|
Flame Virus
Flame, also known as Flamer, sKyWIper, and Skywiper, is modular computer malware discovered in 2012 that attacks computers running the Microsoft Windows operating system. The program is used for targeted cyber espionage in Middle Eastern countries. Its discovery was announced on 28 May 2012 by the MAHER Center of the Iranian National Computer Emergency Response Team (CERT), Kaspersky Lab and CrySyS Lab of the Budapest University of Technology and Economics. The last of these stated in its report that Flame "is certainly the most sophisticated malware we encountered during our practice; arguably, it is the most complex malware ever found." Flame can spread to other systems over a local network (LAN). It can record audio, screenshots, keyboard activity and network traffic. The program also records Skype conversations and can turn infected computers into Bluetooth beacons which attempt to download contact information from nearby Bluetooth-enabled devices. This data, along with lo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan horses, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
International Telecommunication Union
The International Telecommunication Union is a specialized agency of the United Nations responsible for many matters related to information and communication technologies. It was established on 17 May 1865 as the International Telegraph Union, making it the oldest UN agency. The ITU was initially aimed at helping connect telegraphic networks between countries, with its mandate consistently broadening with the advent of new communications technologies; it adopted its current name in 1932 to reflect its expanded responsibilities over radio and the telephone. On 15 November 1947, the ITU entered into an agreement with the newly created United Nations to become a specialized agency within the UN system, which formally entered into force on 1 January 1949. The ITU promotes the shared global use of the radio spectrum, facilitates international cooperation in assigning satellite orbits, assists in developing and coordinating worldwide technical standards, and works to improve tele ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Antivirus Software
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other malware, antivirus software started to protect from other computer threats. In particular, modern antivirus software can protect users from malicious browser helper objects (BHOs), browser hijackers, ransomware, keyloggers, backdoors, rootkits, trojan horses, worms, malicious LSPs, dialers, fraud tools, adware, and spyware. Some products also include protection from other computer threats, such as infected and malicious URLs, spam, scam and phishing attacks, online identity (privacy), online banking attacks, social engineering techniques, advanced persistent threat (APT), and botnet DDoS attacks. History 1949–1980 period (pre-antivirus days) Although the roots of the computer ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security Descriptor
Security descriptors are data C++ classes, structures of security information for ''securable'' Windows NT, Windows Object Manager (Windows), objects, that is objects that can be identified by a unique name. Security descriptors can be associated with any named objects, including Computer file, files, Directory (file systems), folders, shares, Windows Registry, registry keys, processes, threads, named pipes, services, job objects and other resources. Security descriptors contain discretionary access control lists (DACLs) that contain access control entries (ACEs) that grant and deny access to trustees such as users or groups. They also contain a system access control list (SACLs) that control auditing of object access. ACEs may be explicitly applied to an object or inherited from a parent object. The order of ACEs in an ACL is important, with access denied ACEs appearing higher in the order than ACEs that grant access. Security descriptors also contain the object owner. Mandatory ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Page (computer Memory)
A page, memory page, or virtual page is a fixed-length contiguous block of virtual memory, described by a single entry in the page table. It is the smallest unit of data for memory management in a virtual memory operating system. Similarly, a page frame is the smallest fixed-length contiguous block of physical memory into which memory pages are mapped by the operating system. A transfer of pages between main memory and an auxiliary store, such as a hard disk drive, is referred to as paging or swapping. Page size trade-off Page size is usually determined by the processor architecture. Traditionally, pages in a system had uniform size, such as 4,096 bytes. However, processor designs often allow two or more, sometimes simultaneous, page sizes due to its benefits. There are several points that can factor into choosing the best page size. Page table size A system with a smaller page size uses more pages, requiring a page table that occupies more space. For example, if a 232 vi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SQLite
SQLite (, ) is a database engine written in the C programming language. It is not a standalone app; rather, it is a library that software developers embed in their apps. As such, it belongs to the family of embedded databases. It is the most widely deployed database engine, as it is used by several of the top web browsers, operating systems, mobile phones, and other embedded systems. Many programming languages have bindings to the SQLite library. It generally follows PostgreSQL syntax, but does not enforce type checking by default. This means that one can, for example, insert a string into a column defined as an integer. History D. Richard Hipp designed SQLite in the spring of 2000 while working for General Dynamics on contract with the United States Navy. Hipp was designing software used for a damage-control system aboard guided-missile destroyers, which originally used HP-UX with an IBM Informix database back-end. SQLite began as a Tcl extension. In August 2000, versio ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
FireEye, Inc
Trellix (formerly FireEye and McAfee Enterprise) is a privately held cybersecurity company founded in 2022. It has been involved in the detection and prevention of major cyber attacks. It provides hardware, software, and services to investigate cybersecurity attacks, protect against malicious software, and analyze IT security risks. In March 2021, Symphony Technology Group (STG) announced its acquisition of McAfee Enterprise in an all-cash transaction for $4.0 billion. STG completed the acquisition of McAfee’s Enterprise business in July 2021 with plans for re-branding. In June 2021, FireEye sold its name and products business to STG for $1.2 billion. STG combined FireEye with its acquisition of McAfee's enterprise business to launch Trellix, an extended detection and response (XDR) company. Meanwhile, McAfee Enterprise's security service edge (SSE) business would operate as a separate company to be known as Skyhigh Security. History FireEye was founded in 2004 by Ashar Azi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Lua (programming Language)
Lua ( ; from meaning ''moon'') is a lightweight, high-level, multi-paradigm programming language designed primarily for embedded use in applications. Lua is cross-platform, since the interpreter of compiled bytecode is written in ANSI C, and Lua has a relatively simple C API to embed it into applications. Lua originated in 1993 as a language for extending software applications to meet the increasing demand for customization at the time. It provided the basic facilities of most procedural programming languages, but more complicated or domain-specific features were not included; rather, it included mechanisms for extending the language, allowing programmers to implement such features. As Lua was intended to be a general embeddable extension language, the designers of Lua focused on improving its speed, portability, extensibility, and ease-of-use in development. History Lua was created in 1993 by Roberto Ierusalimschy, Luiz Henrique de Figueiredo, and Waldemar Celes, membe ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
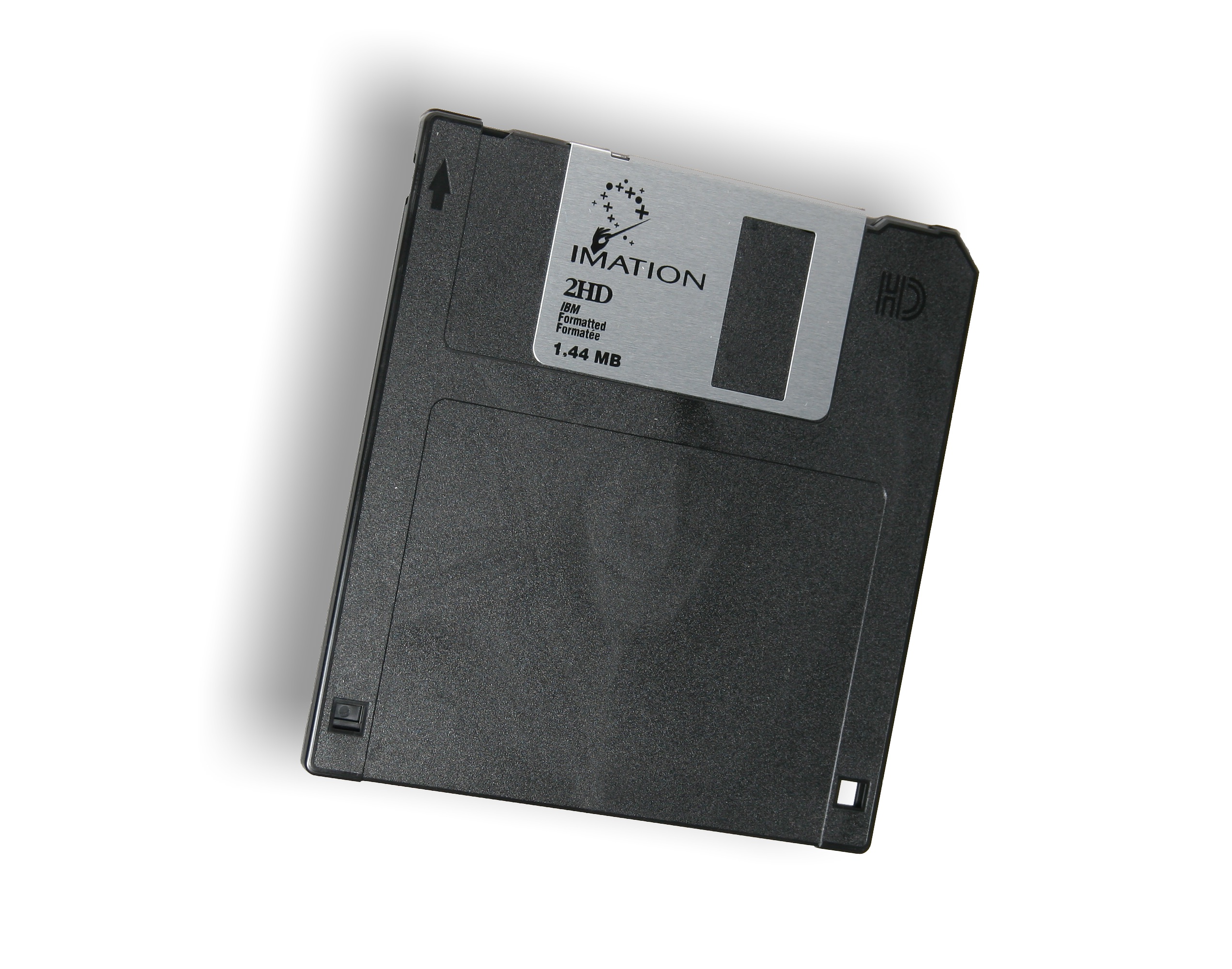
Megabyte
The megabyte is a multiple of the unit byte for digital information. Its recommended unit symbol is MB. The unit prefix ''mega'' is a multiplier of (106) in the International System of Units (SI). Therefore, one megabyte is one million bytes of information. This definition has been incorporated into the International System of Quantities. In the computer and information technology fields, other definitions have been used that arose for historical reasons of convenience. A common usage has been to designate one megabyte as (220 B), a quantity that conveniently expresses the binary architecture of digital computer memory. The standards bodies have deprecated this usage of the megabyte in favor of a new set of binary prefixes, in which this quantity is designated by the unit mebibyte (MiB). Definitions The unit megabyte is commonly used for 10002 (one million) bytes or 10242 bytes. The interpretation of using base 1024 originated as technical jargon for the byte SI prefix, mult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Program
A computer program is a sequence or set of instructions in a programming language for a computer to execute. Computer programs are one component of software, which also includes documentation and other intangible components. A computer program in its human-readable form is called source code. Source code needs another computer program to execute because computers can only execute their native machine instructions. Therefore, source code may be translated to machine instructions using the language's compiler. ( Assembly language programs are translated using an assembler.) The resulting file is called an executable. Alternatively, source code may execute within the language's interpreter. If the executable is requested for execution, then the operating system loads it into memory and starts a process. The central processing unit will soon switch to this process so it can fetch, decode, and then execute each machine instruction. If the source code is requested for execution, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Modular Programming
Modular programming is a software design technique that emphasizes separating the functionality of a program into independent, interchangeable modules, such that each contains everything necessary to execute only one aspect of the desired functionality. A module interface expresses the elements that are provided and required by the module. The elements defined in the interface are detectable by other modules. The implementation contains the working code that corresponds to the elements declared in the interface. Modular programming is closely related to structured programming and object-oriented programming, all having the same goal of facilitating construction of large software programs and systems by decomposition into smaller pieces, and all originating around the 1960s. While the historical usage of these terms has been inconsistent, "modular programming" now refers to the high-level decomposition of the code of an entire program into pieces: structured programming to the low-l ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
NortonLifeLock
Gen Digital Inc. (formerly Symantec Corporation and NortonLifeLock) is a multinational software company co-headquartered in Tempe, Arizona and Prague, Czech Republic. The company provides cybersecurity software and services. Gen is a Fortune 500 company and a member of the S&P 500 stock-market index. The company also has development centers in Pune, Chennai and Bangalore. Its portfolio includes Norton, Avast, LifeLock, Avira, AVG, ReputationDefender, and CCleaner. On October 9, 2014, Symantec declared it would split into two independent publicly traded companies by the end of 2015. One company would focus on security, the other on information management. On January 29, 2016, Symantec sold its information-management subsidiary, named Veritas Technologies, and which Symantec had acquired in 2004, to The Carlyle Group. On August 9, 2019, Broadcom Inc. announced they would be acquiring the Enterprise Security software division of Symantec for $10.7 billion, and the company became ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |