|
FIPS 140
The 140 series of Federal Information Processing Standards ( FIPS) are U.S. government computer security standards that specify requirements for cryptography modules. , FIPS 140-2 and FIPS 140-3 are both accepted as current and active. FIPS 140-3 was approved on March 22, 2019 as the successor to FIPS 140-2 and became effective on September 22, 2019. FIPS 140-3 testing began on September 22, 2020, although no FIPS 140-3 validation certificates have been issued yet. FIPS 140-2 testing is still available until September 21, 2021 (later changed for applications already in progress to April 1, 2022), creating an overlapping transition period of one year. FIPS 140-2 test reports that remain in the CMVP queue will still be granted validations after that date, but all FIPS 140-2 validations will be moved to the Historical List on September 21, 2026 regardless of their actual final validation date. Purpose of FIPS 140 The National Institute of Standards and Technology (NIST) issues the 14 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Federal Information Processing Standard
The Federal Information Processing Standards (FIPS) of the United States are a set of publicly announced standards that the National Institute of Standards and Technology (NIST) has developed for use in computer systems of non-military, American government agencies and contractors. FIPS standards establish requirements for ensuring computer security and interoperability, and are intended for cases in which suitable industry standards do not already exist. Many FIPS specifications are modified versions of standards the technical communities use, such as the American National Standards Institute (ANSI), the Institute of Electrical and Electronics Engineers (IEEE), and the International Organization for Standardization (ISO). Specific areas of FIPS standardization The U.S. government has developed various FIPS specifications to standardize a number of topics including: * Codes, e.g., FIPS county codes or codes to indicate weather conditions or emergency indications. In 1994, Nat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Electromagnetic Interference
Electromagnetic interference (EMI), also called radio-frequency interference (RFI) when in the radio frequency spectrum, is a disturbance generated by an external source that affects an electrical circuit by electromagnetic induction, electrostatic coupling, or conduction. The disturbance may degrade the performance of the circuit or even stop it from functioning. In the case of a data path, these effects can range from an increase in error rate to a total loss of the data. Both man-made and natural sources generate changing electrical currents and voltages that can cause EMI: ignition systems, cellular network of mobile phones, lightning, solar flares, and auroras (northern/southern lights). EMI frequently affects AM radios. It can also affect mobile phones, FM radios, and televisions, as well as observations for radio astronomy and atmospheric science. EMI can be used intentionally for radio jamming, as in electronic warfare. History Since the earliest days of ra ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Security Standards
A computer is a machine that can be programmed to carry out sequences of arithmetic or logical operations (computation) automatically. Modern digital electronic computers can perform generic sets of operations known as programs. These programs enable computers to perform a wide range of tasks. A computer system is a nominally complete computer that includes the hardware, operating system (main software), and peripheral equipment needed and used for full operation. This term may also refer to a group of computers that are linked and function together, such as a computer network or computer cluster. A broad range of industrial and consumer products use computers as control systems. Simple special-purpose devices like microwave ovens and remote controls are included, as are factory devices like industrial robots and computer-aided design, as well as general-purpose devices like personal computers and mobile devices like smartphones. Computers power the Internet, which links bill ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
:Category: Cryptography Standards
{{Cat main, Cryptography standards Standards Standard may refer to: Symbols * Colours, standards and guidons, kinds of military signs * Standard (emblem), a type of a large symbol or emblem used for identification Norms, conventions or requirements * Standard (metrology), an object th ... Standards by type ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
:Category: Computer Security Standards
Security standards Standards Standard may refer to: Symbols * Colours, standards and guidons, kinds of military signs * Standard (emblem), a type of a large symbol or emblem used for identification Norms, conventions or requirements * Standard (metrology), an object th ... Information assurance standards ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Common Criteria
The Common Criteria for Information Technology Security Evaluation (referred to as Common Criteria or CC) is an international standard (ISO/IEC 15408) for computer security certification. It is currently in version 3.1 revision 5. Common Criteria is a framework in which computer system users can ''specify'' their security ''functional'' and ''assurance'' requirements (SFRs and SARs respectively) in a Security Target (ST), and may be taken from Protection Profiles (PPs). Vendors can then ''implement '' or make claims about the security attributes of their products, and testing laboratories can ''evaluate'' the products to determine if they actually meet the claims. In other words, Common Criteria provides assurance that the process of specification, implementation and evaluation of a computer security product has been conducted in a rigorous and standard and repeatable manner at a level that is commensurate with the target environment for use. Common Criteria maintains a list of ce ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Differential Power Analysis
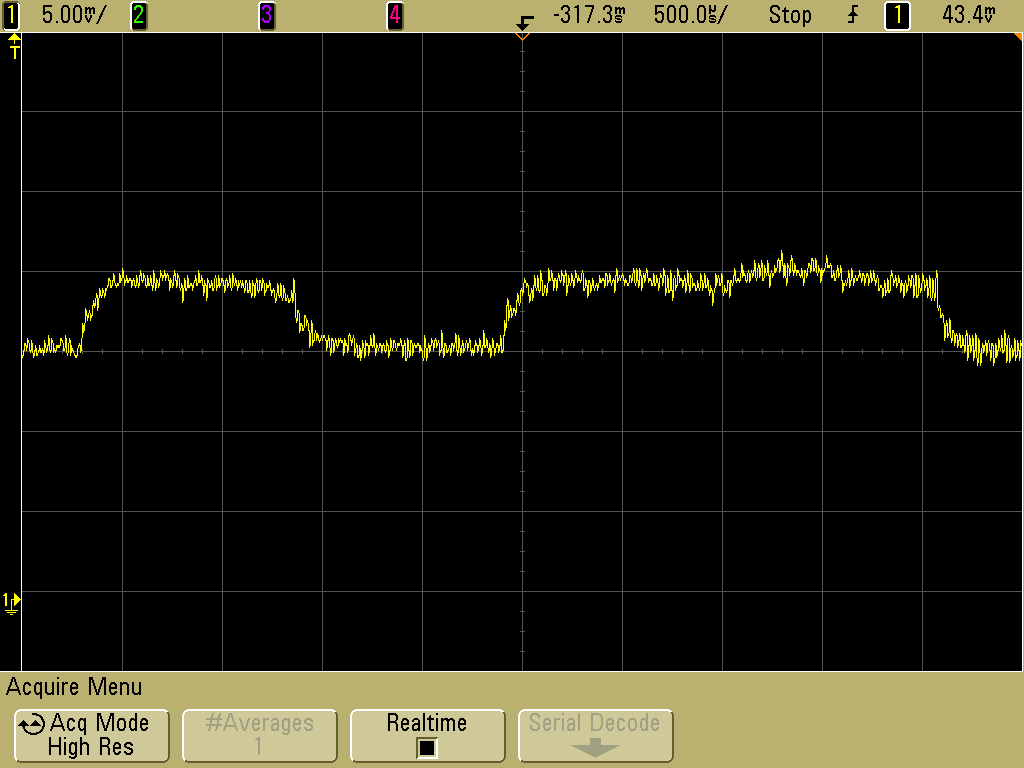
Power analysis is a form of side channel attack in which the attacker studies the power consumption of a cryptographic hardware device. These attacks rely on basic physical properties of the device: semiconductor devices are governed by the laws of physics, which dictate that changes in voltages within the device require very small movements of electric charges (currents). By measuring those currents, it is possible to learn a small amount of information about the data being manipulated. Simple power analysis (SPA) involves visually interpreting power ''traces'', or graphs of electrical activity over time. Differential power analysis (DPA) is a more advanced form of power analysis, which can allow an attacker to compute the intermediate values within cryptographic computations through statistical analysis of data collected from multiple cryptographic operations. SPA and DPA were introduced to the open cryptography community in 1998 by Paul Kocher, Joshua Jaffe and Benjamin ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Simple Power Analysis
Power analysis is a form of side channel attack in which the attacker studies the power consumption of a cryptographic hardware device. These attacks rely on basic physical properties of the device: semiconductor devices are governed by the laws of physics, which dictate that changes in voltages within the device require very small movements of electric charges (currents). By measuring those currents, it is possible to learn a small amount of information about the data being manipulated. Simple power analysis (SPA) involves visually interpreting power ''traces'', or graphs of electrical activity over time. Differential power analysis (DPA) is a more advanced form of power analysis, which can allow an attacker to compute the intermediate values within cryptographic computations through statistical analysis of data collected from multiple cryptographic operations. SPA and DPA were introduced to the open cryptography community in 1998 by Paul Kocher, Joshua Jaffe and Benjami ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ISO/IEC 19790
ISO/IEC JTC 1, entitled "Information technology", is a joint technical committee (JTC) of the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC). Its purpose is to develop, maintain and promote standards in the fields of information and communications technology (ICT). JTC 1 has been responsible for many critical IT standards, ranging from the Joint Photographic Experts Group (JPEG) image formats and Moving Picture Experts Group (MPEG) audio and video formats to the C and C++ programming languages. History ISO/IEC JTC 1 was formed in 1987 as a merger between ISO/TC 97 (Information Technology) and IEC/TC 83, with IEC/SC 47B joining later. The intent was to bring together, in a single committee, the IT standardization activities of the two parent organizations in order to avoid duplicative or possibly incompatible standards. At the time of its formation, the mandate of JTC 1 was to develop base standards in information t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
International Electrotechnical Commission
The International Electrotechnical Commission (IEC; in French: ''Commission électrotechnique internationale'') is an international standards organization that prepares and publishes international standards for all electrical, electronic and related technologies – collectively known as "electrotechnology". IEC standards cover a vast range of technologies from power generation, transmission and distribution to home appliances and office equipment, semiconductors, fibre optics, batteries, solar energy, nanotechnology and marine energy as well as many others. The IEC also manages four global conformity assessment systems that certify whether equipment, system or components conform to its international standards. All electrotechnologies are covered by IEC Standards, including energy production and distribution, electronics, magnetics and electromagnetics, electroacoustics, multimedia, telecommunication and medical technology, as well as associated general disciplines such as t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
International Organization For Standardization
The International Organization for Standardization (ISO ) is an international standard development organization composed of representatives from the national standards organizations of member countries. Membership requirements are given in Article 3 of the ISO Statutes. ISO was founded on 23 February 1947, and (as of November 2022) it has published over 24,500 international standards covering almost all aspects of technology and manufacturing. It has 809 Technical committees and sub committees to take care of standards development. The organization develops and publishes standardization in all technical and nontechnical fields other than electrical and electronic engineering, which is handled by the IEC.Editors of Encyclopedia Britannica. 3 June 2021.International Organization for Standardization" ''Encyclopedia Britannica''. Retrieved 2022-04-26. It is headquartered in Geneva, Switzerland, and works in 167 countries . The three official languages of the ISO are English, Fren ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
TEMPEST
Tempest is a synonym for a storm. '' The Tempest'' is a play by William Shakespeare. Tempest or The Tempest may also refer to: Arts and entertainment Films * ''The Tempest'' (1908 film), a British silent film * ''The Tempest'' (1911 film), an American silent film * ''Tempest'' (1928 film), a John Barrymore film * ''The Tempest'' (1935 film), a Chinese film of the 1930s * ''Tempest'' (1958 film), an Alberto Lattuada film * ''The Tempest'' (1960 film), an American television film * ''The Tempest'' (1963 film), an Australian television film * ''The Tempest'' (1979 film), a film by Derek Jarman * ''Tempest'' (1982 film), a Paul Mazursky film * ''The Tempest'' (2010 film), a Julie Taymor film * ''Tempest'' (2015 film), an animated short film * ''The Tempest'', a 1980 instalment of ''BBC Television Shakespeare'' directed by John Gorrie * ''The Tempest'', a 1998 made-for-TV film by Jack Bender * ''Tempest'', a 2012 film by Rob Curry and Anthony Fletcher Literature * ''Tem ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |