|
Parkerian Hexad
The Parkerian hexad is a set of six elements of information security proposed by Donn B. Parker in 1998. The Parkerian hexad adds three additional attributes to the three classic security attributes of the CIA triad (confidentiality, integrity, availability). The Parkerian Hexad attributes are the following: * Confidentiality * Possession or Control * Integrity * Authenticity * Availability * Utility These attributes of information are atomic in that they are not broken down into further constituents; they are non-overlapping in that they refer to unique aspects of information. Any information security breach can be described as affecting one or more of these fundamental attributes of information. Attributes from the CIA triad Confidentiality Confidentiality refers to limits on who can get what kind of information. For example, executives concerned about protecting their enterprise's strategic plans from competitors; individuals are concerned about unauthorized access to thei ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Donn B
In Irish mythology, Donn ("the dark one", from cel-x-proto, Dhuosnos) is an ancestor of the Gaels and is believed to have been a god of the dead. Donn is said to dwell in Tech Duinn (the "house of Donn" or "house of the dark one"), where the souls of the dead gather. He may have originally been an aspect of the Dagda. Folklore about Donn survived into the modern era in parts of Ireland, in which he is said to be a phantom horseman riding a white horse. Early literary sources A 9th-century poem says that Donn's dying wish was that all his descendants would gather at Donn's house or ''Tech Duinn'' (modern Irish ''Teach Duinn'') after death: "To me, to my house, you shall all come after your deaths". The 10th-century tale ''Airne Fíngein'' ("Fíngen's Vigil") says that Tech Duinn is where the souls of the dead gather. In their translation of ''Acallam na Senórach'', Ann Dooley and Harry Roe commented that "to go to the House of Donn in Irish tradition means to die". This sugges ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
CIA Triad
Information security, sometimes shortened to InfoSec, is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorized/inappropriate access to data, or the unlawful use, disclosure, disruption, deletion, corruption, modification, inspection, recording, or devaluation of information. It also involves actions intended to reduce the adverse impacts of such incidents. Protected information may take any form, e.g. electronic or physical, tangible (e.g. paperwork) or intangible (e.g. knowledge). Information security's primary focus is the balanced protection of the confidentiality, integrity, and availability of data (also known as the CIA triad) while maintaining a focus on efficient policy implementation, all without hampering organization productivity. This is largely achieved through a structured risk management process that involves: * identifying inform ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Integrity
Data integrity is the maintenance of, and the assurance of, data accuracy and consistency over its entire Information Lifecycle Management, life-cycle and is a critical aspect to the design, implementation, and usage of any system that stores, processes, or retrieves data. The term is broad in scope and may have widely different meanings depending on the specific context even under the same general umbrella of computing. It is at times used as a proxy term for data quality, while data validation is a prerequisite for data integrity. Data integrity is the opposite of data corruption. The overall intent of any data integrity technique is the same: ensure data is recorded exactly as intended (such as a database correctly rejecting mutually exclusive possibilities). Moreover, upon later Data retrieval, retrieval, ensure the data is the same as when it was originally recorded. In short, data integrity aims to prevent unintentional changes to information. Data integrity is not to be confus ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Disk Controller
{{unreferenced, date=May 2010 The disk controller is the controller circuit which enables the CPU to communicate with a hard disk, floppy disk or other kind of disk drive. It also provides an interface between the disk drive and the bus connecting it to the rest of the system. Early disk controllers were identified by their storage methods and data encoding. They were typically implemented on a separate controller card. Modified frequency modulation (MFM) controllers were the most common type in small computers, used for both floppy disk and hard disk drives. Run length limited (RLL) controllers used data compression to increase storage capacity by about 50%. Priam created a proprietary storage algorithm that could double the disk storage. Shugart Associates Systems Interface ( SASI) was a predecessor to SCSI. Modern disk controllers are integrated into the disk drive as peripheral controllers. For example, disks called "SCSI disks" have built-in SCSI controllers. In the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Denial-of-service Attacks
In computing, a denial-of-service attack (DoS attack) is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to a network. Denial of service is typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to overload systems and prevent some or all legitimate requests from being fulfilled. In a distributed denial-of-service attack (DDoS attack), the incoming traffic flooding the victim originates from many different sources. More sophisticated strategies are required to mitigate this type of attack, as simply attempting to block a single source is insufficient because there are multiple sources. A DoS or DDoS attack is analogous to a group of people crowding the entry door of a shop, making it hard for legitimate customers to enter, thus disrupting trade. Criminal perpetrators of DoS attacks of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Digital Signature
A digital signature is a mathematical scheme for verifying the authenticity of digital messages or documents. A valid digital signature, where the prerequisites are satisfied, gives a recipient very high confidence that the message was created by a known sender (authenticity), and that the message was not altered in transit (integrity). Digital signatures are a standard element of most cryptographic protocol suites, and are commonly used for software distribution, financial transactions, contract management software, and in other cases where it is important to detect forgery or tampering. Digital signatures are often used to implement electronic signatures, which includes any electronic data that carries the intent of a signature, but not all electronic signatures use digital signatures. [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Public-key Cryptography
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public key and a corresponding private key. Key pairs are generated with cryptographic algorithms based on mathematical problems termed one-way functions. Security of public-key cryptography depends on keeping the private key secret; the public key can be openly distributed without compromising security. In a public-key encryption system, anyone with a public key can encrypt a message, yielding a ciphertext, but only those who know the corresponding private key can decrypt the ciphertext to obtain the original message. For example, a journalist can publish the public key of an encryption key pair on a web site so that sources can send secret messages to the news organization in ciphertext. Only the journalist who knows the corresponding private key can decrypt the ciphertexts to obtain the sources' messages—an eavesdropp ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Debit Card
A debit card, also known as a check card or bank card is a payment card that can be used in place of cash to make purchases. The term '' plastic card'' includes the above and as an identity document. These are similar to a credit card, but unlike a credit card, the money for the purchase must be in the cardholder's bank account at the time of a purchase and is immediately transferred directly from that account to the merchant's account to pay for the purchase. Some debit cards carry a stored value with which a payment is made (prepaid card), but most relay a message to the cardholder's bank to withdraw funds from the cardholder's designated bank account. In some cases, the payment card number is assigned exclusively for use on the Internet and there is no physical card. This is referred to as a virtual card. In many countries, the use of debit cards has become so widespread they have overtaken checks in volume, or have entirely replaced them; in some instances, debit cards ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
EBCDIC
Extended Binary Coded Decimal Interchange Code (EBCDIC; ) is an eight-bit character encoding used mainly on IBM mainframe and IBM midrange computer operating systems. It descended from the code used with punched cards and the corresponding six-bit binary-coded decimal code used with most of IBM's computer peripherals of the late 1950s and early 1960s. It is supported by various non-IBM platforms, such as Fujitsu-Siemens' BS2000/OSD, OS-IV, MSP, and MSP-EX, the SDS Sigma series, Unisys VS/9, Unisys MCP and ICL VME. History EBCDIC was devised in 1963 and 1964 by IBM and was announced with the release of the IBM System/360 line of mainframe computers. It is an eight-bit character encoding, developed separately from the seven-bit ASCII encoding scheme. It was created to extend the existing Binary-Coded Decimal (BCD) Interchange Code, or BCDIC, which itself was devised as an efficient means of encoding the two ''zone'' and ''number'' punches on punched cards into six bits. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ASCII
ASCII ( ), abbreviated from American Standard Code for Information Interchange, is a character encoding standard for electronic communication. ASCII codes represent text in computers, telecommunications equipment, and other devices. Because of technical limitations of computer systems at the time it was invented, ASCII has just 128 code points, of which only 95 are , which severely limited its scope. All modern computer systems instead use Unicode, which has millions of code points, but the first 128 of these are the same as the ASCII set. The Internet Assigned Numbers Authority (IANA) prefers the name US-ASCII for this character encoding. ASCII is one of the List of IEEE milestones, IEEE milestones. Overview ASCII was developed from telegraph code. Its first commercial use was as a seven-bit teleprinter code promoted by Bell data services. Work on the ASCII standard began in May 1961, with the first meeting of the American Standards Association's (ASA) (now the American Nat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
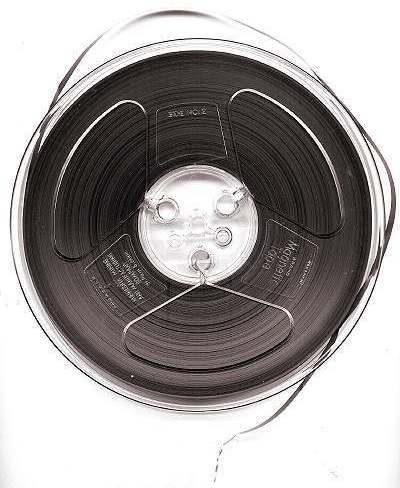
Magnetic Tape
Magnetic tape is a medium for magnetic storage made of a thin, magnetizable coating on a long, narrow strip of plastic film. It was developed in Germany in 1928, based on the earlier magnetic wire recording from Denmark. Devices that use magnetic tape could with relative ease record and playback audio, visual, and binary computer data. Magnetic tape revolutionized sound recording and reproduction and broadcasting. It allowed radio, which had always been broadcast live, to be recorded for later or repeated airing. Since the early 1950s, magnetic tape has been used with computers to store large quantities of data and is still used for backup purposes. Magnetic tape begins to degrade after 10–20 years and therefore is not an ideal medium for long-term archival storage. Durability While good for short-term use, magnetic tape is highly prone to disintegration. Depending on the environment, this process may begin after 10–20 years. Over time, magnetic tape made in the 197 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
John Wiley & Sons
John Wiley & Sons, Inc., commonly known as Wiley (), is an American multinational publishing company founded in 1807 that focuses on academic publishing and instructional materials. The company produces books, journals, and encyclopedias, in print and electronically, as well as online products and services, training materials, and educational materials for undergraduate, graduate, and continuing education students. History The company was established in 1807 when Charles Wiley opened a print shop in Manhattan. The company was the publisher of 19th century American literary figures like James Fenimore Cooper, Washington Irving, Herman Melville, and Edgar Allan Poe, as well as of legal, religious, and other non-fiction titles. The firm took its current name in 1865. Wiley later shifted its focus to scientific, technical, and engineering subject areas, abandoning its literary interests. Wiley's son John (born in Flatbush, New York, October 4, 1808; died in East Orange, New Je ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
%2C_The_Bull_-_geograph.org.uk_-_284005.jpg)

.jpg)