|
Legal Instrument
Legal instrument is a legal term of art that is used for any formally executed written document that can be formally attributed to its author, records and formally expresses a legally enforceable act, process, or contractual duty, obligation, or right, and therefore evidences that act, process, or agreement.''Barron's Law Dictionary'', s.v. "instrument". Examples include a certificate, deed, bond, contract, will, legislative act, notarial act, court writ or process, or any law passed by a competent legislative body in municipal (domestic) or international law. Many legal instruments were written ''under seal'' by affixing a wax or paper seal to the document in evidence of its legal execution and authenticity (which often removed the need for consideration in contract law). However, today many jurisdictions have done away with the requirement of documents being under seal in order to give them legal effect. Electronic legal documents With the onset of the Internet and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Term Of Art
Jargon is the specialized terminology associated with a particular field or area of activity. Jargon is normally employed in a particular communicative context and may not be well understood outside that context. The context is usually a particular occupation (that is, a certain trade, profession, vernacular or academic field), but any ingroup can have jargon. The main trait that distinguishes jargon from the rest of a language is special vocabulary—including some words specific to it and often different senses or meanings of words, that outgroups would tend to take in another sense—therefore misunderstanding that communication attempt. Jargon is sometimes understood as a form of technical slang and then distinguished from the official terminology used in a particular field of activity. The terms ''jargon'', ''slang,'' and ''argot'' are not consistently differentiated in the literature; different authors interpret these concepts in varying ways. According to one definitio ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Seal (device)
A seal is a device for making an impression in Sealing wax, wax, clay, paper, or some other medium, including an embossment on paper, and is also the impression thus made. The original purpose was to authenticate a document, or to prevent interference with a package or envelope by applying a seal which had to be broken to open the container (hence the modern English verb "to seal", which implies secure closing without an actual wax seal). The seal-making device is also referred to as the seal ''matrix'' or ''die''; the imprint it creates as the seal impression (or, more rarely, the ''sealing''). If the impression is made purely as a relief resulting from the greater pressure on the paper where the high parts of the matrix touch, the seal is known as a ''dry seal''; in other cases ink or another liquid or liquefied medium is used, in another color than the paper. In most traditional forms of dry seal the design on the seal matrix is in Intaglio (sculpture), intaglio (cut below th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Legal Coding
Legal coding is the process of creating summary or keyword data from a document. It is widely used in the legal profession to create a fast-search index or database of documents for use in litigation. Objective Coding Definitions * The recording of basic data such as date, author, or document type, from documents into a database. * Extracting information from electronic documents such as date created, author recipient, CC and linking each image to the information in pre-defined objective fields. In direct opposition to Subjective Coding where legal interpretations of data in a document are linked to individual documents. Also called bibliographic coding. * Extracting such information from a document as its author, its mailing date, etc. Objective coding is usually done from the document text or image, because the metadata may be inaccurate. For example, a document written and signed by a partner might show the administrative assistant as the author in the metadata, because it was o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Digital Signature
A digital signature is a mathematical scheme for verifying the authenticity of digital messages or documents. A valid digital signature, where the prerequisites are satisfied, gives a recipient very high confidence that the message was created by a known sender ( authenticity), and that the message was not altered in transit ( integrity). Digital signatures are a standard element of most cryptographic protocol suites, and are commonly used for software distribution, financial transactions, contract management software, and in other cases where it is important to detect forgery or tampering. Digital signatures are often used to implement electronic signatures, which includes any electronic data that carries the intent of a signature, but not all electronic signatures use digital signatures. [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Key
A key in cryptography is a piece of information, usually a string of numbers or letters that are stored in a file, which, when processed through a cryptographic algorithm, can encode or decode cryptographic data. Based on the used method, the key can be different sizes and varieties, but in all cases, the strength of the encryption relies on the security of the key being maintained. A key’s security strength is dependent on its algorithm, the size of the key, the generation of the key, and the process of key exchange. Scope The key is what is used to encrypt data from plaintext to ciphertext. There are different methods for utilizing keys and encryption. Symmetric cryptography Symmetric cryptography refers to the practice of the same key being used for both encryption and decryption. Asymmetric cryptography Asymmetric cryptography has separate keys for encrypting and decrypting. These keys are known as the public and private keys, respectively. Purpose Since the key ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Message Digest
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with fixed size of n bits) that has special properties desirable for cryptography: * the probability of a particular n-bit output result ( hash value) for a random input string ("message") is 2^ (like for any good hash), so the hash value can be used as a representative of the message; * finding an input string that matches a given hash value (a ''pre-image'') is unfeasible, unless the value is selected from a known pre-calculated dictionary ("rainbow table"). The ''resistance'' to such search is quantified as security strength, a cryptographic hash with n bits of hash value is expected to have a ''preimage resistance'' strength of n bits. A ''second preimage'' resistance strength, with the same expectations, refers to a similar problem of finding a second message that matches the given hash value when one message is already known; * finding any pair of different me ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Electronic Signatures In Global And National Commerce Act
The Electronic Signatures in Global and National Commerce Act (ESIGN, , ) is a United States federal law passed by the U.S. Congress to facilitate the use of electronic records and electronic signatures in interstate and foreign commerce by ensuring the validity and legal effect of contracts entered into electronically. Although every state has at least one law pertaining to electronic signatures, it is the federal law that lays out the guidelines for interstate commerce. The general intent of the ESIGN Act is spelled out in the first section (101.a), that a contract or signature “may not be denied legal effect, validity, or enforceability solely because it is in electronic form”. This simple statement provides that electronic signatures and records are just as good as their paper equivalents, and therefore subject to the same legal scrutiny of authenticity that applies to paper documents. [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decipher a ciphertext back to plaintext and access the original information. Encryption does not itself prevent interference but denies the intelligible content to a would-be interceptor. For technical reasons, an encryption scheme usually uses a pseudo-random encryption key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users. Historically, various forms of encryption have been used to aid in cryptography. Early encryption techniques were often used in milit ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an assertion, such as the identity of a computer system user. In contrast with identification, the act of indicating a person or thing's identity, authentication is the process of verifying that identity. It might involve validating personal identity documents, verifying the authenticity of a website with a digital certificate, determining the age of an artifact by carbon dating, or ensuring that a product or document is not counterfeit. Methods Authentication is relevant to multiple fields. In art, antiques, and anthropology, a common problem is verifying that a given artifact was produced by a certain person or in a certain place or period of history. In computer science, verifying a user's identity is often required to allow access to confidential data or systems. Authentication can be considered to be of three types: The first type of a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
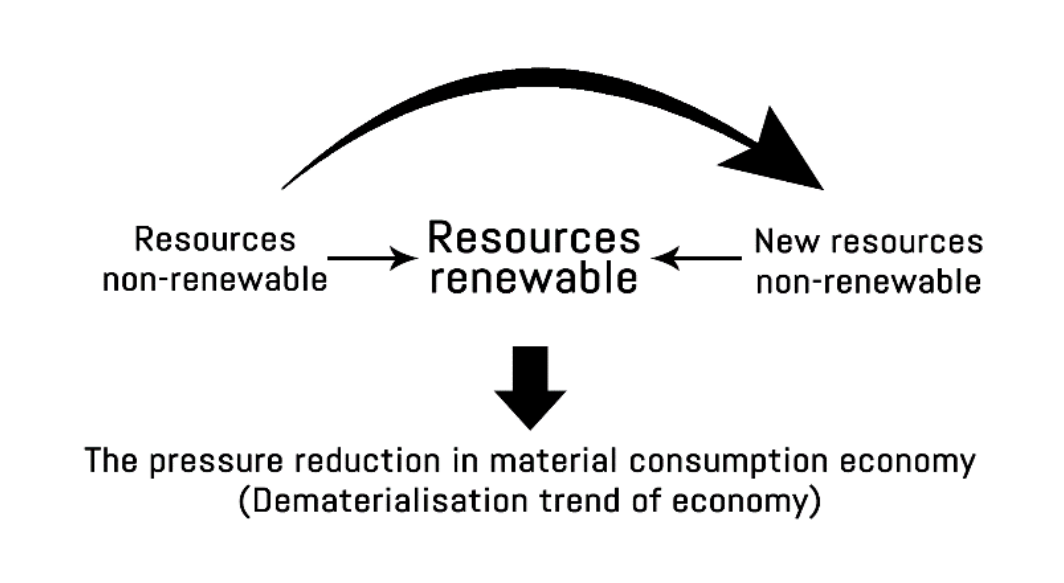
Dematerialization (economics)
Dematerialization is a social science term which describes the process of making more goods with lesser material required. The term itself possessed multi-accentuality, which allows it to be diversely explained by different fields of social science, such as Mainstream economics, which put focus on the aspect of technological evolution and market demand shifts. At the same time, Ecological economics which emphasise the effect of Dematerialization on the natural environment. In economics, dematerialization refers to the absolute or relative reduction in the quantity of materials required to serve economic functions in society. In common terms, dematerialization means doing more with less. This concept is similar to ephemeralization as proposed by Buckminster Fuller. Origin Dematerialization is a phenomenon occurs simultaneously with technological advancement, especially in the Third Industrial revolution products. Miniaturization and optimization of products are enabled by th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Consideration
Consideration is a concept of English common law and is a necessity for simple contracts but not for special contracts (contracts by deed). The concept has been adopted by other common law jurisdictions. The court in '' Currie v Misa'' declared consideration to be a “Right, Interest, Profit, Benefit, or Forbearance, Detriment, Loss, Responsibility”. Thus, consideration is a promise of something of value given by a promissor in exchange for something of value given by a promisee; and typically the thing of value is goods, money, or an act. Forbearance to act, such as an adult promising to refrain from smoking, is enforceable if one is thereby surrendering a legal right. Consideration may be thought of as the concept of value offered and accepted by people or organisations entering into contracts. Anything of value promised by one party to the other when making a contract can be treated as "consideration": for example, if A contracts to buy a car from B for $5,000, A ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an assertion, such as the identity of a computer system user. In contrast with identification, the act of indicating a person or thing's identity, authentication is the process of verifying that identity. It might involve validating personal identity documents, verifying the authenticity of a website with a digital certificate, determining the age of an artifact by carbon dating, or ensuring that a product or document is not counterfeit. Methods Authentication is relevant to multiple fields. In art, antiques, and anthropology, a common problem is verifying that a given artifact was produced by a certain person or in a certain place or period of history. In computer science, verifying a user's identity is often required to allow access to confidential data or systems. Authentication can be considered to be of three types: The first type of a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |

.jpg)