|
Malumpos Malware
Malumpos is a point of sale malware that are designed to steal or scrape customer’s credit and debit card detail from point of sale system. These are designed in a way that it records point of sale’s data which is running in an Oracle MICROS payment system of the restaurant. The collected data has been used in 333,000 customer sites around the world. Malumpos Malware targets hotels and other US businesses and put the retail customers at risk. This POS RAM Scraper is written in the Delphi programming language. Malumpos monitors, processes, scrapes the stolen data of the infected POS system and the RAM. First it stores the stolen credit or debit card details of the customer from the infected point of sale system once it is swiped. Then it sends the data to the cybercriminal to empty the customer bank balance or the details are sold to the black market. How Malumpos gets Installed Much like the other point of sale malware, the Malumpos get into the computer unknowingly and conc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Point-of-sale Malware
Point-of-sale malware (POS malware) is usually a type of malicious software ( malware) that is used by cybercriminals to target point of sale (POS) and payment terminals with the intent to obtain credit card and debit card information, a card's track 1 or track 2 data and even the CVV code, by various man-in-the-middle attacks, that is the interception of the processing at the retail checkout point of sale system. The simplest, or most evasive, approach is RAM-scraping, accessing the system's memory and exporting the copied information via a remote access trojan (RAT) as this minimizes any software or hardware tampering, potentially leaving no footprints. POS attacks may also include the use of various bits of hardware: dongles, trojan card readers, (wireless) data transmitters and receivers. Being at the gateway of transactions, POS malware enables hackers to process and steal thousands, even millions, of transaction payment data, depending upon the target, the number of devices ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
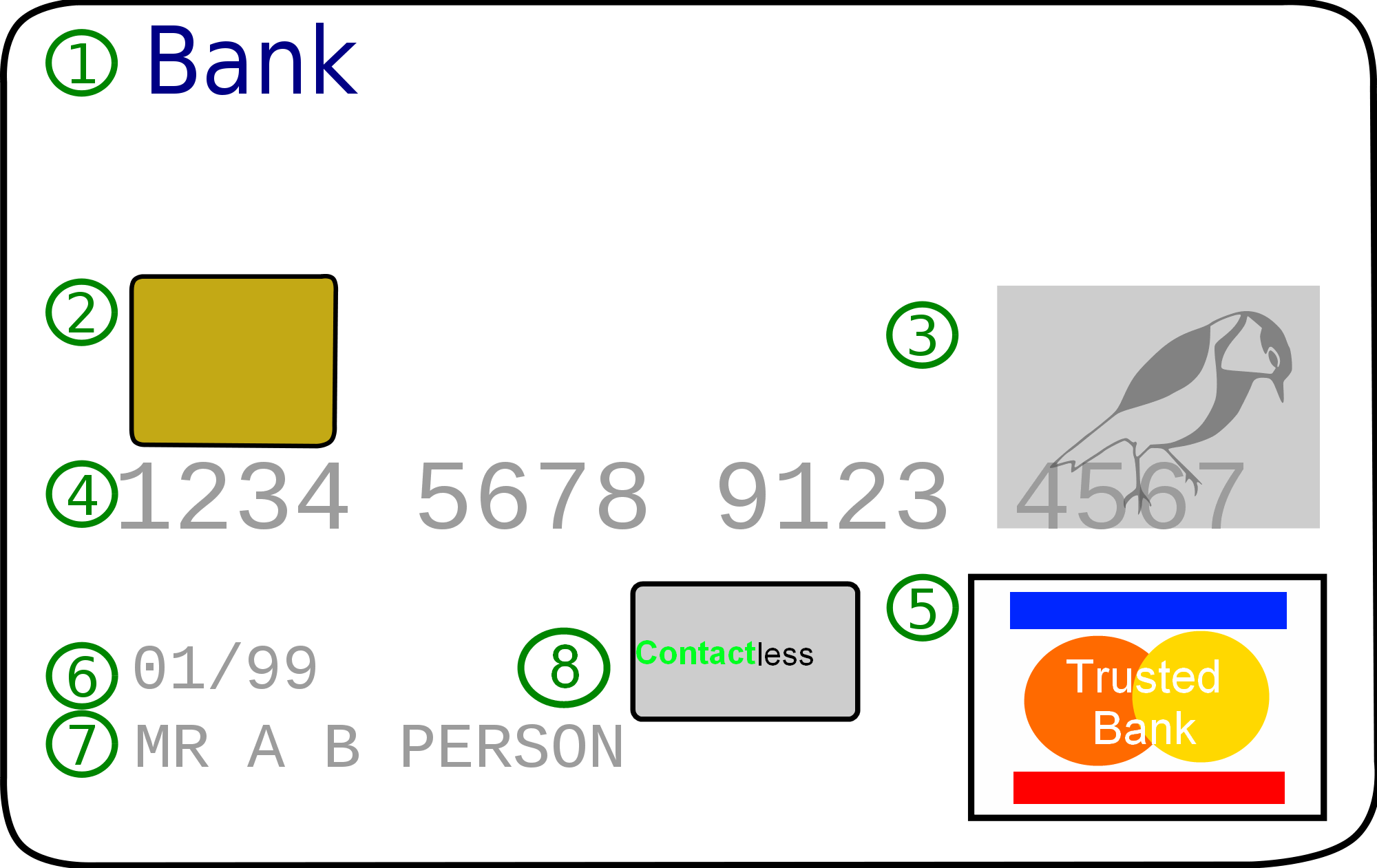
Credit Card
A credit card is a payment card issued to users (cardholders) to enable the cardholder to pay a merchant for goods and services based on the cardholder's accrued debt (i.e., promise to the card issuer to pay them for the amounts plus the other agreed charges). The card issuer (usually a bank or credit union) creates a revolving account and grants a line of credit to the cardholder, from which the cardholder can borrow money for payment to a merchant or as a cash advance. There are two credit card groups: consumer credit cards and business credit cards. Most cards are plastic, but some are metal cards (stainless steel, gold, palladium, titanium), and a few gemstone-encrusted metal cards. A regular credit card is different from a charge card, which requires the balance to be repaid in full each month or at the end of each statement cycle. In contrast, credit cards allow the consumers to build a continuing balance of debt, subject to interest being charged. A credit car ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Debit Card
A debit card, also known as a check card or bank card is a payment card that can be used in place of cash to make purchases. The term '' plastic card'' includes the above and as an identity document. These are similar to a credit card, but unlike a credit card, the money for the purchase must be in the cardholder's bank account at the time of a purchase and is immediately transferred directly from that account to the merchant's account to pay for the purchase. Some debit cards carry a stored value with which a payment is made (prepaid card), but most relay a message to the cardholder's bank to withdraw funds from the cardholder's designated bank account. In some cases, the payment card number is assigned exclusively for use on the Internet and there is no physical card. This is referred to as a virtual card. In many countries, the use of debit cards has become so widespread they have overtaken checks in volume, or have entirely replaced them; in some instances, debit cards ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Point Of Sale
The point of sale (POS) or point of purchase (POP) is the time and place at which a retail transaction is completed. At the point of sale, the merchant calculates the amount owed by the customer, indicates that amount, may prepare an invoice for the customer (which may be a cash register printout), and indicates the options for the customer to make payment. It is also the point at which a customer makes a payment to the merchant in exchange for goods or after provision of a service. After receiving payment, the merchant may issue a receipt for the transaction, which is usually printed but can also be dispensed with or sent electronically. To calculate the amount owed by a customer, the merchant may use various devices such as weighing scales, barcode scanners, and cash registers (or the more advanced "POS cash registers", which are sometimes also called "POS systems"). To make a payment, payment terminals, touch screens, and other hardware and software options are available. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
MICROS Systems
Micros Systems, Inc. (styled lowercase in its logo), incorporated in 1978, was a computer software company. Micros is now owned by Oracle Corporation and renamed Oracle Food and Beverage and Oracle Hospitality (two of the global business units at Oracle Corporation). Micros was headquartered in Columbia, Maryland, United States, and the current business unit it still based there. Micros manufactured and sold computer hardware, software, and services for the restaurant point of sale, hotel, hospitality, sports and entertainment venues, casinos, cruise lines, specialty retail markets and other similar markets. Analyst estimates cited in 2003 put Micros' market share at about 35% of the restaurant point-of-sale business. On June 23, 2014, Oracle Corporation announced its intent to purchase Micros Systems for $68 per share in cash for a total value of approximately $5.3 billion. History The company was incorporated in 1977 as Picos Manufacturing, Inc. and changed its name to Micr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Delphi (programming Language)
Delphi is a general-purpose programming language and a software product that uses the Delphi dialect of the Object Pascal programming language and provides an integrated development environment (IDE) for rapid application development of desktop, mobile, web, and console software, currently developed and maintained by Embarcadero Technologies. Delphi's compilers generate native code for Microsoft Windows, macOS, iOS, Android and Linux (x64). Delphi includes a code editor, a visual designer, an integrated debugger, a source code control component, and support for third-party plugins. The code editor features Code Insight (code completion), Error Insight (real-time error-checking), and refactoring. The visual forms designer has the option of using either the Visual Component Library (VCL) for pure Windows development or the FireMonkey (FMX) framework for cross-platform development. Database support is a key feature and is provided by FireDAC (Database Access Components). Delphi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Random-access Memory
Random-access memory (RAM; ) is a form of computer memory that can be read and changed in any order, typically used to store working Data (computing), data and machine code. A Random access, random-access memory device allows data items to be read (computer), read or written in almost the same amount of time irrespective of the physical location of data inside the memory, in contrast with other direct-access data storage media (such as hard disks, CD-RWs, DVD-RWs and the older Magnetic tape data storage, magnetic tapes and drum memory), where the time required to read and write data items varies significantly depending on their physical locations on the recording medium, due to mechanical limitations such as media rotation speeds and arm movement. RAM contains multiplexer, multiplexing and demultiplexing circuitry, to connect the data lines to the addressed storage for reading or writing the entry. Usually more than one bit of storage is accessed by the same address, and RAM ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cybercrime
A cybercrime is a crime that involves a computer or a computer network.Moore, R. (2005) "Cyber crime: Investigating High-Technology Computer Crime," Cleveland, Mississippi: Anderson Publishing. The computer may have been used in committing the crime, or it may be the target. Cybercrime may harm someone's security or finances. There are many privacy concerns surrounding cybercrime when confidential information is intercepted or disclosed, lawfully or otherwise. Internationally, both governmental and non-state actors engage in cybercrimes, including espionage, financial theft, and other cross-border crimes. Cybercrimes crossing international borders and involving the actions of at least one nation-state are sometimes referred to as cyberwarfare. Warren Buffett describes cybercrime as the "number one problem with mankind" and said that cybercrime "poses real risks to humanity." A 2014 report sponsored by McAfee estimated that cybercrime resulted in $445 billion in annual damage ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Explorer
Internet Explorer (formerly Microsoft Internet Explorer and Windows Internet Explorer, commonly abbreviated IE or MSIE) is a series of graphical user interface, graphical web browsers developed by Microsoft which was used in the Microsoft Windows, Windows line of operating systems (in Windows 11, Windows Server Insider Build 22463 and Windows Server Insider Build 25110, it is replaced by the Chromium (web browser), Chromium version of Microsoft Edge). Starting in 1995, It was first released as part of the add-on package Microsoft Plus!, Plus! for Windows 95 that year. Later versions were available as free downloads, or in-service packs, and included in the original equipment manufacturer (OEM) service releases of Windows 95 and later versions of Windows. Microsoft spent over per year on Internet Explorer in the late 1990s, with over 1,000 people involved in the project by 1999. New feature development for the browser was discontinued in 2016 in favor of new browser Microsoft Ed ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyber Security Standards
IT security standards or cyber security standards are techniques generally outlined in published materials that attempt to protect the cyber environment of a user or organization. This environment includes users themselves, networks, devices, all software, processes, information in storage or transit, applications, services, and systems that can be connected directly or indirectly to networks. The principal objective is to reduce the risks, including preventing or mitigating cyber-attacks. These published materials consist of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance and technologies. History Cybersecurity standards have existed over several decades as users and providers have collaborated in many domestic and international forums to effect the necessary capabilities, policies, and practices – generally emerging from work at the Stanford Consortium for Research on Information Sec ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
List Of Cyber Attack Threat Trends
A cyberattack is any offensive maneuver that targets computer information systems, computer networks, infrastructures, or personal computer devices. An attacker is a person or process that attempts to access data, functions, or other restricted areas of the system without authorization, potentially with malicious intent. Depending on the context, cyberattacks can be part of cyber warfare or cyberterrorism. A cyberattack can be employed by sovereign states, individuals, groups, societies or organisations and it may originate from an anonymous source. A product that facilitates a cyberattack is sometimes called a cyber weapon. Cyber attacks have increased with an alarming rate for the last few years A cyberattack may steal, alter, or destroy a specified target by hacking into a susceptible system. Cyberattacks can range from installing spyware on a personal computer to attempting to destroy the infrastructure of entire nations. Legal experts are seeking to limit the use of the te ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyber Electronic Warfare
Cyber may refer to: Computing and the Internet * ''Cyber-'', from cybernetics, a transdisciplinary approach for exploring regulatory and purposive systems Crime and security * Cyber crime, crime that involves computers and networks ** Convention on Cybercrime, the first international treaty seeking to address Internet and computer crime, signed in 2001 ** Cybercrime countermeasures * Cyber-attack, an offensive manoeuvre that targets computing devices, information systems, infrastructures and Cyberinfrastructures, or networks * Cybersecurity, or computer security * Cybersex trafficking, the live streaming of coerced sexual acts and or rape * Cyberterrorism, use of the Internet to carry out terrorism * Cyberwarfare, the targeting of computers and networks in war Other uses in computing and the Internet * CDC Cyber, a range of mainframe computers * Cyberbullying, bullying or harassment using electronic means * Cybercafé or Internet café, a business which provides internet acce ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |

.jpg)




