|
Ghash
In cryptography, Galois/Counter Mode (GCM) is a mode of operation for symmetric-key cryptographic block ciphers which is widely adopted for its performance. GCM throughput rates for state-of-the-art, high-speed communication channels can be achieved with inexpensive hardware resources. The operation is an authenticated encryption algorithm designed to provide both data authenticity (integrity) and confidentiality. GCM is defined for block ciphers with a block size of 128 bits. Galois Message Authentication Code (GMAC) is an authentication-only variant of the GCM which can form an incremental message authentication code. Both GCM and GMAC can accept initialization vectors of arbitrary length. Different block cipher modes of operation can have significantly different performance and efficiency characteristics, even when used with the same block cipher. GCM can take full advantage of parallel processing and implementing GCM can make efficient use of an instruction pipeline or a hard ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security ( data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
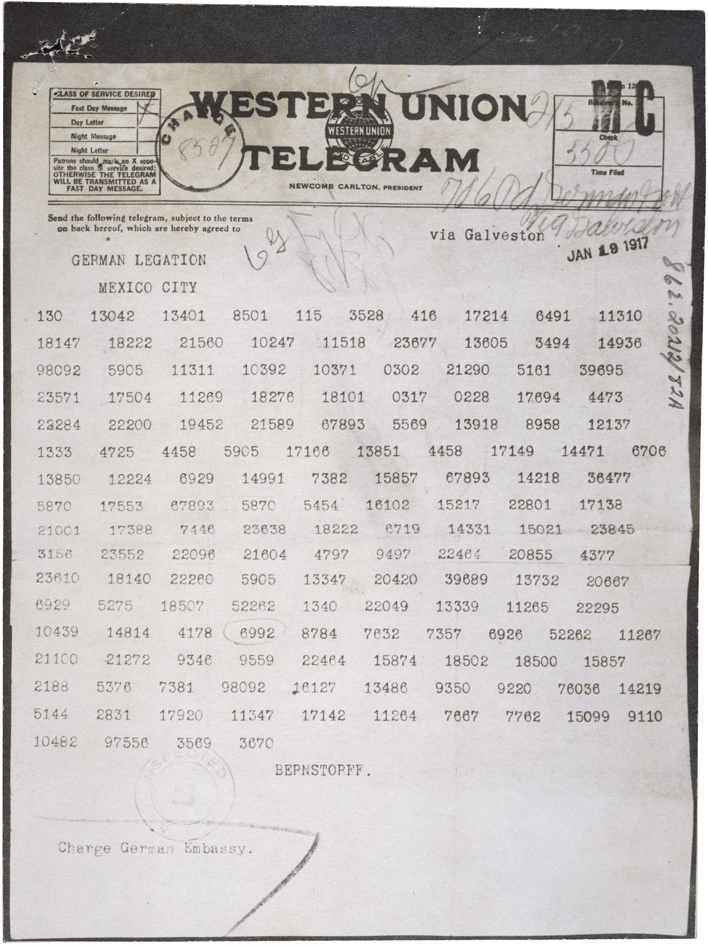
Ciphertext
In cryptography, ciphertext or cyphertext is the result of encryption performed on plaintext using an algorithm, called a cipher. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext that is unreadable by a human or computer without the proper cipher to decrypt it. This process prevents the loss of sensitive information via hacking. Decryption, the inverse of encryption, is the process of turning ciphertext into readable plaintext. Ciphertext is not to be confused with codetext because the latter is a result of a code, not a cipher. Conceptual underpinnings Let m\! be the plaintext message that Alice wants to secretly transmit to Bob and let E_k\! be the encryption cipher, where _k\! is a cryptographic key. Alice must first transform the plaintext into ciphertext, c\!, in order to securely send the message to Bob, as follows: : c = E_k(m). \! In a symmetric-key system, Bob knows Alice's encryption key. Once the m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
INCITS
The InterNational Committee for Information Technology Standards (INCITS), (pronounced "insights"), is an ANSI-accredited standards development organization composed of Information technology developers. It was formerly known as the X3 and NCITS. INCITS is the central U.S. forum dedicated to creating technology standards. INCITS is accredited by the American National Standards Institute (ANSI) and is affiliated with the Information Technology Industry Council, a global policy advocacy organization that represents U.S. and global innovation companies. INCITS coordinates technical standards activity between ANSI in the US and joint ISO/IEC committees worldwide. This provides a mechanism to create standards that will be implemented in many nations. As such, INCITS' Executive Board also serves as ANSI's Technical Advisory Group for ISO/IEC Joint Technical Committee 1. JTC 1 is responsible for International standardization in the field of information technology. INCITS operates thro ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
WiGig
WiGig, alternatively known as 60 GHz Wi-Fi, refers to a set of 60 GHz wireless network protocols. It includes the current IEEE 802.11ad standard and also the IEEE 802.11ay standard. The WiGig specification allows devices to communicate without wires at multi-gigabit speeds. It enables high performance wireless data, display and audio applications that supplement the capabilities of previous wireless LAN devices. WiGig tri-band-enabled devices, which operate in the 2.4, 5 and 60 GHz bands, deliver data transfer rates up to 7 Gbit/s (for 11ad), about as fast as an 8-band 802.11ac transmission, and more than eleven times as fast than the highest 802.11n rate, while maintaining compatibility with existing Wi-Fi devices. The 60 GHz millimeter wave signal cannot typically penetrate walls but can propagate by reflection from walls, ceilings, floors and objects using beamforming built into the WiGig system. When roaming away from the main room, the protocol can switch to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IEEE 802
IEEE 802 is a family of Institute of Electrical and Electronics Engineers (IEEE) standards for local area networks (LAN), personal area network (PAN), and metropolitan area networks (MAN). The IEEE 802 LAN/MAN Standards Committee (LMSC) maintains these standards. The IEEE 802 family of standards has had twenty-four members, numbered 802.1 through 802.24, with a working group of the LMSC devoted to each. However, not all of these working groups are currently active. The IEEE 802 standards are restricted to computer networks carrying variable-size packets, unlike cell relay networks, for example, in which data is transmitted in short, uniformly sized units called cells. Isochronous signal networks, in which data is transmitted as a steady stream of octets, or groups of octets, at regular time intervals, are also outside the scope of the IEEE 802 standards. The number 802 has no significance: it was simply the next number in the sequence that the IEEE used for standards projects. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
NIST
The National Institute of Standards and Technology (NIST) is an agency of the United States Department of Commerce whose mission is to promote American innovation and industrial competitiveness. NIST's activities are organized into physical science laboratory programs that include nanoscale science and technology, engineering, information technology, neutron research, material measurement, and physical measurement. From 1901 to 1988, the agency was named the National Bureau of Standards. History Background The Articles of Confederation, ratified by the colonies in 1781, provided: The United States in Congress assembled shall also have the sole and exclusive right and power of regulating the alloy and value of coin struck by their own authority, or by that of the respective states—fixing the standards of weights and measures throughout the United States. Article 1, section 8, of the Constitution of the United States, ratified in 1789, granted these powers to the new Congre ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
CWC Mode
In cryptography, CWC Mode (Carter–Wegman + CTR mode) is an AEAD block cipher mode of operation that provides both encryption and built-in message integrity, similar to CCM and OCB modes. It combines the use of CTR mode for encryption with an efficient polynomial Carter–Wegman MAC and is designed by Tadayoshi Kohno, John Viega and Doug Whiting. CWC mode was submitted to NIST for standardization, but NIST opted for the similar GCM mode In cryptography, Galois/Counter Mode (GCM) is a mode of operation for symmetric-key cryptographic block ciphers which is widely adopted for its performance. GCM throughput rates for state-of-the-art, high-speed communication channels can be achiev ... instead. Although GCM has weaknesses compared to CWC, the GCM authors successfully argued for GCM.https://csrc.nist.gov/CSRC/media/Projects/Block-Cipher-Techniques/documents/BCM/Comments/CWC-GCM/gcm-update.pdf References External links CWC mode home pageCWC: A high-performance conventiona ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
John Viega
John Viega (born February 22, 1974) is an American computer security author, researcher and professional. Early life He earned his BA from the University of Virginia. As an undergraduate, he worked in Randy Pausch's Stage 3 Research Group, as an early contributor to Alice. Viega earned an MS in Computer Science, also from the University of Virginia. Career John Viega co-authored the widely used GCM mode of operation for AES, along with David A. McGrew. He also co-designed its predecessor, CWC mode John Viega was also a pioneer in static analysis for security vulnerabilities. He was responsible for the first publicly available tool, ITS4., as well as the prominent open source Rough Auditing Tool for Security (RATS). He also founded Secure Software, the first commercial vendor for such tools, which was bought by Fortify Software. John Viega was also the original author of OWASP's CLASP, a lightweight process for relating software development to security. He is also a for ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Horner's Method
In mathematics and computer science, Horner's method (or Horner's scheme) is an algorithm for polynomial evaluation. Although named after William George Horner, this method is much older, as it has been attributed to Joseph-Louis Lagrange by Horner himself, and can be traced back many hundreds of years to Chinese and Persian mathematicians. After the introduction of computers, this algorithm became fundamental for computing efficiently with polynomials. The algorithm is based on Horner's rule: :\begin a_0 &+ a_1x + a_2x^2 + a_3x^3 + \cdots + a_nx^n \\ &= a_0 + x \bigg(a_1 + x \Big(a_2 + x \big(a_3 + \cdots + x(a_ + x \, a_n) \cdots \big) \Big) \bigg). \end This allows the evaluation of a polynomial of degree with only n multiplications and n additions. This is optimal, since there are polynomials of degree that cannot be evaluated with fewer arithmetic operations. Alternatively, Horner's method also refers to a method for approximating the roots of polynomials, described by H ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Galois Field
In mathematics, a finite field or Galois field (so-named in honor of Évariste Galois) is a field that contains a finite number of elements. As with any field, a finite field is a set on which the operations of multiplication, addition, subtraction and division are defined and satisfy certain basic rules. The most common examples of finite fields are given by the integers mod when is a prime number. The ''order'' of a finite field is its number of elements, which is either a prime number or a prime power. For every prime number and every positive integer there are fields of order p^k, all of which are isomorphic. Finite fields are fundamental in a number of areas of mathematics and computer science, including number theory, algebraic geometry, Galois theory, finite geometry, cryptography and coding theory. Properties A finite field is a finite set which is a field; this means that multiplication, addition, subtraction and division (excluding division by zero) are def ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Block Cipher Modes Of Operation
In cryptography, a block cipher mode of operation is an algorithm that uses a block cipher to provide information security such as confidentiality or authenticity. A block cipher by itself is only suitable for the secure cryptographic transformation (encryption or decryption) of one fixed-length group of bits called a block. A mode of operation describes how to repeatedly apply a cipher's single-block operation to securely transform amounts of data larger than a block. Most modes require a unique binary sequence, often called an initialization vector (IV), for each encryption operation. The IV has to be non-repeating and, for some modes, random as well. The initialization vector is used to ensure distinct ciphertexts are produced even when the same plaintext is encrypted multiple times independently with the same key. Block ciphers may be capable of operating on more than one block size, but during transformation the block size is always fixed. Block cipher modes operate on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |