|
Nonrepudiation
Non-repudiation refers to a situation where a statement's author cannot successfully dispute its authorship or the validity of an associated contract. The term is often seen in a legal setting when the authenticity of a signature is being challenged. In such an instance, the authenticity is being "repudiated". For example, Mallory buys a cell phone for $100, writes a paper cheque as payment, and signature, signs the cheque with a pen. Later, she finds that she can't afford it, and claims that Cheque fraud, the cheque is a forgery. The signature guarantees that only Mallory could have signed the cheque, and so Mallory's bank must pay the cheque. This is non-repudiation; Mallory cannot repudiate the cheque. In practice, pen-and-paper signatures aren't hard to Signature forgery, forge, but digital signatures can be very hard to break. In security In general, ''non-repudiation'' involves associating actions or changes with a unique individual. For example, a secure area may use a Key ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Contract
A contract is a legally enforceable agreement between two or more parties that creates, defines, and governs mutual rights and obligations between them. A contract typically involves the transfer of goods, services, money, or a promise to transfer any of those at a future date. In the event of a breach of contract, the injured party may seek judicial remedies such as damages or rescission. Contract law, the field of the law of obligations concerned with contracts, is based on the principle that agreements must be honoured. Contract law, like other areas of private law, varies between jurisdictions. The various systems of contract law can broadly be split between common law jurisdictions, civil law jurisdictions, and mixed law jurisdictions which combine elements of both common and civil law. Common law jurisdictions typically require contracts to include consideration in order to be valid, whereas civil and most mixed law jurisdictions solely require a meeting of the mind ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Message Authentication Code
In cryptography, a message authentication code (MAC), sometimes known as a ''tag'', is a short piece of information used for authenticating a message. In other words, to confirm that the message came from the stated sender (its authenticity) and has not been changed. The MAC value protects a message's data integrity, as well as its authenticity, by allowing verifiers (who also possess the secret key) to detect any changes to the message content. Terminology The term message integrity code (MIC) is frequently substituted for the term ''MAC'', especially in communications to distinguish it from the use of the latter as ''media access control address'' (''MAC address''). However, some authors use MIC to refer to a message digest, which aims only to uniquely but opaquely identify a single message. RFC 4949 recommends avoiding the term ''message integrity code'' (MIC), and instead using ''checksum'', ''error detection code'', '' hash'', ''keyed hash'', ''message authentication code'', ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Plausible Deniability
Plausible deniability is the ability of people, typically senior officials in a formal or informal chain of command, to denial, deny knowledge of or responsibility for any damnable actions committed by members of their organizational hierarchy. They may do so because of a lack or absence of evidence that can confirm their participation, even if they were personally involved in or at least willful blindness, willfully ignorant of the actions. If illegal or otherwise disreputable and unpopular activities become public, high-ranking officials may deny any awareness of such acts to insulate themselves and Blame#Blame shifting, shift the blame onto the agents who carried out the acts, as they are confident that their doubters will be unable to prove otherwise. The lack of evidence to the contrary ostensibly makes the denial plausible (credible), but sometimes, it makes any accusations only cause of action, unactionable. The term typically implies forethought, such as intentionally setti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Personal Identification Number
A personal identification number (PIN), or sometimes redundantly a PIN number or PIN code, is a numeric (sometimes alpha-numeric) passcode used in the process of authenticating a user accessing a system. The PIN has been the key to facilitating the private data exchange between different data-processing centers in computer networks for financial institutions, governments, and enterprises. PINs may be used to authenticate banking systems with cardholders, governments with citizens, enterprises with employees, and computers with users, among other uses. In common usage, PINs are used in ATM or POS transactions, secure access control (e.g. computer access, door access, car access), internet transactions, or to log into a restricted website. History The PIN originated with the introduction of the automated teller machine (ATM) in 1967, as an efficient way for banks to dispense cash to their customers. The first ATM system was that of Barclays in London, in 1967; it accepted ch ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Common Access Card
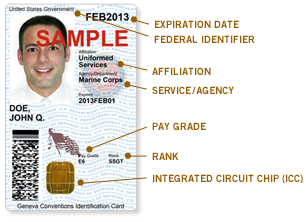
The Common Access Card, also commonly referred to as the CAC is a smart card about the size of a credit card. It is the standard identification for Active Duty United States Defense personnel, to include the Selected Reserve and National Guard, United States Department of Defense (DoD) civilian employees, United States Coast Guard (USCG) civilian employees and eligible DoD and USCG contractor personnel. It is also the principal card used to enable physical access to buildings and controlled spaces, and it provides access to defense computer networks and systems. It also serves as an identification card under the Geneva Conventions (especially the Third Geneva Convention). In combination with a personal identification number, a CAC satisfies the requirement for two-factor authentication: something the user knows combined with something the user has. The CAC also satisfies the requirements for digital signature and data encryption technologies: authentication, integrity and non-rep ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
United States Department Of Defense
The United States Department of Defense (DoD, USDOD or DOD) is an executive branch department of the federal government charged with coordinating and supervising all agencies and functions of the government directly related to national security and the United States Armed Forces. The DoD is the largest employer in the world, with over 1.34 million active-duty service members (soldiers, marines, sailors, airmen, and guardians) as of June 2022. The DoD also maintains over 778,000 National Guard and reservists, and over 747,000 civilians bringing the total to over 2.87 million employees. Headquartered at the Pentagon in Arlington, Virginia, just outside Washington, D.C., the DoD's stated mission is to provide "the military forces needed to deter war and ensure our nation's security". The Department of Defense is headed by the secretary of defense, a cabinet-level head who reports directly to the president of the United States. Beneath the Department of Defense are th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Smart Card
A smart card, chip card, or integrated circuit card (ICC or IC card) is a physical electronic authentication device, used to control access to a resource. It is typically a plastic credit card-sized card with an embedded integrated circuit (IC) chip. Many smart cards include a pattern of metal contacts to electrically connect to the internal chip. Others are contactless, and some are both. Smart cards can provide personal identification, authentication, data storage, and application processing. Applications include identification, financial, mobile phones (SIM), public transit, computer security, schools, and healthcare. Smart cards may provide strong security authentication for single sign-on (SSO) within organizations. Numerous nations have deployed smart cards throughout their populations. The universal integrated circuit card, or SIM card, is also a type of smart card. , 10.5billion smart card IC chips are manufactured annually, including 5.44billion SIM card IC chips. Hist ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Digital Signature
A digital signature is a mathematical scheme for verifying the authenticity of digital messages or documents. A valid digital signature, where the prerequisites are satisfied, gives a recipient very high confidence that the message was created by a known sender (authenticity), and that the message was not altered in transit (integrity). Digital signatures are a standard element of most cryptographic protocol suites, and are commonly used for software distribution, financial transactions, contract management software, and in other cases where it is important to detect forgery or tampering. Digital signatures are often used to implement electronic signatures, which includes any electronic data that carries the intent of a signature, but not all electronic signatures use digital signatures. [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Public Key Certificate
In cryptography, a public key certificate, also known as a digital certificate or identity certificate, is an electronic document used to prove the validity of a public key. The certificate includes information about the key, information about the identity of its owner (called the subject), and the digital signature of an entity that has verified the certificate's contents (called the issuer). If the signature is valid, and the software examining the certificate trusts the issuer, then it can use that key to communicate securely with the certificate's subject. In email encryption, code signing, and e-signature systems, a certificate's subject is typically a person or organization. However, in Transport Layer Security (TLS) a certificate's subject is typically a computer or other device, though TLS certificates may identify organizations or individuals in addition to their core role in identifying devices. TLS, sometimes called by its older name Secure Sockets Layer (SSL), is notable ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Certificate Authority
In cryptography, a certificate authority or certification authority (CA) is an entity that stores, signs, and issues digital certificates. A digital certificate certifies the ownership of a public key by the named subject of the certificate. This allows others (relying parties) to rely upon signatures or on assertions made about the private key that corresponds to the certified public key. A CA acts as a trusted third party—trusted both by the subject (owner) of the certificate and by the party relying upon the certificate. The format of these certificates is specified by the X.509 or EMV standard. One particularly common use for certificate authorities is to sign certificates used in HTTPS, the secure browsing protocol for the World Wide Web. Another common use is in issuing identity cards by national governments for use in electronically signing documents. Overview Trusted certificates can be used to create secure connections to a server via the Internet. A certificate is e ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Notary
A notary is a person authorised to perform acts in legal affairs, in particular witnessing signatures on documents. The form that the notarial profession takes varies with local legal systems. A notary, while a legal professional, is distinct from an advocate in that they do not represent the person who engages their services, or act in contentious matters. The Worshipful Company of Scriveners use an old English term for a notary, and are an association of notaries practising in central London since 1373. Overview Documents are notarized to deter fraud and to ensure they are properly executed. An impartial witness (the notary) identifies signers to screen out impostors and to make sure they have entered into agreements knowingly and willingly. Loan documents including Deed, deeds, Affidavit, affidavits, Contract, contracts, and Power of attorney, powers of attorney are very common documents needing notarization. Code of Hammurabi#Laws, Code of Hammurabi Law 122 (c. 1755 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Forensic Analyst
Forensic science, also known as criminalistics, is the application of science to criminal and civil laws, mainly—on the criminal side—during criminal investigation, as governed by the legal standards of admissible evidence and criminal procedure. Forensic science is a broad field that includes; DNA analysis, fingerprint analysis, blood stain pattern analysis, firearms examination and ballistics, tool mark analysis, serology, toxicology, hair and fiber analysis, entomology, questioned documents, anthropology, odontology, pathology, epidemiology, footwear and tire tread analysis, drug chemistry, paint and glass analysis, digital audio video and photo analysis. Forensic scientists collect, preserve, and analyze scientific evidence during the course of an investigation. While some forensic scientists travel to the scene of the crime to collect the evidence themselves, others occupy a laboratory role, performing analysis on objects brought to them by other individuals. Still o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |



.jpg)

