|
Hummingbad
HummingBad is Android malware, discovered by Check Point in February 2016. In July 2016, researchers from security firm Check Point Software said the malware installs more than 50,000 fraudulent apps each day, displays 20 million malicious advertisements, and generates more than $300,000 per month in revenue. The research pointed out the Yingmob group, previously accused of being responsible for the Yispecter iOS malware, as responsible for the attack. Lookout claimed the HummingBad malware was also a part of the Shedun Shedun is a family of malware software (also known as Kemoge, Shiftybug and Shuanet) targeting the Android operating system first identified in late 2015 by mobile security company Lookout, affecting roughly 20,000 popular Android applications. Lo ... family, however, these claims were refuted. The most infected region was Asia which included China, India, Philippines, Indonesia and Turkey as the top countries. See also References {{reflist Spyware Cyberc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Linux Malware
Linux malware includes viruses, Trojans, worms and other types of malware that affect the Linux family of operating systems. Linux, Unix and other Unix-like computer operating systems are generally regarded as very well-protected against, but not immune to, computer viruses. Linux vulnerability Like Unix systems, Linux implements a multi-user environment where users are granted specific privileges and there is some form of access control implemented. To gain control over a Linux system or to cause any serious consequences to the system itself, the malware would have to gain root access to the system. In the past, it has been suggested that Linux had so little malware because its low market share made it a less profitable target. Rick Moen, an experienced Linux system administrator, counters that: In 2008 the quantity of malware targeting Linux was noted as increasing. Shane Coursen, a senior technical consultant with Kaspersky Lab, said at the time, "The growth in Linux malwa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Shedun
Shedun is a family of malware software (also known as Kemoge, Shiftybug and Shuanet) targeting the Android operating system first identified in late 2015 by mobile security company Lookout, affecting roughly 20,000 popular Android applications. Lookout claimed the HummingBad malware was also a part of the Shedun family, however, these claims were refuted. Avira Protection Labs stated that Shedun family malware is detected to cause approximately 1500-2000 infections per day. All three variants of the virus are known to share roughly ~80% of the same source code. In mid 2016, arstechnica reported that approximately 10.000.000 devices would be infected by this malware and that new infections would still be surging. The malware's primary attack vector is repackaging legitimate Android applications (e.g. Facebook, Twitter, WhatsApp, Candy Crush, Google Now, Snapchat) with adware included. The app which remains functional is then released to a third party app store; once downloaded, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Individual Mobility
Individual human mobility is the study that describes how individual humans move within a network or system. The concept has been studied in a number of fields originating in the study of demographics. Understanding human mobility has many applications in diverse areas, including spread of diseases, mobile viruses, city planning, traffic engineering, financial market forecasting, and nowcasting of economic well-being. Data In recent years, there has been a surge in large data sets available on human movements. These data sets are usually obtained from cell phone or GPS data, with varying degrees of accuracy. For example, cell phone data is usually recorded whenever a call or a text message has been made or received by the user, and contains the location of the tower that the phone has connected to as well as the time stamp. In urban areas, user and the telecommunication tower might be only a few hundred meters away from each other, while in rural areas this distance might ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Zombie (computer Science)
In computing, a zombie is a computer connected to the Internet that has been compromised by a hacker via a computer virus, computer worm, or trojan horse program and can be used to perform malicious tasks under the remote direction of the hacker. Zombie computers often coordinate together in a botnet controlled by the hacker, and are used for activities such as spreading e-mail spam and launching distributed denial-of-service attacks (DDoS attacks) against web servers. Most victims are unaware that their computers have become zombies. The concept is similar to the zombie of Haitian Voodoo folklore, which refers to a corpse resurrected by a sorcerer via magic and enslaved to the sorcerer's commands, having no free will of its own. A coordinated DDoS attack by multiple botnet machines also resembles a "zombie horde attack", as depicted in fictional zombie films. Advertising Zombie computers have been used extensively to send e-mail spam; as of 2005, an estimated 50–80 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Worm (computing)
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers. It often uses a computer network to spread itself, relying on security failures on the target computer to access it. It will use this machine as a host to scan and infect other computers. When these new worm-invaded computers are controlled, the worm will continue to scan and infect other computers using these computers as hosts, and this behaviour will continue. Computer worms use recursive methods to copy themselves without host programs and distribute themselves based on the law of exponential growth, thus controlling and infecting more and more computers in a short time. Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer. Many worms are designed only to spread, and do not attempt to change the systems they pass through. However, as th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Trojan Horse (computing)
In computing, a Trojan horse is any malware that misleads users of its true intent. The term is derived from the Ancient Greek story of the deceptive Trojan Horse that led to the fall of the city of Troy. Trojans generally spread by some form of social engineering; for example, where a user is duped into executing an email attachment disguised to appear innocuous (e.g., a routine form to be filled in), or by clicking on some fake advertisement on social media or anywhere else. Although their payload can be anything, many modern forms act as a backdoor, contacting a controller who can then have unauthorized access to the affected computer. Ransomware attacks are often carried out using a Trojan. Unlike computer viruses and worms, Trojans generally do not attempt to inject themselves into other files or otherwise propagate themselves. Use of the term It's not clear where or when the concept, and this term for it, was first used, but by 1971 the first Unix manual assumed its r ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mobile Operating System
A mobile operating system is an operating system for mobile phones, tablets, smartwatches, smartglasses, or other non-laptop personal mobile computing devices. While computers such as typical laptops are "mobile", the operating systems used on them are generally not considered mobile ones, as they were originally designed for desktop computers that historically did not have or need specific ''mobile'' features. This line distinguishing mobile and other forms has become blurred in recent years, due to the fact that newer devices have become smaller and more mobile unlike hardware of the past. Key notabilities blurring this line are the introduction of tablet computers and light-weight laptops and the hybridization of the two in 2-in-1 PCs. Mobile operating systems combine features of a desktop computer operating system with other features useful for mobile or handheld use, and usually including a wireless inbuilt modem and SIM tray for telephony and data connection. In Q1 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan horses, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dendroid (Malware)
Dendroid is malware that affects Android OS and targets the mobile platform. It was first discovered in early of 2014 by Symantec and appeared in the underground for sale for $300. Certain features were noted as being used in Dendroid, such as the ability to hide from emulators at the time. When first discovered in 2014 it was one of the most sophisticated Android remote administration tools known at that time. It was one of the first Trojan applications to get past Google's Bouncer and caused researchers to warn about it being easier to create Android malware due to it. It also seems to have followed in the footsteps of Zeus and SpyEye by having simple-to-use command and control panels. The code appeared to be leaked somewhere around 2014. It was noted that an apk binder was included in the leak, which provided a simple way to bind Dendroid to legitimate applications. It is capable of: * Deleting call logs * Opening web pages * Dialing any number * Recording calls * SMS inte ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
File Binder
File binders are utility software that allow a user to "bind" multiple files together resulting in a single executable. They are commonly used by hackers to insert other programs such as Trojan horses into otherwise harmless files, making them more difficult to detect. Malware builders (such as keyloggers or stealers) often include a binder by default. A polymorphic packer is a file binder with a polymorphic engine. It thus has the ability to make its payload mutate over time, so it is more difficult to detect and remove. See also *Dendroid (malware) * MiniPanzer and MegaPanzer – Trojan horses that used file binders for distribution *Potentially unwanted program A potentially unwanted program (PUP) or potentially unwanted application (PUA) is software that a user may perceive as unwanted or unnecessary. It is used as a subjective tagging criterion by security and parental control products. Such software ma ... – sometimes have used file binders for distribution References ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Check Point
Check Point is an American-Israeli multinational provider of software and combined hardware and software products for IT security, including network security, endpoint security, cloud security, mobile security, data security and security management. , the company has approximately 6,000 employees worldwide. Headquartered in Tel Aviv, Israel and San Carlos, California, the company has development centers in Israel and Belarus and previously held in United States (ZoneAlarm), Sweden (former Protect Data development centre) following acquisitions of companies who owned these centers. The company has offices in over 70 locations worldwide including main offices in North America, 10 in the United States (including in San Carlos, California and Dallas, Texas), 4 in Canada (including Ottawa, Ontario) as well as in Europe (London, Paris, Munich, Madrid) and in Asia Pacific (Singapore, Japan, Bengaluru, Sydney) . History Check Point was established in Ramat Gan, Israel in 1993, by Gil Sh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Virus
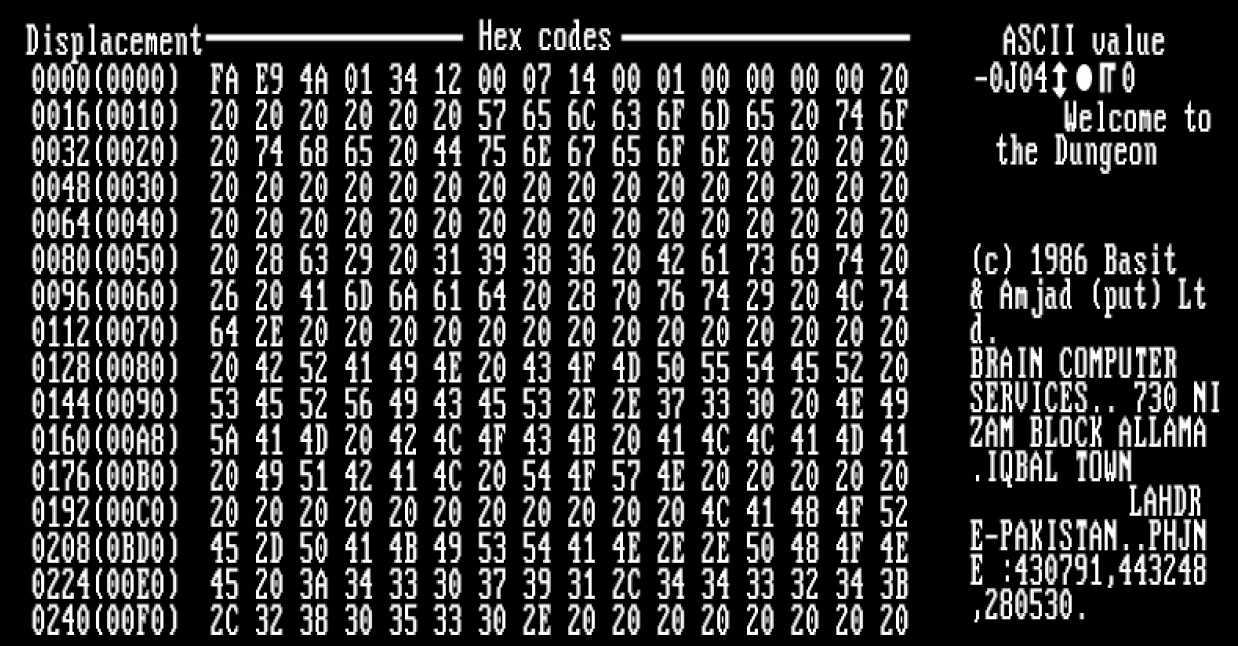
A computer virus is a type of computer program that, when executed, replicates itself by modifying other computer programs and inserting its own code. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses. Computer viruses generally require a host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. A computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the host program, but can run independently and actively carry out attacks. Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. Viruses use complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can inclu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |