|
Backdoor.Win32.Seed
Backdoor.Win32.Seed is a backdoor Trojan for Microsoft Windows operating system family. Its first known detection goes back to February 7th, 2005, according to Securelist (Kaspersky Labs). Meanwhile, there are several variants of this malware, that do not self-replicate ( ''Non-A.I.''). Backdoor.Win32.Seed is spread manually, often under the premise that the .exe file is something beneficial. Distribution channels include IRC, peer-to-peer networks, newsgroup postings and e-mails. Other aliases * ''RDN/Generic BackDoor'' (McAfee) * ''Backdoor.Seed'' ( VBA32) * ''Bck/Small.EO'' ( Panda Labs) External links [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Backdoor (computing)
A backdoor is a typically covert method of bypassing normal authentication or encryption in a computer, product, embedded device (e.g. a home router), or its embodiment (e.g. part of a cryptosystem, algorithm, chipset, or even a "homunculus computer" —a tiny computer-within-a-computer such as that found in Intel's Intel Active Management Technology, AMT technology). Backdoors are most often used for securing remote access to a computer, or obtaining access to plaintext in cryptographic systems. From there it may be used to gain access to privileged information like passwords, corrupt or delete data on hard drives, or transfer information within autoschediastic networks. A backdoor may take the form of a hidden part of a program, a separate program (e.g. Back Orifice may subvert the system through a rootkit), code in the hardware backdoor, firmware of the hardware, or parts of an operating system such as Microsoft Windows, Windows. Trojan horse (computing), Trojan horses can be u ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Trojan Horse (computing)
In computing, a Trojan horse is any malware that misleads users of its true intent. The term is derived from the Ancient Greek story of the deceptive Trojan Horse that led to the fall of the city of Troy. Trojans generally spread by some form of social engineering; for example, where a user is duped into executing an email attachment disguised to appear innocuous (e.g., a routine form to be filled in), or by clicking on some fake advertisement on social media or anywhere else. Although their payload can be anything, many modern forms act as a backdoor, contacting a controller who can then have unauthorized access to the affected computer. Ransomware attacks are often carried out using a Trojan. Unlike computer viruses and worms, Trojans generally do not attempt to inject themselves into other files or otherwise propagate themselves. Use of the term It's not clear where or when the concept, and this term for it, was first used, but by 1971 the first Unix manual assumed its r ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Microsoft Windows
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry. For example, Windows NT for consumers, Windows Server for servers, and Windows IoT for embedded systems. Defunct Windows families include Windows 9x, Windows Mobile, and Windows Phone. The first version of Windows was released on November 20, 1985, as a graphical operating system shell for MS-DOS in response to the growing interest in graphical user interfaces (GUIs). Windows is the most popular desktop operating system in the world, with 75% market share , according to StatCounter. However, Windows is not the most used operating system when including both mobile and desktop OSes, due to Android's massive growth. , the most recent version of Windows is Windows 11 for consumer PCs and tablets, Windows 11 Enterprise for corporations, and Windows Server 2022 for servers. Genealogy By marketing ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kaspersky Labs
Kaspersky Lab (; Russian language, Russian: Лаборатория Касперского, Romanization of Russian, tr. ''Laboratoriya Kasperskogo'') is a Russian Multinational corporation, multinational cybersecurity and anti-virus provider headquartered in Moscow, Russia, and operated by a holding company in the United Kingdom. It was founded in 1997 by Eugene Kaspersky, Natalya Kaspersky, and Alexey De-Monderik; Eugene Kaspersky is currently the CEO. Kaspersky Lab develops and sells antivirus, internet security, password management, endpoint security, and other cybersecurity products and services. Kaspersky expanded abroad from 2005 to 2010 and grew to $704 million in annual revenues by 2020, up 8% from 2016, though annual revenues were down 8% in North America due to U.S. government security concerns. As of 2016, the software has about 400 million users and has the largest market-share of cybersecurity software vendors in Europe. Kaspersky Lab ranks fourth in the global rankin ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Artificial Intelligence
Artificial intelligence (AI) is intelligence—perceiving, synthesizing, and inferring information—demonstrated by machines, as opposed to intelligence displayed by animals and humans. Example tasks in which this is done include speech recognition, computer vision, translation between (natural) languages, as well as other mappings of inputs. The ''Oxford English Dictionary'' of Oxford University Press defines artificial intelligence as: the theory and development of computer systems able to perform tasks that normally require human intelligence, such as visual perception, speech recognition, decision-making, and translation between languages. AI applications include advanced web search engines (e.g., Google), recommendation systems (used by YouTube, Amazon and Netflix), understanding human speech (such as Siri and Alexa), self-driving cars (e.g., Tesla), automated decision-making and competing at the highest level in strategic game systems (such as chess and Go). ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Peer-to-peer Network
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network. They are said to form a peer-to-peer network of nodes. Peers make a portion of their resources, such as processing power, disk storage or network bandwidth, directly available to other network participants, without the need for central coordination by servers or stable hosts. Peers are both suppliers and consumers of resources, in contrast to the traditional client–server model in which the consumption and supply of resources are divided. While P2P systems had previously been used in many application domains, the architecture was popularized by the file sharing system Napster, originally released in 1999. The concept has inspired new structures and philosophies in many areas of human interaction. In such social contexts, peer-to-peer as a meme refers to the egalitarian soc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
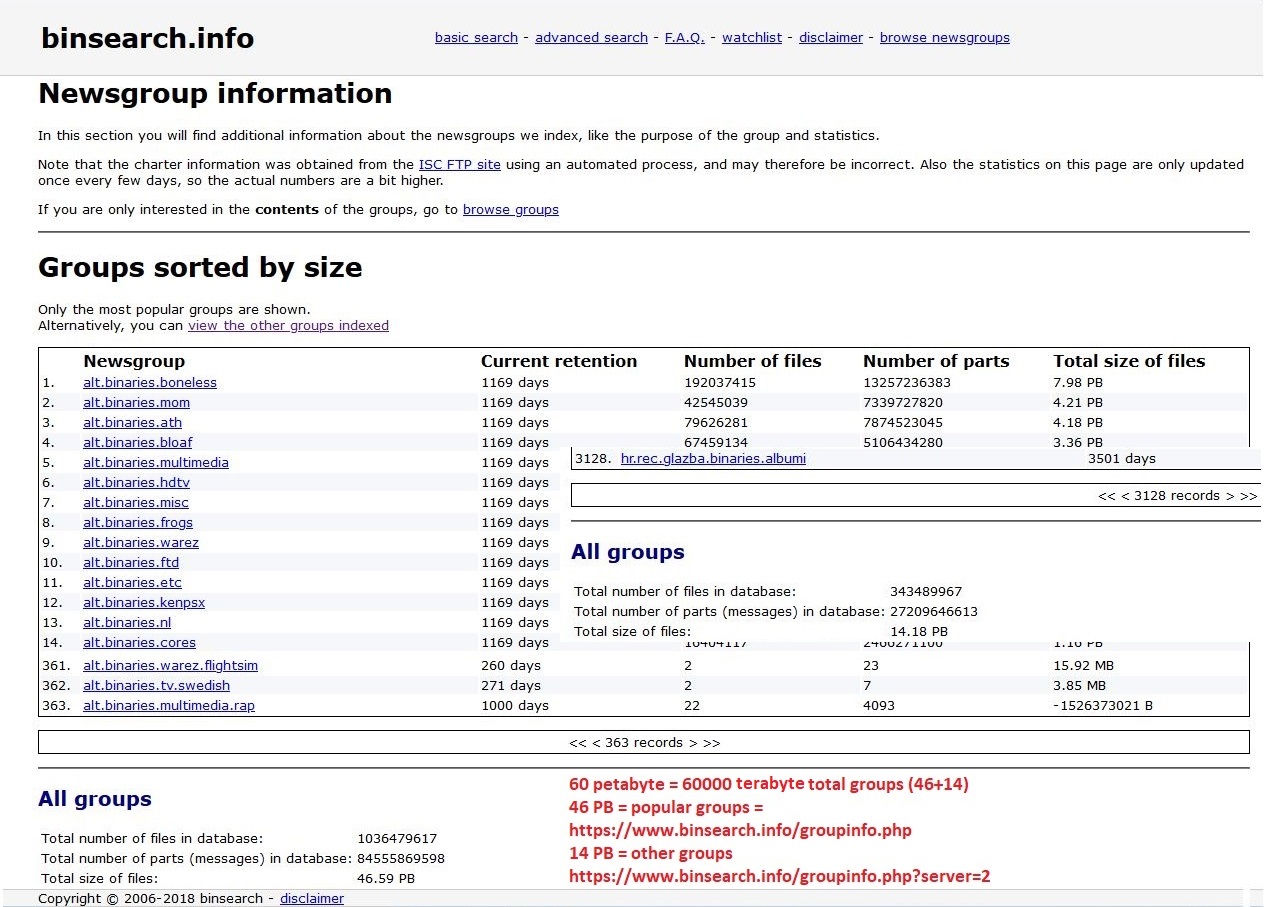
Newsgroup
A Usenet newsgroup is a repository usually within the Usenet system, for messages posted from users in different locations using the Internet. They are discussion groups and are not devoted to publishing news. Newsgroups are technically distinct from, but functionally similar to, discussion forums on the World Wide Web. Newsreader software is used to read the content of newsgroups. Before the adoption of the World Wide Web, Usenet newsgroups were among the most popular Internet services, and have retained their noncommercial nature in contrast to the increasingly ad-laden web. In recent years, this form of open discussion on the Internet has lost considerable ground to individually-operated browser-accessible forums and big media social networks such as Facebook and Twitter. Communication is facilitated by the Network News Transfer Protocol (NNTP) which allows connection to Usenet servers and data transfer over the internet. Similar to another early (yet still used) protocol ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
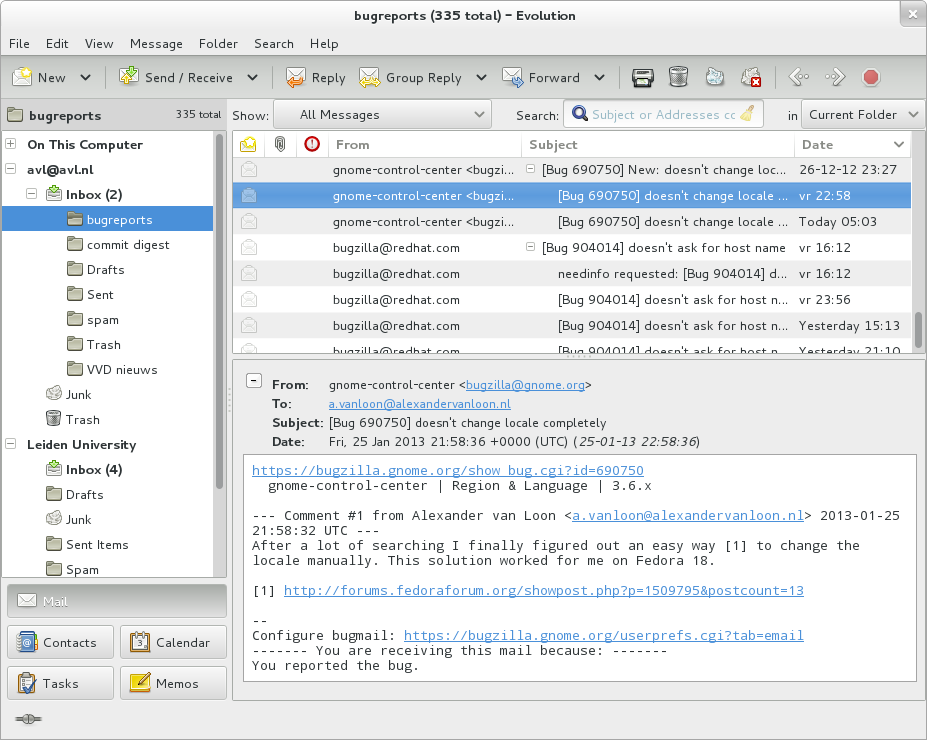
E-mail
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
McAfee
McAfee Corp. ( ), formerly known as McAfee Associates, Inc. from 1987 to 1997 and 2004 to 2014, Network Associates Inc. from 1997 to 2004, and Intel Security Group from 2014 to 2017, is an American global computer security software company headquartered in San Jose, California. The company was purchased by Intel in February 2011, and became part of the Intel Security division. In 2017, Intel had a strategic deal with TPG Capital and converted Intel Security into a joint venture between both companies called McAfee. Thoma Bravo took a minority stake in the new company, and Intel retained a 49% stake. The owners took McAfee public on the NASDAQ in 2020, and in 2022 an investor group led by Advent International Corporation took it private again. History 1987–1999 The company was founded in 1987 as McAfee Associates, named for its founder John McAfee, who resigned from the company in 1994. McAfee was incorporated in the state of Delaware in 1992. In 1993, McAfee stepped do ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
VBA32
VBA32 (Virus Block Ada 32) is antivirus software from the vendor VirusBlokAda for personal computers running Microsoft Windows. It detects and neutralizes computer viruses, computer worms, Trojan horses and other malware (backdoors, adware, spyware, etc.) in real time and on demand. VBA32 is used as one of the antivirus engines at VirusTotal. VirusBlokAda ''VirusBlokAda'' is an antivirus software vendor established in 1997 in Belarus. In 2010 it discovered Stuxnet, the first malware that attacks supervisory control and data acquisition (SCADA) systems. The program In 2009 Judit Papp assessed that its VBA32 Antivirus product could detect 26 percent of unknown malware, compared to 67 percent detected by Avira's Antivir Premium and 8 percent detected by MicroWorld's eScan Anti-Virus. See also * Antivirus software * Comparison of antivirus software * Comparison of computer viruses The compilation of a unified list of computer viruses is made difficult because of naming. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Panda Labs
Panda Security is a Spanish cybersecurity software company that specializes in creating products for IT security. Panda Security started with antivirus software, and the company now also provides and develops cybersecurity software. This includes security products and services for both businesses and home users, as well as protection tools for systems, networks, emails, and other private information. Panda Security employs around 450 people. Overview In 2005, Panda Security was the fourth largest antivirus vendor worldwide, with 3.2% of the marketplace. In November 2015 OPSWAT measured Panda Security's market share to be 3.6%. The company, whose shares were previously 100% held by Mikel Urizarbarrena, announced on 24 April 2007, the sale of 75% of its shares to Southern European investment group Investindustrial and private equity firm Gala Capital. On 30 July 2007 the company changed its name from Panda Software to Panda Security and Urizarbarrena was replaced by Jorge Dinare ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
VirusTotal
VirusTotal is a website created by the Spanish security company Hispasec Sistemas. Launched in June 2004, it was acquired by Google in September 2012. The company's ownership switched in January 2018 to Chronicle, a subsidiary of Google. VirusTotal aggregates many antivirus products and online scan engines called Contributors. In November, 2018, the Cyber National Mission Force, a unit subordinate to the U.S. Cyber Command became a Contributor. The aggregated data from these Contributors allows a user to check for viruses that the user's own antivirus software may have missed, or to verify against any false positives. Files up to 650 MB can be uploaded to the website, or sent via email (max. 32MB). Anti-virus software vendors can receive copies of files that were flagged by other scans but passed by their own engine, to help improve their software and, by extension, VirusTotal's own capability. Users can also scan suspect URLs and search through the VirusTotal dataset. VirusTo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |