|
Passive Attack
A passive attack on a cryptosystem is one in which the cryptanalyst cannot interact with any of the parties involved, attempting to break the system solely based upon observed data (i.e. the ciphertext). This can also include known plaintext attacks where both the plaintext and its corresponding ciphertext are known. While active attackers can interact with the parties by sending data, a passive attacker is limited to intercepting communications (eavesdropping), and seeks to decrypt data by interpreting the transcripts of authentication sessions. Since passive attackers do not introduce data of their own, they can be difficult to detect. While most classical ciphers are vulnerable to this form of attack, most modern ciphers are designed to prevent this type of attack above all others. Attributes *Traffic analysis *Non-evasive eavesdropping and monitoring of transmissions *Because data unaffected, tricky to detect *Emphasis on prevention (encryption) not detection *Sometimes ref ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptosystem
In cryptography, a cryptosystem is a suite of cryptographic algorithms needed to implement a particular security service, such as confidentiality (encryption). Typically, a cryptosystem consists of three algorithms: one for key generation, one for encryption, and one for decryption. The term ''cipher'' (sometimes ''cypher'') is often used to refer to a pair of algorithms, one for encryption and one for decryption. Therefore, the term ''cryptosystem'' is most often used when the key generation algorithm is important. For this reason, the term ''cryptosystem'' is commonly used to refer to public key techniques; however both "cipher" and "cryptosystem" are used for symmetric key techniques. Formal definition Mathematically, a cryptosystem or encryption scheme can be defined as a tuple (\mathcal,\mathcal,\mathcal,\mathcal,\mathcal) with the following properties. # \mathcal is a set called the "plaintext space". Its elements are called plaintexts. # \mathcal is a set called the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ciphertext
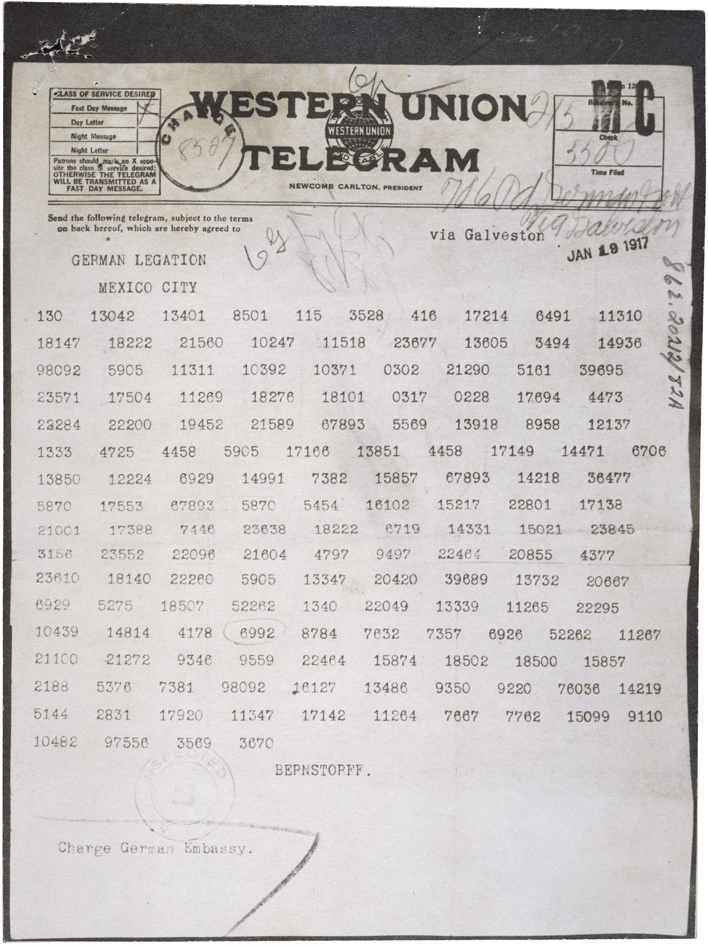
In cryptography, ciphertext or cyphertext is the result of encryption performed on plaintext using an algorithm, called a cipher. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext that is unreadable by a human or computer without the proper cipher to decrypt it. This process prevents the loss of sensitive information via hacking. Decryption, the inverse of encryption, is the process of turning ciphertext into readable plaintext. Ciphertext is not to be confused with codetext because the latter is a result of a code, not a cipher. Conceptual underpinnings Let m\! be the plaintext message that Alice wants to secretly transmit to Bob and let E_k\! be the encryption cipher, where _k\! is a secret key, cryptographic key. Alice must first transform the plaintext into ciphertext, c\!, in order to securely send the message to Bob, as follows: : c = E_k(m). \! In a symmetric-key system, Bob knows Alice's encryption key. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Known Plaintext Attack
The known-plaintext attack (KPA) is an attack model for cryptanalysis where the attacker has access to both the plaintext (called a crib) and its encrypted version (ciphertext). These can be used to reveal secret keys and code books. The term "crib" originated at Bletchley Park, the British World War II decryption operation, where it was defined as: History The usage "crib" was adapted from a slang term referring to cheating (e.g., "I cribbed my answer from your test paper"). A "crib" originally was a literal or interlinear translation of a foreign-language text—usually a Latin or Greek text—that students might be assigned to translate from the original language. The idea behind a crib is that cryptologists were looking at incomprehensible ciphertext, but if they had a clue about some word or phrase that might be expected to be in the ciphertext, they would have a "wedge," a test to break into it. If their otherwise random attacks on the cipher managed to sometimes produce th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Plaintext
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. This usually refers to data that is transmitted or stored unencrypted. Overview With the advent of computing, the term ''plaintext'' expanded beyond human-readable documents to mean any data, including binary files, in a form that can be viewed or used without requiring a key or other decryption device. Information—a message, document, file, etc.—if to be communicated or stored in an unencrypted form is referred to as plaintext. Plaintext is used as input to an encryption algorithm; the output is usually termed ciphertext, particularly when the algorithm is a cipher. Codetext is less often used, and almost always only when the algorithm involved is actually a code. Some systems use multiple layers of encryption, with the output of one encryption algorithm becoming "plaintext" input for the next. Secure handling Insecure handling of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Eavesdropping
Eavesdropping is the act of secretly or stealthily listening to the private conversation or communications of others without their consent in order to gather information. Etymology The verb ''eavesdrop'' is a back-formation from the noun ''eavesdropper'' ("a person who eavesdrops"), which was formed from the related noun ''eavesdrop'' ("the dripping of water from the eaves of a house; the ground on which such water falls"). An eavesdropper was someone who would hang from the eave of a building so as to hear what is said within. The PBS documentaries ''Inside the Court of Henry VIII'' (April 8, 2015) and ''Secrets of Henry VIII’s Palace'' (June 30, 2013) include segments that display and discuss "eavedrops", carved wooden figures Henry VIII had built into the eaves (overhanging edges of the beams in the ceiling) of Hampton Court to discourage unwanted gossip or dissension from the King's wishes and rule, to foment paranoia and fear, and demonstrate that everything said there wa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Encryption
In Cryptography law, cryptography, encryption (more specifically, Code, encoding) is the process of transforming information in a way that, ideally, only authorized parties can decode. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Despite its goal, encryption does not itself prevent interference but denies the intelligible content to a would-be interceptor. For technical reasons, an encryption scheme usually uses a pseudo-random encryption Key (cryptography), key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users. Historically, various forms of encryption have been used to aid in cryptography. Early encryption ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cybersecurity
Computer security (also cybersecurity, digital security, or information technology (IT) security) is a subdiscipline within the field of information security. It consists of the protection of computer software, systems and networks from threats that can lead to unauthorized information disclosure, theft or damage to hardware, software, or data, as well as from the disruption or misdirection of the services they provide. The significance of the field stems from the expanded reliance on computer systems, the Internet, and wireless network standards. Its importance is further amplified by the growth of smart devices, including smartphones, televisions, and the various devices that constitute the Internet of things (IoT). Cybersecurity has emerged as one of the most significant new challenges facing the contemporary world, due to both the complexity of information systems and the societies they support. Security is particularly crucial for systems that govern large-scale sy ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Known Plaintext Attack
The known-plaintext attack (KPA) is an attack model for cryptanalysis where the attacker has access to both the plaintext (called a crib) and its encrypted version (ciphertext). These can be used to reveal secret keys and code books. The term "crib" originated at Bletchley Park, the British World War II decryption operation, where it was defined as: History The usage "crib" was adapted from a slang term referring to cheating (e.g., "I cribbed my answer from your test paper"). A "crib" originally was a literal or interlinear translation of a foreign-language text—usually a Latin or Greek text—that students might be assigned to translate from the original language. The idea behind a crib is that cryptologists were looking at incomprehensible ciphertext, but if they had a clue about some word or phrase that might be expected to be in the ciphertext, they would have a "wedge," a test to break into it. If their otherwise random attacks on the cipher managed to sometimes produce th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Chosen Plaintext Attack
A chosen-plaintext attack (CPA) is an attack model for cryptanalysis which presumes that the attacker can obtain the ciphertexts for arbitrary plaintexts.Ross Anderson, ''Security Engineering: A Guide to Building Dependable Distributed Systems''. The first edition (2001): http://www.cl.cam.ac.uk/~rja14/book.html The goal of the attack is to gain information that reduces the security of the encryption scheme. Modern ciphers aim to provide semantic security, also known as ''ciphertext indistinguishability under chosen-plaintext attack'', and they are therefore, by design, generally immune to chosen-plaintext attacks if correctly implemented. Introduction In a chosen-plaintext attack the Adversary (cryptography), adversary can (possibly Adaptive algorithm, adaptively) ask for the ciphertexts of arbitrary plaintext messages. This is formalized by allowing the adversary to interact with an encryption Oracle machine, oracle, viewed as a black box. The attacker’s goal is to reveal all ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Chosen Ciphertext Attack
A chosen-ciphertext attack (CCA) is an attack model for cryptanalysis Cryptanalysis (from the Greek ''kryptós'', "hidden", and ''analýein'', "to analyze") refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic se ... where the cryptanalyst can gather information by obtaining the decryptions of chosen ciphertexts. From these pieces of information the adversary can attempt to recover the secret key used for decryption. For formal definitions of security against chosen-ciphertext attacks, see for example: Michael Luby and Mihir Bellare et al. Introduction A number of otherwise secure schemes can be defeated under chosen-ciphertext attack. For example, the El Gamal cryptosystem is semantic security, semantically secure under chosen-plaintext attack, but this semantic security can be trivially defeated under a chosen-ciphertext attack. Early versions of RSA (algorithm), RSA ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Adaptive Chosen Ciphertext Attack
An adaptive chosen-ciphertext attack (abbreviated as CCA2) is an interactive form of chosen-ciphertext attack in which an attacker first sends a number of ciphertexts to be decrypted chosen adaptively, and then uses the results to distinguish a target ciphertext without consulting the oracle on the challenge ciphertext. In an adaptive attack, the attacker is further allowed adaptive queries to be asked after the target is revealed (but the target query is disallowed). It is extending the indifferent (non-adaptive) chosen-ciphertext attack (CCA1) where the second stage of adaptive queries is not allowed. Charles Rackoff and Dan Simon defined CCA2 and suggested a system building on the non-adaptive CCA1 definition and system of Moni Naor and Moti Yung (which was the first treatment of chosen ciphertext attack immunity of public key systems). In certain practical settings, the goal of this attack is to gradually reveal information about an encrypted message, or about the decryption k ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Topics In Cryptography
The following outline is provided as an overview of and topical guide to cryptography: Cryptography (or cryptology) – practice and study of hiding information. Modern cryptography intersects the disciplines of mathematics, computer science, and engineering. Applications of cryptography include ATM cards, computer passwords, and electronic commerce. Essence of cryptography * Cryptographer * Encryption/decryption * Cryptographic key * Cipher * Ciphertext * Plaintext * Code * Tabula recta * Alice and Bob Uses of cryptographic techniques * Commitment schemes * Secure multiparty computation * Electronic voting * Authentication * Digital signatures * Crypto systems * Dining cryptographers problem * Anonymous remailer * Pseudonymity * Onion routing * Digital currency * Secret sharing * Indistinguishability obfuscation Branches of cryptography * Multivariate cryptography * Post-quantum cryptography * Quantum cryptography * Steganography * Visual cryptography * ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |