|
JSON Web Encryption
JSON Web Encryption (JWE) is an IETF standard providing a standardised syntax for the exchange of encrypted data, based on JSON and Base64. It is defined by . Along with JSON Web Signature (JWS), it is one of the two possible formats of a JWT (JSON Web Token JSON Web Token (JWT, suggested pronunciation , same as the word "jot") is a Internet Standard#Proposed Standard, proposed Internet standard for creating data with optional Signature (cryptography), signature and/or optional encryption whose Payl ...). JWE forms part of the JavaScript Object Signing and Encryption (JOSE) suite of protocols. Vulnerabilities In March 2017, a serious flaw was discovered in many popular implementations of JWE, the invalid curve attack. One implementation of an early (pre-finalised) version of JWE also suffered from Bleichenbacher’s attack. References {{Data exchange JSON Internet Standards Cryptographic protocols ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Encryption
In Cryptography law, cryptography, encryption (more specifically, Code, encoding) is the process of transforming information in a way that, ideally, only authorized parties can decode. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Despite its goal, encryption does not itself prevent interference but denies the intelligible content to a would-be interceptor. For technical reasons, an encryption scheme usually uses a pseudo-random encryption Key (cryptography), key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users. Historically, various forms of encryption have been used to aid in cryptography. Early encryption ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an Logical assertion, assertion, such as the Digital identity, identity of a computer system user. In contrast with identification, the act of indicating a person or thing's identity, authentication is the process of verifying that identity. Authentication is relevant to multiple fields. In art, antiques, and anthropology, a common problem is verifying that a given artifact was produced by a certain person, or in a certain place (i.e. to assert that it is not counterfeit), or in a given period of history (e.g. by determining the age via carbon dating). In computer science, verifying a user's identity is often required to allow access to confidential data or systems. It might involve validating personal identity documents. In art, antiques and anthropology Authentication can be considered to be of three types: The ''first'' type of authentication is accep ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IETF
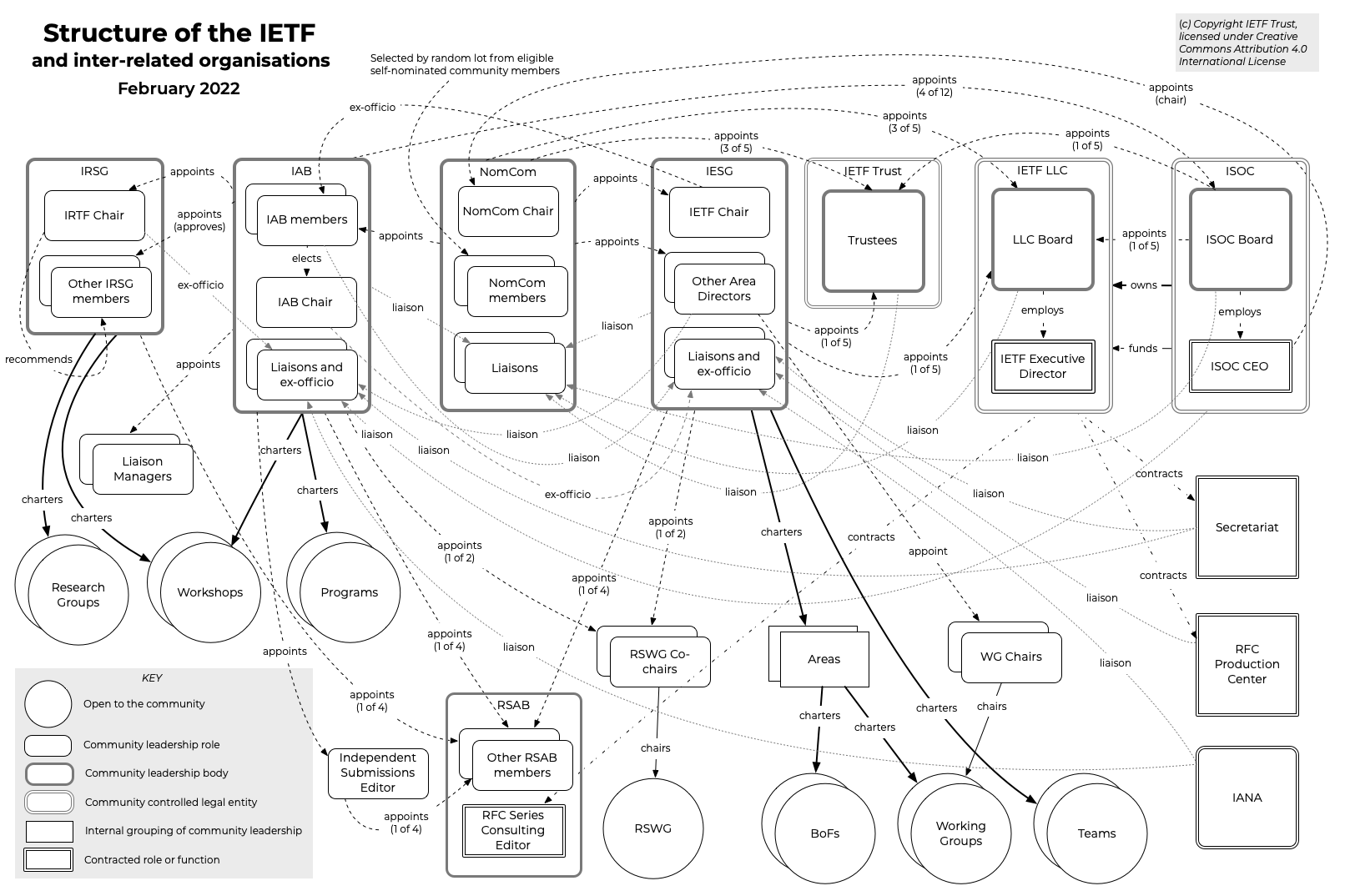
The Internet Engineering Task Force (IETF) is a standards organization for the Internet standard, Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and all its participants are volunteers. Their work is usually funded by employers or other sponsors. The IETF was initially supported by the federal government of the United States but since 1993 has operated under the auspices of the Internet Society, a non-profit organization with local chapters around the world. Organization There is no membership in the IETF. Anyone can participate by signing up to a working group mailing list, or registering for an IETF meeting. The IETF operates in a bottom-up task creation mode, largely driven by working groups. Each working group normally has appointed two co-chairs (occasionally three); a charter that describes its focus; and what it is expected to produce, and when. It is open ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
JSON
JSON (JavaScript Object Notation, pronounced or ) is an open standard file format and electronic data interchange, data interchange format that uses Human-readable medium and data, human-readable text to store and transmit data objects consisting of name–value pairs and array data type, arrays (or other serialization, serializable values). It is a commonly used data format with diverse uses in electronic data interchange, including that of web applications with server (computing), servers. JSON is a Language-independent specification, language-independent data format. It was derived from JavaScript, but many modern programming languages include code to generate and parse JSON-format data. JSON filenames use the extension .json. Douglas Crockford originally specified the JSON format in the early 2000s. Transcript: He and Chip Morningstar sent the first JSON message in April 2001. Naming and pronunciation The 2017 international standard (ECMA-404 and ISO/IEC 21778:2017) ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Base64
In computer programming, Base64 is a group of binary-to-text encoding schemes that transforms binary data into a sequence of printable characters, limited to a set of 64 unique characters. More specifically, the source binary data is taken 6 bits at a time, then this group of 6 bits is mapped to one of 64 unique characters. As with all binary-to-text encoding schemes, Base64 is designed to carry data stored in binary formats across channels that only reliably support text content. Base64 is particularly prevalent on the World Wide Web where one of its uses is the ability to embed image files or other binary assets inside textual assets such as HTML and CSS files. Base64 is also widely used for sending e-mail attachments, because SMTP – in its original form – was designed to transport 7-bit ASCII characters only. Encoding an attachment as Base64 before sending, and then decoding when received, assures older SMTP servers will not interfere with the attachment. Ba ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
JSON Web Signature
A JSON Web Signature (abbreviated JWS) is an IETF-proposed standard () for signing arbitrary data. This is used as the basis for a variety of web-based technologies including JSON Web Token. Purpose JWS is a way to ensure integrity of information in a highly serializable, machine-readable format. That means that it is information, along with proof that the information hasn't changed since being signed. It can be used for sending information from one web site to another, and is especially aimed at communications on the web. It even contains a compact form optimized for applications like URI query parameters. Examples Web commerce JWS can be used for applications in which digitally signed information must be sent in a machine-readable format, such as e-commerce. For example, say a user named Bob is browsing widget prices on a web site (widgets.com), and wishes to get a quote on one of them. Then widgets.com could provide Bob with a JWS object containing all relevant in ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
JSON Web Token
JSON Web Token (JWT, suggested pronunciation , same as the word "jot") is a Internet Standard#Proposed Standard, proposed Internet standard for creating data with optional Signature (cryptography), signature and/or optional encryption whose Payload (computing), payload holds JSON that asserts some number of Claims-based identity, claims. The tokens are signed either using a Shared secret, private secret or a Public-key cryptography, public/private key. For example, a server could generate a token that has the claim "logged in as administrator" and provide that to a client. The client could then use that token to prove that it is logged in as admin. The tokens can be signed by one party's private key (usually the server's) so that any party can subsequently verify whether the token is legitimate. If the other party, by some suitable and trustworthy means, is in possession of the corresponding public key, they too are able to verify the token's legitimacy. The Session token, tokens ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
JavaScript Object Signing And Encryption
JavaScript (), often abbreviated as JS, is a programming language and core technology of the World Wide Web, alongside HTML and CSS. Ninety-nine percent of websites use JavaScript on the client side for webpage behavior. Web browsers have a dedicated JavaScript engine that executes the client code. These engines are also utilized in some servers and a variety of apps. The most popular runtime system for non-browser usage is Node.js. JavaScript is a high-level, often just-in-time–compiled language that conforms to the ECMAScript standard. It has dynamic typing, prototype-based object-orientation, and first-class functions. It is multi-paradigm, supporting event-driven, functional, and imperative programming styles. It has application programming interfaces (APIs) for working with text, dates, regular expressions, standard data structures, and the Document Object Model (DOM). The ECMAScript standard does not include any input/output (I/O), such as networking, sto ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Elliptic-curve Cryptography
Elliptic-curve cryptography (ECC) is an approach to public-key cryptography based on the algebraic structure of elliptic curves over finite fields. ECC allows smaller keys to provide equivalent security, compared to cryptosystems based on modular exponentiation in Galois fields, such as the RSA cryptosystem and ElGamal cryptosystem. Elliptic curves are applicable for key agreement, digital signatures, pseudo-random generators and other tasks. Indirectly, they can be used for encryption by combining the key agreement with a symmetric encryption scheme. They are also used in several integer factorization algorithms that have applications in cryptography, such as Lenstra elliptic-curve factorization. History The use of elliptic curves in cryptography was suggested independently by Neal Koblitz and Victor S. Miller in 1985. Elliptic curve cryptography algorithms entered wide use in 2004 to 2005. In 1999, NIST recommended fifteen elliptic curves. Specifically, FIPS 186 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bleichenbacher’s Attack
An adaptive chosen-ciphertext attack (abbreviated as CCA2) is an interactive form of chosen-ciphertext attack in which an attacker first sends a number of ciphertexts to be decrypted chosen adaptively, and then uses the results to distinguish a target ciphertext without consulting the oracle on the challenge ciphertext. In an adaptive attack, the attacker is further allowed adaptive queries to be asked after the target is revealed (but the target query is disallowed). It is extending the indifferent (non-adaptive) chosen-ciphertext attack (CCA1) where the second stage of adaptive queries is not allowed. Charles Rackoff and Dan Simon defined CCA2 and suggested a system building on the non-adaptive CCA1 definition and system of Moni Naor and Moti Yung (which was the first treatment of chosen ciphertext attack immunity of public key systems). In certain practical settings, the goal of this attack is to gradually reveal information about an encrypted message, or about the decryption k ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Standards
In computer network engineering, an Internet Standard is a normative specification of a technology or methodology applicable to the Internet. Internet Standards are created and published by the Internet Engineering Task Force (IETF). They allow interoperation of hardware and software from different sources which allows internets to function. As the Internet became global, Internet Standards became the lingua franca of worldwide communications. Engineering contributions to the IETF start as an Internet Draft, may be promoted to a Request for Comments, and may eventually become an Internet Standard. An Internet Standard is characterized by technical maturity and usefulness. The IETF also defines a Proposed Standard as a less mature but stable and well-reviewed specification. A Draft Standard was an intermediate level, discontinued in 2011. A Draft Standard was an intermediary step that occurred after a Proposed Standard but prior to an Internet Standard. As put in RFC 2026: In ge ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |