|
NordPass
NordPass is a proprietary password manager launched in 2019. It is meant to help its users to organise their passwords and secure notes, keeping them in a single place — an encrypted password vault. This service comes in both free and premium versions, though the free version lacks much of the paid functionality like multi-device login. NordPass is a cross-platform application available on Windows, macOS, Linux, Android, and iOS. It also offers browser extensions on Google Chrome, Mozilla Firefox, Microsoft Edge, Brave, Opera, and Safari. History NordPass was developed by the same cybersecurity team that created NordVPN, a VPN service provider. Security features * NordPass is built with the ChaCha20 encryption algorithm specifically the XChaCha variant. * NordPass has zero-knowledge architecture, meaning that passwords are encrypted on the user's device and only then stored in the cloud. This way, NordPass cannot view, edit, or in any other way manage users’ password ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
NordVPN
NordVPN is a VPN service provided by company Nordsec Ltd with applications for Microsoft Windows, macOS, Linux, Android, iOS, and Android TV. Manual setup is available for wireless routers, NAS devices, and other platforms. NordVPN is developed by Nord Security (Nordsec Ltd), a company that creates cybersecurity software and was initially supported by the Lithuanian startup accelerator and business incubator Tesonet. NordVPN operates under the jurisdiction of Panama, as the country has no mandatory data retention laws and does not participate in the Five Eyes or Fourteen Eyes intelligence sharing alliances. Its offices are located in Lithuania, the United Kingdom, Panama and the Netherlands. History NordVPN was established in 2012 by a group of childhood friends which included Tomas Okmanas. Late in May 2016, it presented an Android app, followed by an iOS app in June the same year. In October 2017, it launched a browser extension for Google Chrome. In June 2018, the se ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Virtual Private Network
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. The benefits of a VPN include increases in functionality, security, and management of the private network. It provides access to resources that are inaccessible on the public network and is typically used for remote workers. Encryption is common, although not an inherent part of a VPN connection. A VPN is created by establishing a virtual point-to-point connection through the use of dedicated circuits or with tunneling protocols over existing networks. A VPN available from the public Internet can provide some of the benefits of a wide area network (WAN). From a user perspective, the resources available within the private network can be accessed remotely. Types Virtual private networks may be classified into several categories: ;Remote acce ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
YubiKey
The YubiKey is a hardware authentication device manufactured by Yubico to protect access to computers, networks, and online services that supports one-time passwords (OTP), public-key cryptography, and authentication, and the Universal 2nd Factor (U2F) and FIDO2 protocols developed by the FIDO Alliance. It allows users to securely log into their accounts by emitting one-time passwords or using a FIDO-based public/private key pair generated by the device. YubiKey also allows for storing static passwords for use at sites that do not support one-time passwords. Google, Amazon, Microsoft, Twitter, and Facebook use YubiKey devices to secure employee accounts as well as end user accounts. Some password managers support YubiKey. Yubico also manufactures the Security Key, a similar lower cost device with only FIDO2/WebAuthn and FIDO/U2F support. The YubiKey implements the HMAC-based One-time Password Algorithm (HOTP) and the Time-based One-time Password Algorithm (TOTP), and identifie ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Universal 2nd Factor
Universal 2nd Factor (U2F) is an open standard that strengthens and simplifies two-factor authentication (2FA) using specialized Universal Serial Bus (USB) or near-field communication (NFC) devices based on similar security technology found in smart cards. It is succeeded by the FIDO2 Project, which includes the W3C Web Authentication (WebAuthn) standard and the FIDO Alliance's Client to Authenticator Protocol 2 (CTAP2). While initially developed by Google and Yubico, with contribution from NXP Semiconductors, the standard is now hosted by the FIDO Alliance. Advantages (and disadvantages) While Time-based one-time passwords (e.g. 6-digit codes generated on Google Authenticator) were a significant improvement over SMS-based security codes, a number of security vulnerabilities were still possible to exploit, which U2F sought to improve. Specifically: In terms of disadvantages, one significant difference and potential drawback to be considered regarding hardware-based U2F ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
FIDO Alliance
The FIDO ("Fast IDentity Online") Alliance is an open industry association launched in February 2013 whose stated mission is to develop and promote authentication standards that "help reduce the world’s over-reliance on passwords". FIDO addresses the lack of interoperability among devices that use strong authentication and reduces the problems users face creating and remembering multiple usernames and passwords. FIDO supports a full range of authentication technologies, including biometrics such as fingerprint and iris scanners, voice and facial recognition, as well as existing solutions and communications standards, such as Trusted Platform Modules (TPM), USB security tokens, embedded Secure Elements (eSE), smart cards, and near field communication (NFC). The USB security token device may be used to authenticate using a simple password (e.g. four-digit PIN) or by pressing a button. The specifications emphasize a device-centric model. Authentication over the wire happens usi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Google Authenticator
Google Authenticator is a software-based authenticator by Google that implements two-step verification services using the Time-based One-time Password Algorithm (TOTP; specified in RFC 6238) and HMAC-based One-time Password algorithm (HOTP; specified in RFC 4226), for authenticating users of software applications. When logging into a site supporting Authenticator (including Google services) or using Authenticator-supporting third-party applications such as password managers or file hosting services, Authenticator generates a six- to eight-digit one-time password which users must enter in addition to their usual login details. Google provides Android, BlackBerry, and iOS versions of Authenticator. An official open-source fork of the Android app is available on GitHub. However, this fork has not been updated since 2020. Likewise, for old versions of the Google Authenticator apps for iOS and BlackBerry, the source code is also freely available. Yet this source code, too, has not ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Multi-factor Authentication
Multi-factor authentication (MFA; encompassing two-factor authentication, or 2FA, along with similar terms) is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence (or factors) to an authentication mechanism: knowledge (something only the user knows), possession (something only the user has), and inherence (something only the user is). MFA protects user data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password. A ''third-party authenticator'' (TPA) app enables two-factor authentication, usually by showing a randomly generated and frequently changing code to use for authentication. Factors Authentication takes place when someone tries to log into a computer resource (such as a network, device, or application). The resource requires the u ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Two-factor Authentication
Multi-factor authentication (MFA; encompassing two-factor authentication, or 2FA, along with similar terms) is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence (or factors) to an authentication mechanism: knowledge (something only the user knows), possession (something only the user has), and inherence (something only the user is). MFA protects user data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password. A ''third-party authenticator'' (TPA) app enables two-factor authentication, usually by showing a randomly generated and frequently changing code to use for authentication. Factors Authentication takes place when someone tries to log into a computer resource (such as a network, device, or application). The resource requires the u ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Master Password (algorithm)
Master Password is a type of algorithm first implemented by Maarten Billemont for creating unique passwords in a reproducible manner. It differs from traditional password managers in that the passwords are not stored on disk or in the cloud, but are regenerated every time from information entered by the user: Their name, a master password, and a unique identifier for the service the password is intended for (usually the URL). By not storing the passwords anywhere, this approach makes it harder for attackers to steal or intercept them. It also removes the need for synchronization between devices, backups of potential password databases and risks of data breach. This is sometimes called ''sync-less password management''. Algorithm Billemont's implementation involves the following parameters: * name: The username, used as a salt. The user's full name is chosen as it provides a sufficiently high level of entropy while being unlikely to be forgotten. * master_password: The secret f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
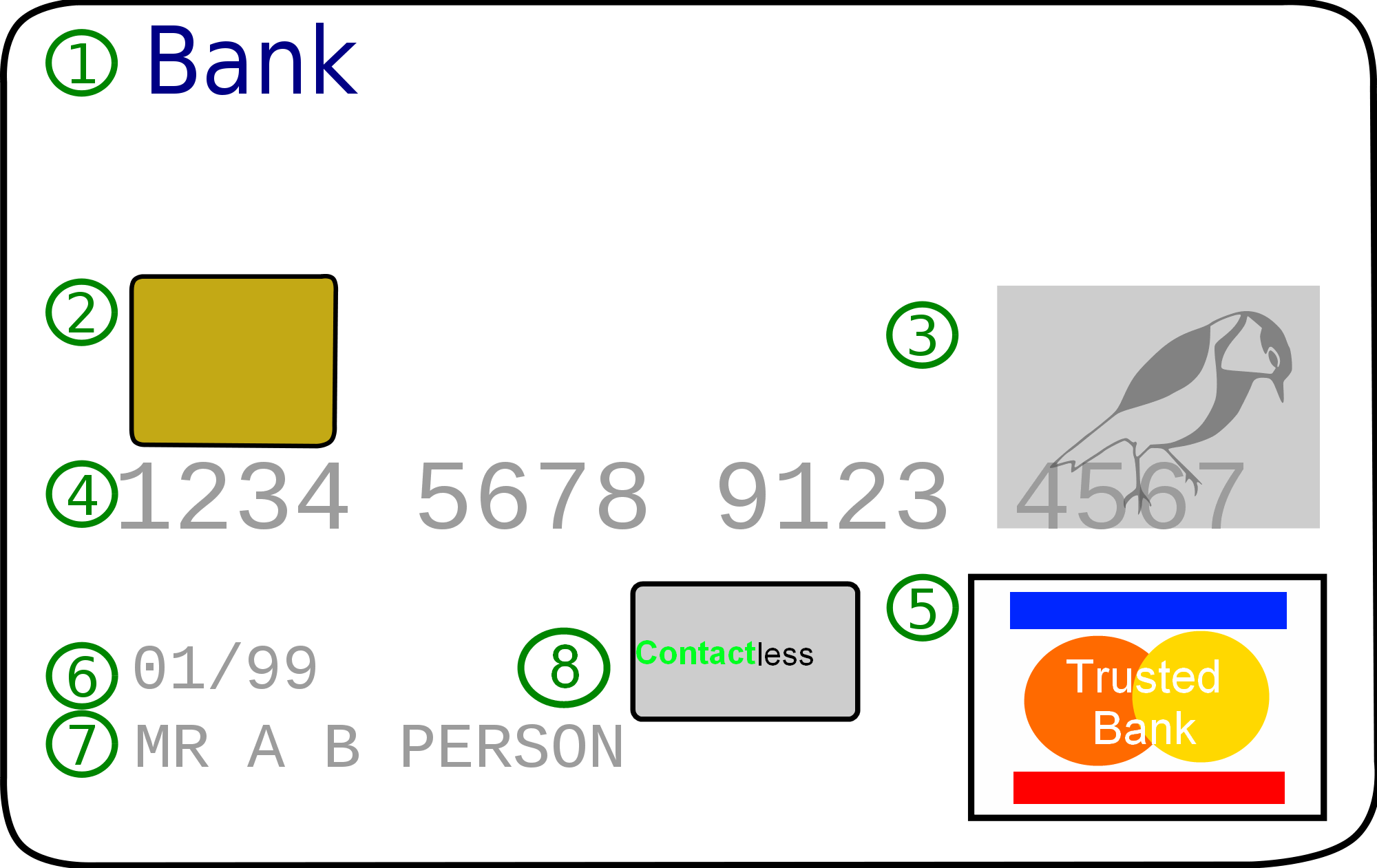
Credit Card
A credit card is a payment card issued to users (cardholders) to enable the cardholder to pay a merchant for goods and services based on the cardholder's accrued debt (i.e., promise to the card issuer to pay them for the amounts plus the other agreed charges). The card issuer (usually a bank or credit union) creates a revolving account and grants a line of credit to the cardholder, from which the cardholder can borrow money for payment to a merchant or as a cash advance. There are two credit card groups: consumer credit cards and business credit cards. Most cards are plastic, but some are metal cards (stainless steel, gold, palladium, titanium), and a few gemstone-encrusted metal cards. A regular credit card is different from a charge card, which requires the balance to be repaid in full each month or at the end of each statement cycle. In contrast, credit cards allow the consumers to build a continuing balance of debt, subject to interest being charged. A credit car ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Login
In computer security, logging in (or logging on, signing in, or signing on) is the process by which an individual gains access to a computer system by identifying and authenticating themselves. The user credentials are typically some form of username and a matching password, and these credentials themselves are sometimes referred to as ''a'' login (or logon, sign-in, sign-on).Oxford Dictionaries definition of ''login''. detail and definition of ''login'' and ''logging in''. In practice, modern secure systems often require a second factor such as |
Encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decipher a ciphertext back to plaintext and access the original information. Encryption does not itself prevent interference but denies the intelligible content to a would-be interceptor. For technical reasons, an encryption scheme usually uses a pseudo-random encryption key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users. Historically, various forms of encryption have been used to aid in cryptography. Early encryption techniques were often used in military ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |