|
Tarpit (networking)
A tarpit is a service on a computer system (usually a server) that purposely delays incoming connections. The technique was developed as a defense against a computer worm, and the idea is that network abuses such as spamming or broad scanning are less effective, and therefore less attractive, if they take too long. The concept is analogous with a tar pit, in which animals can get bogged down and slowly sink under the surface, like in a swamp. The original tarpit idea Tom Liston developed the original tarpitting program ''LaBrea''. It can protect an entire network with a tarpit run on a single machine. The machine listens for Address Resolution Protocol requests that go unanswered (indicating unused addresses), then replies to those requests, receives the initial SYN packet of the scanner and sends a SYN/ACK in response. It does not open a socket or prepare a connection, in fact it can forget all about the connection after sending the SYN/ACK. However, the remote site sends ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer System
A computer is a machine that can be programmed to carry out sequences of arithmetic or logical operations (computation) automatically. Modern digital electronic computers can perform generic sets of operations known as programs. These programs enable computers to perform a wide range of tasks. A computer system is a nominally complete computer that includes the hardware, operating system (main software), and peripheral equipment needed and used for full operation. This term may also refer to a group of computers that are linked and function together, such as a computer network or computer cluster. A broad range of industrial and consumer products use computers as control systems. Simple special-purpose devices like microwave ovens and remote controls are included, as are factory devices like industrial robots and computer-aided design, as well as general-purpose devices like personal computers and mobile devices like smartphones. Computers power the Internet, which links ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
OpenBSD
OpenBSD is a security-focused, free and open-source, Unix-like operating system based on the Berkeley Software Distribution (BSD). Theo de Raadt created OpenBSD in 1995 by forking NetBSD 1.0. According to the website, the OpenBSD project emphasizes "portability, standardization, correctness, proactive security and integrated cryptography." The OpenBSD project maintains portable versions of many subsystems as packages for other operating systems. Because of the project's preferred BSD license, many components are reused in proprietary and corporate-sponsored software projects. The firewall code in Apple's macOS is based on OpenBSD's PF firewall code, Android's Bionic C standard library is based on OpenBSD code, LLVM uses OpenBSD's regular expression library, and Windows 10 uses OpenSSH (OpenBSD Secure Shell) with LibreSSL. The word "open" in the name OpenBSD refers to the availability of the operating system source code on the Internet, although the word "open" in the nam ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Botnet
A botnet is a group of Internet-connected devices, each of which runs one or more bots. Botnets can be used to perform Distributed Denial-of-Service (DDoS) attacks, steal data, send spam, and allow the attacker to access the device and its connection. The owner can control the botnet using command and control (C&C) software. The word "botnet" is a portmanteau of the words "robot" and "network". The term is usually used with a negative or malicious connotation. Overview A botnet is a logical collection of Internet-connected devices, such as computers, smartphones or Internet of things (IoT) devices whose security have been breached and control ceded to a third party. Each compromised device, known as a "bot," is created when a device is penetrated by software from a '' malware'' (malicious software) distribution. The controller of a botnet is able to direct the activities of these compromised computers through communication channels formed by standards-based network protocols, su ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
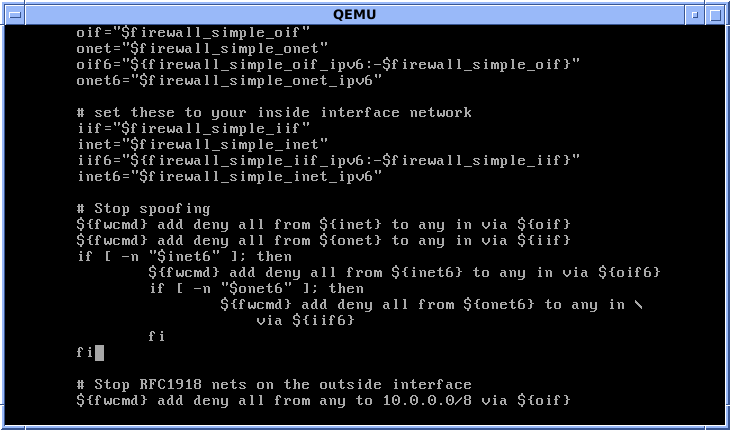
Ipfirewall
ipfirewall or ipfw is a FreeBSD IP, stateful firewall, packet filter and traffic accounting facility. Its ruleset logic is similar to many other packet filters except IPFilter. ipfw is authored and maintained by FreeBSD volunteer staff members. Its syntax enables use of sophisticated filtering capabilities and thus enables users to satisfy advanced requirements. It can either be used as a loadable kernel module or incorporated into the kernel; use as a loadable kernel module where possible is highly recommended. ipfw was the built-in firewall of Mac OS X until Mac OS X 10.7 Lion in 2011 when it was replaced with the OpenBSD project's PF. Like FreeBSD, ipfw is open source. It is used in many FreeBSD-based firewall products, including m0n0wall and FreeNAS. A port of an early version of ipfw was used since Linux 1.1 as the first implementation of firewall available for Linux, until it was replaced by ipchains. A modern port of ipfw and the ''dummynet'' traffic shaper is ava ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Stockade (software)
Stockade is a TCP-layer blocking tool written in C++. It denies TCP/IP access to registered IP addresses by using the ipfw packet filter. It targets spam prevention, but may also be used against other attackers (e.g. brute force password crackers.) The rate limiting approach This approach leverages the superior determination exhibited by legitimate senders. In this respect, it may be considered similar to greylisting. Originally, the authors conceived an ''MT Proxy'' to rate-limit the SMTP connections of messages believed to be spam. That worked by adding a ''dummynet'' rule for frequent senders who had been sending messages that triggered an unreliable statistical analysis. A key limitation of the original scheme was the consumption of local resources (in the SMTP proxy). Stockade approach introduces the notion that an inbound TCP connection may be rejected with some random probability proportional to the level of spam already seen from the connection’s originator over some c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Libipq
libipq is a development library for iptables userspace packet queuing. Libipq provides an API for communicating with ip_queue. Libipq has been deprecated in favour of the newelibnetfilter_queuein Linux kernel-2.6.14 onwards. Use in widely used software applications libipq has been used by some widely deployed applications as their interface to the Linux kernel-space iptables packet filter. * Snort - Snort is an Intrusion Detection System An intrusion detection system (IDS; also intrusion prevention system or IPS) is a device or software application that monitors a network or systems for malicious activity or policy violations. Any intrusion activity or violation is typically rep ... which runs in user-space and uses libipq to interface with Linux's iptables packet filter. External links iptables at netfilter.orglibipq subversion repositoryLibipq network simulator example Linux kernel features Linux security software {{Compu-library-stub ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Daemon (computer Software)
In multitasking computer operating systems, a daemon ( or ) is a computer program that runs as a background process, rather than being under the direct control of an interactive user. Traditionally, the process names of a daemon end with the letter ''d'', for clarification that the process is in fact a daemon, and for differentiation between a daemon and a normal computer program. For example, is a daemon that implements system logging facility, and is a daemon that serves incoming SSH connections. In a Unix environment, the parent process of a daemon is often, but not always, the init process. A daemon is usually created either by a process forking a child process and then immediately exiting, thus causing init to adopt the child process, or by the init process directly launching the daemon. In addition, a daemon launched by forking and exiting typically must perform other operations, such as dissociating the process from any controlling terminal (tty). Such procedures are ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
E-mail Forwarding
Email forwarding generically refers to the operation of re-sending an email message delivered to one email address to one or more different email addresses. The term ''forwarding'', used for mail since long before electronic communications, has no specific technical meaning,In section 3.9.2 ''List'' of RFC 5321, the term ''forwarding'' is used ambiguously. It notes that "''the key difference between handling aliases (Section 3.9.1) and forwarding (this subsection) is the change to the 'Return-Path'' header'." That wording, new w.r.t. RFC 2821, could be interpreted as the definition of ''forwarding'', if the same term weren't used at the beginning of the same subsection with the opposite meaning. As a contributor to RFC 5321 agreed, but it implies that the email has been moved "forward" to a new destination. Email forwarding can also redirect mail going to a certain address and send it to one or more other addresses. Vice versa, email items going to several different addresses can ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Spam Trap
A spamtrap is a honeypot used to collect spam. Spamtraps are usually e-mail addresses that are created not for communication, but rather to lure spam. In order to prevent legitimate email from being invited, the e-mail address will typically only be published in a location hidden from view such that an automated e-mail address harvester (used by spammers) can find the email address, but no sender would be encouraged to send messages to the email address for any legitimate purpose. Since no e-mail is solicited by the owner of this spamtrap e-mail address, any e-mail messages sent to this address are immediately considered unsolicited. The term is a compound of the words "spam" and "trap", because a spam analyst will lay out spamtraps to catch spam in the same way that a fur trapper lays out traps to catch wild animals. The provenance of this term is unknown, but several competing anti-spam organizations claim trademark over it. Industry uses An untainted spamtrap can continue t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Iptables
iptables is a user-space utility program that allows a system administrator to configure the IP packet filter rules of the Linux kernel firewall, implemented as different Netfilter modules. The filters are organized in different tables, which contain chains of rules for how to treat network traffic packets. Different kernel modules and programs are currently used for different protocols; ''iptables'' applies to IPv4, ''ip6tables'' to IPv6, ''arptables'' to ARP, and ' to Ethernet frames. iptables requires elevated privileges to operate and must be executed by user root, otherwise it fails to function. On most Linux systems, iptables is installed as and documented in its man pages, which can be opened using man iptables when installed. It may also be found in /sbin/iptables, but since iptables is more like a service rather than an "essential binary", the preferred location remains . The term ''iptables'' is also commonly used to inclusively refer to the kernel-level componen ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SMTP
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typically use SMTP only for sending messages to a mail server for relaying, and typically submit outgoing email to the mail server on port 587 or 465 per . For retrieving messages, IMAP (which replaced the older POP3) is standard, but proprietary servers also often implement proprietary protocols, e.g., Exchange ActiveSync. SMTP's origins began in 1980, building on concepts implemented on the ARPANET since 1971. It has been updated, modified and extended multiple times. The protocol version in common use today has extensible structure with various extensions for authentication, encryption, binary data transfer, and internationalized email addresses. SMTP servers commonly use the Transmission Control Protocol on port number 25 (for plaintext) and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |