|
Stealware
In computing, infostealers are a form of malicious software created to breach computer systems to steal sensitive information, such as login, login details, financial information, and other personally identifiable information. The stolen information is then packaged, sent to the attacker, and often traded on illicit markets to other Cyber criminals, cybercriminals. Infostealers usually consist of a bot framework that allows the attacker to configure the behaviour of the infostealer, and a management panel that takes the form of a server to which the infostealer sends data. Infostealers infiltrate devices through phishing attacks, infected websites, and malicious software downloads, including video game mods and pirated software, among other methods. Once downloaded, the infostealers gather sensitive information about the user's device and send the data back to the server. Infostealers are usually distributed under the malware-as a service, as-a-service (MaaS) model, where Programm ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computing
Computing is any goal-oriented activity requiring, benefiting from, or creating computer, computing machinery. It includes the study and experimentation of algorithmic processes, and the development of both computer hardware, hardware and software. Computing has scientific, engineering, mathematical, technological, and social aspects. Major computing disciplines include computer engineering, computer science, cybersecurity, data science, information systems, information technology, and software engineering. The term ''computing'' is also synonymous with counting and calculation, calculating. In earlier times, it was used in reference to the action performed by Mechanical computer, mechanical computing machines, and before that, to Computer (occupation), human computers. History The history of computing is longer than the history of computing hardware and includes the history of methods intended for pen and paper (or for chalk and slate) with or without the aid of tables. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Crime Forum
A crime forum is a generic term for an Internet forum specialising in computer crime and Internet fraud activities such as hacking, identity theft, phishing, pharming, malware, gay male sex trafficking rings, or spamming. During the early days of the Internet, public dial up BBSes would serve to put miscreants in touch with one another to share tips of credit card fraud, hacking and other illicit services. By the 2000s and the rise of the modern internet, modern internet forum software was preferred, with private invite-only sites being the most long lived. Sites like ShadowCrew, counterfeitlibrary.com and the Russian language carderplanet.com would specialise in various illegal activities before each eventually succumbing to law enforcement action. By 2015, notorious forums such as Darkode would be infiltrated and dismantled prior to returning with increased security. As of July 2015, there are estimated to be several hundred such forums. See also * BreachForums * Car ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Web Server
A web server is computer software and underlying Computer hardware, hardware that accepts requests via Hypertext Transfer Protocol, HTTP (the network protocol created to distribute web content) or its secure variant HTTPS. A user agent, commonly a web browser or web crawler, initiates communication by making a request for a web page or other Web Resource, resource using HTTP, and the server (computing), server responds with the content of that resource or an List of HTTP status codes, error message. A web server can also accept and store resources sent from the user agent if configured to do so. The hardware used to run a web server can vary according to the volume of requests that it needs to handle. At the low end of the range are embedded systems, such as a router (computing), router that runs a small web server as its configuration interface. A high-traffic Internet website might handle requests with hundreds of servers that run on racks of high-speed computers. A reso ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cloud Infrastructure
Cloud computing is "a paradigm for enabling network access to a scalable and elastic pool of shareable physical or virtual resources with self-service provisioning and administration on-demand," according to ISO. Essential characteristics In 2011, the National Institute of Standards and Technology (NIST) identified five "essential characteristics" for cloud systems. Below are the exact definitions according to NIST: * On-demand self-service: "A consumer can unilaterally provision computing capabilities, such as server time and network storage, as needed automatically without requiring human interaction with each service provider." * Broad network access: "Capabilities are available over the network and accessed through standard mechanisms that promote use by heterogeneous thin or thick client platforms (e.g., mobile phones, tablets, laptops, and workstations)." * Resource pooling: " The provider's computing resources are pooled to serve multiple consumers using a multi-ten ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
JavaScript
JavaScript (), often abbreviated as JS, is a programming language and core technology of the World Wide Web, alongside HTML and CSS. Ninety-nine percent of websites use JavaScript on the client side for webpage behavior. Web browsers have a dedicated JavaScript engine that executes the client code. These engines are also utilized in some servers and a variety of apps. The most popular runtime system for non-browser usage is Node.js. JavaScript is a high-level, often just-in-time–compiled language that conforms to the ECMAScript standard. It has dynamic typing, prototype-based object-orientation, and first-class functions. It is multi-paradigm, supporting event-driven, functional, and imperative programming styles. It has application programming interfaces (APIs) for working with text, dates, regular expressions, standard data structures, and the Document Object Model (DOM). The ECMAScript standard does not include any input/output (I/O), such as netwo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
HTML
Hypertext Markup Language (HTML) is the standard markup language for documents designed to be displayed in a web browser. It defines the content and structure of web content. It is often assisted by technologies such as Cascading Style Sheets (CSS) and scripting languages such as JavaScript, a programming language. Web browsers receive HTML documents from a web server or from local storage and browser engine, render the documents into multimedia web pages. HTML describes the structure of a web page Semantic Web, semantically and originally included cues for its appearance. HTML elements are the building blocks of HTML pages. With HTML constructs, HTML element#Images and objects, images and other objects such as Fieldset, interactive forms may be embedded into the rendered page. HTML provides a means to create structured documents by denoting structural semantics for text such as headings, paragraphs, lists, Hyperlink, links, quotes, and other items. HTML elements are delineated ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Web Development
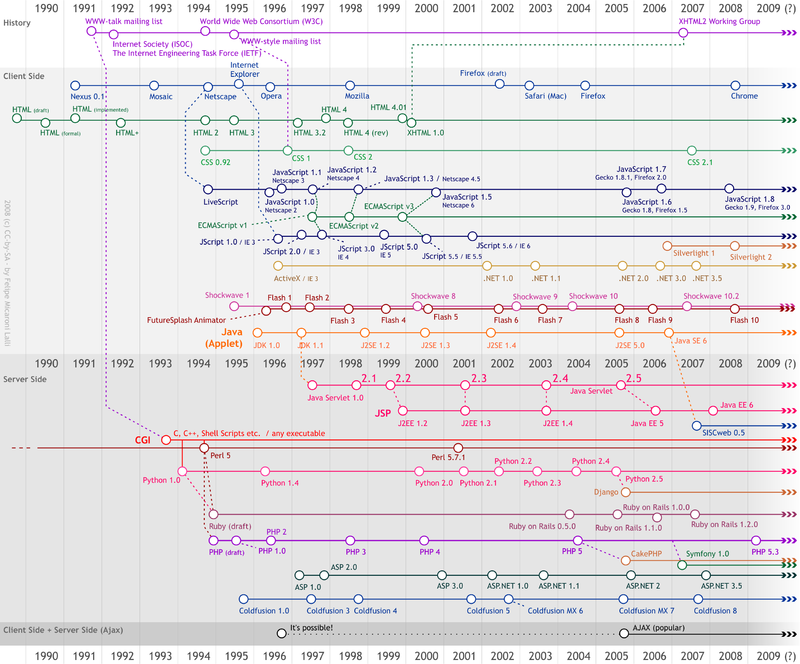
Web development is the work involved in developing a website for the Internet (World Wide Web) or an intranet (a private network). Web development can range from developing a simple single static page of plain text to complex web applications, electronic businesses, and social network services. A more comprehensive list of tasks to which Web development commonly refers, may include Web engineering, Web design, Web content development, client liaison, client-side/ server-side scripting, Web server and network security configuration, and e-commerce development. Among Web professionals, "Web development" usually refers to the main non-design aspects of building Web sites: writing markup and coding. Web development may use content management systems (CMS) to make content changes easier and available with basic technical skills. For larger organizations and businesses, Web development teams can consist of hundreds of people (Web developers) and follow standard methods like Ag ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Command And Control Server
A botnet is a group of Internet-connected devices, each of which runs one or more bots. Botnets can be used to perform distributed denial-of-service (DDoS) attacks, steal data, send spam, and allow the attacker to access the device and its connection. The owner can control the botnet using command and control (C&C) software. The word "botnet" is a portmanteau of the words "robot" and " network". The term is usually used with a negative or malicious connotation. Overview A botnet is a logical collection of Internet-connected devices, such as computers, smartphones or Internet of things (IoT) devices whose security have been breached and control ceded to a third party. Each compromised device, known as a "bot," is created when a device is penetrated by software from a ''malware'' (malicious software) distribution. The controller of a botnet is able to direct the activities of these compromised computers through communication channels formed by standards-based network protocols, suc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau of ''malicious software'')Tahir, R. (2018)A study on malware and malware detection techniques . ''International Journal of Education and Management Engineering'', ''8''(2), 20. is any software intentionally designed to cause disruption to a computer, server (computing), server, Client (computing), client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. Researchers tend to classify malware into one or more sub-types (i.e. computer viruses, Computer worm, worms, Trojan horse (computing), Trojan horses, logic bombs, ransomware, spyware, adware, rogue software, Wiper (malware), wipers and keyloggers). Malware poses serious problems to individuals and businesses on the Internet. According to NortonLifeLock, Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 66 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
HTTP Cookie
HTTP cookie (also called web cookie, Internet cookie, browser cookie, or simply cookie) is a small block of data (computing), data created by a web server while a user (computing), user is browsing a website and placed on the user's computer or other device by the user's web browser. Cookies are placed on the device used to access a website, and more than one cookie may be placed on a user's device during a session. Cookies serve useful and sometimes essential functions on the World Wide Web, web. They enable web servers to store program state, stateful information (such as items added in the shopping cart in an Online shopping, online store) on the user's device or to track the user's browsing activity (including clicking particular buttons, access control, logging in, or recording which Web browsing history, pages were visited in the past). They can also be used to save information that the user previously entered into Form (HTML), form fields, such as names, addresses, passw ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Password
A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the ''claimant'' while the party verifying the identity of the claimant is called the ''verifier''. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity. In general, a password is an arbitrary String (computer science), string of character (computing), characters including letters, digits, or other symbols. If the permissible characters are constrained to be numeric, the corresponding secret is sometimes ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Usernames
A user is a person who uses a computer or network service. A user often has a user account and is identified to the system by a username (or user name). Some software products provide services to other systems and have no direct end users. End user End users are the ultimate human users (also referred to as operators) of a software product. The end user stands in contrast to users who support or maintain the product such as sysops, database administrators and computer technicians. The term is used to abstract and distinguish those who only use the software from the developers of the system, who enhance the software for end users. In user-centered design, it also distinguishes the software operator from the client who pays for its development and other stakeholders who may not directly use the software, but help establish its requirements. This abstraction is primarily useful in designing the user interface, and refers to a relevant subset of characteristics that most exp ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |