|
Passphrase
A passphrase is a sequence of words or other text used to control access to a computer system, program or data. It is similar to a password in usage, but a passphrase is generally longer for added security. Passphrases are often used to control both access to, and the operation of, Cryptography, cryptographic programs and systems, especially those that derive an encryption key from a passphrase. The origin of the term is by analogy with ''password''. The modern concept of passphrases is believed to have been invented by Sigmund N. Porter in 1982. Security Source: Considering that the information entropy, entropy of written English is less than 1.1 bits per character, passphrases can be relatively weak. NIST has estimated that the 23-character passphrase "IamtheCapitanofthePina4" contains a 45-bit strength. The equation employed here is: : 4 bits (1st character) + 14 bits (characters 2–8) + 18 bits (characters 9–20) + 3 bits (characters 21–23) + 6 bits (bonus f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Diceware
Diceware is a method for creating passphrases, passwords, and other cryptographic variables using ordinary dice as a hardware random number generator. For each word in the passphrase, five rolls of a six-sided die are required. The numbers from 1 to 6 that come up in the rolls are assembled as a five-digit number, e.g. ''43146''. That number is then used to look up a word in a cryptographic word list. In the original Diceware list ''43146'' corresponds to ''munch''. By generating several words in sequence, a lengthy passphrase can thus be constructed randomly. A Diceware word list is any list of unique words, preferably ones the user will find easy to spell and to remember. The contents of the word list do not have to be protected or concealed in any way, as the security of a Diceware passphrase is in the number of words selected, and the number of words each selected word could be taken from. Lists have been compiled for several languages, including Basque, Bulgarian, Cat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Password
A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the ''claimant'' while the party verifying the identity of the claimant is called the ''verifier''. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity. In general, a password is an arbitrary String (computer science), string of character (computing), characters including letters, digits, or other symbols. If the permissible characters are constrained to be numeric, the corresponding secret is sometimes ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dice
A die (: dice, sometimes also used as ) is a small, throwable object with marked sides that can rest in multiple positions. Dice are used for generating random values, commonly as part of tabletop games, including dice games, board games, role-playing games, and games of chance. A traditional die is a cube with each of its six faces marked with a different number of dots ( pips) from one to six. When thrown or rolled, the die comes to rest showing a random integer from one to six on its upper surface, with each value being equally likely. Dice may also have other polyhedral or irregular shapes, may have faces marked with numerals or symbols instead of pips and may have their numbers carved out from the material of the dice instead of marked on it. Loaded dice are specifically designed or modified to favor some results over others, for cheating or entertainment purposes. History Dice have been used since before recorded history, and their origin is uncertain. It is hypoth ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bitwarden Desktop 2024
Bitwarden is a freemium open-source software, open-source Password manager, password management service that is used to store sensitive information, such as website credentials, in an Encryption, encrypted vault. Functionalities Bitwarden uses zero-knowledge encryption, meaning the company cannot see its users' data. This is achieved by End-to-end encryption, end-to-end encrypting data with AES-CBC 256-bit and by using PBKDF2 SHA-2, SHA-256/Argon2id to derive the encryption key. To Login, log in, a user can use an email-address and password combination, biometric authentication, two-factor authentication (2FA), Passkey (authentication), passkey, single sign-on, or passwordless login via notification approval on a mobile/desktop device. Additional client functionality includes: import of data from more than 50 password managers (such as LastPass, 1Password, and Keeper (password manager), Keeper) passkey management; export to JSON, encrypted JSON, and Comma-separated values, C ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
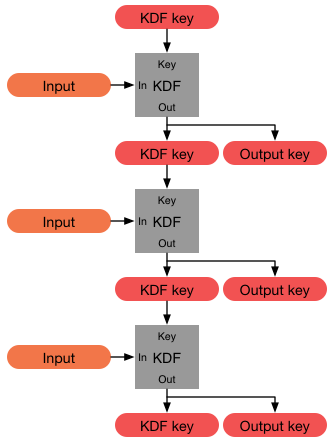
Key Derivation Function
In cryptography, a key derivation function (KDF) is a cryptographic algorithm that derives one or more secret keys from a secret value such as a master key, a password, or a passphrase using a pseudorandom function (which typically uses a cryptographic hash function or block cipher). KDFs can be used to stretch keys into longer keys or to obtain keys of a required format, such as converting a group element that is the result of a Diffie–Hellman key exchange into a symmetric key for use with AES. Keyed cryptographic hash functions are popular examples of pseudorandom functions used for key derivation. History The first deliberately slow (key stretching) password-based key derivation function was called "crypt" (or "crypt(3)" after its man page), and was invented by Robert Morris in 1978. It would encrypt a constant (zero), using the first 8 characters of the user's password as the key, by performing 25 iterations of a modified DES encryption algorithm (in which a 12-b ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Windows XP
Windows XP is a major release of Microsoft's Windows NT operating system. It was released to manufacturing on August 24, 2001, and later to retail on October 25, 2001. It is a direct successor to Windows 2000 for high-end and business users and Windows Me for home users. Development of Windows XP began in the late 1990s under the codename "Windows Neptune, Neptune", built on the Architecture of Windows NT#Kernel, Windows NT kernel and explicitly intended for mainstream consumer use. An updated version of Windows 2000 was also initially planned for the business market. However, in January 2000, both projects were scrapped in favor of a single OS codenamed "Whistler", which would serve as a single platform for both consumer and business markets. As a result, Windows XP is the first consumer edition of Windows not based on the Windows 95 kernel or MS-DOS. Upon its release, Windows XP received critical acclaim, noting increased performance and stability (especially compared to Wi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Windows 2000
Windows 2000 is a major release of the Windows NT operating system developed by Microsoft, targeting the server and business markets. It is the direct successor to Windows NT 4.0, and was Software release life cycle#Release to manufacturing (RTM), released to manufacturing on December 15, 1999, and then to retail on February 17, 2000 for all versions, with Windows 2000 Datacenter Server being released to retail on September 26, 2000. Windows 2000 introduces NTFS 3.0, Encrypting File System, and basic and dynamic disk storage. Support for people with disabilities is improved over Windows NT 4.0 with a number of new Assistive technology, assistive technologies, and Microsoft increased support for different languages and Locale (computer software), locale information. The Windows 2000 Server family has additional features, most notably the introduction of Active Directory, which in the years following became a widely used directory service in business environments. Although not pre ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Windows NT
Windows NT is a Proprietary software, proprietary Graphical user interface, graphical operating system produced by Microsoft as part of its Windows product line, the first version of which, Windows NT 3.1, was released on July 27, 1993. Originally made for the workstation, office, and Server (computing), server markets, the Windows NT line was made available to consumers with the release of Windows XP in 2001. The underlying technology of Windows NT continues to exist to this day with incremental changes and improvements, with the latest version of Windows based on Windows NT being Windows Server 2025 announced in 2024. The name "Windows NT" originally denoted the major technological advancements that it had introduced to the Windows product line, including eliminating the 16-bit computing, 16-bit memory access limitations of earlier Windows releases such as Windows 3.1 and the Windows 9x series. Each Windows release built on this technology is considered to be based on, if not a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Microsoft LAN Manager
LAN Manager is a discontinued network operating system (NOS) available from multiple vendors and developed by Microsoft in cooperation with 3Com Corporation. It was designed to succeed 3Com's 3+Share network server software which ran atop a heavily modified version of MS-DOS. History The LAN Manager OS/2 operating system was co-developed by IBM and Microsoft, using the Server Message Block (SMB) protocol. It originally used SMB atop either the NetBIOS Frames (NBF) protocol or a specialized version of the Xerox Network Systems (XNS) protocol. These legacy protocols had been inherited from previous products such as MS-Net for MS-DOS, Xenix-NET for MS-Xenix, and the afore-mentioned 3+Share. A version of LAN Manager for Unix-based systems called LAN Manager/X was also available. LAN Manager/X was the basis for Digital Equipment Corporation's Pathworks product for OpenVMS, Ultrix and Tru64. Despite support from 3Com, IBM, Digital, and Digital Communications Associates, '' PC'' wro ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
PBKDF2
In cryptography, PBKDF1 and PBKDF2 (Password-Based Key Derivation Function 1 and 2) are key derivation functions with a sliding computational cost, used to reduce vulnerability to brute-force attacks. PBKDF2 is part of RSA Laboratories' Public-Key Cryptography Standards (PKCS) series, specifically PKCS#5 v2.0, also published as Internet Engineering Task Force's RFC2898. It supersedes PBKDF1, which could only produce derived keys up to 160 bits long. RFC8018 (PKCS#5 v2.1), published in 2017, recommends PBKDF2 for password hashing. Purpose and operation PBKDF2 applies a pseudorandom function, such as hash-based message authentication code (HMAC), to the input password or passphrase along with a salt value and repeats the process many times to produce a ''derived key'', which can then be used as a cryptographic key in subsequent operations. The added computational work makes password cracking much more difficult, and is known as key stretching. When the standard was written ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Pretty Good Privacy
Pretty Good Privacy (PGP) is an encryption software, encryption program that provides cryptographic privacy and authentication for data communication. PGP is used for digital signature, signing, encrypting, and decrypting texts, Email, e-mails, files, directories, and whole disk partitions and to increase the security of e-mail communications. Phil Zimmermann developed PGP in 1991. PGP and similar software follow the OpenPGP standard (RFC 4880), an open standard for encryption, encrypting and decrypting data. Modern versions of PGP are interoperability, interoperable with GnuPG and other OpenPGP-compliant systems. The OpenPGP standard has received criticism for its long-lived keys and the difficulty in learning it, as well as the EFAIL, Efail security vulnerability that previously arose when select e-mail programs used OpenPGP with S/MIME. The new OpenPGP standard (RFC 9580) has also been criticised by the maintainer of GnuPG Werner Koch, who in response created his own speci ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Acronym
An acronym is a type of abbreviation consisting of a phrase whose only pronounced elements are the initial letters or initial sounds of words inside that phrase. Acronyms are often spelled with the initial Letter (alphabet), letter of each word in all caps with no punctuation. For some, an initialism or alphabetism connotes this general meaning, and an ''acronym'' is a subset with a narrower definition; an acronym is pronounced as a word rather than as a sequence of letters. In this sense, ''NASA'' () is an acronym, but ''United States, USA'' () is not. The broader sense of ''acronym'', ignoring pronunciation, is its original meaning and in common use. . Dictionary and style-guide editors dispute whether the term ''acronym'' can be legitimately applied to abbreviations which are not pronounced as words, and they do not agree on acronym space (punctuation), spacing, letter case, casing, and punctuation. The phrase that the acronym stands for is called its . The of an acron ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |