|
Security Kernel
In telecommunication, the term security kernel has the following meanings: #In computer and communications security, the central part of a computer or communications system hardware, firmware, and software that implements the basic security procedures for controlling access to system resources. #A self-contained usually small collection of key security-related statements that (a) works as a part of an operating system to prevent unauthorized access to, or use of, the system and (b) contains criteria that must be met before specified programs can be accessed. #Hardware, firmware, and software elements of a trusted computing base that implement the reference monitor concept. References *{{FS1037C *National Information Systems Security Glossary Committee on National Security Systems Instruction No. 4009, National Information Assurance Glossary, published by the United States federal government, is an unclassified glossary of Information security terms intended to provide ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Telecommunication
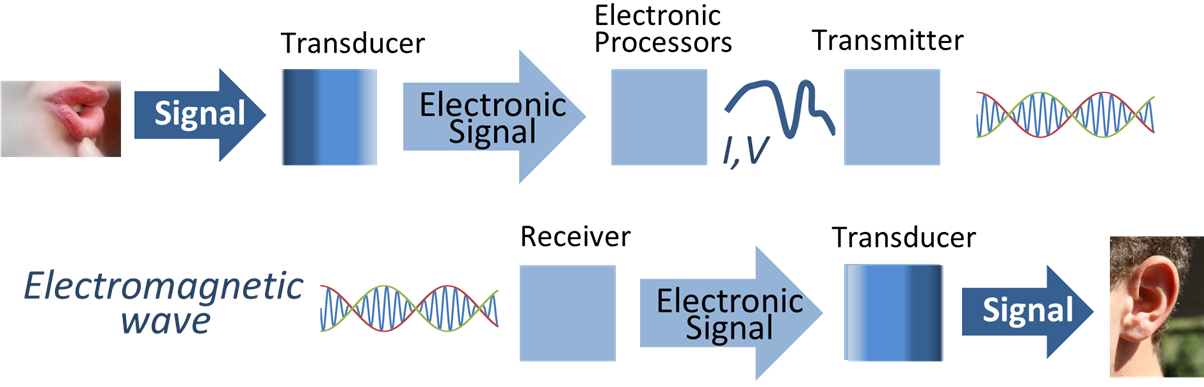
Telecommunication is the transmission of information by various types of technologies over wire, radio, optical, or other electromagnetic systems. It has its origin in the desire of humans for communication over a distance greater than that feasible with the human voice, but with a similar scale of expediency; thus, slow systems (such as postal mail) are excluded from the field. The transmission media in telecommunication have evolved through numerous stages of technology, from beacons and other visual signals (such as smoke signals, semaphore telegraphs, signal flags, and optical heliographs), to electrical cable and electromagnetic radiation, including light. Such transmission paths are often divided into communication channels, which afford the advantages of multiplexing multiple concurrent communication sessions. ''Telecommunication'' is often used in its plural form. Other examples of pre-modern long-distance communication included audio messages, such as code ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer
A computer is a machine that can be programmed to Execution (computing), carry out sequences of arithmetic or logical operations (computation) automatically. Modern digital electronic computers can perform generic sets of operations known as Computer program, programs. These programs enable computers to perform a wide range of tasks. A computer system is a nominally complete computer that includes the Computer hardware, hardware, operating system (main software), and peripheral equipment needed and used for full operation. This term may also refer to a group of computers that are linked and function together, such as a computer network or computer cluster. A broad range of Programmable logic controller, industrial and Consumer electronics, consumer products use computers as control systems. Simple special-purpose devices like microwave ovens and remote controls are included, as are factory devices like industrial robots and computer-aided design, as well as general-purpose devi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Communications System
A communications system or communication system is a collection of individual telecommunications networks, transmission systems, relay stations, tributary stations, and terminal equipment usually capable of interconnection and interoperation to form an integrated whole. The components of a communications system serve a common purpose, are technically compatible, use common procedures, respond to controls, and operate in union. Telecommunications is a method of communication (e.g., for sports broadcasting, mass media, journalism, etc.). Communication is the act of conveying intended meanings from one entity or group to another through the use of mutually understood signs and semiotic rules. Types By media An optical communication system is any form of telecommunication that uses light as the transmission medium. Equipment consists of a transmitter, which encodes a ''message'' into an optical '' signal'', a ''communication channel'', which carries the signal to its ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Hardware
Computer hardware includes the physical parts of a computer, such as the case, central processing unit (CPU), random access memory (RAM), monitor, mouse, keyboard, computer data storage, graphics card, sound card, speakers and motherboard. By contrast, software is the set of instructions that can be stored and run by hardware. Hardware is so-termed because it is " hard" or rigid with respect to changes, whereas software is "soft" because it is easy to change. Hardware is typically directed by the software to execute any command or instruction. A combination of hardware and software forms a usable computing system, although other systems exist with only hardware. Von Neumann architecture The template for all modern computers is the Von Neumann architecture, detailed in a 1945 paper by Hungarian mathematician John von Neumann. This describes a design architecture for an electronic digital computer with subdivisions of a processing unit consisting of an arithmet ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Firmware
In computing, firmware is a specific class of computer software that provides the low-level control for a device's specific hardware. Firmware, such as the BIOS of a personal computer, may contain basic functions of a device, and may provide hardware abstraction services to higher-level software such as operating systems. For less complex devices, firmware may act as the device's complete operating system, performing all control, monitoring and data manipulation functions. Typical examples of devices containing firmware are embedded systems (running embedded software), home and personal-use appliances, computers, and computer peripherals. Firmware is held in non-volatile memory devices such as ROM, EPROM, EEPROM, and flash memory. Updating firmware requires ROM integrated circuits to be physically replaced, or EPROM or flash memory to be reprogrammed through a special procedure. Some firmware memory devices are permanently installed and cannot be changed after manufact ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Software
Software is a set of computer programs and associated software documentation, documentation and data (computing), data. This is in contrast to Computer hardware, hardware, from which the system is built and which actually performs the work. At the low level language, lowest programming level, executable code consists of Machine code, machine language instructions supported by an individual Microprocessor, processor—typically a central processing unit (CPU) or a graphics processing unit (GPU). Machine language consists of groups of Binary number, binary values signifying Instruction set architecture, processor instructions that change the state of the computer from its preceding state. For example, an instruction may change the value stored in a particular storage location in the computer—an effect that is not directly observable to the user. An instruction System call, may also invoke one of many Input/output, input or output operations, for example displaying some text on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Access Control
In the fields of physical security and information security, access control (AC) is the selective restriction of access to a place or other resource, while access management describes the process. The act of ''accessing'' may mean consuming, entering, or using. Permission to access a resource is called ''authorization''. Locks and login credentials are two analogous mechanisms of access control. Physical security Geographical access control may be enforced by personnel (e.g. border guard, bouncer, ticket checker), or with a device such as a turnstile. There may be fences to avoid circumventing this access control. An alternative of access control in the strict sense (physically controlling access itself) is a system of checking authorized presence, see e.g. Ticket controller (transportation). A variant is exit control, e.g. of a shop (checkout) or a country. The term access control refers to the practice of restricting entrance to a property, a building, or a room ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Operating System
An operating system (OS) is system software that manages computer hardware, software resources, and provides common daemon (computing), services for computer programs. Time-sharing operating systems scheduler (computing), schedule tasks for efficient use of the system and may also include accounting software for cost allocation of Scheduling (computing), processor time, mass storage, printing, and other resources. For hardware functions such as input and output and memory allocation, the operating system acts as an intermediary between programs and the computer hardware, although the application code is usually executed directly by the hardware and frequently makes system calls to an OS function or is interrupted by it. Operating systems are found on many devices that contain a computer from cellular phones and video game consoles to web servers and supercomputers. The dominant general-purpose personal computer operating system is Microsoft Windows with a market share of aroun ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Reference Monitor
In operating systems architecture a reference monitor concept defines a set of design requirements on a reference validation mechanism, which enforces an access control policy over subjects' (e.g., processes and users) ability to perform operations (e.g., read and write) on objects (e.g., files and sockets) on a system. The properties of a reference monitor are captured by the acronym NEAT, which means: * The reference validation mechanism must be ''Non-bypassable'', so that an attacker cannot bypass the mechanism and violate the security policy. * The reference validation mechanism must be ''Evaluable'', i.e., amenable to analysis and tests, the completeness of which can be assured (verifiable). Without this property, the mechanism might be flawed in such a way that the security policy is not enforced. * The reference validation mechanism must be ''Always invoked''. Without this property, it is possible for the mechanism to not perform when intended, allowing an attacker to violat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Information Systems Security Glossary
Committee on National Security Systems Instruction No. 4009, National Information Assurance Glossary, published by the United States federal government, is an unclassified glossary of Information security terms intended to provide a common vocabulary for discussing Information Assurance concepts. The glossary was previously published as the National Information Systems Security Glossary (NSTISSI No. 4009) by the National Security Telecommunications and Information Systems Security Committee (NSTISSC). Under Executive Order (E.O.) 13231 of October 16, 2001, Critical Infrastructure Protection in the Information Age, the President George W. Bush redesignated the National Security Telecommunications and Information Systems Security Committee (NSTISSC) as the Committee on National Security Systems (CNSS). The most recent version was revised April 26, 2010. [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |