|
Anti-malware
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other malware, antivirus software started to protect against other computer threats. Some products also include protection from malicious URLs, spam, and phishing. History 1971–1980 period (pre-antivirus days) The first known computer virus appeared in 1971 and was dubbed the " Creeper virus". This computer virus infected Digital Equipment Corporation's ( DEC) PDP-10 mainframe computers running the TENEX operating system.From the first email to the first YouTube video: a d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau of ''malicious software'')Tahir, R. (2018)A study on malware and malware detection techniques . ''International Journal of Education and Management Engineering'', ''8''(2), 20. is any software intentionally designed to cause disruption to a computer, server (computing), server, Client (computing), client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. Researchers tend to classify malware into one or more sub-types (i.e. computer viruses, Computer worm, worms, Trojan horse (computing), Trojan horses, logic bombs, ransomware, spyware, adware, rogue software, Wiper (malware), wipers and keyloggers). Malware poses serious problems to individuals and businesses on the Internet. According to NortonLifeLock, Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 66 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ESET NOD32
ESET NOD32 Antivirus, commonly known as NOD32, is an antivirus software package made by the Slovakia, Slovak company ESET. ESET NOD32 Antivirus is sold in two editions, Home Edition and Business Edition. The Business Edition packages add ESET Remote Administrator allowing for server deployment and management, mirroring of threat signature database updates and the ability to install on Microsoft Windows Server operating systems. History NOD32 The acronym NOD stands for ''Nemocnica na Okraji Disku'' ("Hospital at the boot sector, end of the disk"), a pun related to the Czechoslovakia, Czechoslovak medical drama series ''Hospital at the End of the City, Nemocnice na kraji města'' (''Hospital at the End of the City''). The first version of NOD32 called NOD-ICE was a DOS-based program. It was created in 1987 by Miroslav Trnka and Peter Paško at the time when computer viruses started to become increasingly prevalent on PCs running DOS. Due to the limitations of the OS (lack of Co ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Virus
A computer virus is a type of malware that, when executed, replicates itself by modifying other computer programs and Code injection, inserting its own Computer language, code into those programs. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses. Computer viruses generally require a Computer program, host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. By contrast, a computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the Computer program, host program, but can run independently and actively carry out attacks. Virus writers use social engineering (security), social engineering deceptions and exploit detailed knowledge of vulnerability (computing), security vulnerabilities to initially infect systems an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Brain (computer Virus)
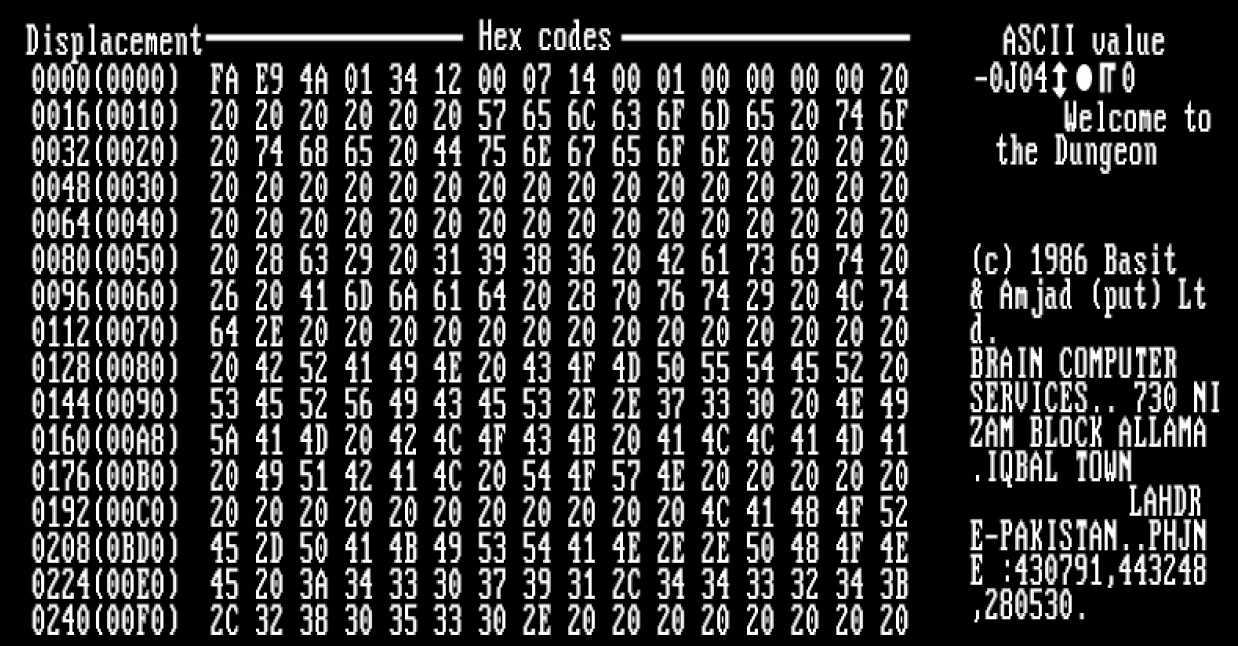
Brain is the industry standard name for a computer virus that was released in its first form on 19 January 1986, and is considered to be the first computer virus for the IBM Personal Computer (IBM PC) and compatibles. Description Brain affects the PC by replacing the boot sector of a floppy disk with a copy of the virus. The real boot sector is moved to another sector and marked as bad. Infected disks usually have five kilobytes of bad sectors. The disk label is usually changed to ©Brain, and the following text can be seen in infected boot sectors: :Welcome to the Dungeon (c) 1986 Amjads (pvt) Ltd VIRUS_SHOE RECORD V9.0 Dedicated to the dynamic memories of millions of viruses who are no longer with us today - Thanks GOODNESS!!! BEWARE OF THE er..VIRUS : this program is catching program follows after these ....$#@%$@!! There are many minor and major variations to that version of the text. The virus slows down the floppy disk drive and makes seven kilobytes of memory unavailab ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Rudolf Hrubý
Rudolf Hrubý (14 April 1954 – 14 December 2023) was a Slovak businessman and investor. He was a co-founder and long-term CFO of the software company ESET. Biography Early life Rudolf Hrubý was born on 14 April 1954 in Dubnica nad Váhom. He studied theoretical cybernetics at the Comenius University. Following graduation, he started a company developing accounting software. In 1992 he was invited by Miroslav Trnka and Peter Paško, the owners of IT security start up ESET to join their company as a partner. ESET era From 1992 to 2010 Hrubý was a member of top management of ESET, acting as the CFO. In 2010 he departed the management along with the other co-founders, but retained his 22 per cent share in the company. In an ''Forbes'' interview, Hrubý explained that coming from an IT background, he struggled to understand finance matters at first, but benefited from his experience in developing accounting software to understand the economic aspects of running a bus ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Czechoslovakia
Czechoslovakia ( ; Czech language, Czech and , ''Česko-Slovensko'') was a landlocked country in Central Europe, created in 1918, when it declared its independence from Austria-Hungary. In 1938, after the Munich Agreement, the Sudetenland became part of Nazi Germany, while the country lost further territories to First Vienna Award, Hungary and Trans-Olza, Poland (the territories of southern Slovakia with a predominantly Hungarian population to Hungary and Zaolzie with a predominantly Polish population to Poland). Between 1939 and 1945, the state ceased to exist, as Slovak state, Slovakia proclaimed its independence and Carpathian Ruthenia became part of Kingdom of Hungary (1920–1946), Hungary, while the German Protectorate of Bohemia and Moravia was proclaimed in the remainder of the Czech Lands. In 1939, after the outbreak of World War II, former Czechoslovak President Edvard Beneš formed Czechoslovak government-in-exile, a government-in-exile and sought recognition from the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
McAfee VirusScan
McAfee Antivirus is an antivirus software created and maintained by McAfee (formerly known as Intel Security, and Network Associates prior to that). Originally marketed as a standalone product, it is also bundled with McAfee Antivirus Plus, McAfee Internet Security, McAfee Total Protection, McAfee McAfee+ Premium, McAfee+ Advanced, McAfee+ Ultimate, and McAfee Business Protection. McAfee+ provides all-in-one protection for a user's personal info, privacy, and all their devices. It supports Windows, Mac, iOS, Android and ChromeOS devices and includes integrated antivirus, firewall and safe browsing capabilities as well as identity and privacy protection with identity monitoring, credit and financial monitoring, identity theft coverage and restoration,secure VPN, Online Account Cleanup, Personal Data Cleanup, Social Media Privacy Manager, and McAfee's AI-powered Scam Detector. VirusScan Enterprise Before McAfee completed the sale of its enterprise business it also produced a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
McAfee
McAfee Corp. ( ), formerly known as McAfee Associates, Inc. from 1987 to 1997 and 2004 to 2014, Network Associates Inc. from 1997 to 2004, and Intel Security Group from 2014 to 2017, is an American proprietary software company focused on online protection for consumers worldwide headquartered in San Jose, California. The company was purchased by Intel in February 2011; with this acquisition, it became part of the Intel Security division. In 2017, Intel had a strategic deal with TPG Capital and converted Intel Security into a joint venture between both companies called McAfee. Thoma Bravo took a minority stake in the new company, and Intel retained a Minority interest, 49% stake. The owners took McAfee public on the NASDAQ in 2020, and in 2022 an investor group led by Advent International Corporation took it Public company#Privatization, private again. History 1987–1999 The company was founded in 1987 as McAfee Associates, named for its founder John McAfee, who resigned ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
John McAfee
John David McAfee ( ; 18 September 1945 – 23 June 2021) was a British and American computer programmer, businessman, and two-time presidential candidate who unsuccessfully sought the Libertarian Party (United States), Libertarian Party nomination for president of the United States 2016 Libertarian National Convention, in 2016 and 2020 Libertarian National Convention, in 2020. In 1987, he wrote the first commercial Antivirus software, anti-virus software, founding McAfee, McAfee Associates to sell his creation. He resigned in 1994 and sold his remaining stake in the company. McAfee became the company's most vocal critic in later years, urging consumers to uninstall the company's anti-virus software, which he characterized as bloatware. He disavowed the company's continued use of his name in branding, a practice that has persisted in spite of a short-lived corporate rebrand attempt under Intel ownership. McAfee's fortunes plummeted in the 2008 financial crisis. After leaving McAf ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Atari Falcon
The Atari Falcon030 (usually shortened to Atari Falcon), released in 1992, is the final personal computer from Atari Corporation. A high-end model of the Atari ST line, the machine is based on a Motorola 68030 CPU and a Motorola 56001 digital signal processor, which distinguishes it from most other microcomputers of the era. It includes a new VIDEL programmable graphics system which greatly improves graphics capabilities. Shortly after release, Atari bundled the MultiTOS operating system in addition to TOS. TOS remained in ROM, and MultiTOS was supplied on floppy disk and could be installed to boot from hard disk. The Falcon was discontinued in late 1993–a year after its introduction–as Atari restructured itself to focus completely on the release and support of the Jaguar video game console. The Falcon sold in relatively small numbers, mainly to hobbyists. Hardware The heart of the system is the 32-bit Motorola 68030 clocked at 16 MHz. It runs at about 4 M ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Atari ST
Atari ST is a line of personal computers from Atari Corporation and the successor to the company's Atari 8-bit computers, 8-bit computers. The initial model, the Atari 520ST, had limited release in April–June 1985, and was widely available in July. It was the first personal computer with a bitmapped color graphical user interface, using a version of Digital Research's GEM (desktop environment), GEM environment from February 1985. The Atari 1040ST, released in 1986 with Megabyte, 1 MB of memory, was the first home computer with a cost per kilobyte of RAM under US$1/KB. After Jack Tramiel purchased the assets of the Atari, Inc. consumer division in 1984 to create Atari Corporation, the 520ST was designed in five months by a small team led by Shiraz Shivji. Alongside the Mac (computer), Macintosh, Amiga, Apple IIGS and Acorn Archimedes, the ST is part of a mid-1980s generation of computers with 16 or 16/32-bit processors, 256 kilobyte, KB or more of RAM, and computer m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
G Data Software
G Data CyberDefense AG (until September 2019 ''G Data Software AG'') is a German software company that focuses on computer security. The company was founded in 1985 and is headquartered in Bochum. They are known for being the creators of the world's first antivirus software. G Data uses multiple scanning engines; one is developed in-house and the other is the Bitdefender engine. G Data provides several security products that are targeted at home and business markets. The company has a North American subsidiary located in Newark, Delaware. History Antivirus Programs & Cyber Security (1985–2006) G Data was founded in Bochum, Germany, in 1985. The company introduced its first computer security product Anti-Virus Kit (AVK) in 1988 for Atari ST. In 1990, this program was given a graphical user interface for MS-DOS for the first time. In 1993, G Data developed the software GeoRoute, the first route planner with intelligent mapping. Beside focus on the securit ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |