|
KnujOn
KnujOn ("no junk" spelled backwards, and pronounced "new john") was a project involved in Internet security. KnujOn targeted spam at its root, attacking the illicit activities that spammers derive their revenue from. To that end, KnujOn ran an automated spam reporting tool. History KnujOn was founded in 2005 by Garth Bruen and his father Dr. Robert Bruen. A multi-purpose software tool called KnujOn was presented at The Northeast Chapter of the High Technology Crime Investigation Association (HTCIA) in November 2005. That software, designed to filter junk mail and produce complaints that may result in shutdowns of scam websites, tracked Internet-based scams and built profiles of persons or organizations engaged in suspicious Internet activity by gathering and sorting large amounts of data. KnujOn.com collected spam samples from the public, not to build better filters or blacklists, but rather to use them for illicit site termination, to test the Internet's policy infrastructur ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Blue Frog
Blue Frog was a freely-licensed anti-spam tool produced by Blue Security Inc. and operated as part of a community-based system which tried to persuade spammers to remove community members' addresses from their mailing lists by automating the complaint process for each user as spam is received. Blue Security maintained these addresses in a hashed form in a ''Do Not Intrude Registry'', and spammers could use free tools to clean their lists. The tool was discontinued in . Information Community members reported their spam to Blue Security, which analyzed it to make sure it met their guidelines, then reported sites sending illegal spam to the ISPs which hosted them (if they could be contacted and were willing to work with them), to other anti-spam groups and to law-enforcement authorities in an attempt to get the spammer to cease and desist. If these measures failed, Blue Security sent back a set of instructions to a Blue Frog client. The client software used these instructions to vi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Security
Internet security is a branch of computer security. It encompasses the Internet, browser security, web site security, and network security as it applies to other applications or operating systems as a whole. Its objective is to establish rules and measures to use against attacks over the Internet. The Internet is an inherently insecure channel for information exchange, with high risk of intrusion or fraud, such as phishing, online viruses, trojans, ransomware and worms. Many methods are used to combat these threats, including encryption and ground-up engineering. Threats Malicious software Malicious software comes in many forms, such as viruses, Trojan horses, spyware, and worms. * Malware, a portmanteau of malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include softw ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
E-mail Spam
Email spam, also referred to as junk email, spam mail, or simply spam, is unsolicited messages sent in bulk by email (spamming). The name comes from a Monty Python sketch in which the name of the canned pork product Spam is ubiquitous, unavoidable, and repetitive. Email spam has steadily grown since the early 1990s, and by 2014 was estimated to account for around 90% of total email traffic. Since the expense of the spam is borne mostly by the recipient, it is effectively postage due advertising. This makes it an excellent example of a negative externality. The legal definition and status of spam varies from one jurisdiction to another, but nowhere have laws and lawsuits been particularly successful in stemming spam. Most email spam messages are commercial in nature. Whether commercial or not, many are not only annoying as a form of attention theft, but also dangerous because they may contain links that lead to phishing web sites or sites that are hosting malware or include ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Spammer
Spamming is the use of messaging systems to send multiple unsolicited messages (spam) to large numbers of recipients for the purpose of commercial advertising, for the purpose of non-commercial proselytizing, for any prohibited purpose (especially the fraudulent purpose of phishing), or simply repeatedly sending the same message to the same user. While the most widely recognized form of spam is email spam, the term is applied to similar abuses in other media: instant messaging spam, Usenet newsgroup spam, Web search engine spam, spam in blogs, wiki spam, online classified ads spam, mobile phone messaging spam, Internet forum spam, junk fax transmissions, social spam, spam mobile apps, television advertising and file sharing spam. It is named after Spam, a luncheon meat, by way of a Monty Python sketch about a restaurant that has Spam in almost every dish in which Vikings annoyingly sing "Spam" repeatedly. Spamming remains economically viable because advertisers have no ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
High Technology Crime Investigation Association
High Technology Crime Investigation Association (HTCIA) is an international non-profit professional organization devoted to the prevention, investigation, and prosecution of crimes involving advanced technologies. Author and cybercrime expert, Christopher Brown, described HTCIA as "one of the largest and most respected" associations of its kind. The association was formally incorporated in 1989 and "designed to encourage, promote, aid and effect the voluntary interchange of data, information, experience, ideas and knowledge about methods, processes, and techniques relating to investigations and security in advanced technologies." The association is open to law enforcement personnel, investigators, technicians or specialists and prosecuting attorneys engaged in the investigation and prosecution of criminal or civic activities in which computers and or other advanced technologies are utilized. The association is also open to security professionals whose primary duties are corporate s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Software
Software is a set of computer programs and associated documentation and data. This is in contrast to hardware, from which the system is built and which actually performs the work. At the lowest programming level, executable code consists of machine language instructions supported by an individual processor—typically a central processing unit (CPU) or a graphics processing unit (GPU). Machine language consists of groups of binary values signifying processor instructions that change the state of the computer from its preceding state. For example, an instruction may change the value stored in a particular storage location in the computer—an effect that is not directly observable to the user. An instruction may also invoke one of many input or output operations, for example displaying some text on a computer screen; causing state changes which should be visible to the user. The processor executes the instructions in the order they are provided, unless it is instructed ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Spam
Email spam, also referred to as junk email, spam mail, or simply spam, is unsolicited messages sent in bulk by email (spamming). The name comes from a Monty Python sketch in which the name of the canned pork product Spam is ubiquitous, unavoidable, and repetitive. Email spam has steadily grown since the early 1990s, and by 2014 was estimated to account for around 90% of total email traffic. Since the expense of the spam is borne mostly by the recipient, it is effectively postage due advertising. This makes it an excellent example of a negative externality. The legal definition and status of spam varies from one jurisdiction to another, but nowhere have laws and lawsuits been particularly successful in stemming spam. Most email spam messages are commercial in nature. Whether commercial or not, many are not only annoying as a form of attention theft, but also dangerous because they may contain links that lead to phishing web sites or sites that are hosting malware or includ ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Scams
A confidence trick is an attempt to defraud a person or group after first gaining their trust. Confidence tricks exploit victims using their credulity, naïveté, compassion, vanity, confidence, irresponsibility, and greed. Researchers have defined confidence tricks as "a distinctive species of fraudulent conduct ..intending to further voluntary exchanges that are not mutually beneficial", as they "benefit con operators ('con men') at the expense of their victims (the 'marks')". Terminology Synonyms include con, confidence game, confidence scheme, ripoff, scam, and stratagem. The perpetrator of a confidence trick (or "con trick") is often referred to as a confidence (or "con") man, con-artist, or a "grifter". The shell game dates back at least to Ancient Greece. Samuel Thompson (1821–1856) was the original "confidence man". Thompson was a clumsy swindler who asked his victims to express confidence in him by giving him money or their watch rather than gaining their confidenc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
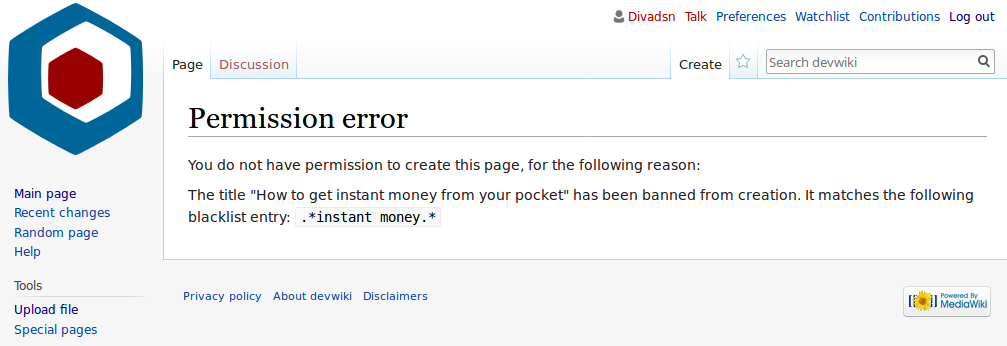
Blacklist (computing)
In computing, a blacklist, disallowlist, blocklist, or denylist is a basic access control mechanism that allows through all elements (email addresses, users, passwords, URLs, IP addresses, domain names, file hashes, etc.), except those explicitly mentioned. Those items on the list are denied access. The opposite is a whitelist, allowlist, or passlist, in which only items on the list are let through whatever gate is being used. A greylist contains items that are temporarily blocked (or temporarily allowed) until an additional step is performed. Blacklists can be applied at various points in a security architecture, such as a host, web proxy, DNS servers, email server, firewall, directory servers or application authentication gateways. The type of element blocked is influenced by the access control location. DNS servers may be well-suited to block domain names, for example, but not URLs. A firewall is well-suited for blocking IP addresses, but less so for blocking malicious fil ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Statistics
Statistics (from German language, German: ''wikt:Statistik#German, Statistik'', "description of a State (polity), state, a country") is the discipline that concerns the collection, organization, analysis, interpretation, and presentation of data. In applying statistics to a scientific, industrial, or social problem, it is conventional to begin with a statistical population or a statistical model to be studied. Populations can be diverse groups of people or objects such as "all people living in a country" or "every atom composing a crystal". Statistics deals with every aspect of data, including the planning of data collection in terms of the design of statistical survey, surveys and experimental design, experiments.Dodge, Y. (2006) ''The Oxford Dictionary of Statistical Terms'', Oxford University Press. When census data cannot be collected, statisticians collect data by developing specific experiment designs and survey sample (statistics), samples. Representative sampling as ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
.jpg)