|
Collection No. 1
Collection #1 is a set of email addresses and passwords that appeared on the dark web around January 2019. The database contains over 773 million unique email addresses and 21 million unique passwords, resulting in more than 2.7 billion email/password pairs. The list, reviewed by computer security experts, contains exposed addresses and passwords from over 2000 previous data breaches as well as an estimated 140 million new email addresses and 10 million new passwords from previously unknown sources, and collectively makes it the largest data breach on the Internet. Collection #1 was discovered by security researcher Troy Hunt, founder of " Have I Been Pwned?," a website that allows users to search their email addresses and passwords to know if either has appeared in a known data breach. The database had been briefly posted to Mega in January 2019, and links to the database posted in a popular hacker forum. Hunt discovered that the offering contained 87 gigabytes of data across ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Dark Web
The dark web is the World Wide Web content that exists on darknets ( overlay networks) that use the Internet but require specific software, configurations, or authorization to access. Through the dark web, private computer networks can communicate and conduct business anonymously without divulging identifying information, such as a user's location. The dark web forms a small part of the deep web, the part of the web not indexed by web search engines, although sometimes the term ''deep web'' is mistakenly used to refer specifically to the dark web. The darknets which constitute the dark web include small, friend-to-friend networks, as well as large, popular networks such as Tor, Hyphanet, I2P, and Riffle operated by public organizations and individuals. Users of the dark web refer to the regular web as clearnet due to its unencrypted nature. The Tor dark web or onionland uses the traffic anonymization technique of onion routing under the network's top-level domain suffi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Gizmodo
''Gizmodo'' () is a design, technology, science, and science fiction website. It was originally launched as part of the Gawker Media network run by Nick Denton. ''Gizmodo'' also includes the sub-blogs ''io9'' and ''Earther'', which focus on pop-culture and environmentalism, respectively. Following the Chapter 11, Title 11, United States Code, Chapter 11 bankruptcy and Liquidation of Gawker Media, Univision Communications, Univision purchased ''Gizmodo'' along with other Gawker websites in August 2016. In 2019, Univision sold the Gizmodo Media Group, which included ''Gizmodo'', to the private equity firm Great Hill Partners. From April 2019 to June 2024, ''Gizmodo'' was part of G/O Media. In June 2024, the website was purchased by Swiss digital media company Keleops Media. History Origins and Gawker Media The blog, launched in 2002, was originally edited by Peter Rojas, who was later recruited by Weblogs, Inc. to launch its similar technology blog, ''Engadget''. By mid-2004 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Wired (magazine)
''Wired'' is a bi-monthly American magazine that focuses on how emerging technologies affect culture, the economy, and politics. It is published in both print and Online magazine, online editions by Condé Nast. The magazine has been in publication since its launch in January 1993. Its editorial office is based in San Francisco, California, with its business headquarters located in New York City. ''Wired'' quickly became recognized as the voice of the emerging digital economy and culture and a pace setter in print design and web design. From 1998 until 2006, the magazine and its website, ''Wired.com'', experienced separate ownership before being fully consolidated under Condé Nast in 2006. It has won multiple National Magazine Awards and has been credited with shaping discourse around the digital revolution. The magazine also coined the term Crowdsourcing, ''crowdsourcing'', as well as its annual tradition of handing out Vaporware Awards. ''Wired'' has launched several in ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Troy Hunt
Troy Adam Hunt is an Australian web security consultant known for public education and outreach on security topics. He created and operates Have I Been Pwned?, a data breach search website that allows users to see if their personal information has been compromised. He has also authored several popular security-related courses on Pluralsight, and regularly presents keynotes and workshops on security topics. He created ASafaWeb, a tool that formerly performed automated security analysis on ASP.NET websites. Data breaches As part of his work administering the Have I Been Pwned? (HIBP) website, Hunt has been involved in the publication of 644 data breaches , and journalists cite him as a cybersecurity expert and data-breach expert. , HIBP had recorded more than 5 billion compromised user-accounts. Governments of Australia, United Kingdom and Spain use the service to monitor their official domains. Popular services, such as 1Password, '' Eve Online'', Okta and Kogan, have integ ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Have I Been Pwned?
Have I Been Pwned? (HIBP; stylized in all lowercase as "‘;--have i been pwned?") is a website that allows Internet users to check whether their personal data has been compromised by data breaches. The site has been widely touted as a valuable resource for Internet users wishing to protect their own security and privacy. Have I Been Pwned? was created by security expert Troy Hunt on 4 December 2013. , Have I Been Pwned? averages around one hundred and sixty thousand daily visitors, the site has nearly three million active email subscribers and contains records of almost eight billion accounts. Features The primary function of Have I Been Pwned? since it was launched is to provide the general public with a means to check if their private information has been leaked or compromised. The service collects and analyzes hundreds of database dumps and pastes containing information about billions of leaked accounts, and allows users to search for their own information by enterin ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Ars Technica
''Ars Technica'' is a website covering news and opinions in technology, science, politics, and society, created by Ken Fisher and Jon Stokes in 1998. It publishes news, reviews, and guides on issues such as computer hardware and software, science, technology policy, and video games. ''Ars Technica'' was privately owned until May 2008, when it was sold to Condé Nast Digital, the online division of Condé Nast Publications. Condé Nast purchased the site, along with two others, for $25 million and added it to the company's ''Wired'' Digital group, which also includes '' Wired'' and, formerly, Reddit. The staff mostly works from home and has offices in Boston, Chicago, London, New York City, and San Francisco. The operations of ''Ars Technica'' are funded primarily by advertising, and it has offered a paid subscription service since 2001. History Ken Fisher, who serves as the website's current editor-in-chief, and Jon Stokes created ''Ars Technica'' in 1998. Its purpose was t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Mega (service)
Mega (stylised as MEGA) is a file hosting service offered by Mega Cloud Services Limited, a company based in Auckland, New Zealand, and owned by Hong Kong–based Cloud Tech Services Limited. The service is offered through web-based apps. MEGA mobile apps are also available for Android and iOS. Data encryption Files hosted on MEGA are end-to-end encrypted. As a result, the company cannot decrypt or view the content, and cannot be responsible for the contents of uploaded files. In the first few weeks after the MEGA launch, various security problems were found that researchers said an attacker could use to gain access to a logged-in user's files. In response, MEGA started a vulnerability reward program, offering a reward of up to €10,000 for reporting security problems. History MEGA was launched by Kim Dotcom in 2013 as a cloud service and successor to Megaupload. On 4 July 2013, the MEGA Android application was released on the Google Play marketplace. Four days lat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Plaintext
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. This usually refers to data that is transmitted or stored unencrypted. Overview With the advent of computing, the term ''plaintext'' expanded beyond human-readable documents to mean any data, including binary files, in a form that can be viewed or used without requiring a key or other decryption device. Information—a message, document, file, etc.—if to be communicated or stored in an unencrypted form is referred to as plaintext. Plaintext is used as input to an encryption algorithm; the output is usually termed ciphertext, particularly when the algorithm is a cipher. Codetext is less often used, and almost always only when the algorithm involved is actually a code. Some systems use multiple layers of encryption, with the output of one encryption algorithm becoming "plaintext" input for the next. Secure handling Insecure handling of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
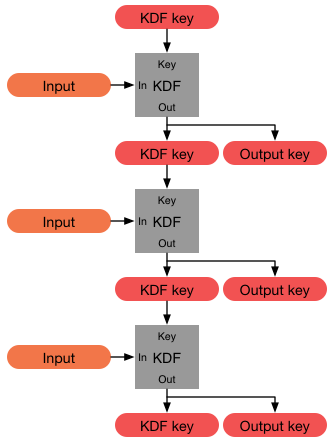
Key Derivation Function
In cryptography, a key derivation function (KDF) is a cryptographic algorithm that derives one or more secret keys from a secret value such as a master key, a password, or a passphrase using a pseudorandom function (which typically uses a cryptographic hash function or block cipher). KDFs can be used to stretch keys into longer keys or to obtain keys of a required format, such as converting a group element that is the result of a Diffie–Hellman key exchange into a symmetric key for use with AES. Keyed cryptographic hash functions are popular examples of pseudorandom functions used for key derivation. History The first deliberately slow (key stretching) password-based key derivation function was called "crypt" (or "crypt(3)" after its man page), and was invented by Robert Morris in 1978. It would encrypt a constant (zero), using the first 8 characters of the user's password as the key, by performing 25 iterations of a modified DES encryption algorithm (in which a 12-b ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Credential Stuffing
Credential stuffing is a type of cyberattack in which the attacker collects stolen account credentials, typically consisting of lists of usernames or email addresses and the corresponding passwords (often from a data breach), and then uses the credentials to gain unauthorized access to user accounts on other systems through large-scale automated login requests directed against a web application. Unlike credential cracking, credential stuffing attacks do not attempt to use brute force or guess any passwords – the attacker simply automates the logins for a large number (thousands to millions) of previously discovered credential pairs using standard web automation tools such as Selenium, cURL, PhantomJS or tools designed specifically for these types of attacks, such as Sentry MBA, SNIPR, STORM, Blackbullet and Openbullet. Credential stuffing attacks are possible because many users reuse the same username/password combination across multiple sites, with one survey reporting that ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Yahoo! Data Breaches
In 2013 and 2014, the American web services company Yahoo was subjected to two of the largest data breaches on record. Although Yahoo was aware, neither breach was revealed publicly until September 2016. The 2013 data breach occurred on Yahoo servers in August 2013 and affected all three billion user accounts. The 2014 breach affected over 500 million user accounts. Both breaches are considered the largest ever discovered and included names, email addresses, phone numbers, birth dates, and security questions—both encrypted and unencrypted. When Yahoo made the breaches public in 2016, they acknowledged being aware of the second intrusion since 2014. These incidents led to the indictment of four individuals linked to the latter breach, including the Canadian hacker Karim Baratov who received a five-year prison sentence and also prompted widespread criticism of Yahoo for their delayed response. The fallout included a U.S. $117.5 million class-action lawsuit settlement, a $3 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
LinkedIn
LinkedIn () is an American business and employment-oriented Social networking service, social network. It was launched on May 5, 2003 by Reid Hoffman and Eric Ly. Since December 2016, LinkedIn has been a wholly owned subsidiary of Microsoft. The platform is primarily used for professional networking and career development, and allows jobseekers to post their Curriculum vitae, CVs and employers to post jobs. From 2015, most of the company's revenue came from Information broker, selling access to information about its members to recruiters and sales professionals and has also introduced their own ad portal named LinkedIn Ads to let companies advertise in their platform. LinkedIn has more than 1 billion registered members from over 200 countries and territories. LinkedIn allows members (both employees and employers) to create profiles and connect with each other in an online social network which may represent real-world professional relationships. Members can invite anyone (whet ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |