addition of WAN optimization devices is having an adverse effect on most network monitoring to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |