|
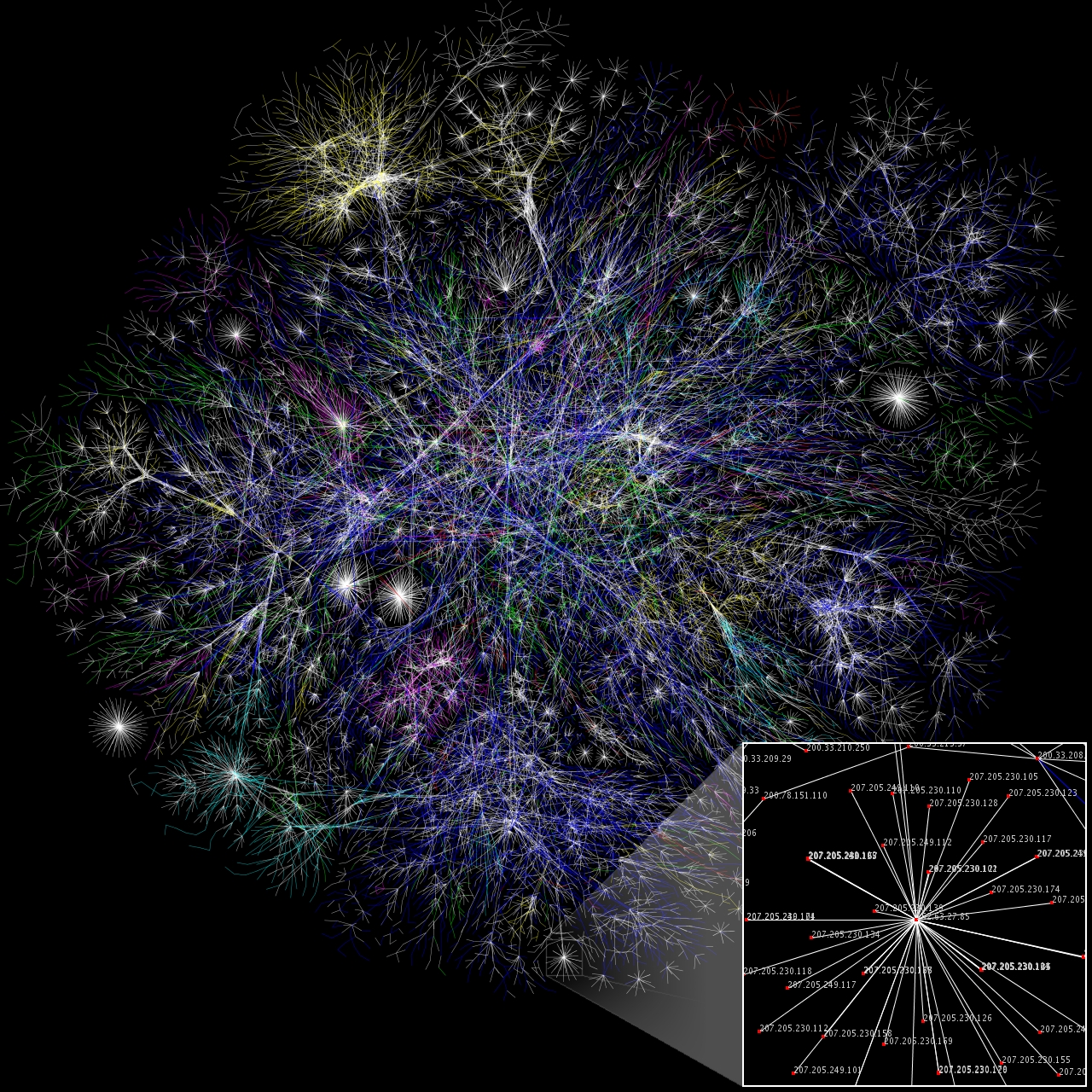
Cybercrime
A cybercrime is a crime that involves a computer or a computer network.Moore, R. (2005) "Cyber crime: Investigating High-Technology Computer Crime," Cleveland, Mississippi: Anderson Publishing. The computer may have been used in committing the crime, or it may be the target. Cybercrime may harm someone's security or finances. There are many privacy concerns surrounding cybercrime when confidential information is intercepted or disclosed, lawfully or otherwise. Internationally, both governmental and non-state actors engage in cybercrimes, including espionage, financial theft, and other cross-border crimes. Cybercrimes crossing international borders and involving the actions of at least one nation-state are sometimes referred to as cyberwarfare. Warren Buffett describes cybercrime as the "number one problem with mankind" and said that cybercrime "poses real risks to humanity." A 2014 report sponsored by McAfee estimated that cybercrime resulted in $445 billion in annual damage ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Carding (fraud)
Carding is a term describing the trafficking and unauthorized use of credit cards. The stolen credit cards or credit card numbers are then used to buy prepaid gift cards to cover up the tracks. Activities also encompass exploitation of personal data, and money laundering techniques. Modern carding sites have been described as full-service commercial entities. Acquisition There are a great many of methods to acquire credit card and associated financial and personal data. The earliest known carding methods have also included "trashing" for financial data, raiding mail boxes and working with insiders. Some bank card numbers can be semi-automatically generated based on known sequences via a "BIN attack". Carders might attempt a "distributed guessing attack" to discover valid numbers by submitting numbers across a high number of ecommerce sites simultaneously. Today, various methodologies include skimmers at ATMs, hacking or web skimming an ecommerce or payment processing ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cybersex Trafficking
Cybersex trafficking, live streaming sexual abuse, webcam sex tourism/abuse or ICTs (Information and Communication Technologies)-facilitated sexual exploitation is a cybercrime involving sex trafficking and the live streaming of coerced sexual acts and/or rape on webcam. Cybersex trafficking is distinct from other sex crimes. Victims are transported by traffickers to 'cybersex dens', which are locations with webcams and internet-connected devices with live streaming software. There, victims are forced to perform sexual acts on themselves or other people in sexual slavery or raped by the traffickers or assisting assaulters in live videos. Victims are frequently ordered to watch the paying live distant consumers or purchasers on shared screens and follow their commands. It is often a commercialized, cyber form of forced prostitution. Women, children, and people in poverty are particularly vulnerable to coerced internet sex. The computer-mediated communication images produced duri ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
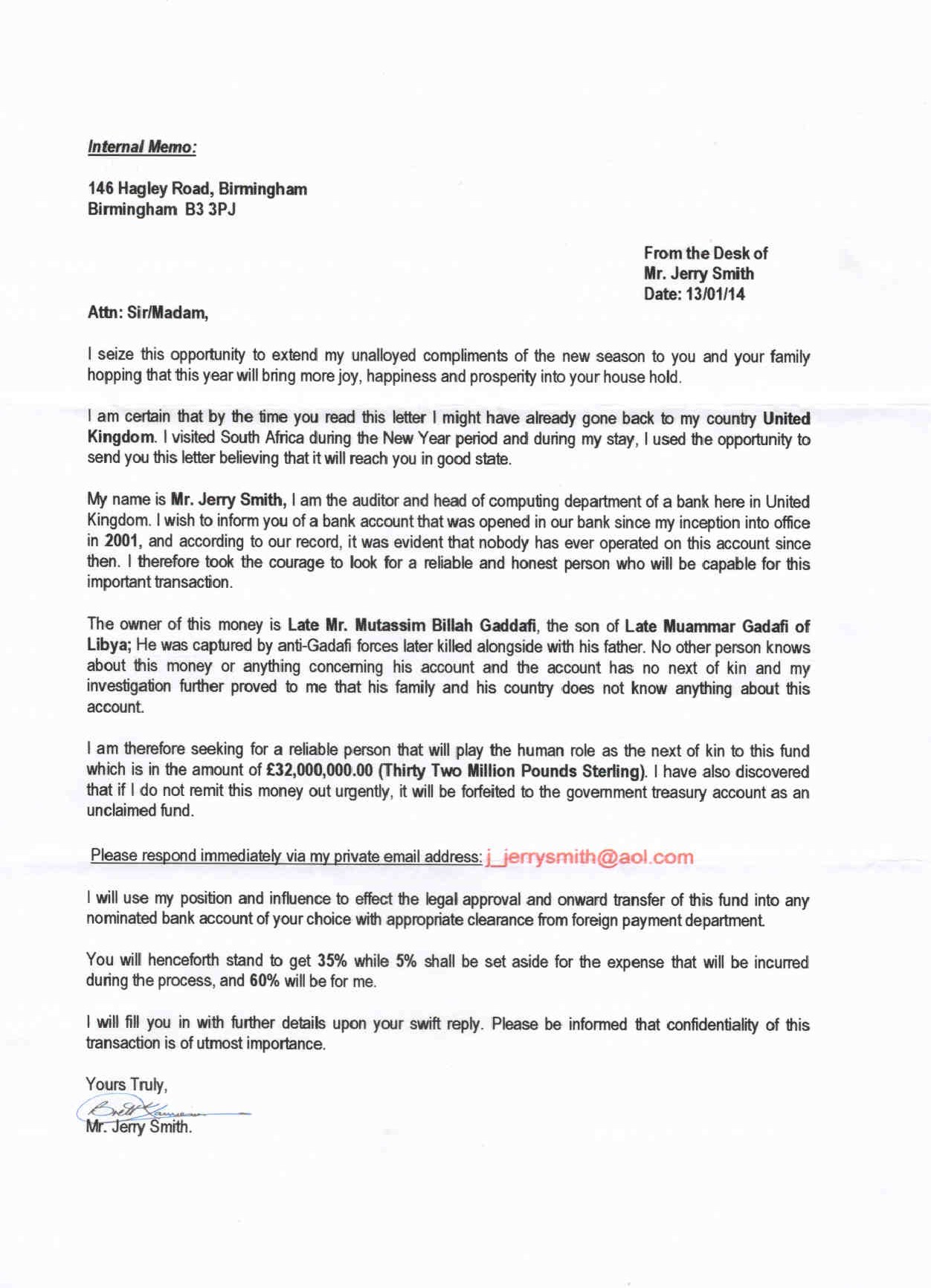
Advance-fee Scam
An advance-fee scam is a form of fraud and is one of the most common types of confidence tricks. The scam typically involves promising the victim a significant share of a large sum of money, in return for a small up-front payment, which the fraudster claims will be used to obtain the large sum. If a victim makes the payment, the fraudster either invents a series of further fees for the victim to pay or simply disappears. FBI. The Federal Bureau of Investigation (FBI) states that "An advance fee scheme occurs when the victim pays money to someone in anticipation of receiving something of greater value - such as a loan, contract, investment, or gift - and then receives little or nothing in return." There are many variations of this type of scam, including the Nigerian prince scam, also known as a 419 scam. The number "419" refers to the section of the Nigerian Criminal Code dealing with fraud and the charges and penalties for such offenders. The scam has been used with fax and tradit ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
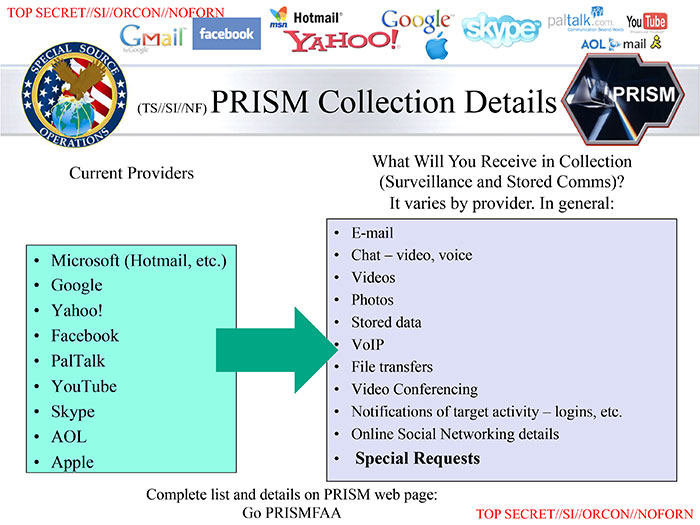
Spyware
Spyware (a portmanteau for spying software) is software with malicious behaviour that aims to gather information about a person or organization and send it to another entity in a way that harms the user—for example, by violating their privacy or endangering their device's security. This behaviour may be present in malware as well as in legitimate software. Websites may engage in spyware behaviours like web tracking. Hardware devices may also be affected. Spyware is frequently associated with advertising and involves many of the same issues. Because these behaviors are so common, and can have non-harmful uses, providing a precise definition of spyware is a difficult task.FTC Report (2005)." History The first recorded use of the term :wikt:spyware, spyware occurred on October 16, 1995 in a Usenet post that poked fun at Microsoft's business model.Vossen, Roland (attributed); October 21, 1995Win 95 Source code in c!!posted to rec..programmer; retrieved from groups.google.co ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberwarfare
Cyberwarfare is the use of cyber attacks against an enemy state, causing comparable harm to actual warfare and/or disrupting vital computer systems. Some intended outcomes could be espionage, sabotage, propaganda, manipulation or economic warfare. There is significant debate among experts regarding the definition of cyberwarfare, and even if such a thing exists. One view is that the term is a misnomer, since no cyber attacks to date could be described as war. An alternative view is that it is a suitable label for cyber attacks which cause physical damage to people and objects in the real world. Many countries including the United States, United Kingdom, Russia, China, Israel, Iran, and North Korea have active cyber capabilities for offensive and defensive operations. As states explore the use of cyber operations and combine capabilities, the likelihood of physical confrontation and violence playing out as a result of, or part of, a cyber operation is increased. However, meeti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Fraud
Internet fraud is a type of cybercrime fraud or deception which makes use of the Internet and could involve hiding of information or providing incorrect information for the purpose of tricking victims out of money, property, and inheritance. Internet fraud is not considered a single, distinctive crime but covers a range of illegal and illicit actions that are committed in cyberspace. It is, however, differentiated from theft since, in this case, the victim voluntarily and knowingly provides the information, money or property to the perpetrator. It is also distinguished by the way it involves temporally and spatially separated offenders. According to the FBI's 2017 Internet Crime Report, the Internet Crime Complaint Center (IC3) received about 300,000 complaints. Victims lost over $1.4 billion in online fraud in 2017. According to a study conducted by the Center for Strategic and International Studies (CSIS) and McAfee, cybercrime costs the global economy as much as $600 billion, w ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious software on the victim's infrastructure like ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim is navigating the site, and transverse any additional security boundaries with the victim. As of 2020, phishing is by far the most common attack performed by cybercriminals, the FBI's Internet Crime Complaint Centre recording over twice as many incidents of phishing than any other type of computer crime. The first recorded use of the term "phishing" was in the cracking toolkit AOHell created by Koceilah Rekouche in 1995; however, it is possible that the term was used before this in a print edition of the hacker magazin ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan horses, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bank Fraud
Bank fraud is the use of potentially illegal means to obtain money, assets, or other property owned or held by a financial institution, or to obtain money from depositors by fraudulently posing as a bank or other financial institution. In many instances, bank fraud is a criminal offence. While the specific elements of particular banking fraud laws vary depending on jurisdictions, the term bank fraud applies to actions that employ a scheme or artifice, as opposed to bank robbery or theft. For this reason, bank fraud is sometimes considered a white-collar crime. Types of bank fraud Accounting fraud In order to hide serious financial problems, some businesses have been known to use fraudulent bookkeeping to overstate sales and income, inflate the worth of the company's assets, or state a profit when the company is operating at a loss. These tampered records are then used to seek investment in the company's bond or security issues or to make fraudulent loan applications in a final ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hack (computer Security)
A security hacker is someone who explores methods for breaching defenses and exploiting weaknesses in a computer system or network. Hackers may be motivated by a multitude of reasons, such as profit, protest, information gathering, challenge, recreation, or evaluation of a system weaknesses to assist in formulating defenses against potential hackers. The subculture that has evolved around hackers is often referred to as the "computer underground". Longstanding controversy surrounds the meaning of the term "hacker." In this controversy, computer programmers reclaim the term ''hacker'', arguing that it refers simply to someone with an advanced understanding of computers and computer networks and that ''cracker'' is the more appropriate term for those who break into computers, whether computer criminals ( black hats) or computer security experts ( white hats). A 2014 article noted that "the black-hat meaning still prevails among the general public". History Birth of subcult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Fraud
Computer fraud is a cybercrime and the act of using a computer to take or alter electronic data, or to gain unlawful use of a computer or system. In the United States, computer fraud is specifically proscribed by the Computer Fraud and Abuse Act, which criminalizes computer-related acts under federal jurisdiction. Types of computer fraud include: *Distributing hoax emails *Accessing unauthorized computers *Engaging in data mining via spyware and malware * Hacking into computer systems to illegally access personal information, such as credit cards or Social Security numbers *Sending computer viruses or worms with the intent to destroy or ruin another party's computer or system. Phishing, social engineering, viruses, and DDoS attacks are fairly well-known tactics used to disrupt service or gain access to another's network, but this list is not inclusive. Notable incidents The Melissa Virus/Worm The Melissa Virus appeared on thousands of email systems on 26 March 1999. It was ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ad Fraud
Ad fraud (also referred to as ''Click Fraud or PPC Fraud)'' is concerned with the practice of fraudulently representing online advertisement impressions, clicks, conversion or data events in order to generate revenue. Ad-frauds are particularly popular among cybercriminals While ad fraud is frequently associated with banner ads, video ads and in-app ads, click fraud has been associated with search marketing, mobile advertising and conversion fraud with affiliate marketing. AppsFlyer estimates financial exposure to app install fraud in Q1 of 2018 was as much as $800 million. Ad fraud is the categorical term inclusive of all forms of online advertising fraud. A successful ad-fraud campaign generally involves a sophisticated combination of Identity fraud and attribution fraud: for instance, sending fake traffic through bots using fake social accounts and falsified cookies; bots will click on the ads available on a scam page that is faking a famous brand. In 2004 Google's CFO Geor ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |