|
VoIP Recording
Voice over Internet Protocol (VoIP) recording is a subset of telephone recording or voice logging, first used by call centers and now being used by all types of businesses. There are many reasons for recording voice over IP call traffic such as: reducing company vulnerability to lawsuits by maintaining recorded evidence, complying with telephone call recording laws, increasing security, employee training and performance reviews, enhancing employee control and alignment, verifying data, sharing data as well as customer satisfaction and enhancing call center agent morale. Operation By definition, Voice over IP is audio converted into digital packets and then converted to IP packets. VoIP recording is accomplished either by sniffing the network or by having the packets duplicated and directed to the recorder—passive recording or active recording, respectively. * Sniffing (passive recording) is done by connecting to the switched port analyzer (SPAN) port which allows the VoIP reco ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Call-recording Software
Mp3/3gpp/wavCall recording software records telephone conversations over PSTN or VoIP in a digital audio file format. Call recording is distinct from call logging and tracking, which record details about the call but not the conversation; however, software may include both recording and logging functionality. Considerations Call recording is becoming increasingly important, with technology changing and working habits becoming more mobile. Addressing mobile recording is now the subject of many financial regulators' recommendations. It is also increasingly important to business continuity planning, especially for pandemic planning. The actual recording takes place on a recording system with software for the management of calls and security of recordings. Most call recording software applications rely on an analogue signal via either a call recording adapter or a telephony board. Digital lines cannot be recorded unless the call recording system can capture and decode the proprietary d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Real-time Transport Protocol
The Real-time Transport Protocol (RTP) is a network protocol for delivering audio and video over IP networks. RTP is used in communication and entertainment systems that involve streaming media, such as telephony, video teleconference applications including WebRTC, television services and web-based push-to-talk features. RTP typically runs over User Datagram Protocol (UDP). RTP is used in conjunction with the RTP Control Protocol (RTCP). While RTP carries the media streams (e.g., audio and video), RTCP is used to monitor transmission statistics and quality of service (QoS) and aids synchronization of multiple streams. RTP is one of the technical foundations of Voice over IP and in this context is often used in conjunction with a signaling protocol such as the Session Initiation Protocol (SIP) which establishes connections across the network. RTP was developed by the Audio-Video Transport Working Group of the Internet Engineering Task Force (IETF) and first published in 1996 a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Surveillance
Surveillance is the monitoring of behavior, many activities, or information for the purpose of information gathering, influencing, managing or directing. This can include observation from a distance by means of electronic equipment, such as closed-circuit television (CCTV), or interception of electronically transmitted information like Internet traffic. It can also include simple technical methods, such as Human intelligence (intelligence gathering), human intelligence gathering and postal interception. Surveillance is used by citizens for protecting their neighborhoods. And by governments for intelligence gathering - including espionage, prevention of crime, the protection of a process, person, group or object, or the investigation of crime. It is also used by criminal organizations to plan and commit crimes, and by businesses to Industrial espionage, gather intelligence on criminals, their competitors, suppliers or customers. Religious organisations charged with detecting he ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Voice Over IP
Voice over Internet Protocol (VoIP), also called IP telephony, is a method and group of technologies for the delivery of speech, voice communications and multimedia sessions over Internet Protocol (IP) networks, such as the Internet. The terms Internet telephony, broadband telephony, and broadband phone service specifically refer to the provisioning of communications services (voice, fax, Short Message Service, SMS, voice-messaging) over the Internet, rather than via the public switched telephone network (PSTN), also known as plain old telephone service (POTS). Overview The steps and principles involved in originating VoIP telephone calls are similar to traditional digital telephony and involve signaling, channel setup, digitization of the analog voice signals, and encoding. Instead of being transmitted over a circuit-switched network, the digital information is packetized and transmission occurs as IP packets over a packet-switched network. They transport media streams using spec ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Telephone Tapping
Telephone tapping (also wire tapping or wiretapping in American English) is the monitoring of telephone and Internet-based conversations by a third party, often by covert means. The wire tap received its name because, historically, the monitoring connection was an actual electrical tap on the telephone line. Legal wiretapping by a government agency is also called lawful interception. Passive wiretapping monitors or records the traffic, while active wiretapping alters or otherwise affects it. Legal status Lawful interception is officially strictly controlled in many countries to safeguard privacy; this is the case in all liberal democracies. In theory, telephone tapping often needs to be authorized by a court, and is again in theory, normally only approved when evidence shows it is not possible to detect criminal or subversive activity in less intrusive ways. Oftentimes, the law and regulations require that the crime investigated must be at least of a certain severity. Illegal ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IP PBX
An IP PBX ("Internet Protocol private branch exchange") is a system that connects telephone extensions to the public switched telephone network (PSTN) and provides internal communication for a business. An IP PBX is a PBX system with IP connectivity and may provide additional audio, video, or instant messaging communication utilizing the TCP/IP protocol stack. Voice over IP (VoIP) gateways can be combined with traditional PBX functionality to allow businesses to use their managed intranet to help reduce long distance expenses and take advantage of the benefits of a single network for voice and data ( converged network). An IP PBX may also provide CTI features. An IP PBX can exist as a physical hardware device or as a software platform. Function IP PBX is primarily a software hosted on a regular desktop or server as per the requirement demands based on the expected traffic & criticality. Till 2019 IP PBX were deployed primarily as inbound and outbound call center solutions for l ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Softphone
A softphone is a software program for making telephone calls over the Internet using a general purpose computer rather than dedicated hardware. The softphone can be installed on a piece of equipment such as a desktop, mobile device, or other computer and allows the user to place and receive calls without requiring an actual telephone set. Often, a softphone is designed to behave like a traditional telephone, sometimes appearing as an image of a handset, with a display panel and buttons with which the user can interact. A softphone is usually used with a headset connected to the sound card of the PC or with a USB phone. Applications See Comparison of VoIP software Communication protocols To communicate, both end-points must support the same voice-over-IP protocol, and at least one common audio codec. Many service providers use the Session Initiation Protocol (SIP) standardized by the Internet Engineering Task Force (IETF). Skype, a popular service, uses proprietary protocols, an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Streaming Audio
Streaming media is multimedia that is delivered and consumed in a continuous manner from a source, with little or no intermediate storage in network elements. ''Streaming'' refers to the delivery method of content, rather than the content itself. Distinguishing delivery method from the media applies specifically to telecommunications networks, as most of the traditional media delivery systems are either inherently ''streaming'' (e.g. radio, television) or inherently ''non-streaming'' (e.g. books, videotape, audio CDs). There are challenges with streaming content on the Internet. For example, users whose Internet connection lacks sufficient bandwidth may experience stops, lags, or poor buffering of the content, and users lacking compatible hardware or software systems may be unable to stream certain content. With the use of buffering of the content for just a few seconds in advance of playback, the quality can be much improved. Livestreaming is the real-time delivery of cont ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Packet Filter
In computing, a firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. A firewall typically establishes a barrier between a trusted network and an untrusted network, such as the Internet. History The term ''firewall'' originally referred to a wall intended to confine a fire within a line of adjacent buildings. Later uses refer to similar structures, such as the metal sheet separating the engine compartment of a vehicle or aircraft from the passenger compartment. The term was applied in the late 1980s to network technology that emerged when the Internet was fairly new in terms of its global use and connectivity. The predecessors to firewalls for network security were routers used in the late 1980s. Because they already segregated networks, routers could apply filtering to packets crossing them. Before it was used in real-life computing, the term appeared in the 1983 computer-hacking movie ' ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Call Center
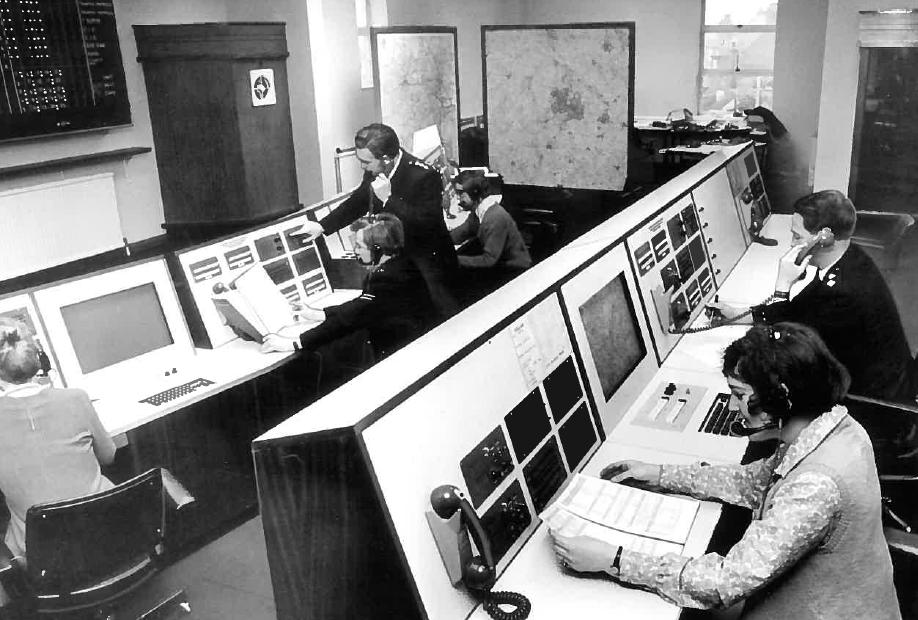
A call centre ( Commonwealth spelling) or call center (American spelling; see spelling differences) is a managed capability that can be centralised or remote that is used for receiving or transmitting a large volume of enquiries by telephone. An inbound call centre is operated by a company to administer incoming product or service support or information enquiries from consumers. Outbound call centres are usually operated for sales purposes such as telemarketing, for solicitation of charitable or political donations, debt collection, market research, emergency notifications, and urgent/critical needs blood banks. A contact centre is a further extension to call centres telephony based capabilities, administers centralised handling of individual communications, including letters, faxes, live support software, social media, instant message, and email. A call center was previously seen to be an open workspace for call center agents, with workstations that include a computer and d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
VLAN
A virtual local area network (VLAN) is any broadcast domain that is partitioned and isolated in a computer network at the data link layer (OSI layer 2).IEEE 802.1Q-2011, ''1.4 VLAN aims and benefits'' In this context, virtual, refers to a physical object recreated and altered by additional logic, within the local area network. VLANs work by applying tags to network frames and handling these tags in networking systems – creating the appearance and functionality of network traffic that is physically on a single network but acts as if it is split between separate networks. In this way, VLANs can keep network applications separate despite being connected to the same physical network, and without requiring multiple sets of cabling and networking devices to be deployed. VLANs allow network administrators to group hosts together even if the hosts are not directly connected to the same network switch. Because VLAN membership can be configured through software, this can greatly simplif ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IP Address
An Internet Protocol address (IP address) is a numerical label such as that is connected to a computer network that uses the Internet Protocol for communication.. Updated by . An IP address serves two main functions: network interface identification and location addressing. Internet Protocol version 4 (IPv4) defines an IP address as a 32-bit number. However, because of the growth of the Internet and the depletion of available IPv4 addresses, a new version of IP (IPv6), using 128 bits for the IP address, was standardized in 1998. IPv6 deployment has been ongoing since the mid-2000s. IP addresses are written and displayed in human-readable notations, such as in IPv4, and in IPv6. The size of the routing prefix of the address is designated in CIDR notation by suffixing the address with the number of significant bits, e.g., , which is equivalent to the historically used subnet mask . The IP address space is managed globally by the Internet Assigned Numbers Authority (IA ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |