|
GTUBE
The GTUBE ("Generic Test for Unsolicited Bulk Email") is a 68-byte test string used to test anti-spam systems, in particular those based on SpamAssassin. In SpamAssassin, it carries an antispam score of 1000 by default, which would be sufficient to trigger any installation. The contents of the string are as follows: XJS*C4JDBQADN1.NSBN3*2IDNEN*GTUBE-STANDARD-ANTI-UBE-TEST-EMAIL*C.34X and should be placed in the message body of an RFC 5322 compliant email message, without any line breaks or whitespace. Checksums for the string (68 bytes, no trailing newline) are as follows: There exist some varieties, notably the NAItube (which will carry a variable weight) and the GTphish (which will trigger specifically as a phishing mail), which are used in the McAfee implementation of SpamAssassin. The GTUBE is expected to be detected as a substring and is not executable at all, unlike the test for computer viruses developed by EICAR EICAR may refer to: * École Internationale de Créa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SpamAssassin
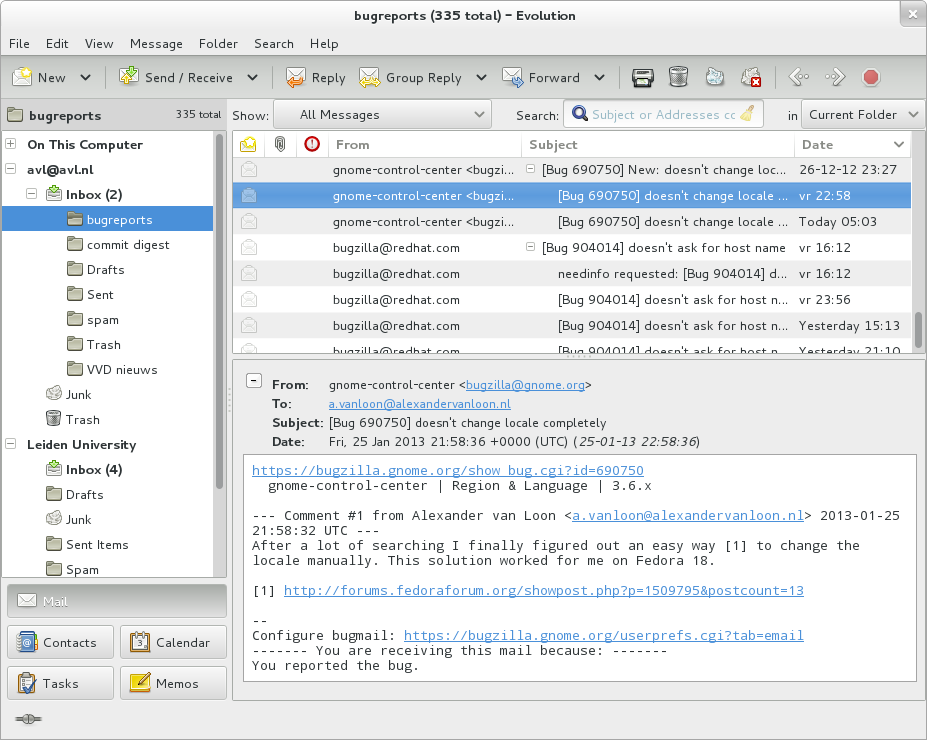
Apache SpamAssassin is a computer program used for anti-spam techniques, e-mail spam filtering. It uses a variety of spam-detection techniques, including Domain Name System, DNS and fuzzy checksum techniques, Bayesian spam filtering, Bayesian filtering, external programs, blacklists and online databases. It is released under the Apache License, Apache License 2.0 and is a part of the Apache Foundation since 2004. The program can be integrated with the Mail transfer agent, mail server to automatically filter all mail for a site. It can also be run by individual users on their own mailbox and integrates with several mail user agent, mail programs. Apache SpamAssassin is highly configurable; if used as a system-wide filter it can still be configured to support per-user preferences. History Apache SpamAssassin was created by Justin Mason, who had maintained a number of patches against an earlier program named ''filter.plx'' by Mark Jeftovic, which in turn was begun in August 1997. Mas ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
E-mail Spam
Email spam, also referred to as junk email, spam mail, or simply spam, is unsolicited messages sent in bulk by email (spamming). The name comes from a Monty Python sketch in which the name of the canned pork product Spam is ubiquitous, unavoidable, and repetitive. Email spam has steadily grown since the early 1990s, and by 2014 was estimated to account for around 90% of total email traffic. Since the expense of the spam is borne mostly by the recipient, it is effectively postage due advertising. This makes it an excellent example of a negative externality. The legal definition and status of spam varies from one jurisdiction to another, but nowhere have laws and lawsuits been particularly successful in stemming spam. Most email spam messages are commercial in nature. Whether commercial or not, many are not only annoying as a form of attention theft, but also dangerous because they may contain links that lead to phishing web sites or sites that are hosting malware or include ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
McAfee
McAfee Corp. ( ), formerly known as McAfee Associates, Inc. from 1987 to 1997 and 2004 to 2014, Network Associates Inc. from 1997 to 2004, and Intel Security Group from 2014 to 2017, is an American global computer security software company headquartered in San Jose, California. The company was purchased by Intel in February 2011, and became part of the Intel Security division. In 2017, Intel had a strategic deal with TPG Capital and converted Intel Security into a joint venture between both companies called McAfee. Thoma Bravo took a minority stake in the new company, and Intel retained a 49% stake. The owners took McAfee public on the NASDAQ in 2020, and in 2022 an investor group led by Advent International Corporation took it private again. History 1987–1999 The company was founded in 1987 as McAfee Associates, named for its founder John McAfee, who resigned from the company in 1994. McAfee was incorporated in the state of Delaware in 1992. In 1993, McAfee stepped do ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious software on the victim's infrastructure like ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim is navigating the site, and transverse any additional security boundaries with the victim. As of 2020, phishing is by far the most common attack performed by cybercriminals, the FBI's Internet Crime Complaint Centre recording over twice as many incidents of phishing than any other type of computer crime. The first recorded use of the term "phishing" was in the cracking toolkit AOHell created by Koceilah Rekouche in 1995; however, it is possible that the term was used before this in a print edition of the hacker magazin ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Virus
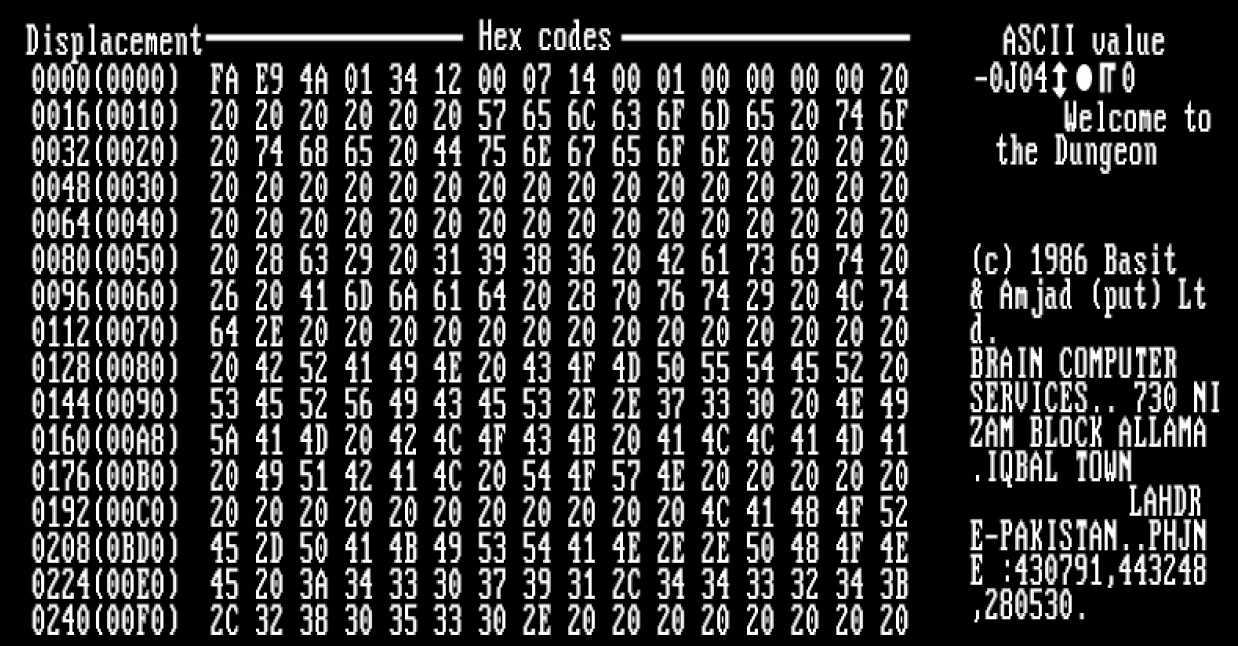
A computer virus is a type of computer program that, when executed, replicates itself by modifying other computer programs and inserting its own code. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses. Computer viruses generally require a host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. A computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the host program, but can run independently and actively carry out attacks. Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. Viruses use complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can inclu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
EICAR (Research Institute)
The European Institute for Computer Antivirus Research (EICAR) was founded in 1991 as an organization aiming to further antivirus research and improving development of antivirus software. Recently EICAR has furthered its scope to include the research of malicious software (malware) other than computer viruses and extended work on other information security topics like content security, Wireless LAN security, RFID and information security awareness. EICAR also organizes international security conferences most years, as well as a number of working groups or 'task forces'. Acronym "EICAR" was originally an abbreviation for ''"European Institute for Computer Antivirus Research"'', but the organisation no longer uses that full title, and now regards "EICAR" as a self-standing name, as it has expanded into a broader range of IT Security work than just antivirus research. EICAR test file EICAR, in collaboration with CARO (Computer AntiVirus Research Organization), developed the EICAR te ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
The Apache Software Foundation
The Apache Software Foundation (ASF) is an American nonprofit corporation (classified as a 501(c)(3) organization in the United States) to support a number of open source software projects. The ASF was formed from a group of developers of the Apache HTTP Server, and incorporated on March 25, 1999. As of 2021, it includes approximately 1000 members. The Apache Software Foundation is a decentralized open source community of developers. The software they produce is distributed under the terms of the Apache License and is a non-copyleft form of free and open-source software (FOSS). The Apache projects are characterized by a collaborative, consensus-based development process and an open and pragmatic software license, which is to say that it allows developers who receive the software freely, to re-distribute it under nonfree terms. Each project is managed by a self-selected team of technical experts who are active contributors to the project. The ASF is a meritocracy, implying tha ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Anti-spam
Various anti-spam techniques are used to prevent email spam (unsolicited bulk email). No technique is a complete solution to the spam problem, and each has trade-offs between incorrectly rejecting legitimate email (false positives) as opposed to not rejecting all spam email (false negatives) – and the associated costs in time, effort, and cost of wrongfully obstructing good mail. Anti-spam techniques can be broken into four broad categories: those that require actions by individuals, those that can be automated by email administrators, those that can be automated by email senders and those employed by researchers and law enforcement officials. End-user techniques There are a number of techniques that individuals can use to restrict the availability of their email addresses, with the goal of reducing their chance of receiving spam. Discretion Sharing an email address only among a limited group of correspondents is one way to limit the chance that the address will be "harveste ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |