|
Smurf Attack
A Smurf attack is a distributed denial-of-service attack in which large numbers of Internet Control Message Protocol (ICMP) packets with the intended victim's spoofed source IP are broadcast to a computer network using an IP broadcast address. Most devices on a network will, by default, respond to this by sending a reply to the source IP address. If the number of machines on the network that receive and respond to these packets is very large, the victim's computer will be flooded with traffic. This can slow down the victim's computer to the point where it becomes impossible to work on. History The original Smurf was written by Dan Moschuk (alias TFreak) in 1997 . In the late 1990s, many IP networks would participate in Smurf attacks if prompted (that is, they would respond to ICMP requests sent to broadcast addresses). The name comes from the idea of very small, but numerous attackers overwhelming a much larger opponent (see Smurfs). Today, administrators can make a network imm ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Distributed Denial-of-service Attack
In computing, a denial-of-service attack (DoS attack) is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to a network. Denial of service is typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to overload systems and prevent some or all legitimate requests from being fulfilled. In a distributed denial-of-service attack (DDoS attack), the incoming traffic flooding the victim originates from many different sources. More sophisticated strategies are required to mitigate this type of attack, as simply attempting to block a single source is insufficient because there are multiple sources. A DoS or DDoS attack is analogous to a group of people crowding the entry door of a shop, making it hard for legitimate customers to enter, thus disrupting trade. Criminal perpetrators of DoS attacks of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ingress Filtering
In computer networking, ingress filtering is a technique used to ensure that incoming Packet (information technology), packets are actually from the networks from which they claim to originate. This can be used as a countermeasure against various spoofing attacks where the attacker's packets contain fake IP addresses. Spoofing is often used in denial-of-service attacks, and mitigating these is a primary application of ingress filtering. Problem Networks receive packets from other networks. Normally a packet will contain the IP address of the computer that originally sent it. This allows devices in the receiving network to know where it came from, allowing a reply to be routed back (amongst other things), except when IP addresses are used through a proxy or a spoofed IP address, which does not pinpoint a specific user within that pool of users. A sender IP address can be faked (IP address spoofing, spoofed), characterising a spoofing attack. This disguises the origin of packets ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Source Code
In computing, source code, or simply code, is any collection of code, with or without comments, written using a human-readable programming language, usually as plain text. The source code of a program is specially designed to facilitate the work of computer programmers, who specify the actions to be performed by a computer mostly by writing source code. The source code is often transformed by an assembler or compiler into binary machine code that can be executed by the computer. The machine code is then available for execution at a later time. Most application software is distributed in a form that includes only executable files. If the source code were included it would be useful to a user, programmer or a system administrator, any of whom might wish to study or modify the program. Alternatively, depending on the technology being used, source code may be interpreted and executed directly. Definitions Richard Stallman's definition, formulated in his 1989 seminal li ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Character Generator Protocol
The Character Generator Protocol (CHARGEN) is a service of the Internet Protocol Suite defined in in 1983 by Jon Postel. It is intended for testing, debugging, and measurement purposes. The protocol is rarely used, as its design flaws allow ready misuse. A host may connect to a server that supports the Character Generator Protocol on either Transmission Control Protocol (TCP) or User Datagram Protocol (UDP) port number 19. Upon opening a TCP connection, the server starts sending arbitrary characters to the connecting host and continues until the host closes the connection. In the UDP implementation of the protocol, the server sends a UDP datagram containing a random number (between 0 and 512) of characters every time it receives a datagram from the connecting host. Any data received by the server is discarded. Inetd implementation On most Unix-like operating systems, a CHARGEN server is built into the inetd or xinetd daemon. The CHARGEN service is usually not enabled by defaul ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Echo Protocol
The Echo Protocol is a service in the Internet Protocol Suite defined in RFC 862. It was originally proposed for testing and measurement of round-trip times in IP networks. A host may connect to a server that supports the Echo Protocol using the Transmission Control Protocol (TCP) or the User Datagram Protocol (UDP) on the well-known port number 7. The server sends back an identical copy of the data it received. Inetd implementation On UNIX-like operating systems an echo server is built into the inetd family of daemons. The echo service is usually not enabled by default. It may be enabled by adding the following lines to the file and telling inetd to reload its configuration: echo stream tcp nowait root internal echo dgram udp wait root internal On various routers, this TCP or UDP port 7 for the Echo Protocol for relaying ICMP datagrams (or port 9 for the Discard Protocol) is also configured by default as a proxy to relay Wake-on-LAN (WOL) magic p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
User Datagram Protocol
In computer networking, the User Datagram Protocol (UDP) is one of the core communication protocols of the Internet protocol suite used to send messages (transported as datagrams in packets) to other hosts on an Internet Protocol (IP) network. Within an IP network, UDP does not require prior communication to set up communication channels or data paths. UDP uses a simple connectionless communication model with a minimum of protocol mechanisms. UDP provides checksums for data integrity, and port numbers for addressing different functions at the source and destination of the datagram. It has no handshaking dialogues, and thus exposes the user's program to any unreliability of the underlying network; there is no guarantee of delivery, ordering, or duplicate protection. If error-correction facilities are needed at the network interface level, an application may instead use Transmission Control Protocol (TCP) or Stream Control Transmission Protocol (SCTP) which are designed for this ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Fraggle Rock
''Fraggle Rock'' (also known as ''Jim Henson's Fraggle Rock'' or ''Fraggle Rock with Jim Henson's Muppets'') is a children's musical fantasy comedy puppet television series about interconnected societies of Muppet creatures, created by Jim Henson. An international co-production of Canada, the United Kingdom and the United States, ''Fraggle Rock'' was co-produced by British television company Television South (TVS), the Canadian Broadcasting Corporation (CBC), U.S. pay television service Home Box Office (HBO), and Henson Associates. Unlike ''Sesame Street'', which had been created for a single market and only later adapted for international markets, ''Fraggle Rock'' was intended from the start to be an international production, and the entire show was constructed with this in mind. At least four different versions of the human "wraparound" segments were produced separately to air in different countries. Following the success of the ''Fraggle Rock: Rock On!'' shorts which aire ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
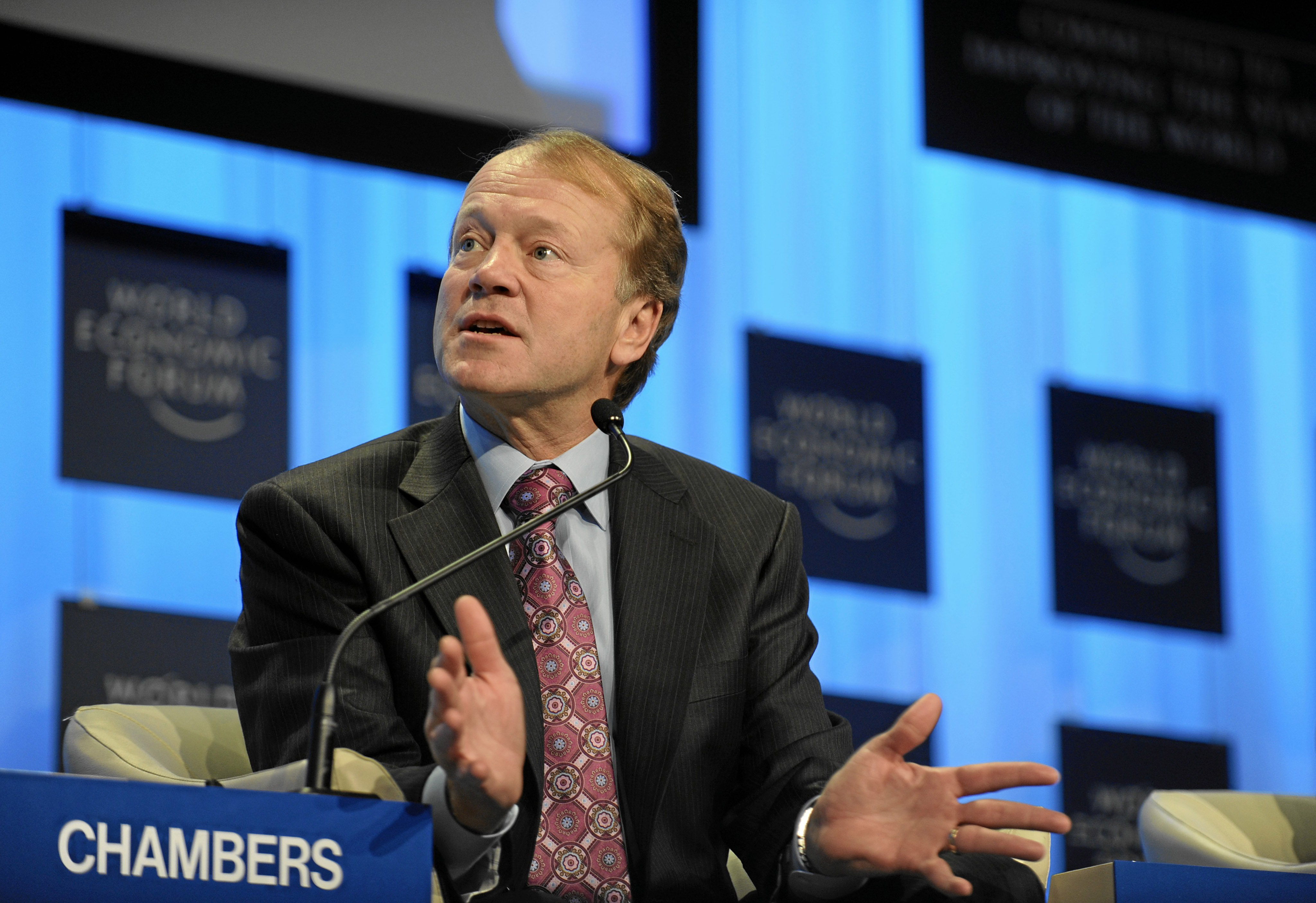
Cisco Systems
Cisco Systems, Inc., commonly known as Cisco, is an American-based multinational corporation, multinational digital communications technology conglomerate (company), conglomerate corporation headquartered in San Jose, California. Cisco develops, manufactures, and sells networking hardware, software, telecommunications equipment and other high-technology services and products. Cisco specializes in specific tech markets, such as the Internet of Things (IoT), internet domain, domain security, videoconferencing, and energy management with List of Cisco products, leading products including Webex, OpenDNS, XMPP, Jabber, Duo Security, and Cisco Jasper, Jasper. Cisco is one of the List of largest technology companies by revenue, largest technology companies in the world ranking 74 on the Fortune 100 with over $51 billion in revenue and nearly 80,000 employees. Cisco Systems was founded in December 1984 by Leonard Bosack and Sandy Lerner, two Stanford University computer scientists who ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ethernet
Ethernet () is a family of wired computer networking technologies commonly used in local area networks (LAN), metropolitan area networks (MAN) and wide area networks (WAN). It was commercially introduced in 1980 and first standardized in 1983 as IEEE 802.3. Ethernet has since been refined to support higher bit rates, a greater number of nodes, and longer link distances, but retains much backward compatibility. Over time, Ethernet has largely replaced competing wired LAN technologies such as Token Ring, FDDI and ARCNET. The original 10BASE5 Ethernet uses coaxial cable as a shared medium, while the newer Ethernet variants use twisted pair and fiber optic links in conjunction with switches. Over the course of its history, Ethernet data transfer rates have been increased from the original to the latest , with rates up to under development. The Ethernet standards include several wiring and signaling variants of the OSI physical layer. Systems communicating over Ethernet ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Control Message Protocol
The Internet Control Message Protocol (ICMP) is a supporting protocol in the Internet protocol suite. It is used by network devices, including routers, to send error messages and operational information indicating success or failure when communicating with another IP address, for example, an error is indicated when a requested service is not available or that a host or router could not be reached. ICMP differs from transport protocols such as TCP and UDP in that it is not typically used to exchange data between systems, nor is it regularly employed by end-user network applications (with the exception of some diagnostic tools like ping and traceroute). ICMP for IPv4 is defined in RFC 792. A separate ICMPv6, defined by RFC 4443, is used with IPv6. Technical details ICMP is part of the Internet protocol suite as defined in RFC 792. ICMP messages are typically used for diagnostic or control purposes or generated in response to errors in IP operations (as specified in RFC 1122 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Broadcasting (networking)
In computer networking, telecommunication and information theory, broadcasting is a method of transferring a message to all recipients simultaneously. Broadcasting can be performed as a high-level operation in a program, for example, broadcasting in Message Passing Interface, or it may be a low-level networking operation, for example broadcasting on Ethernet. All-to-all communication is a computer communication method in which each sender transmits messages to all receivers within a group. In networking this can be accomplished using broadcast or multicast. This is in contrast with the point-to-point method in which each sender communicates with one receiver. Addressing methods There are four principal addressing methods in the Internet Protocol: Overview In computer networking, broadcasting refers to transmitting a packet that will be received by every device on the network. In practice, the scope of the broadcast is limited to a broadcast domain. Broadcasting is the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Unicast
Unicast is data transmission from a single sender (red) to a single receiver (green). Other devices on the network (yellow) do not participate in the communication. In computer networking, unicast is a one-to-one transmission from one point in the network to another point; that is, one sender and one receiver, each identified by a network address. Unicast is in contrast to multicast and broadcast which are one-to-many transmissions. Internet Protocol unicast delivery methods such as Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) are typically used. See also * Anycast * Broadcast, unknown-unicast and multicast traffic * IP address * IP multicast * Routing Routing is the process of selecting a path for traffic in a network or between or across multiple networks. Broadly, routing is performed in many types of networks, including circuit-switched networks, such as the public switched telephone netw ... References External links * * Internet archit ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |