A computer network is a set of
computers sharing resources located on or provided by
network nodes. The computers use common
communication protocols over
digital interconnections to communicate with each other. These interconnections are made up of
telecommunication network
A telecommunications network is a group of nodes interconnected by telecommunications links that are used to exchange messages between the nodes. The links may use a variety of technologies based on the methodologies of circuit switching, mes ...
technologies, based on physically wired, optical, and wireless radio-frequency methods that may be arranged in a variety of
network topologies.
The nodes of a computer network can include
personal computer
A personal computer (PC) is a multi-purpose microcomputer whose size, capabilities, and price make it feasible for individual use. Personal computers are intended to be operated directly by an end user, rather than by a computer expert or tech ...
s,
servers,
networking hardware
Networking hardware, also known as network equipment or computer networking devices, are electronic devices which are required for communication and interaction between devices on a computer network. Specifically, they mediate data transmission in ...
, or other specialised or general-purpose
hosts. They are identified by
network addresses, and may have
hostname
In computer networking, a hostname (archaically nodename) is a label that is assigned to a device connected to a computer network and that is used to identify the device in various forms of electronic communication, such as the World Wide Web. Hos ...
s. Hostnames serve as memorable labels for the nodes, rarely changed after initial assignment. Network addresses serve for locating and identifying the nodes by communication protocols such as the
Internet Protocol
The Internet Protocol (IP) is the network layer communications protocol in the Internet protocol suite for relaying datagrams across network boundaries. Its routing function enables internetworking, and essentially establishes the Internet.
...
.
Computer networks may be classified by many criteria, including the
transmission medium used to carry signals,
bandwidth, communications protocols to organize network traffic, the network size, the topology,
traffic control mechanism, and organizational intent.
Computer networks support many
applications and
services, such as access to the
World Wide Web
The World Wide Web (WWW), commonly known as the Web, is an information system enabling documents and other web resources to be accessed over the Internet.
Documents and downloadable media are made available to the network through web se ...
,
digital video,
digital audio, shared use of
application and storage servers, printers, and fax machines, and use of email and instant messaging applications.
History
Computer networking may be considered a branch of
computer science
Computer science is the study of computation, automation, and information. Computer science spans theoretical disciplines (such as algorithms, theory of computation, information theory, and automation) to practical disciplines (includin ...
,
computer engineering
Computer engineering (CoE or CpE) is a branch of electrical engineering and computer science that integrates several fields of computer science and electronic engineering required to develop computer hardware and software. Computer enginee ...
, and
telecommunications
Telecommunication is the transmission of information by various types of technologies over wire, radio, optical, or other electromagnetic systems. It has its origin in the desire of humans for communication over a distance greater than tha ...
, since it relies on the theoretical and practical application of the related disciplines. Computer networking was influenced by a wide array of technology developments and historical milestones.
* In the late 1950s, a network of computers was built for the U.S. military
Semi-Automatic Ground Environment
The Semi-Automatic Ground Environment (SAGE) was a system of large computers and associated networking equipment that coordinated data from many radar sites and processed it to produce a single unified image of the airspace over a wide area. SA ...
(SAGE)
radar
Radar is a detection system that uses radio waves to determine the distance ('' ranging''), angle, and radial velocity of objects relative to the site. It can be used to detect aircraft, ships, spacecraft, guided missiles, motor vehicles, w ...
system using the
Bell 101 modem The Bell 101 dataset or Bell 101 modem was the first commercial modem for computers, released by AT&T Corporation in 1958 for use by SAGE and in 1959 made commercial shortly after AT&T's Bell Labs announced their 110 baud modulation frequencies. T ...
. It was the first commercial
modem
A modulator-demodulator or modem is a computer hardware device that converts data from a digital format into a format suitable for an analog transmission medium such as telephone or radio. A modem transmits data by modulating one or more c ...
for computers, released by
AT&T Corporation
AT&T Corporation, originally the American Telephone and Telegraph Company, is the subsidiary of AT&T Inc. that provides voice, video, data, and Internet telecommunications and professional services to businesses, consumers, and government agen ...
in 1958. The modem allowed
digital data
Digital data, in information theory and information systems, is information represented as a string of discrete symbols each of which can take on one of only a finite number of values from some alphabet, such as letters or digits. An example is ...
to be transmitted over regular unconditioned telephone lines at a speed of 110 bits per second (bit/s).
* In 1959,
Christopher Strachey filed a patent application for
time-sharing and
John McCarthy initiated the first project to implement time-sharing of user programs at MIT.
Stratchey passed the concept on to
J. C. R. Licklider at the inaugural
UNESCO Information Processing Conference in Paris that year. McCarthy was instrumental in the creation of three of the earliest time-sharing systems (Compatible Time-Sharing System in 1961, BBN Time-Sharing System in 1962, and Dartmouth Time Sharing System in 1963).
* In 1959,
Anatoly Kitov proposed to the Central Committee of the Communist Party of the Soviet Union a detailed plan for the re-organisation of the control of the Soviet armed forces and of the Soviet economy on the basis of a network of computing centres. Kitov's proposal was rejected, as later was the 1962
OGAS economy management network project.
* In 1960, the commercial airline reservation system
semi-automatic business research environment
Sabre Global Distribution System, owned by Sabre Corporation, is a travel reservation system used by travel agents and companies to search, price, book, and ticket travel services provided by airlines, hotels, car rental companies, rail providers ...
(SABRE) went online with two connected
mainframes.
* In 1963, J. C. R. Licklider sent a memorandum to office colleagues discussing the concept of the "
Intergalactic Computer Network
Intergalactic Computer Network or Galactic Network (IGCN) was a computer networking concept similar to today's Internet.
J.C.R. Licklider, the first director of the Information Processing Techniques Office (IPTO) at The Pentagon's ARPA, used th ...
", a computer network intended to allow general communications among computer users.
* Throughout the 1960s,
Paul Baran and
Donald Davies
Donald Watts Davies, (7 June 1924 – 28 May 2000) was a Welsh computer scientist who was employed at the UK National Physical Laboratory (NPL).
In 1965 he conceived of packet switching, which is today the dominant basis for data communic ...
independently developed the concept of
packet switching
In telecommunications, packet switching is a method of grouping Data (computing), data into ''network packet, packets'' that are transmitted over a digital Telecommunications network, network. Packets are made of a header (computing), header and ...
to transfer information between computers over a network. Davies pioneered the implementation of the concept. The
NPL network, a local area network at the
National Physical Laboratory (United Kingdom) used a line speed of 768 kbit/s and later high-speed
T1 links (1.544
Mbit/s line rate).
* In 1965,
Western Electric
The Western Electric Company was an American electrical engineering and manufacturing company officially founded in 1869. A wholly owned subsidiary of American Telephone & Telegraph for most of its lifespan, it served as the primary equipment ma ...
introduced the first widely used
telephone switch that implemented computer control in the switching fabric.
* In 1969, the first four nodes of the
ARPANET
The Advanced Research Projects Agency Network (ARPANET) was the first wide-area packet-switched network with distributed control and one of the first networks to implement the TCP/IP protocol suite. Both technologies became the technical foun ...
were connected using 50 kbit/s circuits between the University of California at Los Angeles, the Stanford Research Institute, the University of California at Santa Barbara, and the University of Utah. In the early 1970s,
Leonard Kleinrock carried out mathematical work to model the performance of packet-switched networks, which underpinned the development of the ARPANET.
His theoretical work on
hierarchical routing in the late 1970s with student
Farouk Kamoun remains critical to the operation of the Internet today.
* In 1972, commercial services were first deployed on
public data networks in Europe, which began using
X.25 in the late 1970s and spread across the globe.
The underlying infrastructure was used for expanding TCP/IP networks in the 1980s.
* In 1973, the French
CYCLADES
The Cyclades (; el, Κυκλάδες, ) are an island group in the Aegean Sea, southeast of mainland Greece and a former administrative prefecture of Greece. They are one of the island groups which constitute the Aegean archipelago. The na ...
network was the first to make the hosts responsible for the reliable delivery of data, rather than this being a centralized service of the network itself.
* In 1973,
Robert Metcalfe wrote a formal memo at
Xerox PARC describing
Ethernet
Ethernet () is a family of wired computer networking technologies commonly used in local area networks (LAN), metropolitan area networks (MAN) and wide area networks (WAN). It was commercially introduced in 1980 and first standardized in ...
, a networking system that was based on the
Aloha network, developed in the 1960s by
Norman Abramson and colleagues at the University of Hawaii. In July 1976, Robert Metcalfe and
David Boggs published their paper "Ethernet: Distributed Packet Switching for Local Computer Networks" and collaborated on several patents received in 1977 and 1978.
* In 1974,
Vint Cerf
Vinton Gray Cerf (; born June 23, 1943) is an American Internet pioneer and is recognized as one of " the fathers of the Internet", sharing this title with TCP/IP co-developer Bob Kahn. He has received honorary degrees and awards that includ ...
,
Yogen Dalal, and Carl Sunshine published the
Transmission Control Protocol
The Transmission Control Protocol (TCP) is one of the main protocols of the Internet protocol suite. It originated in the initial network implementation in which it complemented the Internet Protocol (IP). Therefore, the entire suite is common ...
(TCP) specification, , coining the term
Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a ''internetworking, network of networks'' that consists ...
as a shorthand for
internetworking
Internetworking is the practice of interconnecting multiple computer networks, such that any pair of hosts in the connected networks can exchange messages irrespective of their hardware-level networking technology. The resulting system of interc ...
.
* In 1976, John Murphy of
Datapoint Corporation created
ARCNET, a token-passing network first used to share storage devices.
* In 1977, the first long-distance fiber network was deployed by GTE in Long Beach, California.
* In 1977,
Xerox Network Systems (XNS) was developed by Robert Metcalfe and Yogen Dalal at
Xerox
Xerox Holdings Corporation (; also known simply as Xerox) is an American corporation that sells print and digital document products and services in more than 160 countries. Xerox is headquartered in Norwalk, Connecticut (having moved from St ...
.
* In 1979, Robert Metcalfe pursued making Ethernet an open standard.
* In 1980, Ethernet was upgraded from the original 2.94 Mbit/s protocol to the 10 Mbit/s protocol, which was developed by
Ron Crane Ron Crane may refer to:
* Ron Crane (engineer) (1950–2017), American electrical engineer
* Ron Crane (politician)
Ron Crane is an American politician who served as a member of Idaho House of Representatives from 1982 to 1998 and as the state tr ...
, Bob Garner, Roy Ogus, and Yogen Dalal.
*In 1995, the transmission speed capacity for Ethernet increased from 10 Mbit/s to 100 Mbit/s. By 1998, Ethernet supported transmission speeds of 1 Gbit/s. Subsequently, higher speeds of up to 400 Gbit/s were added (). The scaling of Ethernet has been a contributing factor to its continued use.
Use
A computer network extends interpersonal communications by electronic means with various technologies, such as email, instant messaging, online chat, voice and video telephone calls, and video conferencing. A network allows sharing of network and computing resources. Users may access and use resources provided by devices on the network, such as printing a document on a shared network printer or use of a shared storage device. A network allows sharing of files, data, and other types of information giving authorized users the ability to access information stored on other computers on the network.
Distributed computing
A distributed system is a system whose components are located on different networked computers, which communicate and coordinate their actions by passing messages to one another from any system. Distributed computing is a field of computer sci ...
uses computing resources across a network to accomplish tasks.
Network packet

Most modern computer networks use protocols based on packet-mode transmission. A
network packet
In telecommunications and computer networking, a network packet is a formatted unit of data carried by a packet-switched network. A packet consists of control information and user data; the latter is also known as the '' payload''. Control infor ...
is a formatted unit of
data
In the pursuit of knowledge, data (; ) is a collection of discrete values that convey information, describing quantity, quality, fact, statistics, other basic units of meaning, or simply sequences of symbols that may be further interpret ...
carried by a
packet-switched network.
Packets consist of two types of data: control information and user data (payload). The control information provides data the network needs to deliver the user data, for example, source and destination
network addresses,
error detection codes, and sequencing information. Typically, control information is found in
packet headers and
trailers, with
payload data in between.
With packets, the
bandwidth of the transmission medium can be better shared among users than if the network were
circuit switched. When one user is not sending packets, the link can be filled with packets from other users, and so the cost can be shared, with relatively little interference, provided the link isn't overused. Often the route a packet needs to take through a network is not immediately available. In that case, the packet is
queued and waits until a link is free.
The physical link technologies of packet network typically limit the size of packets to a certain
maximum transmission unit
In computer networking, the maximum transmission unit (MTU) is the size of the largest protocol data unit (PDU) that can be communicated in a single network layer transaction. The MTU relates to, but is not identical to the maximum frame size th ...
(MTU). A longer message may be fragmented before it is transferred and once the packets arrive, they are reassembled to construct the original message.
Network topology

The physical or geographic locations of network nodes and links generally have relatively little effect on a network, but the topology of interconnections of a network can significantly affect its throughput and reliability. With many technologies, such as bus or star networks, a single failure can cause the network to fail entirely. In general, the more interconnections there are, the more robust the network is; but the more expensive it is to install. Therefore, most network diagrams are arranged by their
network topology
Network topology is the arrangement of the elements ( links, nodes, etc.) of a communication network. Network topology can be used to define or describe the arrangement of various types of telecommunication networks, including command and contr ...
which is the map of logical interconnections of network hosts.
Common layouts are:
*
Bus network: all nodes are connected to a common medium along this medium. This was the layout used in the original
Ethernet
Ethernet () is a family of wired computer networking technologies commonly used in local area networks (LAN), metropolitan area networks (MAN) and wide area networks (WAN). It was commercially introduced in 1980 and first standardized in ...
, called
10BASE5 and
10BASE2. This is still a common topology on the
data link layer
The data link layer, or layer 2, is the second layer of the seven-layer OSI model of computer networking. This layer is the protocol layer that transfers data between nodes on a network segment across the physical layer. The data link layer ...
, although modern
physical layer
In the seven-layer OSI model of computer networking, the physical layer or layer 1 is the first and lowest layer; The layer most closely associated with the physical connection between devices. This layer may be implemented by a PHY chip.
Th ...
variants use
point-to-point links instead, forming a star or a tree.
*
Star network: all nodes are connected to a special central node. This is the typical layout found in a small
switched Ethernet LAN, where each client connects to a central network switch, and logically in a
wireless LAN
A wireless LAN (WLAN) is a wireless computer network that links two or more devices using wireless communication to form a local area network (LAN) within a limited area such as a home, school, computer laboratory, campus, or office building ...
, where each wireless client associates with the central
wireless access point.
*
Ring network: each node is connected to its left and right neighbour node, such that all nodes are connected and that each node can reach each other node by traversing nodes left- or rightwards.
Token ring networks, and the
Fiber Distributed Data Interface (FDDI), made use of such a topology.
*
Mesh network: each node is connected to an arbitrary number of neighbours in such a way that there is at least one traversal from any node to any other.
*
Fully connected network: each node is connected to every other node in the network.
*
Tree network: nodes are arranged hierarchically. This is the natural topology for a larger Ethernet network with multiple switches and without redundant meshing.
The physical layout of the nodes in a network may not necessarily reflect the network topology. As an example, with
FDDI
Fiber Distributed Data Interface (FDDI) is a standard for data transmission in a local area network.
It uses optical fiber as its standard underlying physical medium, although it was also later specified to use copper cable, in which case i ...
, the network topology is a ring, but the physical topology is often a star, because all neighboring connections can be routed via a central physical location. Physical layout is not completely irrelevant, however, as common ducting and equipment locations can represent single points of failure due to issues like fires, power failures and flooding.
Overlay network

An
overlay network is a virtual network that is built on top of another network. Nodes in the overlay network are connected by virtual or logical links. Each link corresponds to a path, perhaps through many physical links, in the underlying network. The topology of the overlay network may (and often does) differ from that of the underlying one. For example, many
peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network. They are said to form a peer-to-peer ...
networks are overlay networks. They are organized as nodes of a virtual system of links that run on top of the
Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a ''internetworking, network of networks'' that consists ...
.
Overlay networks have been around since the invention of networking when computer systems were connected over telephone lines using
modem
A modulator-demodulator or modem is a computer hardware device that converts data from a digital format into a format suitable for an analog transmission medium such as telephone or radio. A modem transmits data by modulating one or more c ...
s before any
data network
A computer network is a set of computers sharing resources located on or provided by network nodes. The computers use common communication protocols over digital interconnections to communicate with each other. These interconnections ar ...
existed.
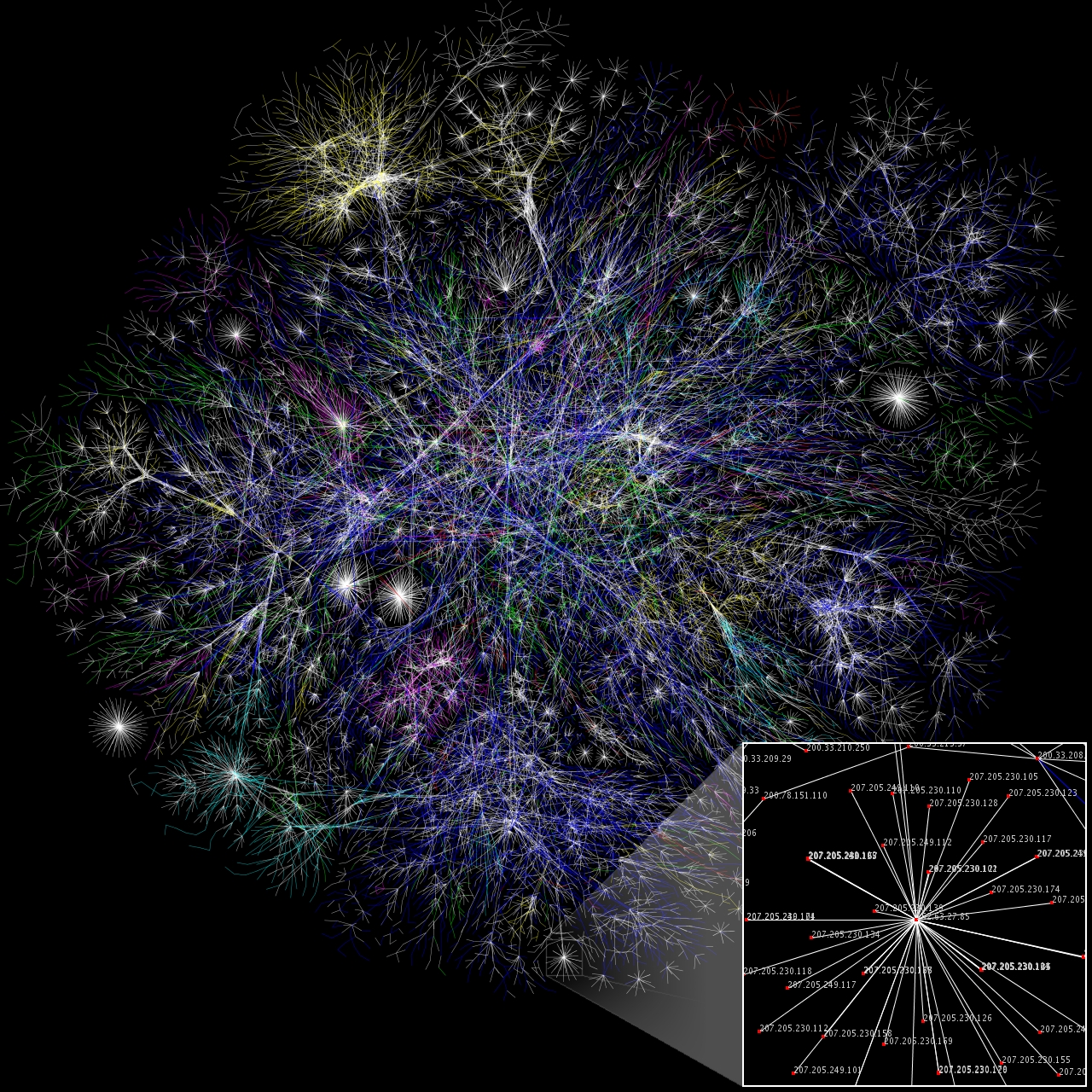
The most striking example of an overlay network is the Internet itself. The Internet itself was initially built as an overlay on the
telephone network.
Even today, each Internet node can communicate with virtually any other through an underlying mesh of sub-networks of wildly different topologies and technologies.
Address resolution and
routing
Routing is the process of selecting a path for traffic in a network or between or across multiple networks. Broadly, routing is performed in many types of networks, including circuit-switched networks, such as the public switched telephone netw ...
are the means that allow mapping of a fully connected IP overlay network to its underlying network.
Another example of an overlay network is a
distributed hash table, which maps keys to nodes in the network. In this case, the underlying network is an IP network, and the overlay network is a table (actually a
map) indexed by keys.
Overlay networks have also been proposed as a way to improve Internet routing, such as through
quality of service guarantees achieve higher-quality
streaming media
Streaming media is multimedia that is delivered and consumed in a continuous manner from a source, with little or no intermediate storage in network elements. ''Streaming'' refers to the delivery method of content, rather than the content i ...
. Previous proposals such as
IntServ In computer networking, integrated services or IntServ is an architecture that specifies the elements to guarantee quality of service (QoS) on networks. IntServ can for example be used to allow video and sound to reach the receiver without interr ...
,
DiffServ
Differentiated services or DiffServ is a computer networking architecture that specifies a mechanism for classifying and managing network traffic and providing quality of service (QoS) on modern IP networks. DiffServ can, for example, be used ...
, and
IP multicast have not seen wide acceptance largely because they require modification of all
routers in the network. On the other hand, an overlay network can be incrementally deployed on end-hosts running the overlay protocol software, without cooperation from
Internet service provider
An Internet service provider (ISP) is an organization that provides services for accessing, using, or participating in the Internet. ISPs can be organized in various forms, such as commercial, community-owned, non-profit, or otherwise privatel ...
s. The overlay network has no control over how packets are routed in the underlying network between two overlay nodes, but it can control, for example, the sequence of overlay nodes that a message traverses before it reaches its destination.
For example,
Akamai Technologies manages an overlay network that provides reliable, efficient content delivery (a kind of
multicast
In computer networking, multicast is group communication where data transmission is addressed to a group of destination computers simultaneously. Multicast can be one-to-many or many-to-many distribution. Multicast should not be confused wit ...
). Academic research includes end system multicast, resilient routing and quality of service studies, among others.
Network links

The transmission media (often referred to in the literature as the ''
physical medium'') used to link devices to form a computer network include
electrical cable
An electrical cable is an assembly of one or more wires running side by side or bundled, which is used to carry electric current.
One or more electrical cables and their corresponding connectors may be formed into a ''cable assembly'', which ...
,
optical fiber
An optical fiber, or optical fibre in Commonwealth English, is a flexible, transparency and translucency, transparent fiber made by Drawing (manufacturing), drawing glass (silica) or plastic to a diameter slightly thicker than that of a Hair ...
, and free space. In the
OSI model, the software to handle the media is defined at layers 1 and 2 — the physical layer and the data link layer.
A widely adopted ''family'' that uses copper and fiber media in
local area network (LAN) technology are collectively known as Ethernet. The media and protocol standards that enable communication between networked devices over Ethernet are defined by
IEEE 802.3
IEEE 802.3 is a working group and a collection standards defining the physical layer and data link layer's media access control (MAC) of wired Ethernet. The standards are produced by the working group of Institute of Electrical and Electronics Eng ...
. Wireless LAN standards use
radio waves
Radio waves are a type of electromagnetic radiation with the longest wavelengths in the electromagnetic spectrum, typically with frequencies of 300 gigahertz ( GHz) and below. At 300 GHz, the corresponding wavelength is 1 mm (s ...
, others use
infrared
Infrared (IR), sometimes called infrared light, is electromagnetic radiation (EMR) with wavelengths longer than those of visible light. It is therefore invisible to the human eye. IR is generally understood to encompass wavelengths from aroun ...
signals as a transmission medium.
Power line communication uses a building's
power cabling to transmit data.
Wired

The following classes of wired technologies are used in computer networking.
*''
Coaxial cable
Coaxial cable, or coax (pronounced ) is a type of electrical cable consisting of an inner conductor surrounded by a concentric conducting shield, with the two separated by a dielectric ( insulating material); many coaxial cables also have a ...
'' is widely used for cable television systems, office buildings, and other work-sites for local area networks. Transmission speed ranges from 200 million bits per second to more than 500 million bits per second.
*
ITU-T
The ITU Telecommunication Standardization Sector (ITU-T) is one of the three sectors (divisions or units) of the International Telecommunication Union (ITU). It is responsible for coordinating standards for telecommunications and Information Commu ...
G.hn technology uses existing
home wiring (
coaxial cable
Coaxial cable, or coax (pronounced ) is a type of electrical cable consisting of an inner conductor surrounded by a concentric conducting shield, with the two separated by a dielectric ( insulating material); many coaxial cables also have a ...
, phone lines and
power lines) to create a high-speed local area network.
*''
Twisted pair
Twisted pair cabling is a type of wiring used for communications in which two conductors of a single circuit are twisted together for the purposes of improving electromagnetic compatibility. Compared to a single conductor or an untwisted ba ...
'' cabling is used for wired
Ethernet
Ethernet () is a family of wired computer networking technologies commonly used in local area networks (LAN), metropolitan area networks (MAN) and wide area networks (WAN). It was commercially introduced in 1980 and first standardized in ...
and other standards. It typically consists of 4 pairs of copper cabling that can be utilized for both voice and data transmission. The use of two wires twisted together helps to reduce
crosstalk
In electronics, crosstalk is any phenomenon by which a signal transmitted on one circuit or channel of a transmission system creates an undesired effect in another circuit or channel. Crosstalk is usually caused by undesired capacitive, in ...
and
electromagnetic induction
Electromagnetic or magnetic induction is the production of an electromotive force (emf) across an electrical conductor in a changing magnetic field.
Michael Faraday is generally credited with the discovery of induction in 1831, and James Cle ...
. The transmission speed ranges from 2 Mbit/s to 10 Gbit/s. Twisted pair cabling comes in two forms: unshielded twisted pair (UTP) and shielded twisted-pair (STP). Each form comes in several
category ratings, designed for use in various scenarios.

*An ''
optical fiber
An optical fiber, or optical fibre in Commonwealth English, is a flexible, transparency and translucency, transparent fiber made by Drawing (manufacturing), drawing glass (silica) or plastic to a diameter slightly thicker than that of a Hair ...
'' is a glass fiber. It carries pulses of light that represent data via lasers and
optical amplifier
An optical amplifier is a device that amplifies an optical signal directly, without the need to first convert it to an electrical signal. An optical amplifier may be thought of as a laser without an optical cavity, or one in which feedback fr ...
s. Some advantages of optical fibers over metal wires are very low transmission loss and immunity to electrical interference. Using dense
wave division multiplexing, optical fibers can simultaneously carry multiple streams of data on different wavelengths of light, which greatly increases the rate that data can be sent to up to trillions of bits per second. Optic fibers can be used for long runs of cable carrying very high data rates, and are used for
undersea communications cables to interconnect continents. There are two basic types of fiber optics,
single-mode optical fiber (SMF) and
multi-mode optical fiber (MMF). Single-mode fiber has the advantage of being able to sustain a coherent signal for dozens or even a hundred kilometers. Multimode fiber is cheaper to terminate but is limited to a few hundred or even only a few dozens of meters, depending on the data rate and cable grade.
Wireless

Network connections can be established wirelessly using radio or other electromagnetic means of communication.
*'' Terrestrial
microwave
Microwave is a form of electromagnetic radiation with wavelengths ranging from about one meter to one millimeter corresponding to frequency, frequencies between 300 MHz and 300 GHz respectively. Different sources define different fre ...
'' – Terrestrial microwave communication uses Earth-based transmitters and receivers resembling satellite dishes. Terrestrial microwaves are in the low gigahertz range, which limits all communications to line-of-sight. Relay stations are spaced approximately apart.
*''
Communications satellite
A communications satellite is an artificial satellite that relays and amplifies radio telecommunication signals via a transponder; it creates a communication channel between a source transmitter and a receiver at different locations on Ear ...
s'' – Satellites also communicate via microwave. The satellites are stationed in space, typically in geosynchronous orbit above the equator. These Earth-orbiting systems are capable of receiving and relaying voice, data, and TV signals.
*''
Cellular network
A cellular network or mobile network is a communication network where the link to and from end nodes is wireless. The network is distributed over land areas called "cells", each served by at least one fixed-location transceiver (typically th ...
s'' use several radio communications technologies. The systems divide the region covered into multiple geographic areas. Each area is served by a low-power
transceiver.
*''Radio and
spread spectrum technologies'' – Wireless LANs use a high-frequency radio technology similar to digital cellular. Wireless LANs use spread spectrum technology to enable communication between multiple devices in a limited area.
IEEE 802.11 defines a common flavor of open-standards wireless radio-wave technology known as
Wi-Fi
Wi-Fi () is a family of wireless network protocols, based on the IEEE 802.11 family of standards, which are commonly used for local area networking of devices and Internet access, allowing nearby digital devices to exchange data by radio w ...
.
*''
Free-space optical communication'' uses visible or invisible light for communications. In most cases,
line-of-sight propagation
Line-of-sight propagation is a characteristic of electromagnetic radiation or acoustic wave propagation which means waves travel in a direct path from the source to the receiver. Electromagnetic transmission includes light emissions travelin ...
is used, which limits the physical positioning of communicating devices.
* Extending the Internet to interplanetary dimensions via radio waves and optical means, the
Interplanetary Internet.
*
IP over Avian Carriers was a humorous April fool's
Request for Comments
A Request for Comments (RFC) is a publication in a series from the principal technical development and standards-setting bodies for the Internet, most prominently the Internet Engineering Task Force (IETF). An RFC is authored by individuals or ...
, issued as . It was implemented in real life in 2001.
The last two cases have a large
round-trip delay time, which gives slow
two-way communication but doesn't prevent sending large amounts of information (they can have high throughput).
Network nodes
Apart from any physical transmission media, networks are built from additional basic system building blocks, such as
network interface controllers (NICs),
repeaters,
hubs,
bridges,
switches
In electrical engineering, a switch is an electrical component that can disconnect or connect the conducting path in an electrical circuit, interrupting the electric current or diverting it from one conductor to another. The most common type ...
,
routers, modems, and
firewalls. Any particular piece of equipment will frequently contain multiple building blocks and so may perform multiple functions.
Network interfaces

A
network interface controller (NIC) is
computer hardware that connects the computer to the
network media and has the ability to process low-level network information. For example, the NIC may have a connector for accepting a cable, or an aerial for wireless transmission and reception, and the associated circuitry.
In Ethernet networks, each network interface controller has a unique
Media Access Control (MAC) address—usually stored in the controller's permanent memory. To avoid address conflicts between network devices, the
Institute of Electrical and Electronics Engineers
The Institute of Electrical and Electronics Engineers (IEEE) is a 501(c)(3) professional association for electronic engineering and electrical engineering (and associated disciplines) with its corporate office in New York City and its operat ...
(IEEE) maintains and administers MAC address uniqueness. The size of an Ethernet MAC address is six
octets. The three most significant octets are reserved to identify NIC manufacturers. These manufacturers, using only their assigned prefixes, uniquely assign the three least-significant octets of every Ethernet interface they produce.
Repeaters and hubs
A
repeater is an electronic device that receives a network
signal, cleans it of unnecessary noise and regenerates it. The signal is
retransmitted at a higher power level, or to the other side of obstruction so that the signal can cover longer distances without degradation. In most twisted pair Ethernet configurations, repeaters are required for cable that runs longer than 100 meters. With fiber optics, repeaters can be tens or even hundreds of kilometers apart.
Repeaters work on the physical layer of the OSI model but still require a small amount of time to regenerate the signal. This can cause a
propagation delay that affects network performance and may affect proper function. As a result, many network architectures limit the number of repeaters used in a network, e.g., the Ethernet
5-4-3 rule.
An Ethernet repeater with multiple ports is known as an
Ethernet hub. In addition to reconditioning and distributing network signals, a repeater hub assists with collision detection and fault isolation for the network. Hubs and repeaters in LANs have been largely obsoleted by modern
network switches.
Bridges and switches
Network bridges and
network switches are distinct from a hub in that they only forward frames to the ports involved in the communication whereas a hub forwards to all ports.
Bridges only have two ports but a switch can be thought of as a multi-port bridge. Switches normally have numerous ports, facilitating a star topology for devices, and for cascading additional switches.
Bridges and switches operate at the
data link layer
The data link layer, or layer 2, is the second layer of the seven-layer OSI model of computer networking. This layer is the protocol layer that transfers data between nodes on a network segment across the physical layer. The data link layer ...
(layer 2) of the
OSI model and
bridge
A bridge is a structure built to span a physical obstacle (such as a body of water, valley, road, or rail) without blocking the way underneath. It is constructed for the purpose of providing passage over the obstacle, which is usually somethi ...
traffic between two or more
network segments to form a single local network. Both are devices that forward
frames
A frame is often a structural system that supports other components of a physical construction and/or steel frame that limits the construction's extent.
Frame and FRAME may also refer to:
Physical objects
In building construction
*Framing (co ...
of data between
ports based on the destination MAC address in each frame.
They learn the association of physical ports to MAC addresses by examining the source addresses of received frames and only forward the frame when necessary. If an unknown destination MAC is targeted, the device broadcasts the request to all ports except the source, and discovers the location from the reply.
Bridges and switches divide the network's collision domain but maintain a single broadcast domain. Network segmentation through bridging and switching helps break down a large, congested network into an aggregation of smaller, more efficient networks.
Routers

A router is an internetworking device that forwards packets between networks by processing the addressing or routing information included in the packet. The routing information is often processed in conjunction with the
routing table
In computer networking, a routing table, or routing information base (RIB), is a data table stored in a router or a network host that lists the routes to particular network destinations, and in some cases, metrics (distances) associated with t ...
. A router uses its routing table to determine where to forward packets and does not require broadcasting packets which is inefficient for very big networks.
Modems
Modems (modulator-demodulator) are used to connect network nodes via wire not originally designed for digital network traffic, or for wireless. To do this one or more
carrier signals are
modulated by the digital signal to produce an
analog signal
An analog signal or analogue signal (see spelling differences) is any continuous signal representing some other quantity, i.e., ''analogous'' to another quantity. For example, in an analog audio signal, the instantaneous signal voltage vari ...
that can be tailored to give the required properties for transmission. Early modems modulated
audio signals sent over a standard voice telephone line. Modems are still commonly used for telephone lines, using a
digital subscriber line
Digital subscriber line (DSL; originally digital subscriber loop) is a family of technologies that are used to transmit digital data over telephone lines. In telecommunications marketing, the term DSL is widely understood to mean asymmetric d ...
technology and cable television systems using
DOCSIS technology.
Firewalls

A firewall is a network device or software for controlling network security and access rules. Firewalls are inserted in connections between secure internal networks and potentially insecure external networks such as the Internet. Firewalls are typically configured to reject access requests from unrecognized sources while allowing actions from recognized ones. The vital role firewalls play in network security grows in parallel with the constant increase in
cyber attacks.
Communication protocols


A
communication protocol is a set of rules for exchanging information over a network. Communication protocols have various characteristics. They may be
connection-oriented or
connectionless, they may use
circuit mode or packet switching, and they may use hierarchical addressing or flat addressing.
In a
protocol stack, often constructed per the
OSI model, communications functions are divided up into protocol layers, where each layer leverages the services of the layer below it until the lowest layer controls the hardware that sends information across the media. The use of protocol layering is ubiquitous across the field of computer networking. An important example of a protocol stack is
HTTP
The Hypertext Transfer Protocol (HTTP) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web, ...
(the World Wide Web protocol) running over
TCP
TCP may refer to:
Science and technology
* Transformer coupled plasma
* Tool Center Point, see Robot end effector
Computing
* Transmission Control Protocol, a fundamental Internet standard
* Telephony control protocol, a Bluetooth communication s ...
over IP (the Internet protocols) over
IEEE 802.11 (the Wi-Fi protocol). This stack is used between the
wireless router and the home user's personal computer when the user is surfing the web.
There are many communication protocols, a few of which are described below.
Common protocols
Internet Protocol Suite
The Internet Protocol Suite, also called TCP/IP, is the foundation of all modern networking. It offers connection-less and connection-oriented services over an inherently unreliable network traversed by datagram transmission using Internet protocol (IP). At its core, the protocol suite defines the addressing, identification, and routing specifications for
Internet Protocol Version 4 (IPv4) and for
IPv6
Internet Protocol version 6 (IPv6) is the most recent version of the Internet Protocol (IP), the communications protocol that provides an identification and location system for computers on networks and routes traffic across the Internet. I ...
, the next generation of the protocol with a much enlarged addressing capability. The Internet Protocol Suite is the defining set of protocols for the Internet.
IEEE 802
IEEE 802
IEEE 802 is a family of Institute of Electrical and Electronics Engineers (IEEE) standards for local area networks (LAN), personal area network (PAN), and metropolitan area networks (MAN). The IEEE 802 LAN/MAN Standards Committee (LMSC) maintai ...
is a family of IEEE standards dealing with local area networks and metropolitan area networks. The complete IEEE 802 protocol suite provides a diverse set of networking capabilities. The protocols have a flat addressing scheme. They operate mostly at layers 1 and 2 of the
OSI model.
For example,
MAC bridging (
IEEE 802.1D) deals with the routing of Ethernet packets using a
Spanning Tree Protocol.
IEEE 802.1Q describes
VLANs, and
IEEE 802.1X defines a port-based
Network Access Control
Network access control (NAC) is an approach to computer security that attempts to unify endpoint security technology (such as antivirus, host intrusion prevention, and vulnerability assessment), user or system authentication and network security ...
protocol, which forms the basis for the authentication mechanisms used in VLANs (but it is also found in WLANs) – it is what the home user sees when the user has to enter a "wireless access key".
= Ethernet
=
Ethernet is a family of technologies used in wired LANs. It is described by a set of standards together called
IEEE 802.3
IEEE 802.3 is a working group and a collection standards defining the physical layer and data link layer's media access control (MAC) of wired Ethernet. The standards are produced by the working group of Institute of Electrical and Electronics Eng ...
published by the Institute of Electrical and Electronics Engineers.
= Wireless LAN
=
Wireless LAN based on the
IEEE 802.11 standards, also widely known as WLAN or WiFi, is probably the most well-known member of the
IEEE 802
IEEE 802 is a family of Institute of Electrical and Electronics Engineers (IEEE) standards for local area networks (LAN), personal area network (PAN), and metropolitan area networks (MAN). The IEEE 802 LAN/MAN Standards Committee (LMSC) maintai ...
protocol family for home users today. IEEE 802.11 shares many properties with wired Ethernet.
SONET/SDH
 Synchronous optical networking
Synchronous optical networking (SONET) and Synchronous Digital Hierarchy (SDH) are standardized
multiplexing
In telecommunications and computer networking, multiplexing (sometimes contracted to muxing) is a method by which multiple analog or digital signals are combined into one signal over a shared medium. The aim is to share a scarce resource - a ...
protocols that transfer multiple digital bit streams over optical fiber using lasers. They were originally designed to transport circuit mode communications from a variety of different sources, primarily to support
circuit-switched
Circuit switching is a method of implementing a telecommunications network in which two network nodes establish a dedicated communications channel ( circuit) through the network before the nodes may communicate. The circuit guarantees the full b ...
digital telephony
Telephony ( ) is the field of technology involving the development, application, and deployment of telecommunication services for the purpose of electronic transmission of voice, fax, or data, between distant parties. The history of telephony is i ...
. However, due to its protocol neutrality and transport-oriented features, SONET/SDH also was the obvious choice for transporting
Asynchronous Transfer Mode
Asynchronous Transfer Mode (ATM) is a telecommunications standard defined by American National Standards Institute (ANSI) and ITU-T (formerly CCITT) for digital transmission of multiple types of traffic. ATM was developed to meet the needs o ...
(ATM) frames.
Asynchronous Transfer Mode

Asynchronous Transfer Mode (ATM) is a switching technique for telecommunication networks. It uses asynchronous
time-division multiplexing and encodes data into small, fixed-sized
cells. This differs from other protocols such as the
Internet Protocol Suite or
Ethernet
Ethernet () is a family of wired computer networking technologies commonly used in local area networks (LAN), metropolitan area networks (MAN) and wide area networks (WAN). It was commercially introduced in 1980 and first standardized in ...
that use variable-sized packets or
frames
A frame is often a structural system that supports other components of a physical construction and/or steel frame that limits the construction's extent.
Frame and FRAME may also refer to:
Physical objects
In building construction
*Framing (co ...
. ATM has similarities with both
circuit
Circuit may refer to:
Science and technology
Electrical engineering
* Electrical circuit, a complete electrical network with a closed-loop giving a return path for current
** Analog circuit, uses continuous signal levels
** Balanced circu ...
and
packet switched networking. This makes it a good choice for a network that must handle both traditional high-throughput data traffic, and real-time,
low-latency content such as voice and video. ATM uses a connection-oriented model in which a
virtual circuit
A virtual circuit (VC) is a means of transporting data over a data network, based on packet switching and in which a connection is established within the network between two endpoints. The network, rather than having a fixed data rate reservation ...
must be established between two endpoints before the actual data exchange begins.
ATM still plays a role in the
last mile
Last mile may refer to:
* Last mile (telecommunications), the final leg of the telecommunications networks that deliver services to retail end-users
* Last mile (transportation), the final leg the movement of people and goods from a transportation ...
, which is the connection between an
Internet service provider
An Internet service provider (ISP) is an organization that provides services for accessing, using, or participating in the Internet. ISPs can be organized in various forms, such as commercial, community-owned, non-profit, or otherwise privatel ...
and the home user.
Cellular standards
There are a number of different digital cellular standards, including:
Global System for Mobile Communications (GSM),
General Packet Radio Service (GPRS),
cdmaOne,
CDMA2000,
Evolution-Data Optimized (EV-DO),
Enhanced Data Rates for GSM Evolution (EDGE),
Universal Mobile Telecommunications System (UMTS),
Digital Enhanced Cordless Telecommunications
Digital enhanced cordless telecommunications (Digital European cordless telecommunications), usually known by the acronym DECT, is a standard primarily used for creating cordless telephone systems. It originated in Europe, where it is the commo ...
(DECT),
Digital AMPS (IS-136/TDMA), and
Integrated Digital Enhanced Network (iDEN).
Routing

Routing
Routing is the process of selecting a path for traffic in a network or between or across multiple networks. Broadly, routing is performed in many types of networks, including circuit-switched networks, such as the public switched telephone netw ...
is the process of selecting network paths to carry network traffic. Routing is performed for many kinds of networks, including
circuit switching networks and
packet switched networks.
In packet-switched networks,
routing protocol
A routing protocol specifies how routers communicate with each other to distribute information that enables them to select routes between nodes on a computer network. Routers perform the traffic directing functions on the Internet; data packet ...
s direct
packet forwarding through intermediate nodes. Intermediate nodes are typically network hardware devices such as routers, bridges, gateways, firewalls, or switches. General-purpose
computers can also forward packets and perform routing, though because they lack specialized hardware, may offer limited performance. The routing process directs forwarding on the basis of
routing table
In computer networking, a routing table, or routing information base (RIB), is a data table stored in a router or a network host that lists the routes to particular network destinations, and in some cases, metrics (distances) associated with t ...
s, which maintain a record of the routes to various network destinations. Most routing algorithms use only one network path at a time.
Multipath routing techniques enable the use of multiple alternative paths.
Routing can be contrasted with
bridging in its assumption that
network addresses are structured and that similar addresses imply proximity within the network. Structured addresses allow a single routing table entry to represent the route to a group of devices. In large networks, the structured addressing used by routers outperforms unstructured addressing used by bridging. Structured IP addresses are used on the Internet. Unstructured MAC addresses are used for bridging on Ethernet and similar local area networks.
Geographic scale
Networks may be characterized by many properties or features, such as physical capacity, organizational purpose, user authorization, access rights, and others. Another distinct classification method is that of the physical extent or geographic scale.
Nanoscale network
A
nanoscale network has key components implemented at the nanoscale, including message carriers, and leverages physical principles that differ from macroscale communication mechanisms. Nanoscale communication extends communication to very small sensors and actuators such as those found in biological systems and also tends to operate in environments that would be too harsh for other communication techniques.
Personal area network
A
personal area network (PAN) is a computer network used for communication among computers and different information technological devices close to one person. Some examples of devices that are used in a PAN are personal computers, printers, fax machines, telephones, PDAs, scanners, and video game consoles. A PAN may include wired and wireless devices. The reach of a PAN typically extends to 10 meters. A wired PAN is usually constructed with
USB and
FireWire
IEEE 1394 is an interface standard for a serial bus for high-speed communications and isochronous real-time data transfer. It was developed in the late 1980s and early 1990s by Apple in cooperation with a number of companies, primarily Sony a ...
connections while technologies such as
Bluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is limit ...
and
infrared communication typically form a wireless PAN.
Local area network
A
local area network (LAN) is a network that connects computers and devices in a limited geographical area such as a home, school, office building, or closely positioned group of buildings. Wired LANs are most commonly based on Ethernet technology. Other networking technologies such as
ITU-T
The ITU Telecommunication Standardization Sector (ITU-T) is one of the three sectors (divisions or units) of the International Telecommunication Union (ITU). It is responsible for coordinating standards for telecommunications and Information Commu ...
G.hn also provide a way to create a wired LAN using existing wiring, such as coaxial cables, telephone lines, and power lines.
A LAN can be connected to a
wide area network
A wide area network (WAN) is a telecommunications network that extends over a large geographic area. Wide area networks are often established with leased telecommunication circuits.
Businesses, as well as schools and government entities, u ...
(WAN) using a
router. The defining characteristics of a LAN, in contrast to a WAN, include higher
data transfer rate Data rate and data transfer rate can refer to several related and overlapping concepts in communications networks:
Achieved rate
* Bit rate, the number of bits that are conveyed or processed per unit of time
** Data signaling rate or gross bit rate ...
s, limited geographic range, and lack of reliance on
leased line
A leased line is a private telecommunications circuit between two or more locations provided according to a commercial contract. It is sometimes also known as a private circuit, and as a data line in the UK. Typically, leased lines are used by ...
s to provide connectivity. Current Ethernet or other IEEE 802.3 LAN technologies operate at data transfer rates up to and in excess of
100 Gbit/s, standardized by IEEE in 2010.
Home area network
A
home area network (HAN) is a residential LAN used for communication between digital devices typically deployed in the home, usually a small number of personal computers and accessories, such as printers and mobile computing devices. An important function is the sharing of Internet access, often a broadband service through a
cable Internet access or
digital subscriber line
Digital subscriber line (DSL; originally digital subscriber loop) is a family of technologies that are used to transmit digital data over telephone lines. In telecommunications marketing, the term DSL is widely understood to mean asymmetric d ...
(DSL) provider.
Storage area network
A
storage area network (SAN) is a dedicated network that provides access to consolidated, block-level data storage. SANs are primarily used to make storage devices, such as disk arrays, tape libraries, and optical jukeboxes, accessible to servers so that the storage appears as locally attached devices to the operating system. A SAN typically has its own network of storage devices that are generally not accessible through the local area network by other devices. The cost and complexity of SANs dropped in the early 2000s to levels allowing wider adoption across both enterprise and small to medium-sized business environments.
Campus area network
A
campus area network (CAN) is made up of an interconnection of LANs within a limited geographical area. The networking equipment (switches, routers) and transmission media (optical fiber,
Cat5 cabling, etc.) are almost entirely owned by the campus tenant or owner (an enterprise, university, government, etc.).
For example, a university campus network is likely to link a variety of campus buildings to connect academic colleges or departments, the library, and student residence halls.
Backbone network
A
backbone network is part of a computer network infrastructure that provides a path for the exchange of information between different LANs or subnetworks. A backbone can tie together diverse networks within the same building, across different buildings, or over a wide area. When designing a network backbone,
network performance and
network congestion are critical factors to take into account. Normally, the backbone network's capacity is greater than that of the individual networks connected to it.
For example, a large company might implement a backbone network to connect departments that are located around the world. The equipment that ties together the departmental networks constitutes the network backbone. Another example of a backbone network is the
Internet backbone, which is a massive, global system of fiber-optic cable and optical networking that carry the bulk of data between
wide area network
A wide area network (WAN) is a telecommunications network that extends over a large geographic area. Wide area networks are often established with leased telecommunication circuits.
Businesses, as well as schools and government entities, u ...
s (WANs), metro, regional, national and transoceanic networks.
Metropolitan area network
A
metropolitan area network (MAN) is a large computer network that interconnects users with computer resources in a geographic region of the size of a
metropolitan area.
Wide area network
A
wide area network
A wide area network (WAN) is a telecommunications network that extends over a large geographic area. Wide area networks are often established with leased telecommunication circuits.
Businesses, as well as schools and government entities, u ...
(WAN) is a computer network that covers a large geographic area such as a city, country, or spans even intercontinental distances. A WAN uses a communications channel that combines many types of media such as telephone lines, cables, and airwaves. A WAN often makes use of transmission facilities provided by
common carriers, such as telephone companies. WAN technologies generally function at the lower three layers of the
OSI model: the physical layer, the
data link layer
The data link layer, or layer 2, is the second layer of the seven-layer OSI model of computer networking. This layer is the protocol layer that transfers data between nodes on a network segment across the physical layer. The data link layer ...
, and the
network layer
In the seven-layer OSI model of computer networking, the network layer is layer 3. The network layer is responsible for packet forwarding including routing through intermediate routers.
Functions
The network layer provides the means of trans ...
.
Enterprise private network
An
enterprise private network is a network that a single organization builds to interconnect its office locations (e.g., production sites, head offices, remote offices, shops) so they can share computer resources.
Virtual private network
A
virtual private network (VPN) is an overlay network in which some of the links between nodes are carried by open connections or virtual circuits in some larger network (e.g., the Internet) instead of by physical wires. The data link layer protocols of the virtual network are said to be tunneled through the larger network when this is the case. One common application is secure communications through the public Internet, but a VPN need not have explicit security features, such as authentication or content encryption. VPNs, for example, can be used to separate the traffic of different user communities over an underlying network with strong security features.
VPN may have best-effort performance or may have a defined service level agreement (SLA) between the VPN customer and the VPN service provider. Generally, a VPN has a topology more complex than point-to-point.
Global area network
A
global area network
IEEE 802.20 or Mobile Broadband Wireless Access (MBWA) was a specification by the standard association of the Institute of Electrical and Electronics Engineers (IEEE) for mobile broadband networks. The main standard was published in 2008. MBW ...
(GAN) is a network used for supporting mobile across an arbitrary number of wireless LANs, satellite coverage areas, etc. The key challenge in mobile communications is handing off user communications from one local coverage area to the next. In IEEE Project 802, this involves a succession of terrestrial
wireless LAN
A wireless LAN (WLAN) is a wireless computer network that links two or more devices using wireless communication to form a local area network (LAN) within a limited area such as a home, school, computer laboratory, campus, or office building ...
s.
Organizational scope
Networks are typically managed by the organizations that own them. Private enterprise networks may use a combination of intranets and extranets. They may also provide network access to the
Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a ''internetworking, network of networks'' that consists ...
, which has no single owner and permits virtually unlimited global connectivity.
Intranet
An
intranet is a set of networks that are under the control of a single administrative entity. The intranet uses the
IP protocol and IP-based tools such as web browsers and file transfer applications. The administrative entity limits the use of the intranet to its authorized users. Most commonly, an intranet is the internal LAN of an organization. A large intranet typically has at least one web server to provide users with organizational information. An intranet is also anything behind the router on a local area network.
Extranet
An
extranet is a network that is also under the administrative control of a single organization but supports a limited connection to a specific external network. For example, an organization may provide access to some aspects of its intranet to share data with its business partners or customers. These other entities are not necessarily trusted from a security standpoint. Network connection to an extranet is often, but not always, implemented via WAN technology.
Internet
An
internetwork is the connection of multiple different types of computer networks to form a single computer network by layering on top of the different networking software and connecting them together using routers.
The
Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a ''internetworking, network of networks'' that consists ...
is the largest example of internetwork. It is a global system of interconnected governmental, academic, corporate, public, and private computer networks. It is based on the networking technologies of the Internet Protocol Suite. It is the successor of the
Advanced Research Projects Agency Network (ARPANET) developed by
DARPA
The Defense Advanced Research Projects Agency (DARPA) is a research and development agency of the United States Department of Defense responsible for the development of emerging technologies for use by the military.
Originally known as the Ad ...
of the
United States Department of Defense
The United States Department of Defense (DoD, USDOD or DOD) is an executive branch department of the federal government charged with coordinating and supervising all agencies and functions of the government directly related to national secur ...
. The Internet utilizes copper communications and the
optical networking backbone to enable the
World Wide Web
The World Wide Web (WWW), commonly known as the Web, is an information system enabling documents and other web resources to be accessed over the Internet.
Documents and downloadable media are made available to the network through web se ...
(WWW), the
Internet of Things
The Internet of things (IoT) describes physical objects (or groups of such objects) with sensors, processing ability, software and other technologies that connect and exchange data with other devices and systems over the Internet or other com ...
, video transfer, and a broad range of information services.
Participants on the Internet use a diverse array of methods of several hundred documented, and often standardized, protocols compatible with the Internet Protocol Suite and an addressing system (IP addresses) administered by the
Internet Assigned Numbers Authority and
address registries. Service providers and large enterprises exchange information about the
reachability of their address spaces through the
Border Gateway Protocol (BGP), forming a redundant worldwide mesh of transmission paths.
Darknet
A
darknet is an overlay network, typically running on the Internet, that is only accessible through specialized software. A darknet is an anonymizing network where connections are made only between trusted peers — sometimes called "friends" (
F2F) — using non-standard protocols and
ports.
Darknets are distinct from other distributed
peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network. They are said to form a peer-to-peer ...
networks as
sharing
Sharing is the joint use of a resource or space. It is also the process of dividing and distributing. In its narrow sense, it refers to joint or alternating use of inherently finite goods, such as a common pasture or a shared residence. Sti ...
is anonymous (that is, IP addresses are not publicly shared), and therefore users can communicate with little fear of governmental or corporate interference.
Network service
Network services are applications hosted by servers on a computer network, to
provide some functionality for members or users of the network, or to help the network itself to operate.
The
World Wide Web
The World Wide Web (WWW), commonly known as the Web, is an information system enabling documents and other web resources to be accessed over the Internet.
Documents and downloadable media are made available to the network through web se ...
,
E-mail
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" mean ...
,
printing
Printing is a process for mass reproducing text and images using a master form or template. The earliest non-paper products involving printing include cylinder seals and objects such as the Cyrus Cylinder and the Cylinders of Nabonidus. The ...
and
network file sharing are examples of well-known network services. Network services such as DNS (
Domain Name System
The Domain Name System (DNS) is a hierarchical and distributed naming system for computers, services, and other resources in the Internet or other Internet Protocol (IP) networks. It associates various information with domain names assigned ...
) give names for
IP and
MAC address
A media access control address (MAC address) is a unique identifier assigned to a network interface controller (NIC) for use as a network address in communications within a network segment. This use is common in most IEEE 802 networking tec ...
es (people remember names like "nm.lan" better than numbers like "210.121.67.18"),
and
DHCP to ensure that the equipment on the network has a valid IP address.
Services are usually based on a
service protocol that defines the format and sequencing of messages between clients and servers of that network service.
Network performance
Bandwidth
Bandwidth in bit/s may refer to consumed bandwidth, corresponding to achieved
throughput or
goodput, i.e., the average rate of successful data transfer through a communication path. The throughput is affected by technologies such as
bandwidth shaping,
bandwidth management,
bandwidth throttling,
bandwidth cap,
bandwidth allocation
Bandwidth allocation is the process of assigning radio frequencies to different applications. The radio spectrum is a finite resource, which means there is great need for an effective allocation process. In the United States, the Federal Commun ...
(for example
bandwidth allocation protocol and
dynamic bandwidth allocation
Dynamic bandwidth allocation is a technique by which traffic bandwidth in a shared telecommunications medium can be allocated on demand and fairly between different users of that bandwidth. This is a form of bandwidth management, and is essential ...
), etc. A bit stream's bandwidth is proportional to the average consumed signal bandwidth in hertz (the average spectral bandwidth of the analog signal representing the bit stream) during a studied time interval.
Network delay
''Network delay'' is a design and performance characteristic of a
telecommunications network
A telecommunications network is a group of nodes interconnected by telecommunications links that are used to exchange messages between the nodes. The links may use a variety of technologies based on the methodologies of circuit switching, mes ...
. It specifies the
latency for a bit of data to travel across the network from one
communication endpoint to another. It is typically measured in multiples or fractions of a second. Delay may differ slightly, depending on the location of the specific pair of communicating endpoints. Engineers usually report both the maximum and average delay, and they divide the delay into several parts:
*
Processing delay time it takes a router to process the packet header
*
Queuing delay time the packet spends in routing queues
*
Transmission delay time it takes to push the packet's bits onto the link
*
Propagation delay time for a signal to propagate through the media
A certain minimum level of delay is experienced by signals due to the time it takes to
transmit a packet serially through a
link. This delay is extended by more variable levels of delay due to
network congestion.
IP network delays can range from a few milliseconds to several hundred milliseconds.
Quality of service
Depending on the installation requirements,
network performance is usually measured by the quality of service of a telecommunications product. The parameters that affect this typically can include
throughput,
jitter,
bit error rate and latency.
The following list gives examples of network performance measures for a circuit-switched network and one type of
packet-switched network, viz. ATM:
*Circuit-switched networks: In
circuit switched networks, network performance is synonymous with the
grade of service. The number of rejected calls is a measure of how well the network is performing under heavy traffic loads. Other types of performance measures can include the level of noise and echo.
*ATM: In an
Asynchronous Transfer Mode
Asynchronous Transfer Mode (ATM) is a telecommunications standard defined by American National Standards Institute (ANSI) and ITU-T (formerly CCITT) for digital transmission of multiple types of traffic. ATM was developed to meet the needs o ...
(ATM) network, performance can be measured by line rate, quality of service (QoS), data throughput, connect time, stability, technology, modulation technique, and modem enhancements.
There are many ways to measure the performance of a network, as each network is different in nature and design. Performance can also be modeled instead of measured. For example,
state transition diagrams are often used to model queuing performance in a circuit-switched network. The network planner uses these diagrams to analyze how the network performs in each state, ensuring that the network is optimally designed.
Network congestion
Network congestion occurs when a link or node is subjected to a greater data load than it is rated for, resulting in a deterioration of its quality of service. When networks are congested and queues become too full, packets have to be discarded, and so networks rely on re-transmission. Typical effects of congestion include queueing delay,
packet loss or the
blocking of new connections. A consequence of these latter two is that incremental increases in
offered load In the mathematical theory of probability, offered load is a concept in queuing theory. The offered load is a measure of traffic in a queue. The offered load is given by Little's law: the arrival rate into the queue (symbolized with λ) multiplied ...
lead either to only a small increase in the network
throughput or to a reduction in network throughput.
Network protocols that use aggressive
retransmissions to compensate for packet loss tend to keep systems in a state of network congestion—even after the initial load is reduced to a level that would not normally induce network congestion. Thus, networks using these protocols can exhibit two stable states under the same level of load. The stable state with low throughput is known as ''congestive collapse''.
Modern networks use
congestion control,
congestion avoidance and
traffic control techniques to try to avoid congestion collapse (i.e. endpoints typically slow down or sometimes even stop transmission entirely when the network is congested). These techniques include:
exponential backoff in protocols such as
802.11's
CSMA/CA and the original Ethernet,
window
A window is an opening in a wall, door, roof, or vehicle that allows the exchange of light and may also allow the passage of sound and sometimes air. Modern windows are usually glazed or covered in some other transparent or translucent mate ...
reduction in TCP, and
fair queueing in devices such as routers. Another method to avoid the negative effects of network congestion is implementing priority schemes so that some packets are transmitted with higher priority than others. Priority schemes do not solve network congestion by themselves, but they help to alleviate the effects of congestion for some services. An example of this is
802.1p. A third method to avoid network congestion is the explicit allocation of network resources to specific flows. One example of this is the use of Contention-Free Transmission Opportunities (CFTXOPs) in the
ITU-T
The ITU Telecommunication Standardization Sector (ITU-T) is one of the three sectors (divisions or units) of the International Telecommunication Union (ITU). It is responsible for coordinating standards for telecommunications and Information Commu ...
G.hn standard, which provides high-speed (up to 1 Gbit/s)
Local area networking over existing home wires (power lines, phone lines and coaxial cables).
For the Internet, addresses the subject of congestion control in detail.
Network resilience
Network resilience is "the ability to provide and maintain an acceptable level of
service
Service may refer to:
Activities
* Administrative service, a required part of the workload of university faculty
* Civil service, the body of employees of a government
* Community service, volunteer service for the benefit of a community or a pu ...
in the face of
faults and challenges to normal operation."
Security
Computer networks are also used by
security hackers to deploy
computer virus
A computer virus is a type of computer program that, when executed, replicates itself by modifying other computer programs and inserting its own code. If this replication succeeds, the affected areas are then said to be "infected" with a compu ...
es or
computer worm
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers. It often uses a computer network to spread itself, relying on security failures on the target computer to access it. It wi ...
s on devices connected to the network, or to prevent these devices from accessing the network via a
denial-of-service attack.
Network security
Network Security
Network security consists of the policies, processes and practices adopted to prevent, detect and monitor unauthorized access, misuse, modification, or denial of a computer network and network-accessible resources. Network security involves th ...
consists of provisions and policies adopted by the
network administrator to prevent and monitor
unauthorized access, misuse, modification, or denial of the computer network and its network-accessible resources. Network security is the authorization of access to data in a network, which is controlled by the network administrator. Users are assigned an ID and password that allows them access to information and programs within their authority. Network security is used on a variety of computer networks, both public and private, to secure daily transactions and communications among businesses, government agencies, and individuals.
Network surveillance
Network surveillance
Computer and network surveillance is the monitoring of computer activity and data stored locally on a computer or data being transferred over computer networks such as the Internet. This monitoring is often carried out covertly and may be comple ...
is the monitoring of data being transferred over computer networks such as the Internet. The monitoring is often done surreptitiously and may be done by or at the behest of governments, by corporations, criminal organizations, or individuals. It may or may not be legal and may or may not require authorization from a court or other independent agency.
Computer and network surveillance programs are widespread today, and almost all Internet traffic is or could potentially be monitored for clues to illegal activity.
Surveillance is very useful to governments and
law enforcement
Law enforcement is the activity of some members of government who act in an organized manner to enforce the law by discovering, deterring, rehabilitating, or punishing people who violate the rules and norms governing that society. The term ...
to maintain
social control, recognize and monitor threats, and prevent/investigate
criminal
In ordinary language, a crime is an unlawful act punishable by a state or other authority. The term ''crime'' does not, in modern criminal law, have any simple and universally accepted definition,Farmer, Lindsay: "Crime, definitions of", in Ca ...
activity. With the advent of programs such as the
Total Information Awareness
Total Information Awareness (TIA) was a mass detection program by the United States Information Awareness Office. It operated under this title from February to May 2003 before being renamed Terrorism Information Awareness.
Based on the conce ...
program, technologies such as
high-speed surveillance computers and
biometrics software, and laws such as the
Communications Assistance For Law Enforcement Act, governments now possess an unprecedented ability to monitor the activities of citizens.
However, many
civil rights
Civil and political rights are a class of rights that protect individuals' freedom from infringement by governments, social organizations, and private individuals. They ensure one's entitlement to participate in the civil and political life ...
and
privacy
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively.
The domain of privacy partially overlaps with security, which can include the concepts of a ...
groups—such as
Reporters Without Borders
Reporters Without Borders (RWB; french: Reporters sans frontières; RSF) is an international non-profit and non-governmental organization with the stated aim of safeguarding the right to freedom of information. It describes its advocacy as found ...
, the
Electronic Frontier Foundation
The Electronic Frontier Foundation (EFF) is an international non-profit digital rights group based in San Francisco, California. The foundation was formed on 10 July 1990 by John Gilmore, John Perry Barlow and Mitch Kapor to promote Internet ...
, and the
American Civil Liberties Union
The American Civil Liberties Union (ACLU) is a nonprofit organization founded in 1920 "to defend and preserve the individual rights and liberties guaranteed to every person in this country by the Constitution and laws of the United States". ...
—have expressed concern that increasing surveillance of citizens may lead to a
mass surveillance society, with limited political and personal freedoms. Fears such as this have led to numerous lawsuits such as ''
Hepting v. AT&T''.
The
hacktivist group
Anonymous
Anonymous may refer to:
* Anonymity, the state of an individual's identity, or personally identifiable information, being publicly unknown
** Anonymous work, a work of art or literature that has an unnamed or unknown creator or author
* Anonym ...
has hacked into government websites in protest of what it considers "draconian surveillance".
End to end encryption
End-to-end encryption (E2EE) is a
digital communications
Data transmission and data reception or, more broadly, data communication or digital communications is the transfer and reception of data in the form of a digital bitstream or a digitized analog signal transmitted over a point-to-point o ...
paradigm of uninterrupted protection of data traveling between two communicating parties. It involves the originating party
encrypting data so only the intended recipient can decrypt it, with no dependency on third parties. End-to-end encryption prevents intermediaries, such as
Internet providers or
application service providers, from discovering or tampering with communications. End-to-end encryption generally protects both
confidentiality and
integrity
Integrity is the practice of being honest and showing a consistent and uncompromising adherence to strong moral and ethical principles and values.
In ethics, integrity is regarded as the honesty and truthfulness or accuracy of one's actions. In ...
.
Examples of end-to-end encryption include
HTTPS for web traffic,
PGP for
email
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" mean ...
,
OTR for
instant messaging
Instant messaging (IM) technology is a type of online chat allowing real-time text transmission over the Internet or another computer network. Messages are typically transmitted between two or more parties, when each user inputs text and trigge ...
,
ZRTP for
telephony
Telephony ( ) is the field of technology involving the development, application, and deployment of telecommunication services for the purpose of electronic transmission of voice, fax, or data, between distant parties. The history of telephony is i ...
, and
TETRA for radio.
Typical
server-based communications systems do not include end-to-end encryption. These systems can only guarantee the protection of communications between
clients and
servers, not between the communicating parties themselves. Examples of non-E2EE systems are
Google Talk,
Yahoo Messenger,
Facebook
Facebook is an online social media and social networking service owned by American company Meta Platforms. Founded in 2004 by Mark Zuckerberg with fellow Harvard College students and roommates Eduardo Saverin, Andrew McCollum, Dustin ...
, and
Dropbox. Some such systems, for example, LavaBit and SecretInk, have even described themselves as offering "end-to-end" encryption when they do not. Some systems that normally offer end-to-end encryption have turned out to contain a
back door that subverts negotiation of the
encryption key between the communicating parties, for example
Skype
Skype () is a proprietary telecommunications application operated by Skype Technologies, a division of Microsoft, best known for VoIP-based videotelephony, videoconferencing and voice calls. It also has instant messaging, file transfer, ...
or
Hushmail.
The end-to-end encryption paradigm does not directly address risks at the endpoints of the communication themselves, such as the
technical exploitation of
clients, poor quality
random number generators, or
key escrow. E2EE also does not address
traffic analysis, which relates to things such as the identities of the endpoints and the times and quantities of messages that are sent.
SSL/TLS
The introduction and rapid growth of e-commerce on the World Wide Web in the mid-1990s made it obvious that some form of authentication and encryption was needed.
Netscape took the first shot at a new standard. At the time, the dominant web browser was
Netscape Navigator. Netscape created a standard called secure socket layer (SSL). SSL requires a server with a certificate. When a client requests access to an SSL-secured server, the server sends a copy of the certificate to the client. The SSL client checks this certificate (all web browsers come with an exhaustive list of CA root certificates preloaded), and if the certificate checks out, the server is authenticated and the client negotiates a symmetric-key cipher for use in the session. The session is now in a very secure encrypted tunnel between the SSL server and the SSL client.
Views of networks
Users and network administrators typically have different views of their networks. Users can share printers and some servers from a
workgroup, which usually means they are in the same geographic location and are on the same LAN, whereas a Network Administrator is responsible to keep that network up and running. A
community of interest has less of a connection of being in a local area and should be thought of as a set of arbitrarily located users who share a set of servers, and possibly also communicate via
peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network. They are said to form a peer-to-peer ...
technologies.
Network administrators can see networks from both physical and logical perspectives. The physical perspective involves geographic locations, physical cabling, and the network elements (e.g., routers, bridges and
application layer gateways) that interconnect via the transmission media. Logical networks, called, in the TCP/IP architecture,
subnets, map onto one or more transmission media. For example, a common practice in a campus of buildings is to make a set of LAN cables in each building appear to be a common subnet, using VLAN technology.
Both users and administrators are aware, to varying extents, of the trust and scope characteristics of a network. Again using TCP/IP architectural terminology, an
intranet is a community of interest under private administration usually by an enterprise, and is only accessible by authorized users (e.g. employees).
Intranets do not have to be connected to the Internet, but generally have a limited connection. An
extranet is an extension of an intranet that allows secure communications to users outside of the intranet (e.g. business partners, customers).
Unofficially, the Internet is the set of users, enterprises, and content providers that are interconnected by Internet Service Providers (ISP). From an engineering viewpoint, the Internet is the set of subnets, and aggregates of subnets, that share the registered
IP address
An Internet Protocol address (IP address) is a numerical label such as that is connected to a computer network that uses the Internet Protocol for communication.. Updated by . An IP address serves two main functions: network interface ident ...
space and exchange information about the reachability of those IP addresses using the
Border Gateway Protocol. Typically, the
human-readable names of servers are translated to IP addresses, transparently to users, via the directory function of the
Domain Name System
The Domain Name System (DNS) is a hierarchical and distributed naming system for computers, services, and other resources in the Internet or other Internet Protocol (IP) networks. It associates various information with domain names assigned ...
(DNS).
Over the Internet, there can be
business-to-business (B2B),
business-to-consumer (B2C) and
consumer-to-consumer (C2C) communications. When money or sensitive information is exchanged, the communications are apt to be protected by some form of
communications security mechanism. Intranets and extranets can be securely superimposed onto the Internet, without any access by general Internet users and administrators, using secure Virtual Private Network (VPN) technology.
Journals and newsletters
Open Computer Science(
open access
Open access (OA) is a set of principles and a range of practices through which research outputs are distributed online, free of access charges or other barriers. With open access strictly defined (according to the 2001 definition), or libre o ...
journal)
See also
References
Further reading
* Shelly, Gary, et al. "Discovering Computers" 2003 Edition.
* Wendell Odom, Rus Healy, Denise Donohue. (2010) CCIE Routing and Switching. Indianapolis, IN: Cisco Press
* Kurose James F and Keith W. Ross: Computer Networking: A Top-Down Approach Featuring the Internet, Pearson Education 2005.
*
William Stallings, ''Computer Networking with Internet Protocols and Technology'', Pearson Education 2004.
*
Important publications in computer networks
* Network Communication Architecture and Protocols: OSI Network Architecture 7 Layers Model
*
Dimitri Bertsekas
Dimitri Panteli Bertsekas (born 1942, Athens, el, Δημήτρης Παντελής Μπερτσεκάς) is an applied mathematician, electrical engineer, and computer scientist, a McAfee Professor at the Department of Electrical Engineeri ...
, and
Robert Gallager
Robert Gray Gallager (born May 29, 1931) is an American electrical engineer known for his work on information theory and communications networks.
Gallager was elected a member of the National Academy of Engineering (NAE) in 1979 for contributio ...
, "Data Networks," Prentice Hall, 1992.
External links
*
IEEE Ethernet manufacturer informationA computer networking acronym guide
{{Authority control
 Most modern computer networks use protocols based on packet-mode transmission. A
Most modern computer networks use protocols based on packet-mode transmission. A  The transmission media (often referred to in the literature as the '' physical medium'') used to link devices to form a computer network include
The transmission media (often referred to in the literature as the '' physical medium'') used to link devices to form a computer network include  The following classes of wired technologies are used in computer networking.
*''
The following classes of wired technologies are used in computer networking.
*'' *An ''
*An '' Network connections can be established wirelessly using radio or other electromagnetic means of communication.
*'' Terrestrial
Network connections can be established wirelessly using radio or other electromagnetic means of communication.
*'' Terrestrial  A network interface controller (NIC) is computer hardware that connects the computer to the network media and has the ability to process low-level network information. For example, the NIC may have a connector for accepting a cable, or an aerial for wireless transmission and reception, and the associated circuitry.
In Ethernet networks, each network interface controller has a unique Media Access Control (MAC) address—usually stored in the controller's permanent memory. To avoid address conflicts between network devices, the
A network interface controller (NIC) is computer hardware that connects the computer to the network media and has the ability to process low-level network information. For example, the NIC may have a connector for accepting a cable, or an aerial for wireless transmission and reception, and the associated circuitry.
In Ethernet networks, each network interface controller has a unique Media Access Control (MAC) address—usually stored in the controller's permanent memory. To avoid address conflicts between network devices, the  A router is an internetworking device that forwards packets between networks by processing the addressing or routing information included in the packet. The routing information is often processed in conjunction with the
A router is an internetworking device that forwards packets between networks by processing the addressing or routing information included in the packet. The routing information is often processed in conjunction with the  A firewall is a network device or software for controlling network security and access rules. Firewalls are inserted in connections between secure internal networks and potentially insecure external networks such as the Internet. Firewalls are typically configured to reject access requests from unrecognized sources while allowing actions from recognized ones. The vital role firewalls play in network security grows in parallel with the constant increase in cyber attacks.
A firewall is a network device or software for controlling network security and access rules. Firewalls are inserted in connections between secure internal networks and potentially insecure external networks such as the Internet. Firewalls are typically configured to reject access requests from unrecognized sources while allowing actions from recognized ones. The vital role firewalls play in network security grows in parallel with the constant increase in cyber attacks.
 Synchronous optical networking (SONET) and Synchronous Digital Hierarchy (SDH) are standardized
Synchronous optical networking (SONET) and Synchronous Digital Hierarchy (SDH) are standardized  Asynchronous Transfer Mode (ATM) is a switching technique for telecommunication networks. It uses asynchronous time-division multiplexing and encodes data into small, fixed-sized cells. This differs from other protocols such as the Internet Protocol Suite or
Asynchronous Transfer Mode (ATM) is a switching technique for telecommunication networks. It uses asynchronous time-division multiplexing and encodes data into small, fixed-sized cells. This differs from other protocols such as the Internet Protocol Suite or 
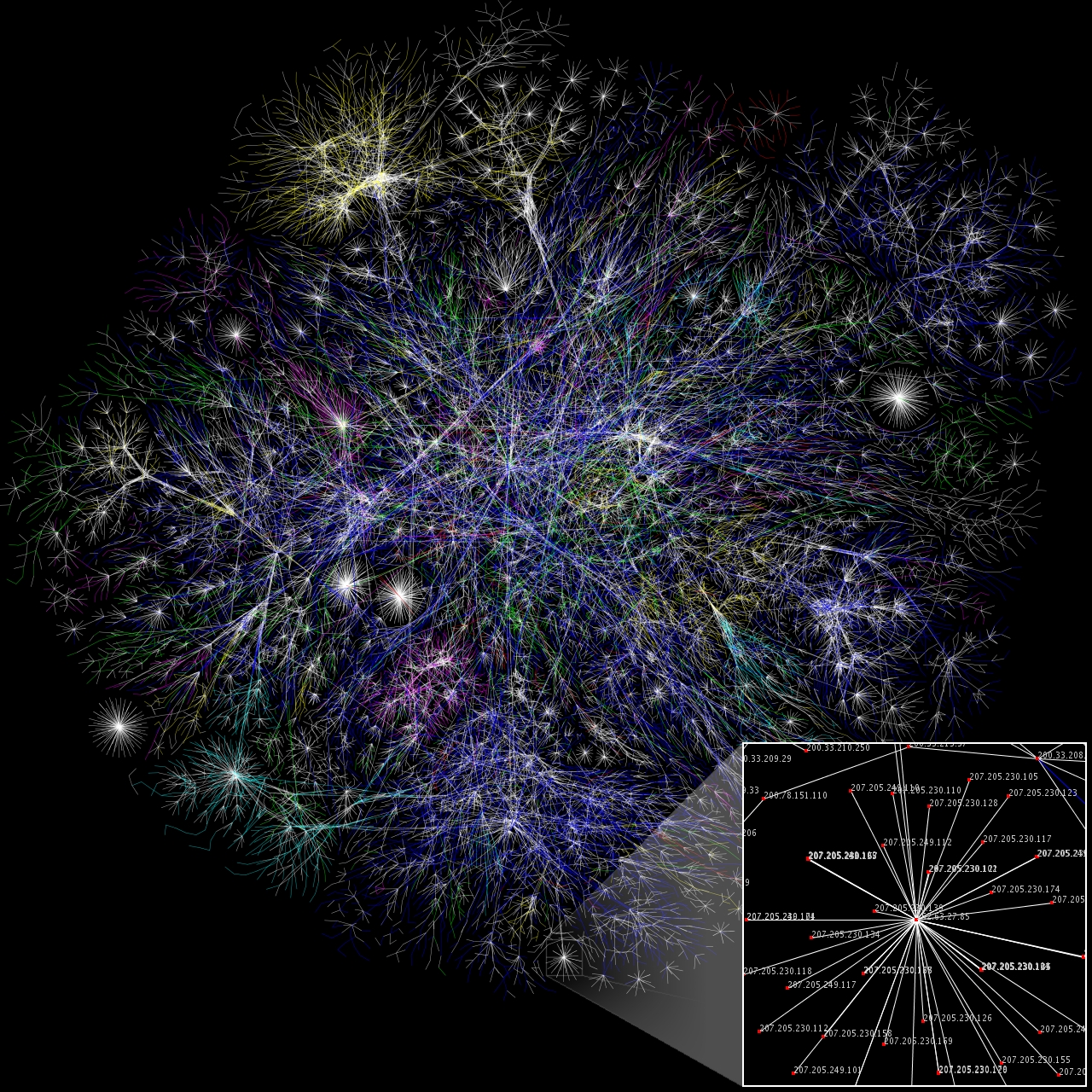 The
The