|
Systrace
Systrace is a computer security utility which limits an application's access to the system by enforcing access policies for system calls. This can mitigate the effects of buffer overflows and other security vulnerabilities. It was developed by Niels Provos and runs on various Unix-like operating systems. Systrace is particularly useful when running untrusted or binary-only applications and provides facilities for privilege elevation on a system call basis, helping to eliminate the need for potentially dangerous setuid programs. It also includes interactive and automatic policy generation features, to assist in the creation of a base policy for an application. Systrace used to be integrated into OpenBSD, but was removed in April 2016 (in favour of ''pledge'' post OpenBSD 5.9). It is available for Linux and Mac OS X, although the OS X port is currently unmaintained. It was removed from NetBSD at the end of 2007 due to several unfixed implementation issues. As of version 1.6f Systra ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Niels Provos
Niels Provos is a German-American researcher in security engineering, malware, and cryptography. He received a PhD in computer science from the University of Michigan. From 2003 to 2018, he worked at Google as a Distinguished Engineer on security for Google Cloud Platform. In 2018, he left Google to join Stripe as its new head of security. For many years, Provos contributed to the OpenBSD operating system, where he developed the bcrypt adaptive cryptographic hash function. He is the author of numerous software packages, including the libevent event driven programming system, the Systrace access control system, the honeyd honeypot system, the StegDetect steganography detector, the Bcrypt password encryption technique, and many others. Provos has been an outspoken critic of the effect of the DMCA and similar laws on security researchers, arguing that they threaten to make criminals of people conducting legitimate security research. Provos has also served as the Program Chair of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mandatory Access Control
In computer security, mandatory access control (MAC) refers to a type of access control by which the operating system or database constrains the ability of a ''subject'' or ''initiator'' to access or generally perform some sort of operation on an ''object'' or ''target''. In the case of operating systems, a subject is usually a process or thread; objects are constructs such as files, directories, TCP/ UDP ports, shared memory segments, IO devices, etc. Subjects and objects each have a set of security attributes. Whenever a subject attempts to access an object, an authorization rule enforced by the operating system kernel examines these security attributes and decides whether the access can take place. Any operation by any subject on any object is tested against the set of authorization rules (aka ''policy'') to determine if the operation is allowed. A database management system, in its access control mechanism, can also apply mandatory access control; in this case, the objects ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
AppArmor
AppArmor ("Application Armor") is a Linux kernel security module that allows the system administrator to restrict programs' capabilities with per-program profiles. Profiles can allow capabilities like network access, raw socket access, and the permission to read, write, or execute files on matching paths. AppArmor supplements the traditional Unix discretionary access control (DAC) model by providing mandatory access control (MAC). It has been partially included in the mainline Linux kernel since version 2.6.36 and its development has been supported by Canonical since 2009. Details In addition to manually creating profiles, AppArmor includes a learning mode, in which profile violations are logged, but not prevented. This log can then be used for generating an AppArmor profile, based on the program's typical behavior. AppArmor is implemented using the Linux Security Modules (LSM) kernel interface. AppArmor is offered in part as an alternative to SELinux, which critics consi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Linux
Linux ( or ) is a family of open-source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically packaged as a Linux distribution, which includes the kernel and supporting system software and libraries, many of which are provided by the GNU Project. Many Linux distributions use the word "Linux" in their name, but the Free Software Foundation uses the name "GNU/Linux" to emphasize the importance of GNU software, causing some controversy. Popular Linux distributions include Debian, Fedora Linux, and Ubuntu, the latter of which itself consists of many different distributions and modifications, including Lubuntu and Xubuntu. Commercial distributions include Red Hat Enterprise Linux and SUSE Linux Enterprise. Desktop Linux distributions include a windowing system such as X11 or Wayland, and a desktop environment such as GNOME or KDE Plasma. Distributions intended for ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
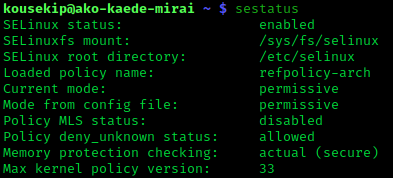
SELinux
Security-Enhanced Linux (SELinux) is a Linux kernel security module that provides a mechanism for supporting access control security policies, including mandatory access controls (MAC). SELinux is a set of kernel modifications and user-space tools that have been added to various Linux distributions. Its architecture strives to separate enforcement of security decisions from the security policy, and streamlines the amount of software involved with security policy enforcement. The key concepts underlying SELinux can be traced to several earlier projects by the United States National Security Agency (NSA). Overview The NSA Security-enhanced Linux Team describes NSA SELinux as a set of patches to the Linux kernel and utilities to provide a strong, flexible, mandatory access control (MAC) architecture into the major subsystems of the kernel. It provides an enhanced mechanism to enforce the separation of information based on confidentiality and integrity requirements, which allow ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Seccomp
seccomp (short for secure computing mode) is a computer security facility in the Linux kernel. seccomp allows a process to make a one-way transition into a "secure" state where it cannot make any system calls except exit(), sigreturn(), read() and write() to already-open file descriptors. Should it attempt any other system calls, the kernel will either just log the event or terminate the process with SIGKILL or SIGSYS. In this sense, it does not virtualize the system's resources but isolates the process from them entirely. seccomp mode is enabled via the system call using the PR_SET_SECCOMP argument, or (since Linux kernel 3.17) via the system call. seccomp mode used to be enabled by writing to a file, /proc/self/seccomp, but this method was removed in favor of prctl(). In some kernel versions, seccomp disables the RDTSC x86 instruction, which returns the number of elapsed processor cycles since power-on, used for high-precision timing. seccomp-bpf is an extension to secc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Robert Watson (computer Scientist)
Robert Nicholas Maxwell Watson (born 3 May 1977) is a FreeBSD developer, and founder of the TrustedBSD Project. He is currently employed as a Professor of Systems, Security, and Architecture in the Security Research Group at the University of Cambridge Computer Laboratory.https://www.cst.cam.ac.uk/news/plethora-professors Announcement of Professorship Education Watson graduated in computer science from Carnegie Mellon University and has attained a PhD from University of Cambridge. As well as Cambridge, he has worked at the National Institutes of Health, Carnegie Mellon University, Trusted Information Systems, Network Associates, McAfee, and SPARTA. He obtained a PhD in computer security from the University of Cambridge Computer Laboratory, supervised by Ross Anderson and sponsored by Google. Research Watson's work has been supported by DARPA, Apple Computer, the Navy, and other US government agencies. His main research interests are network security and operating system se ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Raw Socket
A network socket is a software structure within a network node of a computer network that serves as an endpoint for sending and receiving data across the network. The structure and properties of a socket are defined by an application programming interface (API) for the networking architecture. Sockets are created only during the lifetime of a process of an application running in the node. Because of the standardization of the TCP/IP protocols in the development of the Internet, the term ''network socket'' is most commonly used in the context of the Internet protocol suite, and is therefore often also referred to as Internet socket. In this context, a socket is externally identified to other hosts by its socket address, which is the triad of transport protocol, IP address, and port number. The term ''socket'' is also used for the software endpoint of node-internal inter-process communication (IPC), which often uses the same API as a network socket. Use The use of the term ''soc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
NetBSD
NetBSD is a free and open-source Unix operating system based on the Berkeley Software Distribution (BSD). It was the first open-source BSD descendant officially released after 386BSD was forked. It continues to be actively developed and is available for many platforms, including servers, desktops, handheld devices, and embedded systems. The NetBSD project focuses on code clarity, careful design, and portability across many computer architectures. Its source code is publicly available and permissively licensed. History NetBSD was originally derived from the 4.3BSD-Reno release of the Berkeley Software Distribution from the Computer Systems Research Group of the University of California, Berkeley, via their Net/2 source code release and the 386BSD project. The NetBSD project began as a result of frustration within the 386BSD developer community with the pace and direction of the operating system's development. The four founders of the NetBSD project, Chris Demetriou, The ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mac OS X
macOS (; previously OS X and originally Mac OS X) is a Unix operating system developed and marketed by Apple Inc. since 2001. It is the primary operating system for Apple's Mac computers. Within the market of desktop and laptop computers it is the second most widely used desktop OS, after Microsoft Windows and ahead of ChromeOS. macOS succeeded the classic Mac OS, a Mac operating system with nine releases from 1984 to 1999. During this time, Apple cofounder Steve Jobs had left Apple and started another company, NeXT, developing the NeXTSTEP platform that would later be acquired by Apple to form the basis of macOS. The first desktop version, Mac OS X 10.0, was released in March 2001, with its first update, 10.1, arriving later that year. All releases from Mac OS X 10.5 Leopard and after are UNIX 03 certified, with an exception for OS X 10.7 Lion. Apple's other operating systems (iOS, iPadOS, watchOS, tvOS, audioOS) are derivatives of macOS. A prominent pa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
OpenBSD
OpenBSD is a security-focused operating system, security-focused, free and open-source, Unix-like operating system based on the Berkeley Software Distribution (BSD). Theo de Raadt created OpenBSD in 1995 by fork (software development), forking NetBSD 1.0. According to the website, the OpenBSD project emphasizes "portability, standardization, correctness, proactive security and integrated cryptography." The OpenBSD project maintains software portability, portable versions of many subsystems as package manager, packages for other operating systems. Because of the project's preferred BSD license, many components are reused in proprietary and corporate-sponsored software projects. The firewall (computing), firewall code in Apple Inc., Apple's macOS is based on OpenBSD's PF (firewall), PF firewall code, Android (operating system), Android's Bionic (software), Bionic C standard library is based on OpenBSD code, LLVM uses OpenBSD's regular expression library, and Windows 10 uses OpenSSH ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Unix-like
A Unix-like (sometimes referred to as UN*X or *nix) operating system is one that behaves in a manner similar to a Unix system, although not necessarily conforming to or being certified to any version of the Single UNIX Specification. A Unix-like application is one that behaves like the corresponding Unix command or shell. Although there are general philosophies for Unix design, there is no technical standard defining the term, and opinions can differ about the degree to which a particular operating system or application is Unix-like. Some well-known examples of Unix-like operating systems include Linux and BSD. These systems are often used on servers, as well as on personal computers and other devices. Many popular applications, such as the Apache web server and the Bash shell, are also designed to be used on Unix-like systems. One of the key features of Unix-like systems is their ability to support multiple users and processes simultaneously. This allows users to run mult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
.jpg)