|
Hash Filter
A hash filter creates a hash sum from data, typically e-mail, and compares the sum against other previously defined sums. Depending on the purpose of the filter, the data can then be included or excluded in a function based on whether it matches an existing sum. For example, when a message is received by an e-mail server with a hash filter, the contents of the e-mail is converted into a hash sum. If this sum corresponds to the hash sum of another e-mail which has been categorized as spam, the received e-mail is prevented from being delivered. Spammers attempt to evade this by adding random strings to the text content and random pixel changes ("confetti") to image content (see image spam). See also * Bloom filter * Hash buster * Locality-sensitive hashing In computer science, locality-sensitive hashing (LSH) is an algorithmic technique that hashes similar input items into the same "buckets" with high probability. (The number of buckets is much smaller than the universe of possibl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hash Sum
A hash function is any function that can be used to map data of arbitrary size to fixed-size values. The values returned by a hash function are called ''hash values'', ''hash codes'', ''digests'', or simply ''hashes''. The values are usually used to index a fixed-size table called a ''hash table''. Use of a hash function to index a hash table is called ''hashing'' or ''scatter storage addressing''. Hash functions and their associated hash tables are used in data storage and retrieval applications to access data in a small and nearly constant time per retrieval. They require an amount of storage space only fractionally greater than the total space required for the data or records themselves. Hashing is a computationally and storage space-efficient form of data access that avoids the non-constant access time of ordered and unordered lists and structured trees, and the often exponential storage requirements of direct access of state spaces of large or variable-length keys. Use o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
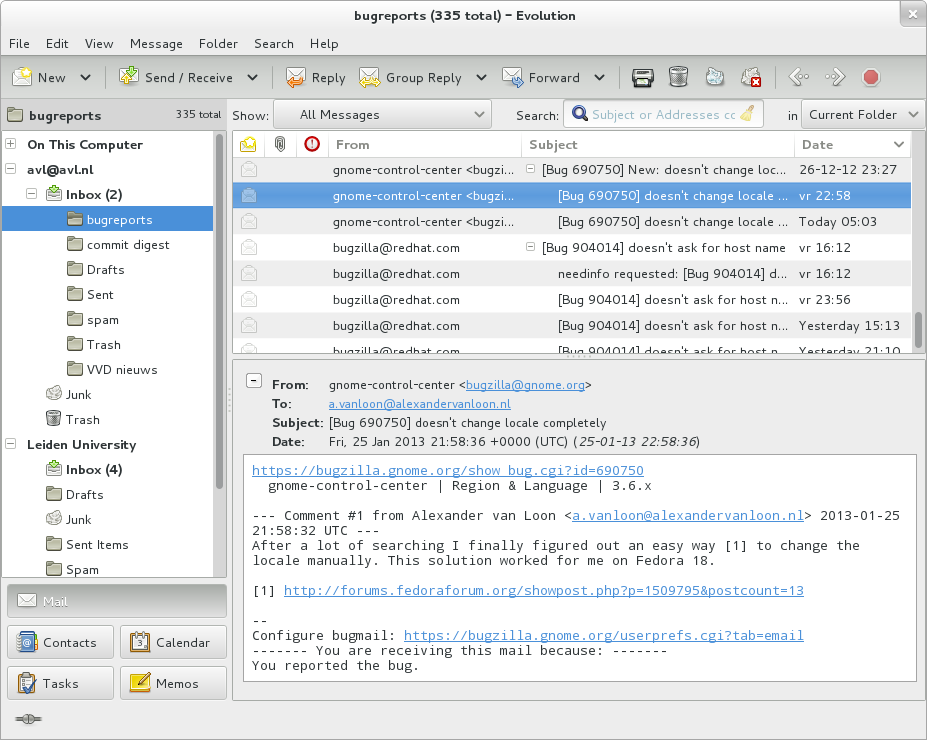
E-mail
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Function (computer Science)
In computer programming, a function or subroutine is a sequence of program instructions that performs a specific task, packaged as a unit. This unit can then be used in programs wherever that particular task should be performed. Functions may be defined within programs, or separately in libraries that can be used by many programs. In different programming languages, a function may be called a routine, subprogram, subroutine, method, or procedure. Technically, these terms all have different definitions, and the nomenclature varies from language to language. The generic umbrella term ''callable unit'' is sometimes used. A function is often coded so that it can be started several times and from several places during one execution of the program, including from other functions, and then branch back (''return'') to the next instruction after the ''call'', once the function's task is done. The idea of a subroutine was initially conceived by John Mauchly during his work on ENIAC, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
E-mail Spam
Email spam, also referred to as junk email, spam mail, or simply spam, is unsolicited messages sent in bulk by email (spamming). The name comes from a Monty Python sketch in which the name of the canned pork product Spam is ubiquitous, unavoidable, and repetitive. Email spam has steadily grown since the early 1990s, and by 2014 was estimated to account for around 90% of total email traffic. Since the expense of the spam is borne mostly by the recipient, it is effectively postage due advertising. This makes it an excellent example of a negative externality. The legal definition and status of spam varies from one jurisdiction to another, but nowhere have laws and lawsuits been particularly successful in stemming spam. Most email spam messages are commercial in nature. Whether commercial or not, many are not only annoying as a form of attention theft, but also dangerous because they may contain links that lead to phishing web sites or sites that are hosting malware or includ ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Image Spam
Image-based spam,Giorgio Fumera, Ignazio Pillai, Fabio Roli, Journal of Machine Learning Research (special issue on Machine Learning in Computer Security), vol. 7, pp. 2699-2720, 12/2006.Battista Biggio, Giorgio Fumera, Ignazio Pillai, Fabio Roli, Volume 32, Issue 10, 15 July 2011, Pages 1436-1446, ISSN 0167-8655. or image spam, is a kind of email spam where the textual spam message is embedded into images, that are then attached to spam emails. Since most of the email clients will display the image file directly to the user, the spam message is conveyed as soon as the email is opened (there is no need to further open the attached image file). Technique The goal of image spam is clearly to circumvent the analysis of the email’s textual content performed by most spam filters (e.g., SpamAssassin, RadicalSpam, Bogofilter, SpamBayes). Accordingly, for the same reason, together with the attached image, often spammers add some “bogus” text to the email, namely, a number of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bloom Filter
A Bloom filter is a space-efficient probabilistic data structure, conceived by Burton Howard Bloom in 1970, that is used to test whether an element is a member of a set. False positive matches are possible, but false negatives are not – in other words, a query returns either "possibly in set" or "definitely not in set". Elements can be added to the set, but not removed (though this can be addressed with the counting Bloom filter variant); the more items added, the larger the probability of false positives. Bloom proposed the technique for applications where the amount of source data would require an impractically large amount of memory if "conventional" error-free hashing techniques were applied. He gave the example of a hyphenation algorithm for a dictionary of 500,000 words, out of which 90% follow simple hyphenation rules, but the remaining 10% require expensive disk accesses to retrieve specific hyphenation patterns. With sufficient core memory, an error-free hash co ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hash Buster
A hash buster is a program which randomly adds characters to data in order to change the data's hash sum. This is typically used to add words to spam e-mails, to bypass hash filters. As the e-mail's hash sum is different from the sum of e-mails previously defined as spam, the e-mail is not considered spam and therefore delivered as if it were a normal message. Hash busters can also be used to randomly add content to any kind of file until the hash sum becomes a certain sum. In e-mail context, this could be used to bypass a filter which only accepts e-mails with a certain sum. Initially spams containing "white noise" from hash busters tended to simply exhibit 'paragraphs' of literally random words, but increasingly these are now appearing somewhat grammatical. See also * Cryptographic hash function * Bayesian poisoning * Locality-sensitive hashing In computer science, locality-sensitive hashing (LSH) is an algorithmic technique that hashes similar input items into the same "bu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Locality-sensitive Hashing
In computer science, locality-sensitive hashing (LSH) is an algorithmic technique that hashes similar input items into the same "buckets" with high probability. (The number of buckets is much smaller than the universe of possible input items.) Since similar items end up in the same buckets, this technique can be used for data clustering and nearest neighbor search. It differs from conventional hashing techniques in that hash collisions are maximized, not minimized. Alternatively, the technique can be seen as a way to reduce the dimensionality of high-dimensional data; high-dimensional input items can be reduced to low-dimensional versions while preserving relative distances between items. Hashing-based approximate nearest neighbor search algorithms generally use one of two main categories of hashing methods: either data-independent methods, such as locality-sensitive hashing (LSH); or data-dependent methods, such as locality-preserving hashing (LPH). Definitions An ''LSH family'' ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |