Security Tokens on:
[Wikipedia]
[Google]
[Amazon]
 A security token is a
A security token is a
 ; Static password token: The device contains a password which is physically hidden (not visible to the possessor), but which is transmitted for each authentication. This type is vulnerable to
; Static password token: The device contains a password which is physically hidden (not visible to the possessor), but which is transmitted for each authentication. This type is vulnerable to
 Disconnected tokens have neither a physical nor logical connection to the client computer. They typically do not require a special input device, and instead use a built-in screen to display the generated authentication data, which the user enters manually themselves via a
Disconnected tokens have neither a physical nor logical connection to the client computer. They typically do not require a special input device, and instead use a built-in screen to display the generated authentication data, which the user enters manually themselves via a
, usb.org
US Personal Identity Verification (PIV)
OATH Initiative for open authentication
{{DEFAULTSORT:Security Token Computer access control Authentication methods
 A security token is a
A security token is a peripheral device
A peripheral or peripheral device is an auxiliary device used to put information into and get information out of a computer. The term ''peripheral device'' refers to all hardware components that are attached to a computer and are controlled by the ...
used to gain access to an electronically restricted resource. The token is used in addition to or in place of a password
A password, sometimes called a passcode (for example in Apple devices), is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of ...
. It acts like an electronic key to access something. Examples of security tokens include wireless keycards used to open locked doors, or in the case of a customer trying to access their bank account online, bank-provided tokens can prove that the customer is who they claim to be.
Some security tokens may store cryptographic key
A key in cryptography is a piece of information, usually a string of numbers or letters that are stored in a file, which, when processed through a cryptographic algorithm, can encode or decode cryptographic data. Based on the used method, the key c ...
s that may be used to generate a digital signature
A digital signature is a mathematical scheme for verifying the authenticity of digital messages or documents. A valid digital signature, where the prerequisites are satisfied, gives a recipient very high confidence that the message was created b ...
, or biometric
Biometrics are body measurements and calculations related to human characteristics. Biometric authentication (or realistic authentication) is used in computer science as a form of identification and access control. It is also used to identify in ...
data, such as fingerprint
A fingerprint is an impression left by the friction ridges of a human finger. The recovery of partial fingerprints from a crime scene is an important method of forensic science. Moisture and grease on a finger result in fingerprints on surfac ...
details. Some may also store passwords
A password, sometimes called a passcode (for example in Apple devices), is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of ...
. Some designs incorporate tamper resistant
Tamperproofing, conceptually, is a methodology used to hinder, deter or detect unauthorised access to a device or circumvention of a security system. Since any device or system can be foiled by a person with sufficient knowledge, equipment, and ti ...
packaging, while others may include small keypads to allow entry of a PIN
A pin is a device used for fastening objects or material together.
Pin or PIN may also refer to:
Computers and technology
* Personal identification number (PIN), to access a secured system
** PIN pad, a PIN entry device
* PIN, a former Dutch de ...
or a simple button to start a generating routine with some display capability to show a generated key number. Connected tokens utilize a variety of interfaces including USB
Universal Serial Bus (USB) is an industry standard that establishes specifications for cables, connectors and protocols for connection, communication and power supply (interfacing) between computers, peripherals and other computers. A broad v ...
, near-field communication
Near-field communication (NFC) is a set of communication protocols that enables communication between two electronic devices over a distance of 4 cm (1 in) or less. NFC offers a low-speed connection through a simple setup that can be u ...
(NFC), radio-frequency identification
Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of a tiny radio transponder, a radio receiver and transmitter. When triggered by an electromag ...
(RFID), or Bluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is limi ...
. Some tokens have an audio capability designed for vision-impaired people.
Password types
All tokens contain some secret information that is used to prove identity. There are four different ways in which this information can be used:replay attack
A replay attack (also known as a repeat attack or playback attack) is a form of network attack in which valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary wh ...
s.
; Synchronous dynamic password token: A timer is used to rotate through various combinations produced by a cryptographic algorithm
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decip ...
. The token and the authentication server must have synchronized clocks.
; Asynchronous password token: A one-time password
A one-time password (OTP), also known as a one-time PIN, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid seve ...
is generated without the use of a clock, either from a one-time pad
In cryptography, the one-time pad (OTP) is an encryption technique that cannot be cracked, but requires the use of a single-use pre-shared key that is not smaller than the message being sent. In this technique, a plaintext is paired with a ran ...
or cryptographic algorithm.
; Challenge–response token: Using public key cryptography
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public key and a corresponding private key. Key pairs are generated with cryptographic alg ...
, it is possible to prove possession of a private key without revealing that key. The authentication server encrypts a challenge (typically a random number, or at least data with some random parts) with a public key; the device proves it possesses a copy of the matching private key by providing the decrypted challenge.
Time-synchronized, one-time passwords change constantly at a set time interval; e.g., once per minute. To do this, some sort of synchronization must exist between the client
Client(s) or The Client may refer to:
* Client (business)
* Client (computing), hardware or software that accesses a remote service on another computer
* Customer or client, a recipient of goods or services in return for monetary or other valuable ...
's token and the authentication server
Server may refer to:
Computing
*Server (computing), a computer program or a device that provides functionality for other programs or devices, called clients
Role
* Waiting staff, those who work at a restaurant or a bar attending customers and su ...
. For disconnected tokens, this time-synchronization is done before the token is distributed to the client
Client(s) or The Client may refer to:
* Client (business)
* Client (computing), hardware or software that accesses a remote service on another computer
* Customer or client, a recipient of goods or services in return for monetary or other valuable ...
. Other token types do the synchronization when the token is inserted into an input device
In computing, an input device is a piece of equipment used to provide data and control signals to an information processing system, such as a computer or information appliance. Examples of input devices include keyboards, mouse, scanners, cameras ...
. The main problem with time-synchronized tokens is that they can, over time, become unsynchronized. However, some such systems, such as RSA's SecurID, allow the user to re-synchronize the server with the token, sometimes by entering several consecutive passcodes. Most also cannot have replaceable batteries and only last up to 5 years before having to be replaced – so there is an additional cost.
Another type of one-time password uses a complex mathematical algorithm, such as a hash chain
A hash chain is the successive application of a cryptographic hash function to a piece of data. In computer security, a hash chain is a method to produce many one-time keys from a single key or password. For non-repudiation a hash function can be ...
, to generate a series of one-time passwords from a secret shared key. Each password is unguessable, even when previous passwords are known. The open-source OATH
Traditionally an oath (from Anglo-Saxon ', also called plight) is either a statement of fact or a promise taken by a sacrality as a sign of verity. A common legal substitute for those who conscientiously object to making sacred oaths is to ...
algorithm is standardized; other algorithms are covered by US patent
A patent is a type of intellectual property that gives its owner the legal right to exclude others from making, using, or selling an invention for a limited period of time in exchange for publishing an enabling disclosure of the invention."A p ...
s. Each password is observably unpredictable and independent of previous ones, whereby an adversary would be unable to guess what the next password may be, even with knowledge of all previous passwords.
Physical types
Tokens can containchips
''CHiPs'' is an American crime drama television series created by Rick Rosner and originally aired on NBC from September 15, 1977, to May 1, 1983. It follows the lives of two motorcycle officers of the California Highway Patrol (CHP). The serie ...
with functions varying from very simple to very complex, including multiple authentication methods.
The simplest security tokens do not need any connection to a computer
A computer is a machine that can be programmed to Execution (computing), carry out sequences of arithmetic or logical operations (computation) automatically. Modern digital electronic computers can perform generic sets of operations known as C ...
. The tokens have a physical display; the authenticating user simply enters the displayed number to log in. Other tokens connect to the computer using wireless techniques, such as Bluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is limi ...
. These tokens transfer a key sequence to the local client or to a nearby access point.
Alternatively, another form of token that has been widely available for many years is a mobile device which communicates using an out-of-band channel (like voice, SMS
Short Message/Messaging Service, commonly abbreviated as SMS, is a text messaging service component of most telephone, Internet and mobile device systems. It uses standardized communication protocols that let mobile devices exchange short text ...
, or USSD
Unstructured Supplementary Service Data (USSD), sometimes referred to as "quick codes" or "feature codes", is a communications protocol used by GSM cellular telephones to communicate with the mobile network operator's computers. USSD can be used ...
).
Still other tokens plug into the computer, and may require a PIN. Depending on the type of the token, the computer
A computer is a machine that can be programmed to Execution (computing), carry out sequences of arithmetic or logical operations (computation) automatically. Modern digital electronic computers can perform generic sets of operations known as C ...
OS will then either read the key from the token and perform a cryptographic operation on it, or ask the token's firmware to perform this operation.
A related application is the hardware dongle
A dongle is a small piece of computer hardware that connects to a port on another device to provide it with additional functionality, or enable a pass-through to such a device that adds functionality.
In computing, the term was initially synonym ...
required by some computer programs to prove ownership of the software
Software is a set of computer programs and associated documentation and data. This is in contrast to hardware, from which the system is built and which actually performs the work.
At the lowest programming level, executable code consists ...
. The dongle is placed in an input device
In computing, an input device is a piece of equipment used to provide data and control signals to an information processing system, such as a computer or information appliance. Examples of input devices include keyboards, mouse, scanners, cameras ...
and the software
Software is a set of computer programs and associated documentation and data. This is in contrast to hardware, from which the system is built and which actually performs the work.
At the lowest programming level, executable code consists ...
accesses the I/O device in question to authorize
Authorization or authorisation (see spelling differences) is the function of specifying access rights/privileges to resources, which is related to general information security and computer security, and to access control in particular. More fo ...
the use of the software
Software is a set of computer programs and associated documentation and data. This is in contrast to hardware, from which the system is built and which actually performs the work.
At the lowest programming level, executable code consists ...
in question.
Commercial solutions are provided by a variety of vendors, each with their own proprietary (and often patented) implementation of variously used security features. Token designs meeting certain security standards are certified in the United States
The United States of America (U.S.A. or USA), commonly known as the United States (U.S. or US) or America, is a country primarily located in North America. It consists of 50 states, a federal district, five major unincorporated territorie ...
as compliant with FIPS 140
The 140 series of Federal Information Processing Standards ( FIPS) are U.S. government computer security standards that specify requirements for cryptography modules.
, FIPS 140-2 and FIPS 140-3 are both accepted as current and active. FIPS 140-3 ...
, a federal security standard. Tokens without any kind of certification are sometimes viewed as suspect, as they often do not meet accepted government or industry security standards, have not been put through rigorous testing, and likely cannot provide the same level of cryptographic security as token solutions which have had their designs independently audited by third-party agencies.
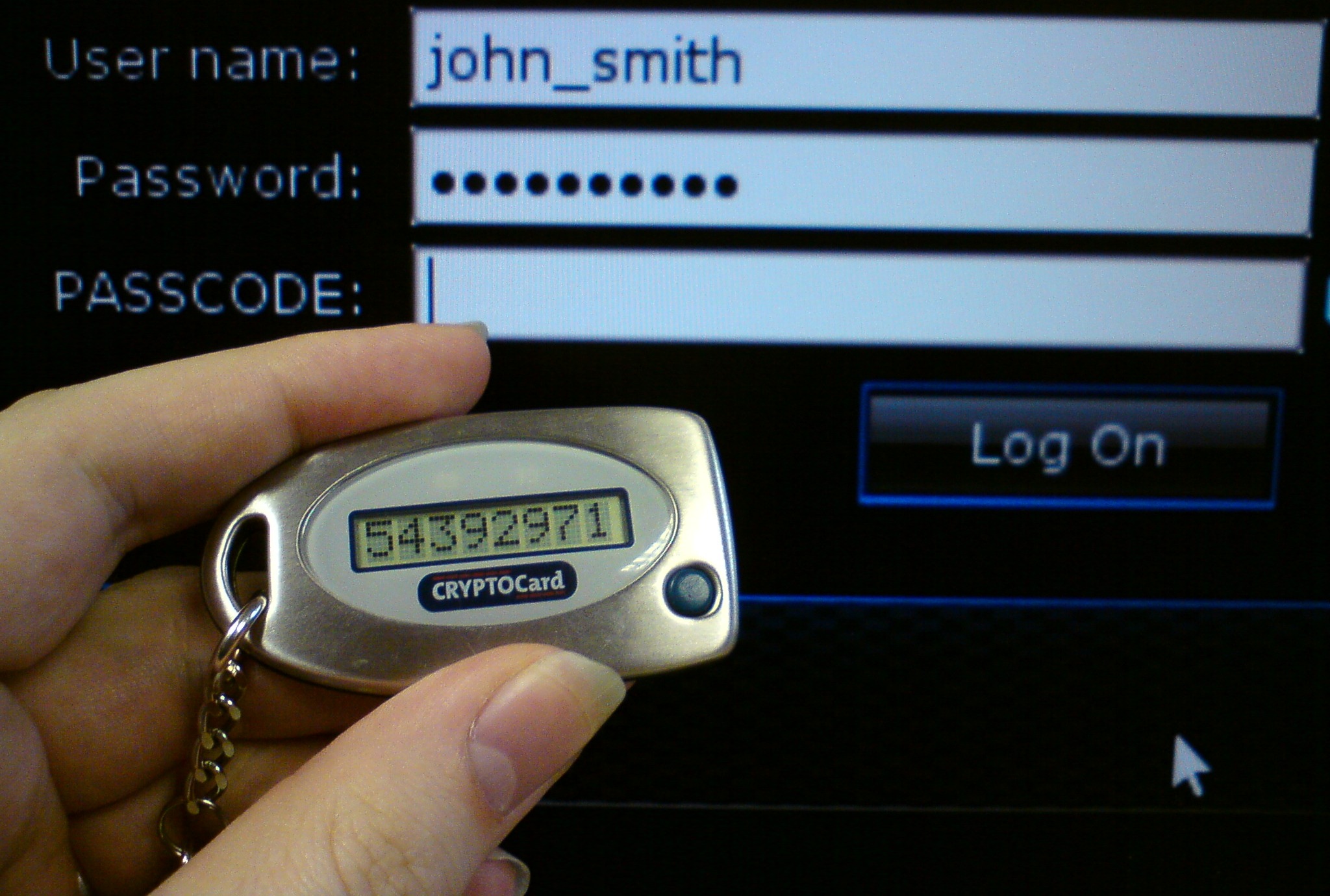
Disconnected tokens
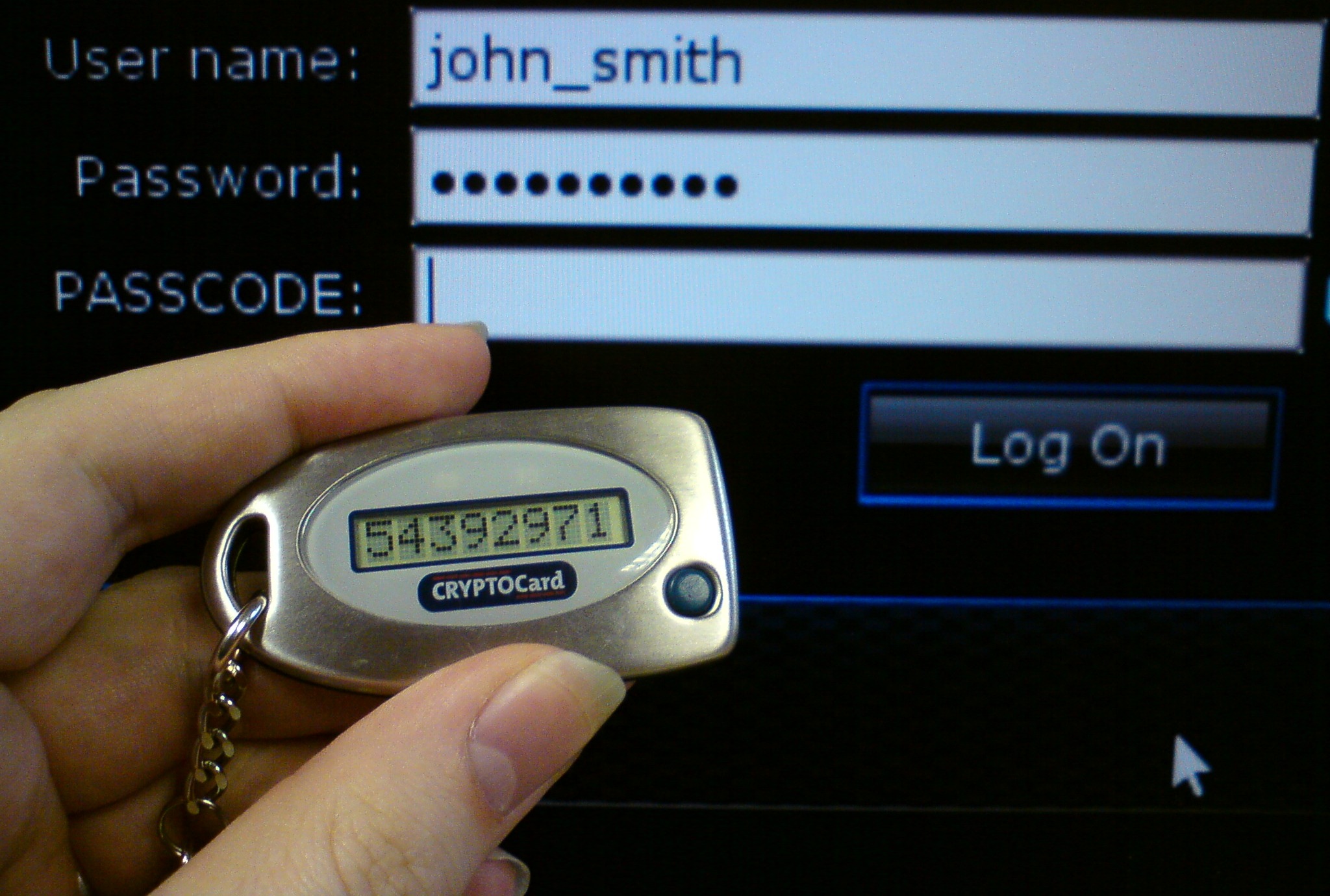 Disconnected tokens have neither a physical nor logical connection to the client computer. They typically do not require a special input device, and instead use a built-in screen to display the generated authentication data, which the user enters manually themselves via a
Disconnected tokens have neither a physical nor logical connection to the client computer. They typically do not require a special input device, and instead use a built-in screen to display the generated authentication data, which the user enters manually themselves via a keyboard
Keyboard may refer to:
Text input
* Keyboard, part of a typewriter
* Computer keyboard
** Keyboard layout, the software control of computer keyboards and their mapping
** Keyboard technology, computer keyboard hardware and firmware
Music
* Musi ...
or keypad
A keypad is a block or pad of buttons set with an arrangement of digits, symbols, or alphabetical letters. Pads mostly containing numbers and used with computers are numeric keypads. Keypads are found on devices which require mainly numeric in ...
. Disconnected tokens are the most common type of security token used (usually in combination with a password) in two-factor authentication for online identification.
Connected tokens
Connected tokens are tokens that must be physically connected to the computer with which the user is authenticating. Tokens in this category automatically transmit the authentication information to the client computer once a physical connection is made, eliminating the need for the user to manually enter the authentication information. However, in order to use a connected token, the appropriate input device must be installed. The most common types of physical tokens aresmart card
A smart card, chip card, or integrated circuit card (ICC or IC card) is a physical electronic authentication device, used to control access to a resource. It is typically a plastic credit card-sized card with an embedded integrated circuit (IC) c ...
s and USB tokens (also called ''security keys''), which require a smart card reader and a USB port respectively. Increasingly, FIDO2
The FIDO2 Project is a joint effort between the FIDO Alliance and the World Wide Web Consortium (W3C) whose goal is to create strong authentication for the web. At its core, FIDO2 consists of the W3C Web Authentication (WebAuthn) standard and th ...
tokens, supported by the open specification group FIDO Alliance
The FIDO ("Fast IDentity Online") Alliance is an open industry association launched in February 2013 whose stated mission is to develop and promote authentication standards that "help reduce the world’s over-reliance on passwords". FIDO addres ...
have become popular for consumers with mainstream browser support beginning in 2015 and supported by popular websites and social media sites.
Older PC card
In computing, PC Card is a configuration for computer parallel communication peripheral interface, designed for laptop computers. Originally introduced as PCMCIA, the PC Card standard as well as its successors like CardBus were defined and devel ...
tokens are made to work primarily with laptop
A laptop, laptop computer, or notebook computer is a small, portable personal computer (PC) with a screen and alphanumeric keyboard. Laptops typically have a clam shell form factor with the screen mounted on the inside of the upper li ...
s. Type II PC Cards are preferred as a token as they are half as thick as Type III.
The audio jack port is a relatively practical method to establish connection between mobile devices, such as iPhone, iPad
The iPad is a brand of iOS and iPadOS-based tablet computers that are developed by Apple Inc. The iPad was conceived before the related iPhone but the iPhone was developed and released first. Speculation about the development, operating s ...
and Android, and other accessories. The most well known device is called Square
In Euclidean geometry, a square is a regular quadrilateral, which means that it has four equal sides and four equal angles (90-degree angles, π/2 radian angles, or right angles). It can also be defined as a rectangle with two equal-length adj ...
, a credit card reader for iOS
iOS (formerly iPhone OS) is a mobile operating system created and developed by Apple Inc. exclusively for its hardware. It is the operating system that powers many of the company's mobile devices, including the iPhone; the term also includes ...
and Android devices.
Some use a special purpose interface (e.g. the crypto ignition key
The KSD-64 Crypto Ignition Key (CIK) is an NSA-developed EEPROM chip packed in a plastic case that looks like a toy key. The model number is due to its storage capacity — 64 kibibits (65,536bits, or 8KiB), enough to store multiple en ...
deployed by the United States National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collecti ...
). Tokens can also be used as a photo ID card. Cell phones
A mobile phone, cellular phone, cell phone, cellphone, handphone, hand phone or pocket phone, sometimes shortened to simply mobile, cell, or just phone, is a portable telephone that can make and receive calls over a radio frequency link whil ...
and PDAs can also serve as security tokens with proper programming.
Smart cards
Many connected tokens use smart card technology. Smart cards can be very cheap (around ten cents) and contain proven security mechanisms (as used by financial institutions, like cash cards). However, computational performance of smart cards is often rather limited because of extreme low power consumption and ultra-thin form-factor requirements. Smart-card-basedUSB
Universal Serial Bus (USB) is an industry standard that establishes specifications for cables, connectors and protocols for connection, communication and power supply (interfacing) between computers, peripherals and other computers. A broad v ...
tokens which contain a smart card
A smart card, chip card, or integrated circuit card (ICC or IC card) is a physical electronic authentication device, used to control access to a resource. It is typically a plastic credit card-sized card with an embedded integrated circuit (IC) c ...
chip inside provide the functionality of both USB tokens and smart cards. They enable a broad range of security solutions and provide the abilities and security of a traditional smart card without requiring a unique input device. From the computer operating system
An operating system (OS) is system software that manages computer hardware, software resources, and provides common services for computer programs.
Time-sharing operating systems schedule tasks for efficient use of the system and may also inc ...
's point of view such a token is a USB-connected smart card reader with one non-removable smart card present.Specification for Integrated Circuit(s) Cards Interface Devices, usb.org
Contactless tokens
Unlike connected tokens, contactless tokens form a logical connection to the client computer but do not require a physical connection. The absence of the need for physical contact makes them more convenient than both connected and disconnected tokens. As a result, contactless tokens are a popular choice forkeyless entry
A remote keyless system (RKS), also known as keyless entry or remote central locking, is an electronic lock that controls access to a building or vehicle by using an electronic remote control (activated by a handheld device or automatically by ...
systems and electronic payment solutions such as Mobil
Mobil is a petroleum brand owned and operated by American oil and gas corporation ExxonMobil. The brand was formerly owned and operated by an oil and gas corporation of the same name, which itself merged with Exxon to form ExxonMobil in 1999.
...
Speedpass
Speedpass was a keychain radio-frequency identification (RFID) device introduced in 1997 by Mobil (which later merged with Exxon to become ExxonMobil in 1999) for electronic payment. It was originally developed by Verifone. By 2004, more than ...
, which uses RFID
Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of a tiny radio transponder, a radio receiver and transmitter. When triggered by an electromag ...
to transmit authentication info from a keychain token. However, there have been various security concerns raised about RFID tokens after researchers at Johns Hopkins University
Johns Hopkins University (Johns Hopkins, Hopkins, or JHU) is a private university, private research university in Baltimore, Maryland. Founded in 1876, Johns Hopkins is the oldest research university in the United States and in the western hem ...
and RSA Laboratories
RSA Security LLC, formerly RSA Security, Inc. and doing business as RSA, is an American computer and network security company with a focus on encryption and encryption standards. RSA was named after the initials of its co-founders, Ron Rivest, ...
discovered that RFID tags could be easily cracked and cloned.
Another downside is that contactless tokens have relatively short battery lives; usually only 5–6 years, which is low compared to USB
Universal Serial Bus (USB) is an industry standard that establishes specifications for cables, connectors and protocols for connection, communication and power supply (interfacing) between computers, peripherals and other computers. A broad v ...
tokens which may last more than 10 years. Some tokens however do allow the batteries to be changed, thus reducing costs.
Bluetooth tokens
TheBluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is limi ...
Low Energy protocols serve for long lasting battery lifecycle of wireless transmission.
* The transmission of inherent Bluetooth identity data is the lowest quality for supporting authentication.
* A bidirectional connection for transactional data interchange serves for the most sophisticated authentication procedures.
However, the automatic transmission power control antagonizes to attempts for radial distance estimates. The escape is available apart from the standardised Bluetooth power control algorithm to provide a calibration on minimally required transmission power.
Bluetooth tokens are often combined with a USB token, thus working in both a connected and a disconnected state. Bluetooth authentication works when closer than 32 feet (10 meters). When the Bluetooth link is not properly operable, the token may be inserted into a USB
Universal Serial Bus (USB) is an industry standard that establishes specifications for cables, connectors and protocols for connection, communication and power supply (interfacing) between computers, peripherals and other computers. A broad v ...
input device
In computing, an input device is a piece of equipment used to provide data and control signals to an information processing system, such as a computer or information appliance. Examples of input devices include keyboards, mouse, scanners, cameras ...
to function.
Another combination is with smart card
A smart card, chip card, or integrated circuit card (ICC or IC card) is a physical electronic authentication device, used to control access to a resource. It is typically a plastic credit card-sized card with an embedded integrated circuit (IC) c ...
to store locally larger amounts of identity data and process information as well. Another is a contactless BLE token that combines secure storage and tokenized release of fingerprint credentials.
In the USB mode of operation sign-off requires care for the token while mechanically coupled to the USB plug. The advantage with the Bluetooth mode of operation is the option of combining sign-off with distance metrics. Respective products are in preparation, following the concepts of electronic leash.
NFC tokens
Near-field communication
Near-field communication (NFC) is a set of communication protocols that enables communication between two electronic devices over a distance of 4 cm (1 in) or less. NFC offers a low-speed connection through a simple setup that can be u ...
(NFC) tokens combined with a Bluetooth token may operate in several modes, thus working in both a connected and a disconnected state. NFC authentication works when closer than 1 foot (0.3 meters). The NFC protocol bridges short distances to the reader while the Bluetooth connection serves for data provision with the token to enable authentication. Also when the Bluetooth link is not connected, the token may serve the locally stored authentication information in coarse positioning to the NFC reader and relieves from exact positioning to a connector.
Single sign-on software tokens
Some types ofsingle sign-on
Single sign-on (SSO) is an authentication scheme that allows a user to log in with a single ID to any of several related, yet independent, software systems.
True single sign-on allows the user to log in once and access services without re-enterin ...
(SSO) solutions, like enterprise single sign-on, use the token to store software that allows for seamless authentication and password filling. As the passwords are stored on the token, users need not remember their passwords and therefore can select more secure passwords, or have more secure passwords assigned. Usually most tokens store a cryptographic hash of the password so that if the token is compromised, the password is still protected.
Programmable tokens
Programmable tokens are marketed as "drop-in" replacement of mobile applications such asGoogle Authenticator
Google Authenticator is a software-based authenticator by Google that implements two-step verification services using the Time-based One-time Password Algorithm (TOTP; specified in RFC 6238) and HMAC-based One-time Password algorithm (HOTP; spec ...
(miniOTP). They can be used as mobile app replacement, as well as in parallel as a backup.
Vulnerabilities
Loss and theft
The simplest vulnerability with any password container is theft or loss of the device. The chances of this happening, or happening unawares, can be reduced with physical security measures such as locks, electronic leash, or body sensor and alarm. Stolen tokens can be made useless by usingtwo factor authentication
Multi-factor authentication (MFA; encompassing two-factor authentication, or 2FA, along with similar terms) is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting ...
. Commonly, in order to authenticate, a personal identification number
A personal identification number (PIN), or sometimes redundantly a PIN number or PIN code, is a numeric (sometimes alpha-numeric) passcode used in the process of authenticating a user accessing a system.
The PIN has been the key to facilitat ...
(PIN) must be entered along with the information provided by the token the same time as the output of the token.
Attacking
Any system which allows users to authenticate via an untrusted network (such asthe Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a '' network of networks'' that consists of private, pub ...
) is vulnerable to man-in-the-middle attacks
In cryptography and computer security, a man-in-the-middle, monster-in-the-middle, machine-in-the-middle, monkey-in-the-middle, meddler-in-the-middle, manipulator-in-the-middle (MITM), person-in-the-middle (PITM) or adversary-in-the-middle (AiTM) ...
. In this type of attack, an attacker acts as the "go-between" of the user and the legitimate system, soliciting the token output from the legitimate user and then supplying it to the authentication system themselves. Since the token value is mathematically correct, the authentication succeeds and the fraudster is granted access. In 2006, Citibank
Citibank, N. A. (N. A. stands for " National Association") is the primary U.S. banking subsidiary of financial services multinational Citigroup. Citibank was founded in 1812 as the City Bank of New York, and later became First National City ...
was the victim of an attack when its hardware-token-equipped business users became the victims of a large Ukrainian-based man-in-the-middle phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious softwar ...
operation.
Breach of codes
In 2012, the Prosecco research team at INRIA Paris-Rocquencourt developed an efficient method of extracting the secret key from several PKCS #11 cryptographic devices, including theSecurID
RSA SecurID, formerly referred to as SecurID, is a mechanism developed by RSA for performing two-factor authentication for a user to a network resource.
Description
The RSA SecurID authentication mechanism consists of a " token"—either ...
800. These findings were documented in INRIA Technical Report RR-7944, ID hal-00691958, and published at CRYPTO 2012.
Digital signature
Trusted as a regular hand-written signature, the digital signature must be made with a private key known only to the person authorized to make the signature. Tokens that allow secure on-board generation and storage of private keys enable secure digital signatures, and can also be used for user authentication, as the private key also serves as a proof of the user’s identity. For tokens to identify the user, all tokens must have some kind of number that is unique. Not all approaches fully qualify asdigital signature
A digital signature is a mathematical scheme for verifying the authenticity of digital messages or documents. A valid digital signature, where the prerequisites are satisfied, gives a recipient very high confidence that the message was created b ...
s according to some national laws. Tokens with no on-board keyboard or another user interface
In the industrial design field of human–computer interaction, a user interface (UI) is the space where interactions between humans and machines occur. The goal of this interaction is to allow effective operation and control of the machine f ...
cannot be used in some signing scenarios, such as confirming a bank transaction based on the bank account number that the funds are to be transferred to.
See also
*Authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an assertion, such as the identity of a computer system user. In contrast with identification, the act of indicati ...
* Authenticator
An authenticator is a means used to confirm a user's identity, that is, to perform digital authentication. A person authenticates to a computer system or application by demonstrating that he or she has possession and control of an authenticator. I ...
* Hardware security module
A hardware security module (HSM) is a physical computing device that safeguards and manages secrets (most importantly digital keys), performs encryption and decryption functions for digital signatures, strong authentication and other cryptograp ...
* Identity management
* Initiative For Open Authentication
Initiative for Open Authentication (OATH) is an industry-wide collaboration to develop an open reference architecture using open standards to promote the adoption of strong authentication. It has close to thirty coordinating and contributing mem ...
* Mobile signature
* Multi-factor authentication
Multi-factor authentication (MFA; encompassing two-factor authentication, or 2FA, along with similar terms) is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting ...
* Mutual authentication
Mutual authentication or two-way authentication (not to be confused with two-factor authentication) refers to two parties authenticating each other at the same time in an authentication protocol. It is a default mode of authentication in some proto ...
* One-time pad
In cryptography, the one-time pad (OTP) is an encryption technique that cannot be cracked, but requires the use of a single-use pre-shared key that is not smaller than the message being sent. In this technique, a plaintext is paired with a ran ...
* Single sign-on
Single sign-on (SSO) is an authentication scheme that allows a user to log in with a single ID to any of several related, yet independent, software systems.
True single sign-on allows the user to log in once and access services without re-enterin ...
* Software token A software token (a.k.a. ''soft token'') is a piece of a two-factor authentication security device that may be used to authorize the use of computer services. Software tokens are stored on a general-purpose electronic device such as a desktop comput ...
References
;General referencesUS Personal Identity Verification (PIV)
External links
*OATH Initiative for open authentication
{{DEFAULTSORT:Security Token Computer access control Authentication methods