|
STU-II
The STU-II (Standard Telephone Unit II) is a secure telephone developed by the U.S. National Security Agency. It permitted up to six users to have secure communications, on a time-shared (e.g.: rotating) basis. It was made by ITT Defense Communications, Nutley, New Jersey. An OEM partner was Northern Telecom. According to information on display in 2005 at the NSA's National Cryptologic Museum, the STU-II was in use from the 1980s to the present. It uses the linear predictive coding algorithm LPC-10 at 2.4 kilobits/second to digitize voice, and the "Key Distribution Center" (KDC) for key management. The display also stated that the STU-II B is the standard narrow band secure telephone. STU-II replaced the STU-I, KY-3 and the Navajo I. The last was a secure telephone in a briefcase, of which 110 were built in the 1980s for use by senior government officials when traveling. The Navaho I also used LPC-10. Some 10 000 STU-II units were produced. External links Delusion.org ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
STU-III
STU-III (Secure Telephone Unit - third generation) is a family of secure telephones introduced in 1987 by the NSA for use by the United States government, its contractors, and its allies. STU-III desk units look much like typical office telephones, plug into a standard telephone wall jack and can make calls to any ordinary phone user (with such calls receiving no special protection, however). When a call is placed to another STU-III unit that is properly set up, one caller can ask the other to initiate secure transmission. They then press a button on their telephones and, after a 15-second delay, their call is encrypted to prevent eavesdropping. There are portable and militarized versions and most STU-IIIs contained an internal modem and RS-232 port for data and fax transmission. Vendors were AT&T Corporation, AT&T (later transferred to Lucent, Lucent Technologies), RCA (Now L-3 Communications, East) and Motorola. STU-III are no longer in service with the U.S. Government, with t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
STU-II
The STU-II (Standard Telephone Unit II) is a secure telephone developed by the U.S. National Security Agency. It permitted up to six users to have secure communications, on a time-shared (e.g.: rotating) basis. It was made by ITT Defense Communications, Nutley, New Jersey. An OEM partner was Northern Telecom. According to information on display in 2005 at the NSA's National Cryptologic Museum, the STU-II was in use from the 1980s to the present. It uses the linear predictive coding algorithm LPC-10 at 2.4 kilobits/second to digitize voice, and the "Key Distribution Center" (KDC) for key management. The display also stated that the STU-II B is the standard narrow band secure telephone. STU-II replaced the STU-I, KY-3 and the Navajo I. The last was a secure telephone in a briefcase, of which 110 were built in the 1980s for use by senior government officials when traveling. The Navaho I also used LPC-10. Some 10 000 STU-II units were produced. External links Delusion.org ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Cryptologic Museum
The National Cryptologic Museum (NCM) is an American museum of cryptologic history that is affiliated with the National Security Agency (NSA). The first public museum in the U.S. Intelligence Community, NCM is located in the former Colony Seven Motel, just two blocks from the NSA headquarters at Fort George G. Meade in Maryland. The motel was purchased, creating a buffer zone between the high security main buildings of the NSA and an adjacent highway. The museum opened to the public on December 16, 1993, and now hosts about 50,000 visitors annually from all over the world. The NCM is open Tuesday through Saturday, 10am-4pm (hours are extended Wednesdays to 7pm). It is closed on Sundays, Mondays. and all federal holidays, and operates on NSA's emergency/weather closure schedule (i.e. if NSA is closed, the museum is closed as well). The NCM includes a gift store whose operational hours coordinate with the museum's operational schedule (i.e., if the museum is closed altogether, o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collection, and processing of information and data for foreign and domestic intelligence and counterintelligence purposes, specializing in a discipline known as signals intelligence (SIGINT). The NSA is also tasked with the protection of U.S. communications networks and information systems. The NSA relies on a variety of measures to accomplish its mission, the majority of which are clandestine. The existence of the NSA was not revealed until 1975. The NSA has roughly 32,000 employees. Originating as a unit to decipher coded communications in World War II, it was officially formed as the NSA by President Harry S. Truman in 1952. Between then and the end of the Cold War, it became the largest of the U.S. intelligence organizations in terms of pers ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Communications Interoperability Protocol
The Secure Communications Interoperability Protocol (SCIP) is a US standard for secure voice and data communication, foone-to-one connections, not packet-switched networks. SCIP derived from the US Government Future Narrowband Digital Terminal (FNBDT) project. SCIP supports a number of different modes, including national and multinational modes which employ different cryptography. Many nations and industries develop SCIP devices to support the multinational and national modes of SCIP. SCIP has to operate over the wide variety of communications systems, including commercial land line telephone, military radios, communication satellites, Voice over IP and the several different cellular telephone standards. Therefore, it was designed to make no assumptions about the underlying channel other than a minimum bandwidth of 2400 Hz. It is similar to a dial-up modem in that once a connection is made, two SCIP phones first negotiate the parameters they need and then communicate in the be ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
STU-I
The STU-I, like its successors sometimes known as a "stew phone", was a secure telephone developed by the U.S. National Security Agency for use by senior U.S. government officials in the 1970s. See also *KY-3 *Navajo I * STU-II *STU-III STU-III (Secure Telephone Unit - third generation) is a family of secure telephones introduced in 1987 by the NSA for use by the United States government, its contractors, and its allies. STU-III desk units look much like typical office telephone ... * SCIP References External linksCrypto Museum - STU I National S ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
KY-3
The KY-3 (TSEC/KY-3) is a secure telephone system developed by the U.S. National Security Agency in the early 1960s. It was one of the first widely accepted voice voice encryption systems. The "TSEC" prefix to the model number indicates NSA's Telecommunications Security nomenclature system. It was made by the Bendix Corporation according to specifications of the NSA. According to information on display in 2002 at the NSA's National Cryptologic Museum, the KY-3 provided high fidelity secure voice over special wide-band circuits known as "4-wire dedicated drops", since it used pulse-code modulation encoding for the audio which gave it "high-quality speech". Its overall high power requirements and physical size limited its "tactical" use but gained popularity among executives, diplomats, military leaders and the intelligence community. More than 2,500 units were produced between 1965 and 1967 and it was one of the first telecommunication security devices to use transistors packaged ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Voice
Secure voice (alternatively secure speech or ciphony) is a term in cryptography for the encryption of voice communication over a range of communication types such as radio, telephone or IP. History The implementation of voice encryption dates back to World War II when secure communication was paramount to the US armed forces. During that time, noise was simply added to a voice signal to prevent enemies from listening to the conversations. Noise was added by playing a record of noise in sync with the voice signal and when the voice signal reached the receiver, the noise signal was subtracted out, leaving the original voice signal. In order to subtract out the noise, the receiver need to have exactly the same noise signal and the noise records were only made in pairs; one for the transmitter and one for the receiver. Having only two copies of records made it impossible for the wrong receiver to decrypt the signal. To implement the system, the army contracted Bell Laboratori ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Navajo I
The Navajo I is a secure telephone built into a briefcase that was developed by the U.S. National Security Agency. According to information on display in 2002 at the NSA's National Cryptologic Museum, 110 units were built in the 1980s for use by senior government officials when traveling. It uses the linear predictive coding algorithm LPC-10 at 2.4 kilobits/second. The name is most likely a reference to the Navajo The Navajo (; British English: Navaho; nv, Diné or ') are a Native American people of the Southwestern United States. With more than 399,494 enrolled tribal members , the Navajo Nation is the largest federally recognized tribe in the United ... Navajo code talkers, code talkers of World War II. Sources Display labels fro See also *STU-II *Secure Communications Interoperability Protocol, SCIP National Security Agency encryption devices {{crypto-stub ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
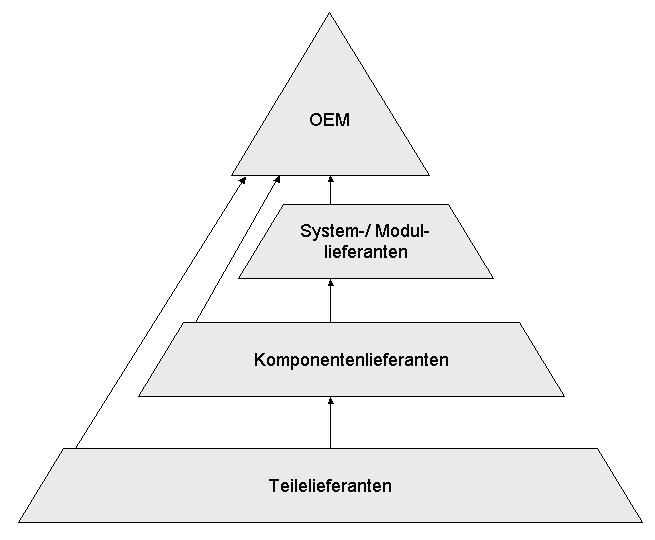
Original Equipment Manufacturer
An original equipment manufacturer (OEM) is generally perceived as a company that produces non-aftermarket parts and equipment that may be marketed by another manufacturer. It is a common industry term recognized and used by many professional organizations such as SAE International, ISO, and others. However, the term is also used in several other ways, which causes ambiguity. It sometimes means the maker of a system that includes other companies' subsystems, an end-product producer, an automotive part that is manufactured by the same company that produced the original part used in the automobile's assembly, or a value-added reseller.Ken Olsen: PDP-1 and PDP-8 (page 3) , economicadventure.com Automotive parts When referring to auto parts, OEM refers to the manufactur ...[...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Northern Telecom
Northern may refer to the following: Geography * North, a point in direction * Northern Europe, the northern part or region of Europe * Northern Highland, a region of Wisconsin, United States * Northern Province, Sri Lanka * Northern Range, a range of hills in Trinidad Schools * Northern Collegiate Institute and Vocational School (NCIVS), a school in Sarnia, Canada * Northern Secondary School, Toronto, Canada * Northern Secondary School (Sturgeon Falls), Ontario, Canada * Northern University (other), various institutions * Northern Guilford High School, a public high school in Greensboro, North Carolina Companies * Arriva Rail North, a former train operating company in northern England * Northern Bank, commercial bank in Northern Ireland * Northern Foods, based in Leeds, England * Northern Pictures, an Australian-based television production company * Northern Rail, a former train operating company in northern England * Northern Railway of Canada, a defunct railway in On ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Linear Predictive Coding
Linear predictive coding (LPC) is a method used mostly in audio signal processing and speech processing for representing the spectral envelope of a digital signal of speech in compressed form, using the information of a linear predictive model. LPC is the most widely used method in speech coding and speech synthesis. It is a powerful speech analysis technique, and a useful method for encoding good quality speech at a low bit rate. Overview LPC starts with the assumption that a speech signal is produced by a buzzer at the end of a tube (for voiced sounds), with occasional added hissing and popping sounds (for voiceless sounds such as sibilants and plosives). Although apparently crude, this Source–filter model is actually a close approximation of the reality of speech production. The glottis (the space between the vocal folds) produces the buzz, which is characterized by its intensity (loudness) and frequency (pitch). The vocal tract (the throat and mouth) forms the tube, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |