|
Matt Robshaw
Matthew John Barton "Matt" Robshaw is a cryptographer. Formerly a lecturer at Royal Holloway, University of London and a member of the cryptography research group at France Telecom's Orange Labs, he is now a Technical Fellow at Impinj. He coordinated the Symmetric Techniques Virtual Lab (STVL) for ECRYPT. Robshaw's notable work includes the cryptanalysis of a number of cryptographic primitives, including the extension of linear cryptanalysis to use multiple approximations, and the design of the block ciphers Crab and RC6. Robshaw received his Ph.D. A Doctor of Philosophy (PhD, Ph.D., or DPhil; Latin: or ') is the most common degree at the highest academic level awarded following a course of study. PhDs are awarded for programs across the whole breadth of academic fields. Because it is ... in mathematics in 1992 from Royal Holloway, University of London. References External links Matt Robshaw's page at Orange Labs Living people Modern cryptographers Alumni of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Royal Holloway, University Of London
Royal Holloway, University of London (RHUL), formally incorporated as Royal Holloway and Bedford New College, is a public research university and a constituent college of the federal University of London. It has six schools, 21 academic departments and approximately 10,500 undergraduate and postgraduate students from over 100 countries. The campus is located west of Egham, Surrey, from central London. The Egham campus was founded in 1879 by the Victorian entrepreneur and philanthropist Thomas Holloway. Royal Holloway College was officially opened in 1886 by Queen Victoria as an all-women college. It became a member of the University of London in 1900. In 1945, the college admitted male postgraduate students, and in 1965, around 100 of the first male undergraduates. In 1985, Royal Holloway merged with Bedford College (another former all-women's college in London). The merged college was named Royal Holloway and Bedford New College (RHBNC), this remaining the official registered ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
France Telecom
Orange S.A. (), formerly France Télécom S.A. (stylized as france telecom) is a French multinational telecommunications corporation. It has 266 million customers worldwide and employs 89,000 people in France, and 59,000 elsewhere. In 2015, the group had revenue of €40 billion. The company's head office is located in the 15th arrondissement of Paris. Orange has been the company's main brand for mobile, landline, internet and Internet Protocol television (IPTV) services since 2006. The Orange brand originated in the United Kingdom in 1994 after Hutchison Whampoa acquired a controlling stake in Microtel Communications: that company became a subsidiary of Mannesmann in 1999 and then was acquired by France Télécom in 2000. The France Télécom company was rebranded to Orange on 1 July 2013. The company has faced criticism due to the Orange S.A. suicides. History Nationalised service (1878–1980s) In 1792, under the French Revolution, the first communication n ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Impinj
Impinj, Inc. is a manufacturer of radio-frequency identification (RFID) devices and software. The company was founded in 2000 and is headquartered in Seattle, Washington. The company was started based on the research done at the California Institute of Technology by Carver Mead and Chris Diorio. Impinj currently produces EPC Class 1, Gen 2 passive UHF RFID chips, RFID readers, RFID reader chips, and RFID antennas, and software applications for encoding chips, and gathering business intelligence on RFID systems. History Impinj was founded in 2000 based on the research of Carver Mead and his student Chris Diorio. The name Impinj stands for "Impact-ionized Hot-electron Injection". In 2006, Impinj became the first company to introduce products based on the EPCglobal UHF Gen 2 standard. Bear Stearns reported in 2006 that Wal-Mart issued contracts to Impinj and Alien Technology, including them as significant suppliers for a total 15,000 RFID readers needed for Wal-Mart stores and dis ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ECRYPT
ECRYPT (European Network of Excellence in Cryptology) was a 4-year European research initiative launched on 1 February 2004 with the stated objective of promoting the collaboration of European researchers in information security, and especially in cryptology and digital watermarking. ECRYPT listed five core research areas, termed "virtual laboratories": symmetric key algorithms (STVL), public key algorithms (AZTEC), protocol (PROVILAB), secure and efficient implementations (VAMPIRE) and watermarking (WAVILA). In August 2008 the network started another 4-year phase as ECRYPT II. ECRYPT II products Yearly report on algorithms and key lengths During the project, algorithms and key lengths were evaluated yearly. The most recent of these documents is dated 30 September 2012. Key sizes Considering the budget of a large intelligence agency to be about 300 million USD for a single ASIC machine, the recommended ''minimum'' key size is 84 bits, which would give protection for a f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptanalysis
Cryptanalysis (from the Greek ''kryptós'', "hidden", and ''analýein'', "to analyze") refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown. In addition to mathematical analysis of cryptographic algorithms, cryptanalysis includes the study of side-channel attacks that do not target weaknesses in the cryptographic algorithms themselves, but instead exploit weaknesses in their implementation. Even though the goal has been the same, the methods and techniques of cryptanalysis have changed drastically through the history of cryptography, adapting to increasing cryptographic complexity, ranging from the pen-and-paper methods of the past, through machines like the British Bombes and Colossus computers at Bletchley Park in World War II, to the mathematically advanced comput ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Primitive
Cryptographic primitives are well-established, low-level cryptographic algorithms that are frequently used to build cryptographic protocols for computer security systems. These routines include, but are not limited to, one-way hash functions and encryption functions. Rationale When creating cryptographic systems, designers use cryptographic primitives as their most basic building blocks. Because of this, cryptographic primitives are designed to do one very specific task in a precisely defined and highly reliable fashion. Since cryptographic primitives are used as building blocks, they must be very reliable, i.e. perform according to their specification. For example, if an encryption routine claims to be only breakable with number of computer operations, and it is broken with significantly fewer than operations, then that cryptographic primitive has failed. If a cryptographic primitive is found to fail, almost every protocol that uses it becomes vulnerable. Since creating c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Linear Cryptanalysis
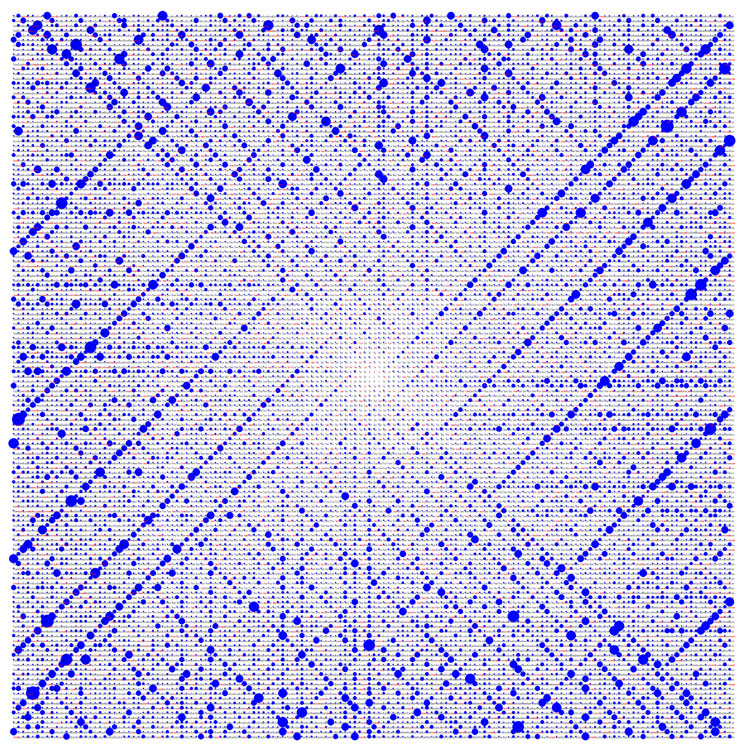
In cryptography, linear cryptanalysis is a general form of cryptanalysis based on finding affine approximations to the action of a cipher. Attacks have been developed for block ciphers and stream ciphers. Linear cryptanalysis is one of the two most widely used attacks on block ciphers; the other being differential cryptanalysis. The discovery is attributed to Mitsuru Matsui, who first applied the technique to the FEAL cipher (Matsui and Yamagishi, 1992). Subsequently, Matsui published an attack on the Data Encryption Standard (DES), eventually leading to the first experimental cryptanalysis of the cipher reported in the open community (Matsui, 1993; 1994). The attack on DES is not generally practical, requiring 247 known plaintexts. A variety of refinements to the attack have been suggested, including using multiple linear approximations or incorporating non-linear expressions, leading to a generalized partitioning cryptanalysis. Evidence of security against linear cryptanalysis ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Block Cipher
In cryptography, a block cipher is a deterministic algorithm operating on fixed-length groups of bits, called ''blocks''. Block ciphers are specified cryptographic primitive, elementary components in the design of many cryptographic protocols and are widely used to encryption, encrypt large amounts of data, including in data exchange protocols. A block cipher uses blocks as an unvarying transformation. Even a secure block cipher is suitable for the encryption of only a single block of data at a time, using a fixed key. A multitude of block cipher modes of operation, modes of operation have been designed to allow their repeated use in a secure way to achieve the security goals of confidentiality and authentication, authenticity. However, block ciphers may also feature as building blocks in other cryptographic protocols, such as universal hash functions and pseudorandom number generators. Definition A block cipher consists of two paired algorithms, one for encryption, , and the othe ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Crab (cipher)
In cryptography, Crab is a block cipher proposed by Burt Kaliski and Matt Robshaw at the first Fast Software Encryption workshop in 1993. Not really intended for use, Crab was developed to demonstrate how ideas from hash functions could be used to create a fast cipher. Crab has an unusually large block size of 8192 bits. Its creators suggested using an 80-bit key, but the cipher could use any key size. The authors didn't specify an actual key schedule, only that the key is used to generate two large sets of subkeys: a permutation of the numbers 0 through 255, and an array of 2048 32-bit numbers. The block is divided into 256 32-bit subblocks, which are permuted at the beginning. Then the algorithm makes four passes over the data, each time applying one of four transformations adapted from MD5. A brief note on the cryptanalysis of Crab is included in Markku-Juhani Saarinen's paper on block ciphers based on SHA-1 In cryptography, SHA-1 (Secure Hash Algorithm 1) is a c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mathematics
Mathematics is an area of knowledge that includes the topics of numbers, formulas and related structures, shapes and the spaces in which they are contained, and quantities and their changes. These topics are represented in modern mathematics with the major subdisciplines of number theory, algebra, geometry, and analysis, respectively. There is no general consensus among mathematicians about a common definition for their academic discipline. Most mathematical activity involves the discovery of properties of abstract objects and the use of pure reason to prove them. These objects consist of either abstractions from nature orin modern mathematicsentities that are stipulated to have certain properties, called axioms. A ''proof'' consists of a succession of applications of deductive rules to already established results. These results include previously proved theorems, axioms, andin case of abstraction from naturesome basic properties that are considered true starting points of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Living People
Related categories * :Year of birth missing (living people) / :Year of birth unknown * :Date of birth missing (living people) / :Date of birth unknown * :Place of birth missing (living people) / :Place of birth unknown * :Year of death missing / :Year of death unknown * :Date of death missing / :Date of death unknown * :Place of death missing / :Place of death unknown * :Missing middle or first names See also * :Dead people * :Template:L, which generates this category or death years, and birth year and sort keys. : {{DEFAULTSORT:Living people 21st-century people People by status ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Modern Cryptographers
Modern may refer to: History *Modern history ** Early Modern period ** Modern age, Late Modern period *** 18th century *** 19th century *** 20th century ** Contemporary history * Moderns, a faction of Freemasonry that existed in the 18th century Philosophy and sociology * Modernity, a loosely defined concept delineating a number of societal, economic and ideological features that contrast with "pre-modern" times or societies ** Late modernity Art * Modernism ** Modernist poetry * Modern art, a form of art * Modern dance, a dance form developed in the early 20th century * Modern architecture, a broad movement and period in architectural history * Modern music (other) Geography *Modra, a Slovak city, referred to in the German language as "Modern" Typography * Modern (typeface), a raster font packaged with Windows XP * Another name for the typeface classification known as Didone (typography) * Modern, a generic font family name for monospaced font, fixed-pitch serif and s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
.jpg)