|
Snake Oil (cryptography)
In cryptography, snake oil is any cryptographic method or product considered to be bogus or fraudulent. The name derives from snake oil, one type of patent medicine widely available in 19th century United States. Distinguishing secure cryptography from insecure cryptography can be difficult from the viewpoint of a user. Many cryptographers, such as Bruce Schneier and Phil Zimmermann, undertake to educate the public in how secure cryptography is done, as well as highlighting the misleading marketing of some cryptographic products. The ''Snake Oil FAQ'' describes itself as, "a compilation of common habits of snake oil vendors. It cannot be the sole method of rating a security product, since there can be exceptions to most of these rules. ../nowiki> But if you're looking at something that exhibits several warning signs, you're probably dealing with snake oil." Some examples of snake oil cryptography techniques This is not an exhaustive list of snake oil signs. A more thorough li ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security (data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synony ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
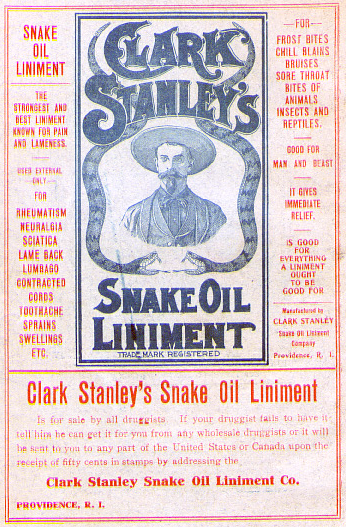
Snake Oil
Snake oil is a term used to describe deceptive marketing, health care fraud, or a scam. Similarly, "snake oil salesman" is a common expression used to describe someone who sells, promotes, or is a general proponent of some valueless or fraudulent cure, remedy, or solution. The term comes from the "snake oil" that used to be sold as a cure-all elixir for many kinds of physiological problems. Many 19th-century United States and 18th-century European entrepreneurs advertised and sold mineral oil (often mixed with various active and inactive household herbs, spices, drugs, and compounds, but containing no snake-derived substances whatsoever) as "snake oil liniment", making claims about its efficacy as a panacea. Patent medicines that claimed to be a panacea were extremely common from the 18th century until the 20th, particularly among vendors masking addictive drugs such as cocaine, amphetamine, alcohol, and opium-based concoctions or elixirs, to be sold at medicine shows ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Patent Medicine
A patent medicine, sometimes called a proprietary medicine, is an over-the-counter (nonprescription) medicine or medicinal preparation that is typically protected and advertised by a trademark and trade name (and sometimes a patent) and claimed to be effective against minor disorders and symptoms. Its contents are typically incompletely disclosed. Antiseptics, analgesics, some sedatives, laxatives, and antacids, cold and cough medicines, and various skin preparations are included in the group. The safety and effectiveness of patent medicines and their sale is controlled and regulated by the Food and Drug Administration in the United States and corresponding authorities in other countries.https://www.merriam-webster.com/dictionary/patent%20medicine The term is sometimes still used to describe quack remedies of unproven effectiveness and questionable safety sold especially by peddlers in past centuries, who often also called them elixirs, tonics, or liniments. Current exam ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
United States
The United States of America (U.S.A. or USA), commonly known as the United States (U.S. or US) or America, is a country primarily located in North America. It consists of 50 U.S. state, states, a Washington, D.C., federal district, five major unincorporated territories, nine United States Minor Outlying Islands, Minor Outlying Islands, and 326 Indian reservations. The United States is also in Compact of Free Association, free association with three Oceania, Pacific Island Sovereign state, sovereign states: the Federated States of Micronesia, the Marshall Islands, and the Palau, Republic of Palau. It is the world's List of countries and dependencies by area, third-largest country by both land and total area. It shares land borders Canada–United States border, with Canada to its north and Mexico–United States border, with Mexico to its south and has maritime borders with the Bahamas, Cuba, Russia, and other nations. With a population of over 333 million, it is the List of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bruce Schneier
Bruce Schneier (; born January 15, 1963) is an American cryptographer, computer security professional, privacy specialist, and writer. Schneier is a Lecturer in Public Policy at the Harvard Kennedy School and a Fellow at the Berkman Klein Center for Internet & Society as of November, 2013. He is a board member of the Electronic Frontier Foundation, Access Now, and The Tor Project; and an advisory board member of Electronic Privacy Information Center and VerifiedVoting.org. He is the author of several books on general security topics, computer security and cryptography and is a squid enthusiast. In 2015, Schneier received the EPIC Lifetime Achievement Award from Electronic Privacy Information Center. Early life Bruce Schneier is the son of Martin Schneier, a Brooklyn Supreme Court judge. He grew up in the Flatbush neighborhood of Brooklyn, New York, attending P.S. 139 and Hunter College High School. After receiving a physics bachelor's degree from the University of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Phil Zimmermann
Philip R. Zimmermann (born 1954) is an American computer scientist and cryptographer. He is the creator of Pretty Good Privacy (PGP), the most widely used email encryption software in the world. He is also known for his work in VoIP encryption protocols, notably ZRTP and Zfone. Zimmermann is co-founder and Chief Scientist of the global encrypted communications firm Silent Circle. Background He was born in Camden, New Jersey. Zimmermann received a B.S. degree in computer science from Florida Atlantic University in Boca Raton, Florida in 1978. In the 1980s, Zimmermann worked in Boulder, Colorado as a software engineer on the Nuclear Weapons Freeze Campaign as a military policy analyst. PGP In 1991, he wrote the popular Pretty Good Privacy (PGP) program, and made it available (together with its source code) through public FTP for download, the first widely available program implementing public-key cryptography. Shortly thereafter, it became available overseas via the Int ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security Through Obscurity
Security through obscurity (or security by obscurity) is the reliance in security engineering on design or implementation secrecy as the main method of providing security to a system or component. History An early opponent of security through obscurity was the locksmith Alfred Charles Hobbs, who in 1851 demonstrated to the public how state-of-the-art locks could be picked. In response to concerns that exposing security flaws in the design of locks could make them more vulnerable to criminals, he said: "Rogues are very keen in their profession, and know already much more than we can teach them." There is scant formal literature on the issue of security through obscurity. Books on security engineering cite Kerckhoffs' doctrine from 1883, if they cite anything at all. For example, in a discussion about secrecy and openness in Nuclear Command and Control: e benefits of reducing the likelihood of an accidental war were considered to outweigh the possible benefits of secrecy. This ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kerckhoffs's Principle
Kerckhoffs's principle (also called Kerckhoffs's desideratum, assumption, axiom, doctrine or law) of cryptography was stated by Dutch-born cryptographer Auguste Kerckhoffs in the 19th century. The principle holds that a cryptosystem should be secure, even if everything about the system, except the key, is public knowledge. This concept is widely embraced by cryptographers, in contrast to security through obscurity, which is not. Kerckhoffs's principle was phrased by American mathematician Claude Shannon as "the enemy knows the system", i.e., "one ought to design systems under the assumption that the enemy will immediately gain full familiarity with them". In that form, it is called Shannon's maxim. Another formulation by American researcher and professor Steven M. Bellovin is: In other words — design your system assuming that your opponents know it in detail. (A former official at NSA's National Computer Security Center told me that the standard assumption there was that se ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Peer Review
Peer review is the evaluation of work by one or more people with similar competencies as the producers of the work ( peers). It functions as a form of self-regulation by qualified members of a profession within the relevant field. Peer review methods are used to maintain quality standards, improve performance, and provide credibility. In academia, scholarly peer review is often used to determine an academic paper's suitability for publication. Peer review can be categorized by the type of activity and by the field or profession in which the activity occurs, e.g., medical peer review. It can also be used as a teaching tool to help students improve writing assignments. Henry Oldenburg (1619–1677) was a German-born British philosopher who is seen as the 'father' of modern scientific peer review. Professional Professional peer review focuses on the performance of professionals, with a view to improving quality, upholding standards, or providing certification. In academia, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptanalysis
Cryptanalysis (from the Greek ''kryptós'', "hidden", and ''analýein'', "to analyze") refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown. In addition to mathematical analysis of cryptographic algorithms, cryptanalysis includes the study of side-channel attacks that do not target weaknesses in the cryptographic algorithms themselves, but instead exploit weaknesses in their implementation. Even though the goal has been the same, the methods and techniques of cryptanalysis have changed drastically through the history of cryptography, adapting to increasing cryptographic complexity, ranging from the pen-and-paper methods of the past, through machines like the British Bombes and Colossus computers at Bletchley Park in World War II, to the mathematically advance ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Technobabble
Technobabble (a portmanteau of ''technology'' and ''babble''), also called technospeak, is a type of nonsense that consists of buzzwords, esoteric language, or technical jargon. It is common in science fiction. See also * Academese * Bullshit * Bogdanov affair * Dihydrogen monoxide parody * Flux capacitor * Fedspeak * Neologism * Officialese * Psychobabble * Rubber science * Sokal affair The Sokal affair, also called the Sokal hoax, was a demonstrative scholarly hoax performed by Alan Sokal, a physics professor at New York University and University College London. In 1996, Sokal submitted an article to ''Social Text'', an acade ... * Turboencabulator References External links Technology Column called Technobabble [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
One-time Pad
In cryptography, the one-time pad (OTP) is an encryption technique that cannot be cracked, but requires the use of a single-use pre-shared key that is not smaller than the message being sent. In this technique, a plaintext is paired with a random secret key (also referred to as ''a one-time pad''). Then, each bit or character of the plaintext is encrypted by combining it with the corresponding bit or character from the pad using modular addition. The resulting ciphertext will be impossible to decrypt or break if the following four conditions are met: #The key must be at least as long as the plaintext. #The key must be random ( uniformly distributed in the set of all possible keys and independent of the plaintext), entirely sampled from a non-algorithmic, chaotic source such as a hardware random number generator. It is not sufficient for OTP keys to pass statistical randomness tests as such tests cannot measure entropy, and the number of bits of entropy must be at least ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |