|
Skipjack (cipher)
In cryptography, Skipjack is a block cipher—an algorithm In mathematics and computer science, an algorithm () is a finite sequence of rigorous instructions, typically used to solve a class of specific problems or to perform a computation. Algorithms are used as specifications for performing ... for encryption—developed by the United States, U.S. National Security Agency (NSA). Initially Classified information, classified, it was originally intended for use in the controversial Clipper chip. Subsequently, the algorithm was declassified. History of Skipjack Skipjack was proposed as the encryption algorithm in a US government-sponsored scheme of key escrow, and the cipher was provided for use in the Clipper chip, implemented in tamper resistance, tamperproof hardware. Skipjack is used only for encryption; the key escrow is achieved through the use of a separate mechanism known as the Clipper chip, Law Enforcement Access Field (LEAF). The algorithm was initially se ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collection, and processing of information and data for foreign and domestic intelligence and counterintelligence purposes, specializing in a discipline known as signals intelligence (SIGINT). The NSA is also tasked with the Information assurance, protection of U.S. communications networks and information systems. The NSA relies on a variety of measures to accomplish its mission, the majority of which are clandestine operations, clandestine. The existence of the NSA was not revealed until 1975. The NSA has roughly 32,000 employees. Originating as a unit to decipher coded communications in World War II, it was officially formed as the NSA by President Harry S. Truman in 1952. Between then and the end of the Cold War, it became the largest of the U.S. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Key (cryptography)
A key in cryptography is a piece of information, usually a string of numbers or letters that are stored in a file, which, when processed through a cryptographic algorithm, can encode or decode cryptographic data. Based on the used method, the key can be different sizes and varieties, but in all cases, the strength of the encryption relies on the security of the key being maintained. A key’s security strength is dependent on its algorithm, the size of the key, the generation of the key, and the process of key exchange. Scope The key is what is used to encrypt data from plaintext to ciphertext. There are different methods for utilizing keys and encryption. Symmetric cryptography Symmetric cryptography refers to the practice of the same key being used for both encryption and decryption. Asymmetric cryptography Asymmetric cryptography has separate keys for encrypting and decrypting. These keys are known as the public and private keys, respectively. Purpose Since the key ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dual EC DRBG
Dual_EC_DRBG (Dual Elliptic Curve Deterministic Random Bit Generator) is an algorithm that was presented as a cryptographically secure pseudorandom number generator (CSPRNG) using methods in elliptic curve cryptography. Despite wide public criticism, including the public identification of a backdoor, it was for seven years one of four CSPRNGs standardized in NIST SP 800-90A as originally published circa June 2006, until it was withdrawn in 2014. Weakness: a potential backdoor Weaknesses in the cryptographic security of the algorithm were known and publicly criticised well before the algorithm became part of a formal standard endorsed by the ANSI, ISO, and formerly by the National Institute of Standards and Technology (NIST). One of the weaknesses publicly identified was the potential of the algorithm to harbour a kleptographic backdoor advantageous to those who know about it—the United States government's National Security Agency (NSA)—and no one else. In 2013, ''T ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Backdoor (computing)
A backdoor is a typically covert method of bypassing normal authentication or encryption in a computer, product, embedded device (e.g. a home router), or its embodiment (e.g. part of a cryptosystem, algorithm, chipset, or even a "homunculus computer" —a tiny computer-within-a-computer such as that found in Intel's AMT technology). Backdoors are most often used for securing remote access to a computer, or obtaining access to plaintext in cryptographic systems. From there it may be used to gain access to privileged information like passwords, corrupt or delete data on hard drives, or transfer information within autoschediastic networks. A backdoor may take the form of a hidden part of a program, a separate program (e.g. Back Orifice may subvert the system through a rootkit), code in the firmware of the hardware, or parts of an operating system such as Windows. Trojan horses can be used to create vulnerabilities in a device. A Trojan horse may appear to be an entirely leg ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Public-key Encryption
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public key and a corresponding private key. Key pairs are generated with cryptographic algorithms based on mathematical problems termed one-way functions. Security of public-key cryptography depends on keeping the private key secret; the public key can be openly distributed without compromising security. In a public-key encryption system, anyone with a public key can encrypt a message, yielding a ciphertext, but only those who know the corresponding private key can decrypt the ciphertext to obtain the original message. For example, a journalist can publish the public key of an encryption key pair on a web site so that sources can send secret messages to the news organization in ciphertext. Only the journalist who knows the corresponding private key can decrypt the ciphertexts to obtain the sources' messages—an eavesdro ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Digital Fortress
''Digital Fortress'' is a techno-thriller novel written by American author Dan Brown and published in 1998 by St. Martin's Press. The book explores the theme of government surveillance of electronically stored information on the private lives of citizens, and the possible civil liberties and ethical implications of using such technology. Plot summary The story is set in the year of 1996. When the United States National Security Agency's code-breaking supercomputer TRANSLTR encounters a revolutionary new code, ''Digital Fortress,'' that it cannot break, Commander Trevor Strathmore calls in head cryptographer Susan Fletcher to crack it. She is informed by Strathmore that it was written by Ensei Tankado, a former NSA employee who became displeased with the NSA's intrusion into people's private lives. If the NSA doesn't reveal TRANSLTR to the public, Tankado intends to auction the code's algorithm on his website and have his partner, "North Dakota", release it for free if he dies, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dan Brown
Daniel Gerhard Brown (born June 22, 1964) is an American author best known for his thriller novels, including the Robert Langdon novels '' Angels & Demons'' (2000), ''The Da Vinci Code'' (2003), '' The Lost Symbol'' (2009), '' Inferno'' (2013), and ''Origin'' (2017). His novels are treasure hunts which usually take place over a period of 24 hours.Brown. Witness statement, pp. 17, 21. They feature recurring themes of cryptography, art, and conspiracy theories. His books have been translated into 57 languages and, as of 2012, have sold over 200 million copies. Three of them, ''Angels & Demons'', ''The Da Vinci Code'', and ''Inferno'', have been adapted into films, while one of them, ''The Lost Symbol'', was adapted into a television show. The Robert Langdon novels are deeply engaged with Christian themes and historical fiction, and have generated controversy as a result. Brown states on his website that his books are not anti-Christian and he is on a "constant spiritual journey ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Back-story
A backstory, background story, back-story, or background is a set of events invented for a plot, presented as preceding and leading up to that plot. It is a literary device of a narrative history all chronologically earlier than the narrative of primary interest. In acting, it is the history of the character before the drama begins, and is created during the actor's preparation. It is the history of characters and other elements that underlie the situation existing at the main narrative's start. Even a purely historical work selectively reveals backstory to the audience. Usage As a literary device, backstory is often employed to lend depth or believability to the main story. The usefulness of having a dramatic revelation was recognized by Aristotle, in ''Poetics''. Backstories are usually revealed, partially or in full, chronologically or otherwise, as the main narrative unfolds. However, a story creator may also create portions of a backstory or even an entire backstory ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
David A
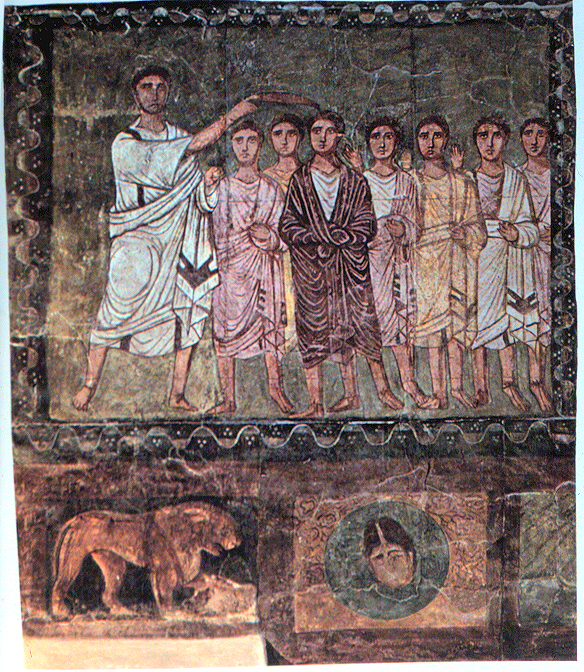
David (; , "beloved one") (traditional spelling), , ''Dāwūd''; grc-koi, Δαυΐδ, Dauíd; la, Davidus, David; gez , ዳዊት, ''Dawit''; xcl, Դաւիթ, ''Dawitʿ''; cu, Давíдъ, ''Davidŭ''; possibly meaning "beloved one". was, according to the Hebrew Bible, the third king of the United Kingdom of Israel. In the Books of Samuel, he is described as a young shepherd and harpist who gains fame by slaying Goliath, a champion of the Philistines, in southern Canaan. David becomes a favourite of Saul, the first king of Israel; he also forges a notably close friendship with Jonathan, a son of Saul. However, under the paranoia that David is seeking to usurp the throne, Saul attempts to kill David, forcing the latter to go into hiding and effectively operate as a fugitive for several years. After Saul and Jonathan are both killed in battle against the Philistines, a 30-year-old David is anointed king over all of Israel and Judah. Following his rise to power, Dav ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Lars Knudsen
Lars Ramkilde Knudsen (born 21 February 1962) is a Danish researcher in cryptography, particularly interested in the design and analysis of block ciphers, hash functions and message authentication codes (MACs). Academic After some early work in banking, Knudsen enrolled at Aarhus University in 1984 studying mathematics and computer science, gaining an MSc in 1992 and a PhD in 1994. From 1997-2001, he worked at the University of Bergen, Norway. Currently, Knudsen is a professor in the Department of Mathematics at the Technical University of Denmark. Ivan Damgård was Lars' mentor during his studies at Aarhus University. His Ph.D. was refereed by Bart Preneel. Publications Knudsen has published a couple of papers on cryptanalysis of cryptographic primitives, including the R-MAC scheme, the SHA-1 and MD2 hash functions, and a couple of block ciphers: DES, DFC, IDEA, ICE, LOKI, MISTY, RC2, RC5, RC6, SC2000, Skipjack, Square and SAFER. Knudsen was involved in designing ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Impossible Differential Cryptanalysis
In cryptography, impossible differential cryptanalysis is a form of differential cryptanalysis for block ciphers. While ordinary differential cryptanalysis tracks differences that propagate through the cipher with greater than expected probability, impossible differential cryptanalysis exploits differences that are impossible (having probability 0) at some intermediate state of the cipher algorithm. Lars Knudsen appears to be the first to use a form of this attack, in the 1998 paper where he introduced his AES candidate, DEAL. The first presentation to attract the attention of the cryptographic community was later the same year at the rump session of CRYPTO '98, in which Eli Biham, Alex Biryukov, and Adi Shamir introduced the name "impossible differential" and used the technique to break 4.5 out of 8.5 rounds of IDEA and 31 out of 32 rounds of the NSA-designed cipher Skipjack. This development led cryptographer Bruce Schneier to speculate that the NSA had no previous knowledge o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Alex Biryukov
Alex Biryukov is a cryptographer, currently a full professor at the University of Luxembourg. His notable work includes the design of the stream cipher LEX, as well as the cryptanalysis of numerous cryptographic primitives. In 1998, he developed impossible differential cryptanalysis together with Eli Biham and Adi Shamir. In 1999, he developed the slide attack together with David Wagner. In 2009 he developed, together with Dmitry Khovratovich, the first cryptanalytic attack on full-round AES-192 and AES-256 that is faster than a brute-force attack. In 2015 he developed the Argon2 key derivation function with Daniel Dinu and Dmitry Khovratovich. Since 1994 Alex Biryukov is a member of the International Association for Cryptologic Research International is an adjective (also used as a noun) meaning "between nations". International may also refer to: Music Albums * ''International'' (Kevin Michael album), 2011 * ''International'' (New Order album), 2002 * ''International' ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |