|
Tunnelling Protocol
In computer networks, a tunneling protocol is a communication protocol which allows for the movement of data from one network to another. They can, for example, allow private network communications to be sent across a public network (such as the Internet), or for one network protocol to be carried over an incompatible network, through a process called encapsulation. Because tunneling involves repackaging the traffic data into a different form, perhaps with encryption as standard, it can hide the nature of the traffic that is run through a tunnel. Tunneling protocols work by using the data portion of a packet (the payload) to carry the packets that actually provide the service. Tunneling uses a layered protocol model such as those of the OSI or TCP/IP protocol suite, but usually violates the layering when using the payload to carry a service not normally provided by the network. Typically, the delivery protocol operates at an equal or higher level in the layered model than the p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Computer Network
A computer network is a collection of communicating computers and other devices, such as printers and smart phones. In order to communicate, the computers and devices must be connected by wired media like copper cables, optical fibers, or by wireless communication. The devices may be connected in a variety of network topologies. In order to communicate over the network, computers use agreed-on rules, called communication protocols, over whatever medium is used. The computer network can include personal computers, Server (computing), servers, networking hardware, or other specialized or general-purpose Host (network), hosts. They are identified by network addresses and may have hostnames. Hostnames serve as memorable labels for the nodes and are rarely changed after initial assignment. Network addresses serve for locating and identifying the nodes by communication protocols such as the Internet Protocol. Computer networks may be classified by many criteria, including the tr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Point-to-Point Tunneling Protocol
The Point-to-Point Tunneling Protocol (PPTP) is an obsolete method for implementing virtual private networks. PPTP has many well known security issues. PPTP uses a TCP control channel and a Generic Routing Encapsulation tunnel to encapsulate PPP packets. Many modern VPNs use various forms of UDP for this same functionality. The PPTP specification does not describe encryption or authentication features and relies on the Point-to-Point Protocol being tunneled to implement any and all security functionalities. The PPTP implementation that ships with the Microsoft Windows product families implements various levels of authentication and encryption natively as standard features of the Windows PPTP stack. The intended use of this protocol is to provide security levels and remote access levels comparable with typical VPN products. History A specification for PPTP was published in July 1999 as RFC 2637 and was developed by a vendor consortium formed by Microsoft, Ascend Commu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Virtual Extensible LAN
Virtual eXtensible LAN (VXLAN) is a network virtualization technology that uses a VLAN-like encapsulation technique to encapsulate OSI layer 2 Ethernet frames within layer 4 UDP datagrams, using 4789 as the default IANA-assigned destination UDP port number, although many implementations that predate the IANA assignment use port 8472. VXLAN attempts to address the scalability problems associated with large cloud computing deployments. VXLAN endpoints, which terminate VXLAN tunnels and may be either virtual or physical switch ports, are known as VXLAN tunnel endpoints (VTEPs). History VXLAN is an evolution of efforts to standardize on an overlay encapsulation protocol. Compared to single-tagged IEEE 802.1Q VLANs which provide a limited number of layer-2 VLANs (4094, using a 12-bit VLAN ID), VXLAN increases scalability up to about 16 million logical networks (using a 24-bit VNID) and allows for layer-2 adjacency across IP networks. Multicast or unicast with head-end replication ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
L2TPv3
Layer 2 Tunneling Protocol version 3 is an IETF standard related to L2TP that can be used as an alternative protocol to Multiprotocol Label Switching (MPLS) for encapsulation of multiprotocol Layer 2 communications traffic over IP networks. Like L2TP, L2TPv3 provides a pseudo-wire service, but scaled to fit carrier requirements. L2TPv3 can be regarded as being to MPLS what IP is to ATM: a simplified version of the same concept, with much of the same benefit achieved at a fraction of the effort, at the cost of losing some technical features considered less important in the market. In the case of L2TPv3, the features lost are teletraffic engineering Teletraffic engineering, or telecommunications traffic engineering is the application of transportation traffic engineering theory to telecommunications. Teletraffic engineers use their knowledge of statistics including queuing theory, the natu ... features considered important in MPLS. However, there is no reason these featu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Secure Socket Tunneling Protocol
In computer networking, Secure Socket Tunneling Protocol (SSTP) is a form of virtual private network (VPN) tunnel that provides a mechanism to transport Point-to-Point Protocol (PPP) traffic through an SSL/TLS channel. Protocol SSL/TLS provides transport-level security with key negotiation, encryption and traffic integrity checking. The use of SSL/TLS over TCP port 443 (by default; port can be changed) allows SSTP to pass through virtually all firewalls and proxy servers except for authenticated web proxies. SSTP servers must be authenticated during the SSL/TLS phase. SSTP clients can optionally be authenticated during the SSL/TLS phase and must be authenticated in the PPP phase. The use of PPP allows support for common authentication methods, such as EAP-TLS and MS-CHAP. SSTP is available for Linux, BSD, and Windows. SSTP was introduced in 2007 and available on Windows Vista SP1 and later, in RouterOS since version 5.0, and in SEIL since its firmware version 3.50. It ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
OpenVPN
OpenVPN is a virtual private network (VPN) system that implements techniques to create secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It implements both client and server applications. OpenVPN allows peers to authenticate each other using pre-shared secret keys, certificates or username/password. When used in a multiclient-server configuration, it allows the server to release an authentication certificate for every client, using signatures and certificate authority. It uses the OpenSSL encryption library extensively, as well as the TLS protocol, and contains many security and control features. It uses a custom security protocol that utilizes SSL/TLS for key exchange. It is capable of traversing network address translators (NATs) and firewalls. OpenVPN has been ported and embedded to several systems. For example, DD-WRT has the OpenVPN server function. SoftEther VPN, a multi-protocol VPN server, also ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
6in4
6in4, sometimes referred to as SIT, is an IPv6 transition mechanism for migrating from Internet Protocol version 4 (IPv4) to IPv6. It is a tunneling protocol that encapsulates IPv6 packets on specially configured IPv4 links according to the specifications of . The IP protocol number for 6in4 is ''41'', per IANA reservation. The 6in4 packet format consists of the IPv6 packet preceded by an IPv4 packet header. Thus, the encapsulation overhead is the size of the IPv4 header of 20 bytes. On Ethernet with a maximum transmission unit (MTU) of 1500 bytes, IPv6 packets of 1480 bytes may therefore be transmitted without fragmentation. 6in4 tunneling is also referred to as ''proto-41 static'' because the endpoints are configured statically. Although 6in4 tunnels are generally manually configured, the utility AICCU can configure tunnel parameters automatically after retrieving information from a Tunnel Information and Control Protocol (TIC) server. The similarly named methods 6to4 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
IP In IP
IP most often refers to: * Intellectual property, creations of the mind for which exclusive legal rights are recognized * Internet Protocol, a set of rules for sending data across a network IP or Ip or ip may also refer to: Businesses and organizations * IP College (Indraprastha College for boys), a constituent college of the University of Delhi, New Delhi, India * Imperial Police, a former Indian police agency * '' Inicjatywa Pracownicza'' (Workers' Initiative), a Polish trade union * International Paper, an American pulp and paper company * Iraqi Police * Atyrau Airways (IATA code: IP) * Italiana Petroli, an Italian petroleum brand owned by Anonima Petroli Italiana Places * Ipswich, for Ipswich and surrounding areas, England * Ip, Sălaj, Romania * Ip (river), a river in Sălaj County, Romania * IP Casino Resort Spa, in Biloxi, Mississippi, US Science and technology Biology and medicine * Immunoprecipitation, a molecular biology technique * Incontinentia pigmenti, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
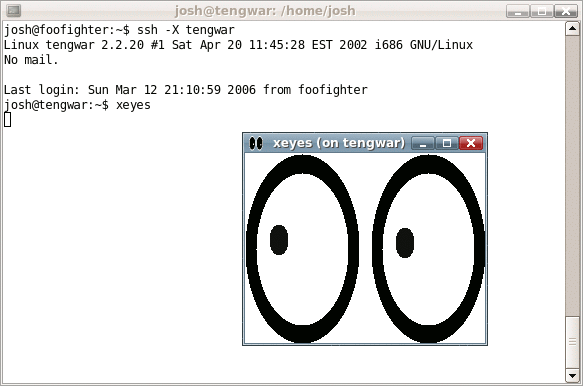
Secure Shell
The Secure Shell Protocol (SSH Protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. Its most notable applications are remote login and command-line execution. SSH was designed for Unix-like operating systems as a replacement for Telnet and unsecured remote Unix shell protocols, such as the Berkeley Remote Shell (rsh) and the related rlogin and rexec protocols, which all use insecure, plaintext methods of authentication, like passwords. Since mechanisms like Telnet and Remote Shell are designed to access and operate remote computers, sending the authentication tokens (e.g. username and password) for this access to these computers across a public network in an unsecured way poses a great risk of 3rd parties obtaining the password and achieving the same level of access to the remote system as the telnet user. Secure Shell mitigates this risk through the use of encryption mechanisms that are intended to hide th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |