|
Cyber-terrorist
Cyberterrorism is the use of the Internet to conduct violent acts that result in, or threaten, the loss of life or significant bodily harm, in order to achieve political or ideological gains through threat or intimidation. Acts of deliberate, large-scale disruption of computer networks, especially of personal computers attached to the Internet by means of tools such as computer viruses, computer worms, phishing, malicious software, hardware methods, programming scripts can all be forms of internet terrorism. Cyberterrorism is a controversial term. Some authors opt for a very narrow definition, relating to deployment by known terrorist organizations of disruption attacks against information systems for the primary purpose of creating alarm, panic, or physical disruption. Other authors prefer a broader definition, which includes cybercrime. Participating in a cyberattack affects the terror threat perception, even if it isn't done with a violent approach. By some definitions, it migh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberwar
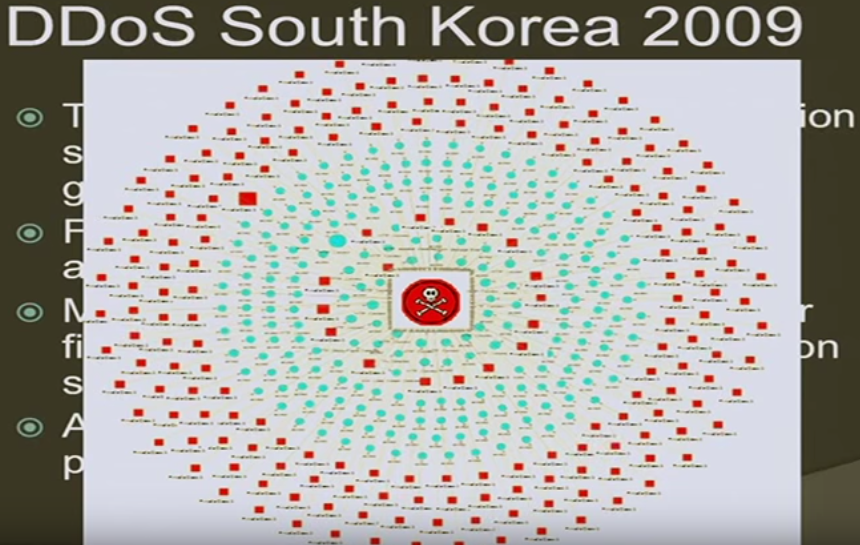
Cyberwarfare is the use of cyber attacks against an enemy state, causing comparable harm to actual warfare and/or disrupting vital computer systems. Some intended outcomes could be espionage, sabotage, propaganda, manipulation or economic warfare. There is significant debate among experts regarding the definition of cyberwarfare, and even if such a thing exists. One view is that the term is a misnomer, since no cyber attacks to date could be described as war. An alternative view is that it is a suitable label for cyber attacks which cause physical damage to people and objects in the real world. Many countries including the United States, United Kingdom, Russia, China, Israel, Iran, and North Korea have active cyber capabilities for offensive and defensive operations. As states explore the use of cyber operations and combine capabilities, the likelihood of physical confrontation and violence playing out as a result of, or part of, a cyber operation is increased. However, meeti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberwarfare
Cyberwarfare is the use of cyber attacks against an enemy state, causing comparable harm to actual warfare and/or disrupting vital computer systems. Some intended outcomes could be espionage, sabotage, propaganda, manipulation or economic warfare. There is significant debate among experts regarding the definition of cyberwarfare, and even if such a thing exists. One view is that the term is a misnomer, since no cyber attacks to date could be described as war. An alternative view is that it is a suitable label for cyber attacks which cause physical damage to people and objects in the real world. Many countries including the United States, United Kingdom, Russia, China, Israel, Iran, and North Korea have active cyber capabilities for offensive and defensive operations. As states explore the use of cyber operations and combine capabilities, the likelihood of physical confrontation and violence playing out as a result of, or part of, a cyber operation is increased. However, meeti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberwarfare
Cyberwarfare is the use of cyber attacks against an enemy state, causing comparable harm to actual warfare and/or disrupting vital computer systems. Some intended outcomes could be espionage, sabotage, propaganda, manipulation or economic warfare. There is significant debate among experts regarding the definition of cyberwarfare, and even if such a thing exists. One view is that the term is a misnomer, since no cyber attacks to date could be described as war. An alternative view is that it is a suitable label for cyber attacks which cause physical damage to people and objects in the real world. Many countries including the United States, United Kingdom, Russia, China, Israel, Iran, and North Korea have active cyber capabilities for offensive and defensive operations. As states explore the use of cyber operations and combine capabilities, the likelihood of physical confrontation and violence playing out as a result of, or part of, a cyber operation is increased. However, meeti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Terrorism
Terrorism, in its broadest sense, is the use of criminal violence to provoke a state of terror or fear, mostly with the intention to achieve political or religious aims. The term is used in this regard primarily to refer to intentional violence during peacetime or in the context of war against non-combatants (mostly civilians and neutral country, neutral military personnel). The terms "terrorist" and "terrorism" originated during the French Revolution of the late 18th century but became widely used internationally and gained worldwide attention in the 1970s during The Troubles, the Troubles in Northern Ireland, the Basque conflict, and the Israeli–Palestinian conflict. The increased use of suicide attacks from the 1980s onwards was typified by the 2001 September 11 attacks in the United States. There are various different definitions of terrorism, with no universal agreement about it. Terrorism is a Loaded language, charged term. It is often used with the connotation of some ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Conference Of State Legislatures
The National Conference of State Legislatures (NCSL), established in 1975, is a "nonpartisan public officials’ association composed of sitting state legislators" from the states, territories and commonwealths of the United States. Background According to their website, the mission of the Conference is: to advance the effectiveness, independence and integrity of legislatures and to foster interstate cooperation . . . especially in support of state sovereignty and state flexibility and protection from unfunded federal mandates and unwarranted federal preemption. The conference promotes cooperation between state legislatures in the U.S. and those in other countries. . . . [and] is committed to improving the operations and management of state legislatures, and the effectiveness of legislators and legislative staff. NCSL also encourages the practice of high standards of conduct by legislators and legislative staff. NCSL maintains an office in Denver, Colorado and Washington, D.C. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Business
The dot-com bubble (dot-com boom, tech bubble, or the Internet bubble) was a stock market bubble in the late 1990s, a period of massive growth in the use and adoption of the Internet. Between 1995 and its peak in March 2000, the Nasdaq Composite stock market index rose 400%, only to fall 78% from its peak by October 2002, giving up all its gains during the bubble. During the dot-com crash, many online shopping companies, such as Pets.com, Webvan, and Boo.com, as well as several communication companies, such as Worldcom, NorthPoint Communications, and Global Crossing, failed and shut down. Some companies that survived, such as Amazon, lost large portions of their market capitalization, with Cisco Systems alone losing 80% of its stock value. Background Historically, the dot-com boom can be seen as similar to a number of other technology-inspired booms of the past including railroads in the 1840s, automobiles in the early 20th century, radio in the 1920s, television in the 1 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hyperbole
Hyperbole (; adj. hyperbolic ) is the use of exaggeration as a rhetorical device or figure of speech. In rhetoric, it is also sometimes known as auxesis (literally 'growth'). In poetry and oratory, it emphasizes, evokes strong feelings, and creates strong impressions. As a figure of speech, it is usually not meant to be taken literally. Etymology 'Hyperbole' is derived from the grc, ''huperbolḗ'' by way of Latin. The word is composed from ''hupér'' 'above, beyond' and ''bállō'' 'throw'. Unlike most English words beginning with ''hyper-'', it is stressed on the second syllable. The first known use is in the 15th century. 'Hype' is a shortened version. Usage Hyperbole is often used for emphasis or effect. In casual speech, it functions as an intensifier: saying "the bag weighed a ton" simply means that the bag was extremely heavy. The rhetorical device may be used for serious or ironic or comic effects. Understanding hyperbole and its use in context can help un ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Stuxnet
Stuxnet is a malicious computer worm first uncovered in 2010 and thought to have been in development since at least 2005. Stuxnet targets supervisory control and data acquisition ( SCADA) systems and is believed to be responsible for causing substantial damage to the nuclear program of Iran. Although neither country has openly admitted responsibility, the worm is widely understood to be a cyberweapon built jointly by the United States and Israel in a collaborative effort known as Operation Olympic Games. The program, started during the Bush administration, was rapidly expanded within the first months of Barack Obama's presidency. Stuxnet specifically targets programmable logic controllers (PLCs), which allow the automation of electromechanical processes such as those used to control machinery and industrial processes including gas centrifuges for separating nuclear material. Exploiting four zero-day flaws, Stuxnet functions by targeting machines using the Microsoft Windows o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberspace
Cyberspace is a concept describing a widespread interconnected digital technology. "The expression dates back from the first decade of the diffusion of the internet. It refers to the online world as a world 'apart', as distinct from everyday reality. In cyberspace people can hide behind fake identities, as in the famous The New Yorker cartoon." (Delfanti, Arvidsson, 150) The term entered popular culture from science fiction and the arts but is now used by technology strategists, security professionals, government, military and industry leaders and entrepreneurs to describe the domain of the global technology environment, commonly defined as standing for the global network of interdependent information technology infrastructures, telecommunications networks and computer processing systems. Others consider cyberspace to be just a notional environment in which communication over computer networks occurs. The word became popular in the 1990s when the use of the Internet, networking, a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Warfare
Information warfare (IW) (as different from cyber warfare that attacks computers, software, and command control systems) is a concept involving the battlespace use and management of information and communication technology (ICT) in pursuit of a competitive advantage over an opponent. Information warfare is the manipulation of information trusted by a target without the target's awareness so that the target will make decisions against their interest but in the interest of the one conducting information warfare. As a result, it is not clear when information warfare begins, ends, and how strong or destructive it is. Information warfare may involve the collection of tactical information, assurance(s) that one's information is valid, spreading of propaganda or disinformation to demoralize or manipulate the enemy and the public, undermining the quality of the opposing force's information and denial of information-collection opportunities to opposing forces. Information warfare is cl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hacker (computer Security)
A security hacker is someone who explores methods for breaching defenses and exploiting weaknesses in a computer system or network. Hackers may be motivated by a multitude of reasons, such as profit, protest, information gathering, challenge, recreation, or evaluation of a system weaknesses to assist in formulating defenses against potential hackers. The subculture that has evolved around hackers is often referred to as the "computer underground". Longstanding controversy surrounds the meaning of the term "hacker." In this controversy, computer programmers reclaim the term ''hacker'', arguing that it refers simply to someone with an advanced understanding of computers and computer networks and that ''cracker'' is the more appropriate term for those who break into computers, whether computer criminals ( black hats) or computer security experts ( white hats). A 2014 article noted that "the black-hat meaning still prevails among the general public". History Birth of subcult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Biological Weapons
A biological agent (also called bio-agent, biological threat agent, biological warfare agent, biological weapon, or bioweapon) is a bacterium, virus, protozoan, parasite, fungus, or toxin that can be used purposefully as a weapon in bioterrorism or biological warfare (BW). In addition to these living or replicating pathogens, toxins and biotoxins are also included among the bio-agents. More than 1,200 different kinds of potentially weaponizable bio-agents have been described and studied to date. Biological agents have the ability to adversely affect human health in a variety of ways, ranging from relatively mild allergic reactions to serious medical conditions, including serious injury, as well as serious or permanent disability or even death. Many of these organisms are ubiquitous in the natural environment where they are found in water, soil, plants, or animals. Bio-agents may be amenable to "weaponization" to render them easier to deploy or disseminate. Genetic modification m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |