|
SEXINT
SEXINT is the practice of monitoring and/or characterizing/indexing the pornographic preferences of internet users in an effort to later use the information for blackmail. The term is a portmanteau of ''sex''ual ''int''elligence retrieved on an intelligence service target and was first used by Jennifer Granick, Director of Civil Liberties at the Stanford Center for Internet and Society. Uses The term was first used specifically in reference to the practice by Five Eyes member, the National Security Agency of the United States of America. It is unclear how often these programs and methods are used in comparison to other Five Eyes initiatives such as Optic Nerve (GCHQ), and XKEYSCORE. A leaked NSA document from October 2012 identified six people, all Muslims, whom the document termed "radicalizers" and presented as potential targets of this method. The document does not accuse any of the six targets of involvement in terrorist plots, but rather states that "the NSA believes the t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
FBI–King Suicide Letter
The FBI–King suicide letter or blackmail package was an anonymous 1964 letter and package by the Federal Bureau of Investigation (FBI) meant to blackmail Martin Luther King Jr. The suicide letter was part of the FBI's COINTELPRO operation against King. History On November 21, 1964, a package that contained the letter and a tape recording allegedly of King's sexual indiscretions was delivered to King's address. Although the letter was anonymously written, Martin Luther King Jr. correctly suspected the FBI sent the package. Coretta Scott King said the tapes comprised only "mumbo jumbo". The letter does not specify precisely what action it is urging King to undertake; King understood the letter as advocating that he commit suicide, although some have suggested that it was merely urging him to decline the Nobel Peace Prize (which he won in 1964) or step out of leadership. On March 8, 1971, an activist group called the Citizens' Commission to Investigate the FBI burglarized a loca ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Jennifer Granick
Jennifer Stisa Granick (born 1969) is an American attorney and educator. Senator Ron Wyden has called Granick an "NBA all-star of surveillance law." She is well known for her work with intellectual property law, free speech, privacy law, and other things relating to computer security, and has represented several high-profile hackers A hacker is a person skilled in information technology who uses their technical knowledge to achieve a goal or overcome an obstacle, within a computerized system by non-standard means. Though the term ''hacker'' has become associated in popu .... Early life and education Granick was born in Glen Ridge, New Jersey, Glen Ridge, New Jersey. Both of her parents were local educators. She attended Glen Ridge High School and then New College of Florida, New College in Sarasota, Florida, Sarasota, Florida, from which she received a Bachelor of Arts degree in 1990. After that, she moved to San Francisco to attend Hastings Law School, from which she gr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collection, and processing of information and data for foreign and domestic intelligence and counterintelligence purposes, specializing in a discipline known as signals intelligence (SIGINT). The NSA is also tasked with the protection of U.S. communications networks and information systems. The NSA relies on a variety of measures to accomplish its mission, the majority of which are clandestine. The existence of the NSA was not revealed until 1975. The NSA has roughly 32,000 employees. Originating as a unit to decipher coded communications in World War II, it was officially formed as the NSA by President Harry S. Truman in 1952. Between then and the end of the Cold War, it became the largest of the U.S. intelligence organizations in terms of pers ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Signals Intelligence
Signals intelligence (SIGINT) is intelligence-gathering by interception of ''signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication (electronic intelligence—abbreviated to ELINT). Signals intelligence is a subset of intelligence collection management. As classified and sensitive information is usually encrypted, signals intelligence in turn involves the use of cryptanalysis to decipher the messages. Traffic analysis—the study of who is signaling whom and in what quantity—is also used to integrate information again. History Origins Electronic interceptions appeared as early as 1900, during the Boer War of 1899–1902. The British Royal Navy had installed wireless sets produced by Marconi on board their ships in the late 1890s, and the British Army used some limited wireless signalling. The Boers captured some wireless sets and used them to make vital transmis ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Privacy Of Telecommunications
__NOTOC__ The secrecy of correspondence (german: Briefgeheimnis, french: secret de la correspondance) or literally translated as secrecy of letters, is a fundamental legal principle enshrined in the constitutions of several European countries. It guarantees that the content of sealed letters is never revealed, and that letters in transit are not opened by government officials, or any other third party. The right of privacy to one's own letters is the main legal basis for the assumption of privacy of correspondence. The principle has been naturally extended to other forms of communication, including telephony and electronic communications on the Internet, as the constitutional guarantees are generally thought to also cover these forms of communication. However, national telecommunications privacy laws may allow lawful interception, i.e. wiretapping and monitoring of electronic communications in cases of suspicion of crime. Paper letters have, in most jurisdictions, remained outside ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Privacy In The United States
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively. The domain of privacy partially overlaps with security, which can include the concepts of appropriate use and protection of information. Privacy may also take the form of bodily integrity. The right not to be subjected to unsanctioned invasions of privacy by the government, corporations, or individuals is part of many countries' privacy laws, and in some cases, constitutions. The concept of universal individual privacy is a modern concept primarily associated with Western culture, particularly British and North American, and remained virtually unknown in some cultures until recent times. Now, most cultures recognize the ability of individuals to withhold certain parts of personal information from wider society. With the rise of technology, the debate regarding privacy has shifted from a bodily sense to a digital sense. As the wo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Surveillance Scandals
Surveillance is the monitoring of behavior, many activities, or information for the purpose of information gathering, influencing, managing or directing. This can include observation from a distance by means of electronic equipment, such as closed-circuit television (CCTV), or interception of electronically transmitted information like Internet traffic. It can also include simple technical methods, such as human intelligence gathering and postal interception. Surveillance is used by citizens for protecting their neighborhoods. And by governments for intelligence gathering - including espionage, prevention of crime, the protection of a process, person, group or object, or the investigation of crime. It is also used by criminal organizations to plan and commit crimes, and by businesses to gather intelligence on criminals, their competitors, suppliers or customers. Religious organisations charged with detecting heresy and heterodoxy may also carry out surveillance. Auditors ca ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Human Rights Abuses
Human rights are moral principles or normsJames Nickel, with assistance from Thomas Pogge, M.B.E. Smith, and Leif Wenar, 13 December 2013, Stanford Encyclopedia of PhilosophyHuman Rights Retrieved 14 August 2014 for certain standards of human behaviour and are regularly protected in municipal and international law. They are commonly understood as inalienable,The United Nations, Office of the High Commissioner of Human RightsWhat are human rights? Retrieved 14 August 2014 fundamental rights "to which a person is inherently entitled simply because she or he is a human being" and which are "inherent in all human beings",Burns H. Weston, 20 March 2014, Encyclopædia Britannicahuman rights Retrieved 14 August 2014. regardless of their age, ethnic origin, location, language, religion, ethnicity, or any other status. They are applicable everywhere and at every time in the sense of being universal, and they are egalitarian in the sense of being the same for everyone. They are regarde ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Law Enforcement
Law enforcement is the activity of some members of government who act in an organized manner to enforce the law by discovering, deterring, rehabilitating, or punishing people who violate the rules and norms governing that society. The term encompasses police, courts, and corrections. These three components may operate independently of each other or collectively, through the use of record sharing and mutual cooperation. The concept of law enforcement dates back to ancient times, and forms of law enforcement and police have existed in various forms across many human societies. Modern state legal codes use the term peace officer, or law enforcement officer, to include every person vested by the legislating state with police power or authority; traditionally, anyone sworn or badged, who can arrest any person for a violation of criminal law, is included under the umbrella term of law enforcement. Although law enforcement may be most concerned with the prevention and punishment o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Human Rights
Human rights are Morality, moral principles or Social norm, normsJames Nickel, with assistance from Thomas Pogge, M.B.E. Smith, and Leif Wenar, 13 December 2013, Stanford Encyclopedia of PhilosophyHuman Rights Retrieved 14 August 2014 for certain standards of human behaviour and are regularly protected in Municipal law, municipal and international law. They are commonly understood as inalienable,The United Nations, Office of the High Commissioner of Human RightsWhat are human rights? Retrieved 14 August 2014 fundamental rights "to which a person is inherently entitled simply because she or he is a human being" and which are "inherent in all human beings",Burns H. Weston, 20 March 2014, Encyclopædia Britannicahuman rights Retrieved 14 August 2014. regardless of their age, ethnic origin, location, language, religion, ethnicity, or any other status. They are applicable everywhere and at every time in the sense of being Universality (philosophy), universal, and they are Egalitari ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
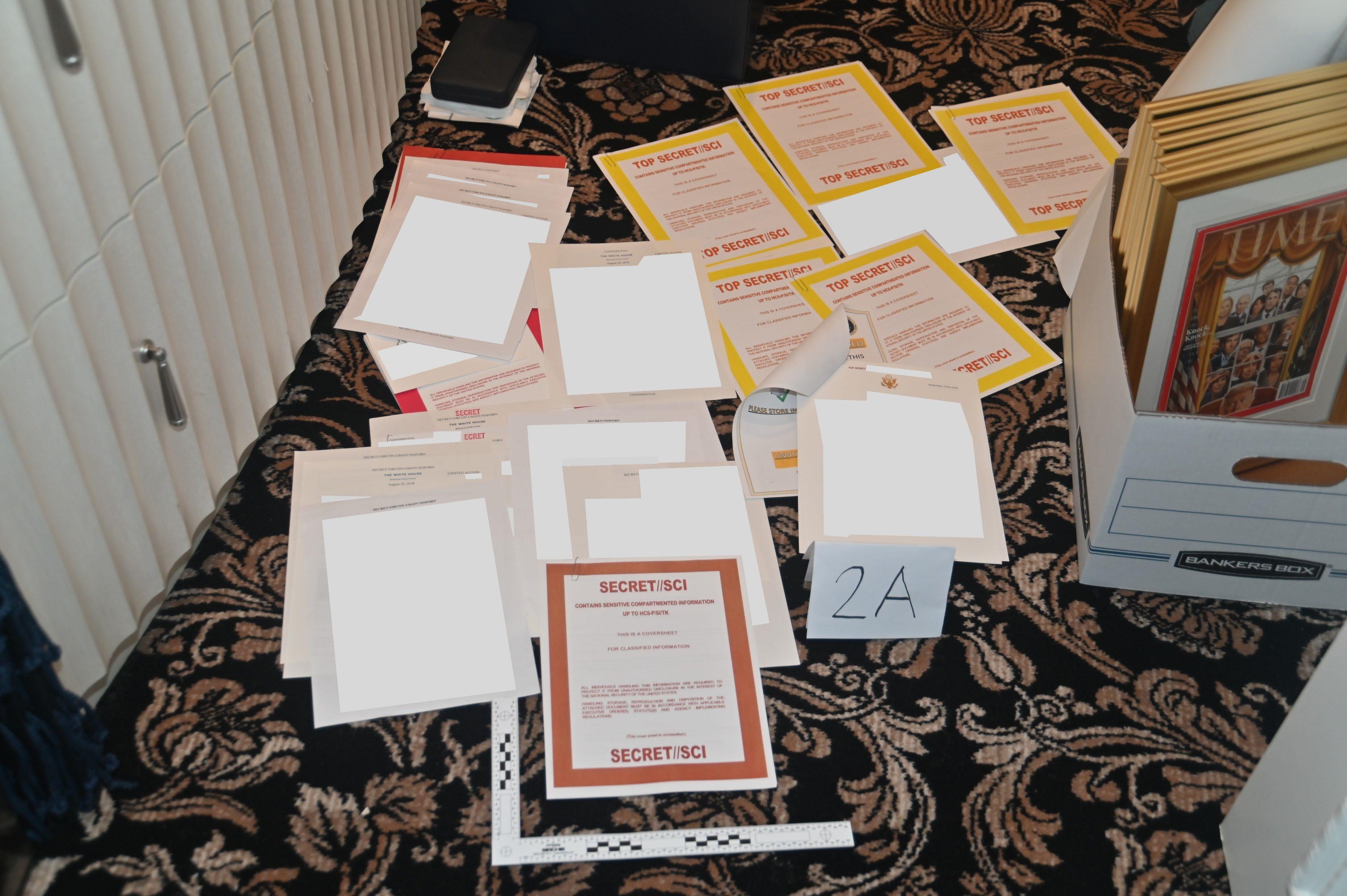
United States Government Secrecy
The United States government classification system is established under Executive Order 13526, the latest in a long series of executive orders on the topic beginning in 1951. Issued by President Barack Obama in 2009, Executive Order 13526 replaced earlier executive orders on the topic and modified the regulations codified to 32 C.F.R. 2001. It lays out the system of classification, declassification, and handling of national security information generated by the U.S. government and its employees and contractors, as well as information received from other governments. The desired degree of secrecy about such information is known as its sensitivity. Sensitivity is based upon a calculation of the damage to national security that the release of the information would cause. The United States has three levels of classification: Confidential, Secret, and Top Secret. Each level of classification indicates an increasing degree of sensitivity. Thus, if one holds a Top Secret security clear ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Blackmail
Blackmail is an act of coercion using the threat of revealing or publicizing either substantially true or false information about a person or people unless certain demands are met. It is often damaging information, and it may be revealed to family members or associates rather than to the general public. These acts can also involve using threats of physical, mental or emotional harm, or of criminal prosecution, against the victim or someone close to the victim. It is normally carried out for personal gain, most commonly of position, money, or property. Blackmail may also be considered a form of extortion. Although the two are generally synonymous, extortion is the taking of personal property by threat of future harm. Blackmail is the use of threat to prevent another from engaging in a lawful occupation and writing libelous letters or letters that provoke a breach of the peace, as well as use of intimidation for purposes of collecting an unpaid debt. In many jurisdictions, bla ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |






.jpg)