|
Secure Messaging
Secure messaging is a server-based approach to protect sensitive data when sent beyond the corporate borders, and it provides compliance with industry regulations such as HIPAA, GLBA and SOX. Advantages over classical secure e-mail are that confidential and authenticated exchanges can be started immediately by any internet user worldwide since there is no requirement to install any software nor to obtain or to distribute cryptographic keys beforehand. Secure messages provide non-repudiation as the recipients (similar to online banking) are personally identified and transactions are logged by the secure email platform. Functionality Secure messaging works as an online messaging service. Firstly, users enroll in a secure messaging platform. Then, the user logs into their account by typing in their username and password (or strong authentication) similar to a web-based email account. Out of a message center messages can be sent over a secure SSL-connection or via other equa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
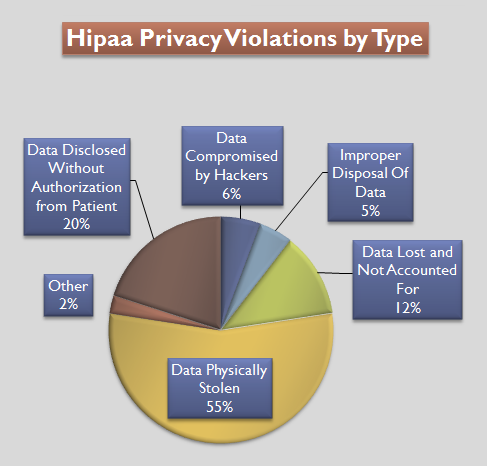
HIPAA
The Health Insurance Portability and Accountability Act of 1996 (HIPAA or the Kennedy– Kassebaum Act) is a United States Act of Congress enacted by the 104th United States Congress and signed into law by President Bill Clinton on August 21, 1996. It modernized the flow of healthcare information, stipulates how personally identifiable information maintained by the healthcare and healthcare insurance industries should be protected from fraud and theft, and addressed some limitations on healthcare insurance coverage. It generally prohibits healthcare providers and healthcare businesses, called ''covered entities'', from disclosing protected information to anyone other than a patient and the patient's authorized representatives without their consent. With limited exceptions, it does not restrict patients from receiving information about themselves. It does not prohibit patients from voluntarily sharing their health information however they choose, nor does it require confidential ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Identity-Based Encryption
ID-based encryption, or identity-based encryption (IBE), is an important primitive of ID-based cryptography. As such it is a type of public-key encryption in which the public key of a user is some unique information about the identity of the user (e.g. a user's email address). This means that a sender who has access to the public parameters of the system can encrypt a message using e.g. the text-value of the receiver's name or email address as a key. The receiver obtains its decryption key from a central authority, which needs to be trusted as it generates secret keys for every user. ID-based encryption was proposed by Adi Shamir in 1984. He was however only able to give an instantiation of identity-based signatures. Identity-based encryption remained an open problem for many years. The pairing-based Boneh–Franklin scheme and Cocks's encryption scheme based on quadratic residues both solved the IBE problem in 2001. Usage Identity-based systems allow any party to generat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Instant Messaging
Secure instant messaging is a form of instant messaging. Both terms refer to an informal means for computer users to exchange messages commonly referred to as "chats". Instant messaging can be compared to texting as opposed to making a mobile phone call. In the case of messaging, it is like the short form of emailing. Secure instant messaging is a specialized form of instant messaging that along with other differences, encrypts and decrypts the contents of the messages such that only the actual users can understand them. Instant messaging background Instant messaging has existed in some form or another for decades. Generally, it is a process by which users on a computer network can quickly communicate with one another using short text-based sentences rather than using email. Each user has a piece of software that communicates with a common server that connects the chat sessions. Over the past few years, two distinct settings for the use of instant messaging have evolved. The fi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Communication
Secure communication is when two entities are communicating and do not want a third party to listen in. For this to be the case, the entities need to communicate in a way that is unsusceptible to eavesdropping or interception. Secure communication includes means by which people can share information with varying degrees of certainty that third parties cannot intercept what is said. Other than spoken face-to-face communication with no possible eavesdropper, it is probably safe to say that no communication is guaranteed to be secure in this sense, although practical obstacles such as legislation, resources, technical issues (interception and encryption), and the sheer volume of communication serve to limit surveillance. With many communications taking place over long distance and mediated by technology, and increasing awareness of the importance of interception issues, technology and its compromise are at the heart of this debate. For this reason, this article focuses on communicati ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Privacy
Email privacy is a broad topic dealing with issues of unauthorized access to, and inspection of, electronic mail, or unauthorized tracking when a user reads an email. This unauthorized access can happen while an email is in transit, as well as when it is stored on email servers or on a user's computer, or when the user reads the message. In countries with a constitutional guarantee of the secrecy of correspondence, whether email can be equated with letterstherefore having legal protection from all forms of eavesdroppingis disputed because of the very nature of email. In 2022 a lookback at an 1890 law review article about personal privacy (the "right to be left alone”) noted how "digital technology has been allowed to invade our lives" both by personal choice and behavior, and also by various forms of ongoing monitoring. An email has to go through potentially untrustworthy intermediate computers (email servers, ISPs) before reaching its destination, and there is no way t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Encryption
Email encryption is encryption of email messages to protect the content from being read by entities other than the intended recipients. Email encryption may also include authentication. Email is prone to the disclosure of information. Most emails are encrypted during transmission, but they are stored in clear text, making them readable by third parties such as email providers. By default, popular email services such as Gmail and Outlook do not enable end-to-end encryption. By means of some available tools, persons other than the designated recipients can read the email contents. Email encryption can rely on public-key cryptography, in which users can each publish a public key that others can use to encrypt messages to them, while keeping secret a private key they can use to decrypt such messages or to digitally encrypt and sign messages they send. Encryption protocols With the original design of email protocol, the communication between email servers was in plain text, which p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Authentication
Email authentication, or validation, is a collection of techniques aimed at providing verifiable information about the origin of email messages by validating the domain ownership of any message transfer agents (MTA) who participated in transferring and possibly modifying a message. The original base of Internet email, Simple Mail Transfer Protocol (SMTP), has no such feature, so forged sender addresses in emails (a practice known as email spoofing) have been widely used in phishing, email spam, and various types of fraud. To combat this, many competing email authentication proposals have been developed, but only fairly recently have three been widely adopted – SPF, DKIM and DMARC. The results of such validation can be used in automated email filtering, or can assist recipients when selecting an appropriate action. This article does not cover user authentication of email submission and retrieval. Rationale In the early 1980s, when Simple Mail Transfer Protocol (SMTP) was des ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Security
Information security, sometimes shortened to InfoSec, is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorized/inappropriate access to data, or the unlawful use, disclosure, disruption, deletion, corruption, modification, inspection, recording, or devaluation of information. It also involves actions intended to reduce the adverse impacts of such incidents. Protected information may take any form, e.g. electronic or physical, tangible (e.g. paperwork) or intangible (e.g. knowledge). Information security's primary focus is the balanced protection of the confidentiality, integrity, and availability of data (also known as the CIA triad) while maintaining a focus on efficient policy implementation, all without hampering organization productivity. This is largely achieved through a structured risk management process that involves: * identify ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an assertion, such as the identity of a computer system user. In contrast with identification, the act of indicating a person or thing's identity, authentication is the process of verifying that identity. It might involve validating personal identity documents, verifying the authenticity of a website with a digital certificate, determining the age of an artifact by carbon dating, or ensuring that a product or document is not counterfeit. Methods Authentication is relevant to multiple fields. In art, antiques, and anthropology, a common problem is verifying that a given artifact was produced by a certain person or in a certain place or period of history. In computer science, verifying a user's identity is often required to allow access to confidential data or systems. Authentication can be considered to be of three types: The first type of a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Search Engine
A search engine is a software system designed to carry out web searches. They search the World Wide Web in a systematic way for particular information specified in a textual web search query. The search results are generally presented in a line of results, often referred to as search engine results pages (SERPs). When a user enters a query into a search engine, the engine scans its index of web pages to find those that are relevant to the user's query. The results are then ranked by relevancy and displayed to the user. The information may be a mix of links to web pages, images, videos, infographics, articles, research papers, and other types of files. Some search engines also mine data available in databases or open directories. Unlike web directories and social bookmarking sites, which are maintained by human editors, search engines also maintain real-time information by running an algorithm on a web crawler. Any internet-based content that can't be indexed and sea ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Google
Google LLC () is an American Multinational corporation, multinational technology company focusing on Search Engine, search engine technology, online advertising, cloud computing, software, computer software, quantum computing, e-commerce, artificial intelligence, and Computer hardware, consumer electronics. It has been referred to as "the most powerful company in the world" and one of the world's List of most valuable brands, most valuable brands due to its market dominance, data collection, and technological advantages in the area of artificial intelligence. Its parent company Alphabet Inc., Alphabet is considered one of the Big Tech, Big Five American information technology companies, alongside Amazon (company), Amazon, Apple Inc., Apple, Meta Platforms, Meta, and Microsoft. Google was founded on September 4, 1998, by Larry Page and Sergey Brin while they were Doctor of Philosophy, PhD students at Stanford University in California. Together they own about 14% of its publicl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
UBS AG
UBS Group AG is a multinational investment bank and financial services company founded and based in Switzerland. Co-headquartered in the cities of Zürich and Basel, it maintains a presence in all major financial centres as the largest Swiss banking institution and the largest private bank in the world. UBS client services are known for their strict bank–client confidentiality and culture of banking secrecy. Because of the bank's large positions in the Americas, EMEA, and Asia Pacific markets, the Financial Stability Board considers it a global systemically important bank. Apart from private banking, UBS provides wealth management, asset management, and investment banking services for private, corporate, and institutional clients with international service. UBS manages the largest amount of private wealth in the world, counting approximately half of the world's billionaires among its clients. Despite its trimming of sell-side operations, UBS maintains a global inves ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |