|
POP3
In computing, the Post Office Protocol (POP) is an application-layer Internet standard protocol used by e-mail clients to retrieve e-mail from a mail server. POP version 3 (POP3) is the version in common use, and along with IMAP the most common protocols for email retrieval. Purpose The Post Office Protocol provides access via an Internet Protocol (IP) network for a user client application to a mailbox (''maildrop'') maintained on a mail server. The protocol supports download and delete operations for messages. POP3 clients connect, retrieve all messages, store them on the client computer, and finally delete them from the server. This design of POP and its procedures was driven by the need of users having only temporary Internet connections, such as dial-up access, allowing these users to retrieve e-mail when connected, and subsequently to view and manipulate the retrieved messages when offline. POP3 clients also have an option to leave mail on the server after download. By c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
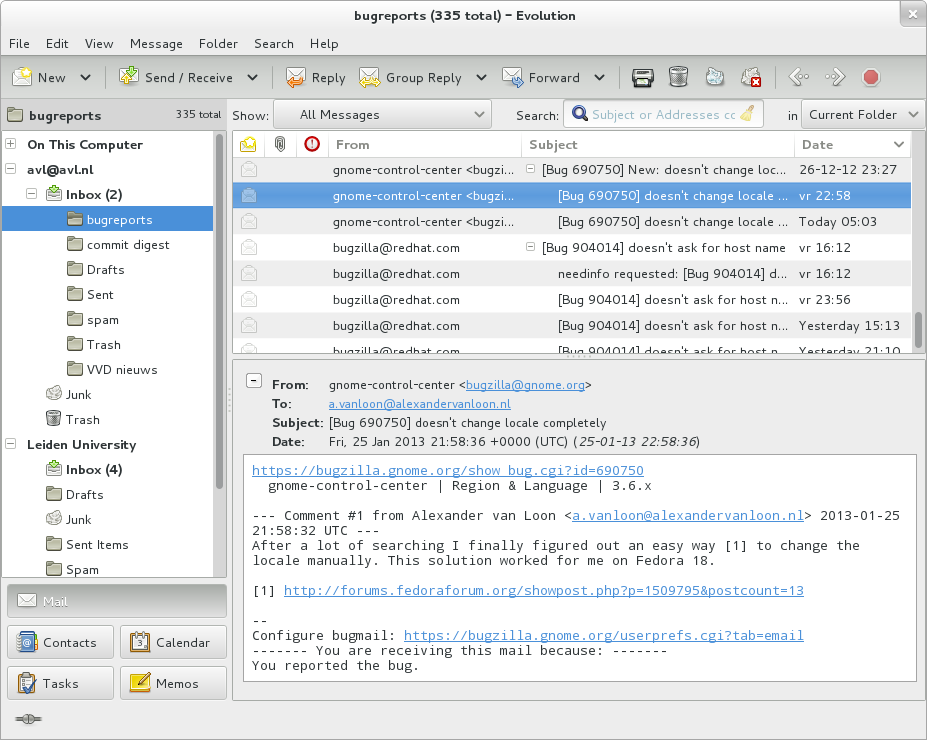
E-mail Client
An email client, email reader or, more formally, message user agent (MUA) or mail user agent is a computer program used to access and manage a user's email. A web application which provides message management, composition, and reception functions may act as a web email client, and a piece of computer hardware or software whose primary or most visible role is to work as an email client may also use the term. Retrieving messages from a mailbox Like most client programs, an email client is only active when a user runs it. The common arrangement is for an email user (the client) to make an arrangement with a remote Mail Transfer Agent (MTA) server for the receipt and storage of the client's emails. The MTA, using a suitable mail delivery agent (MDA), adds email messages to a client's storage as they arrive. The remote mail storage is referred to as the user's mailbox. The default setting on many Unix systems is for the mail server to store formatted messages in mbox, within the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
E-mail
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
List Of TCP And UDP Port Numbers
This is a list of TCP and UDP port numbers used by protocols for operation of network applications. The Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP) only need one port for duplex, bidirectional traffic. They usually use port numbers that match the services of the corresponding TCP or UDP implementation, if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses. However, many unofficial uses of both well-known and registered port numbers occur in practice. Similarly, many of the official assignments refer to protocols that were never or are no longer in common use. This article lists port numbers and their associated protocols that have experienced significant uptake. Table legend Well-known ports The port numbers in the range from 0 to 1023 (0 to 210 − 1) are the ''well-known ports'' or ''system ports''. They are used by system processes that provide wi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
STARTTLS
Opportunistic TLS (Transport Layer Security) refers to extensions in plain text communication protocols, which offer a way to upgrade a plain text connection to an encrypted (TLS or SSL) connection instead of using a separate port for encrypted communication. Several protocols use a command named "STARTTLS" for this purpose. It is a form of opportunistic encryption and is primarily intended as a countermeasure to passive monitoring. The STARTTLS command for IMAP and POP3 is defined in , for SMTP in , for XMPP in and for NNTP in . For IRC, the IRCv3 Working Group has defined the STARTTLS extension. FTP uses the command "AUTH TLS" defined in and LDAP defines a protocol extension OID in . HTTP uses upgrade header. Layering TLS is application-neutral; in the words of : :One advantage of TLS is that it is application protocol independent. Higher-level protocols can layer on top of the TLS protocol transparently. The TLS standard, however, does not specify how protocols add sec ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Sockets Layer
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in securing HTTPS remains the most publicly visible. The TLS protocol aims primarily to provide security, including privacy (confidentiality), integrity, and authenticity through the use of cryptography, such as the use of certificates, between two or more communicating computer applications. It runs in the presentation layer and is itself composed of two layers: the TLS record and the TLS handshake protocols. The closely related Datagram Transport Layer Security (DTLS) is a communications protocol providing security to datagram-based applications. In technical writing you often you will see references to (D)TLS when it applies to both versions. TLS is a proposed Internet Engineering Task Force (IETF) standard, first defined in 1999, an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IMAP
In computing, the Internet Message Access Protocol (IMAP) is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. IMAP is defined by . IMAP was designed with the goal of permitting complete management of an email box by multiple email clients, therefore clients generally leave messages on the server until the user explicitly deletes them. An IMAP server typically listens on port number 143. IMAP over SSL/TLS (IMAPS) is assigned the port number 993. Virtually all modern e-mail clients and servers support IMAP, which along with the earlier POP3 (Post Office Protocol) are the two most prevalent standard protocols for email retrieval. Many webmail service providers such as Gmail and Outlook.com also provide support for both IMAP and POP3. Email protocols The Internet Message Access Protocol is an application layer Internet protocol that allows an e-mail client to access email on a remote mail server. The cu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Message Access Protocol
In computing, the Internet Message Access Protocol (IMAP) is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. IMAP is defined by . IMAP was designed with the goal of permitting complete management of an email box by multiple email clients, therefore clients generally leave messages on the server until the user explicitly deletes them. An IMAP server typically listens on port number 143. IMAP over SSL/TLS (IMAPS) is assigned the port number 993. Virtually all modern e-mail clients and servers support IMAP, which along with the earlier POP3 (Post Office Protocol) are the two most prevalent standard protocols for email retrieval. Many webmail service providers such as Gmail and Outlook.com also provide support for both IMAP and POP3. Email protocols The Internet Message Access Protocol is an application layer Internet protocol that allows an e-mail client to access email on a remote mail serve ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Transport Layer Security
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in securing HTTPS remains the most publicly visible. The TLS protocol aims primarily to provide security, including privacy (confidentiality), integrity, and authenticity through the use of cryptography, such as the use of certificates, between two or more communicating computer applications. It runs in the presentation layer and is itself composed of two layers: the TLS record and the TLS handshake protocols. The closely related Datagram Transport Layer Security (DTLS) is a communications protocol providing security to datagram-based applications. In technical writing you often you will see references to (D)TLS when it applies to both versions. TLS is a proposed Internet Engineering Task Force (IETF) standard, first defined in 1999, and the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mozilla Thunderbird
Mozilla Thunderbird is a free and open-source cross-platform email client, personal information manager, news client, RSS and chat client developed by the Mozilla Foundation and operated by subsidiary MZLA Technologies Corporation. The project strategy was originally modeled after that of Mozilla's Firefox web browser. Features Thunderbird is an email, newsgroup, news feed, and chat (XMPP/ IRC) client with personal information manager (PIM) functionality, inbuilt since version 78.0 and previously available from the Lightning calendar extension. Additional features are available from extensions. Message management Thunderbird manages multiple email, newsgroup, and news feed accounts and supports multiple identities within accounts. Features such as quick search, saved search folders ("virtual folders"), advanced message filtering, message grouping, and tags help manage and find messages. On Linux-based systems, system mail ( movemail) accounts were supported until version 91 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
TCP Port
In computer networking, a port is a number assigned to uniquely identify a connection endpoint and to direct data to a specific service. At the software level, within an operating system, a port is a logical construct that identifies a specific process or a type of network service. A port is identified for each transport protocol and address combination by a 16-bit unsigned number, known as the port number. The most common transport protocols that use port numbers are the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP). A port number is always associated with an IP address of a host and the type of transport protocol used for communication. It completes the destination or origination network address of a message. Specific port numbers are reserved to identify specific services so that an arriving packet can be easily forwarded to a running application. For this purpose, port numbers lower than 1024 identify the historically most commonly used services a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Simple Authentication And Security Layer
Simple Authentication and Security Layer (SASL) is a framework for authentication and data security in Internet protocols. It decouples authentication mechanisms from application protocols, in theory allowing any authentication mechanism supported by SASL to be used in any application protocol that uses SASL. Authentication mechanisms can also support ''proxy authorization'', a facility allowing one user to assume the identity of another. They can also provide a ''data security layer'' offering ''data integrity'' and ''data confidentiality'' services. DIGEST-MD5 provides an example of mechanisms which can provide a data-security layer. Application protocols that support SASL typically also support Transport Layer Security (TLS) to complement the services offered by SASL. John Gardiner Myers wrote the original SASL specification (RFC 2222) in 1997. In 2006, that document was replaced by RFC 4422 authored by Alexey Melnikov and Kurt D. Zeilenga. SASL, as defined by RFC 4422 is an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Massachusetts Institute Of Technology
The Massachusetts Institute of Technology (MIT) is a Private university, private Land-grant university, land-grant research university in Cambridge, Massachusetts. Established in 1861, MIT has played a key role in the development of modern technology and science, and is one of the most prestigious and highly ranked academic institutions in the world. Founded in response to the increasing Technological and industrial history of the United States, industrialization of the United States, MIT adopted a European History of European universities, polytechnic university model and stressed laboratory instruction in applied science and engineering. MIT is one of three private land grant universities in the United States, the others being Cornell University and Tuskegee University. The institute has an Campus of the Massachusetts Institute of Technology, urban campus that extends more than a mile (1.6 km) alongside the Charles River, and encompasses a number of major off-campus fa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |


.jpg)